Everyone focuses on websites, but what about the software on your computers? Your custom finance tools, healthcare apps, and internal software are often a huge security blind spot. Attackers love to exploit them.
Desktop application penetration testing is how you find critical bugs in these programs that scanners always miss. It’s a manual, human-led process to secure your business without the high prices and long waits from traditional pentesting firms.
Why Desktop Application Pen Testing Matters

Think of your security like a fortress. Your website is the main gate, but what about all the side doors? Your desktop apps are those side doors. A desktop application penetration test is a practice attack to find and lock them before a real attacker does.
For IT managers, CISOs, and founders, this isn't just a technical exercise; it's a business need. We hear the frustration all the time. Old-school pentesting firms charge a fortune, take months for a report, and often find nothing useful. We deliver fast, affordable manual pentests with real results and a report in about a week.
Uncover Your Security Blind Spots Now
Many companies pour their security budgets into web app pentesting, leaving desktop software completely exposed. This is a huge mistake. Attackers know these apps are less guarded, making them an easy way into your network.
Once inside, they can steal sensitive data or attack other systems. A desktop application penetration test is no longer optional, especially for businesses in regulated fields like finance or healthcare that must meet SOC 2, HIPAA, or PCI DSS compliance.
Manual Pentesting Finds What Scanners Miss
Automated scanners are good for finding obvious problems, but they can’t understand your app's unique logic. This is where a manual penetration test by certified experts makes all the difference. Our pentesters hold certifications like OSCP, CEH, and CREST and think like real attackers.
Our human-led approach uncovers issues like insecure data storage or flaws that let an attacker take control. A desktop application pentest gives a much clearer picture of your security than a simple scan. It's the most effective way to identify the critical issues that actually matter.
Desktop Pentesting Vs Other Security Tests
While scanners look for known problems and web pentests focus on servers, a desktop penetration test zeroes in on the unique risks of client-side software. By focusing here, our penetration testing process provides a complete picture of your app's security.
This is an affordable investment that gives you the detailed findings you need to secure your apps and pass audits. All within a budget and timeline that makes sense for your business.
Understand Your Application's Threat Landscape
Every desktop app has its own security risks. Think of your software as a house; our job is to find the unlocked windows before a real intruder does. Understanding these risks helps you see why a manual pen test is non-negotiable.
Whether your app is built for Windows, macOS, or a framework like Electron or .NET, it faces specific threats. To protect it, you need a layered defense in depth strategy. A real desktop application penetration test covers all angles, giving you a clear, honest picture of your security.
