Figuring out what to do with all the data you collect is a headache. A data retention policy is your company’s official rulebook for that. It says how long you keep information and when you must securely destroy it. This isn't just for big companies; a clear policy helps startups dodge huge fines and makes compliance audits way less painful.
What Is a Data Retention Policy?

Think of a data retention policy as your guide for handling information. The idea is simple: only keep data as long as you have a good business or legal reason. This simple document is a core part of your security and compliance strategy. Without a policy, you become a data hoarder, which creates unnecessary risk.
The more data you keep, the more you have to protect. A data breach becomes more damaging, and storage costs climb. A smart policy fixes this by setting "expiration dates" for different kinds of data. This isn't just a suggestion; it's often the law. Global data protection trends show that most countries now have privacy laws.
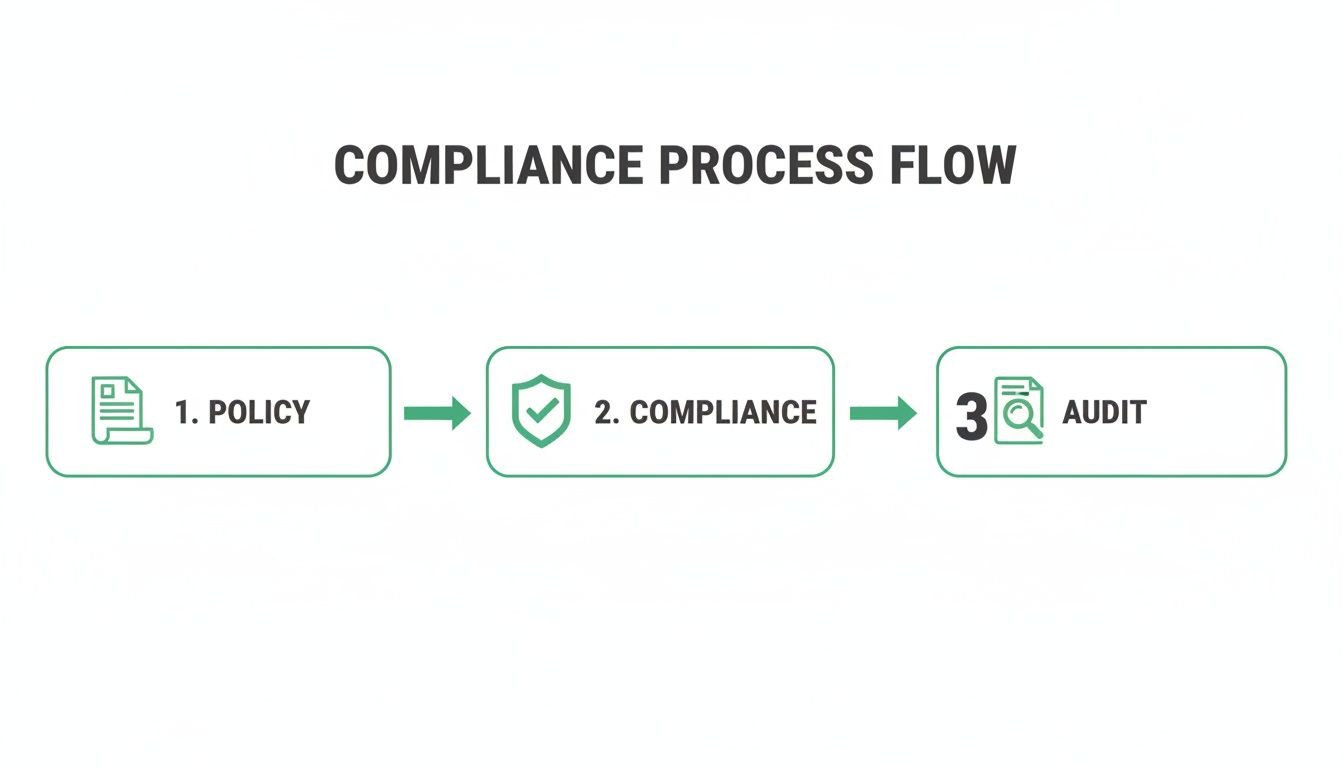
A strong data retention policy is a must-have for passing audits. For frameworks like SOC 2, HIPAA, or PCI DSS, auditors will absolutely ask to see it. Deleting old data also shrinks your attack surface. Hackers can't steal what you don't have. But how do you know your systems actually follow your rules? This is where a penetration test comes in.
An affordable pen test from certified pros (OSCP, CEH, CREST) can confirm your systems are working as designed. You get a report in under a week, showing you where your controls are solid and where they need fixing. To see how we can help, fill out our contact form.
Why You Need a Data Retention Policy
Running a business without a data retention policy is a massive gamble. It’s like driving without insurance. A single mistake can be catastrophic. Hoarding data makes you a bigger target for hackers and exposes you to huge fines. And those fines are getting steeper every year.
Regulators are not messing around. Many firms are still stuck using manual, error-prone processes that attackers love to exploit. You can read more in these data privacy and compliance statistics for 2026. A data retention policy isn't just a legal document—it's a security tool. By systematically deleting data you no longer need, you shrink your attack surface.
Every piece of data you store is a potential liability. A clear policy forces you to get rid of old information, which directly shrinks your risk. This isn't just about hackers. In a legal dispute, you could be forced to produce years of old emails. Following a routine data destruction schedule legally reduces the information available, saving you time and money.
For certifications like SOC 2 or ISO 27001, a data retention policy isn't optional. It's a core requirement. Auditors will ask for it on day one. Understanding principles like EU Data Sovereignty is also a big piece of the puzzle. But how do you prove your policy actually works? The answer is an affordable penetration test.
Our expert pentesters, holding OSCP, CEH, and CREST certifications, validate that your controls enforce your policy. Unlike slow and expensive firms, we deliver a detailed penetration testing report in under a week. This fast and affordable pen testing service gives you the assurance you need.
The Core Parts of Your Policy
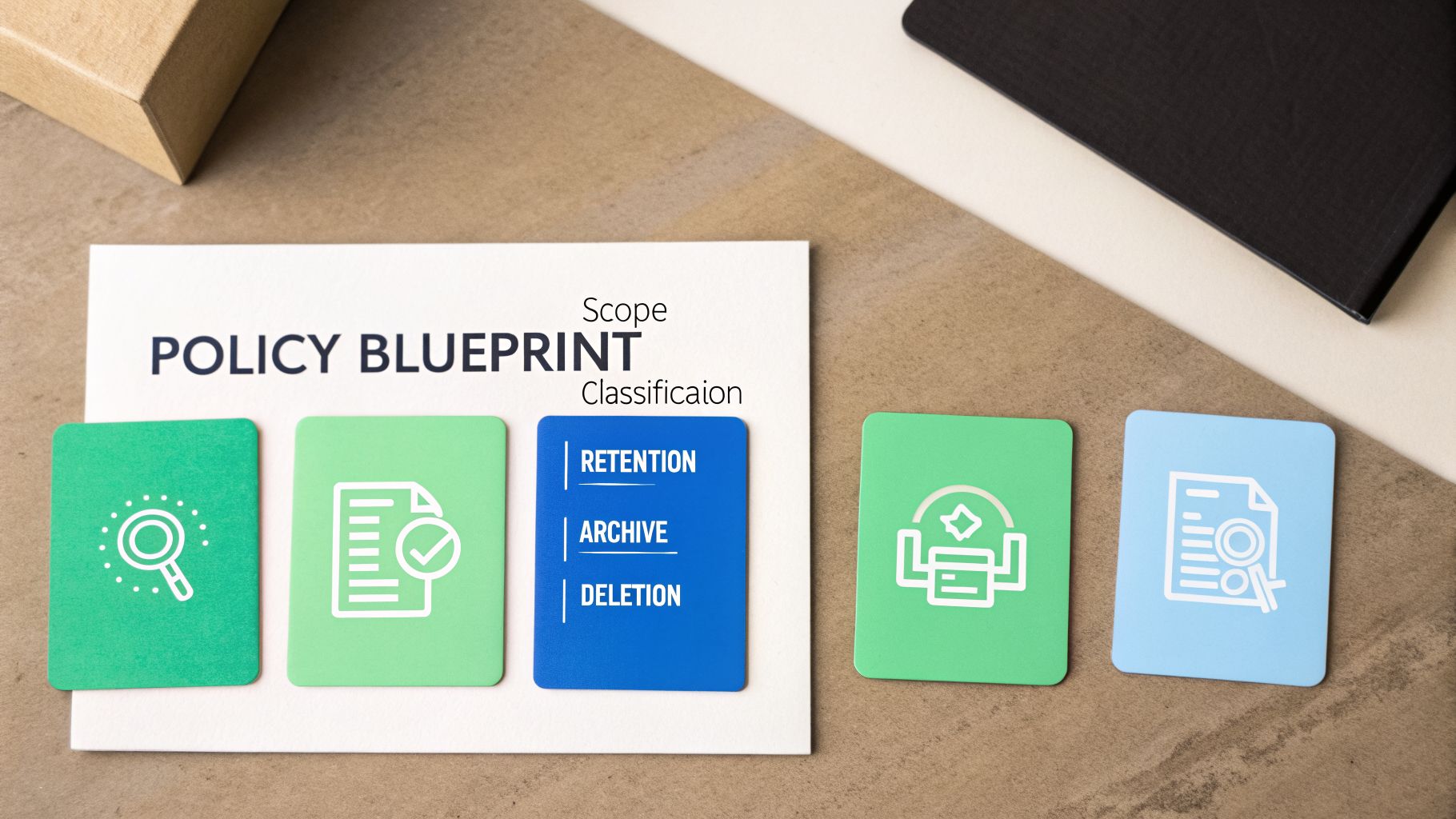
Let's build your data retention policy. Think of it like a blueprint. Each part is critical for the whole thing to stand strong. A solid policy is a collection of clear components that work together. This framework will help you draft a policy that makes sense for your business, no law degree required.
First, decide what data your policy covers. This is the scope. Does it apply to every file, or just specific types like customer info? A clear scope covers all digital files, physical records, and all storage locations, from company servers to cloud services. This removes any guesswork about what needs to be managed.
Next, you have to sort your data. This is data classification. It's like sorting mail into piles based on how sensitive it is. A simple system includes Public, Internal, and Confidential/Sensitive data. This lets you apply the right rules to the right information. You can find more in our information security policy template.
A retention schedule is the heart of your policy. It's a list that defines how long each type of data must be kept. For instance, tax documents might need to be kept for seven years, while old support chats might only be needed for one. Your schedule must balance legal requirements with business needs. Hold data only as long as required, and not a day longer.
When data hits its expiration date, you need clear procedures for archiving and deleting. Archiving is moving data to cheaper, long-term storage. Secure deletion means permanent, irreversible destruction. For tips, check out this guide on crafting a secure data destruction policy. An affordable pen test is the best way to verify your controls work as designed. Our pentesters (OSCP, CEH, CREST) can confirm your data is handled correctly and get you a report in under a week.
How Your Policy Helps With Compliance
Think of a solid data retention policy as your cheat sheet for passing audits. You're juggling rulebooks like SOC 2, HIPAA, and PCI DSS. A single, well-built policy helps you satisfy most of them at once. It saves you from starting from scratch for every framework.
But this isn't just about having a document. It’s about proving you follow your own rules. Auditors can spot the difference between a policy on paper and a policy in practice. If you can't show evidence your policy is enforced, it’s just a red flag for them.
SOC 2 and ISO 27001 are all about trust. They require you to demonstrate control over your data’s entire lifecycle. Your data retention policy is the cornerstone of this proof. It shows auditors you have a system to manage information. Auditors will dig in to verify your systems actually follow these rules.
If you handle Protected Health Information (PHI), HIPAA is non-negotiable. The law requires you to keep patient documents for at least six years, but some states demand longer. Your policy must detail exactly how you retain, archive, and destroy PHI to protect patient privacy.
The Payment Card Industry Data Security Standard (PCI DSS) is focused on protecting credit card info. It's more about what you absolutely cannot keep. You are prohibited from storing sensitive data, like the three-digit code on a card, after a transaction is authorized. Your policy must be explicit about destroying this data immediately. For more on compliance, check out our guide on what is compliance management.
Writing the policy is just step one. An affordable penetration test is the best way to validate your controls. Our certified pentesters simulate real-world attacks to find gaps where data is over-retained or insecure. Unlike slow, expensive firms, we deliver a comprehensive penetration testing report in under a week.
How to Implement Your Retention Policy
A data retention policy sitting on a shelf is worthless. You have to bring it to life. A policy is a living part of your security strategy. Putting it into action means getting everyone on the same page, from leadership down to every employee.
For any policy to succeed, you need support from the top. Explain the business benefits: reduced risk, lower costs, and smoother audits. Once leadership is on board, train your employees. Everyone handles data, so everyone needs to understand their role. A well-trained team is your first line of defense.
Relying on people to manually delete data is a recipe for failure. The only reliable way to enforce your policy is through automation. Work with your IT team to configure your systems to automatically manage the data lifecycle. This includes setting up rules in your email servers, cloud storage, and databases to archive or delete data automatically.
How do you know your automated systems are working? You have to test it. This is where an affordable pen test is essential. A penetration test validates that your technical controls are enforcing your policy correctly. Our OSCP, CEH, and CREST-certified pentesters act like real attackers, searching for gaps where data is over-retained.
Global trends show a need for validation. A Cisco survey showed most businesses want simpler rules, but regulators are still actively auditing. You can learn more about the global data governance survey. With our affordable penetration testing, you get a detailed report in under a week, without the high costs of traditional firms.
Data Retention Policy FAQs
Have questions about data retention policies? Here are direct answers to common questions from IT managers and founders.
How Long Should We Keep Customer Data?
There’s no single answer. It depends entirely on the type of data and the legal rules that apply to it. Financial records often need to be kept for seven years or more. Marketing data might only be needed for a few months. Your policy must define specific timelines for each category of data based on legal obligations and business needs.
What Is the Difference Between Archiving and Deleting?
Think of it like cleaning out a filing cabinet. Archiving is moving files you don't need daily to secure, long-term storage. Deleting is like putting those files through a shredder. It means permanently destroying the data. Your policy needs to be crystal clear about when to archive versus when to delete.
How Can We Prove Our Policy Is Working?
Proof comes from documentation and technical validation. First, you need clear logs of deletion and archival activities. But logs only show what is supposed to be happening. This is where a pen test is essential. Our OSCP, CEH, and CREST-certified pentesters can verify there are no gaps where data is being over-retained. We deliver your report in just a week.
Can We Use a Template for Our Policy?
Yes, a template is a great starting point, but you must customize it for your business. A generic policy won't satisfy an auditor. Your policy needs to reflect the specific types of data you handle, your industry's legal requirements, and your internal systems. Think of a template as a frame; you still need to build the house.
What Are the Biggest Data Retention Challenges?
The biggest challenges aren't writing the policy; it's enforcing it. Data disposal is a huge hurdle. Files get copied and moved, falling outside automated workflows. Another issue is tool sprawl, with different teams using different apps. Enforcing one policy across disconnected platforms is tough. This is why a pen test is so valuable; it helps find data hiding in forgotten corners.
Ready to validate that your data retention policy is actually working? At Affordable Pentesting, we provide fast, affordable, and thorough penetration testing to give you the proof you need. Our certified experts will identify gaps in your data handling before an attacker or auditor does.
Get your affordable pentest report in under a week by filling out our contact form.
.svg)
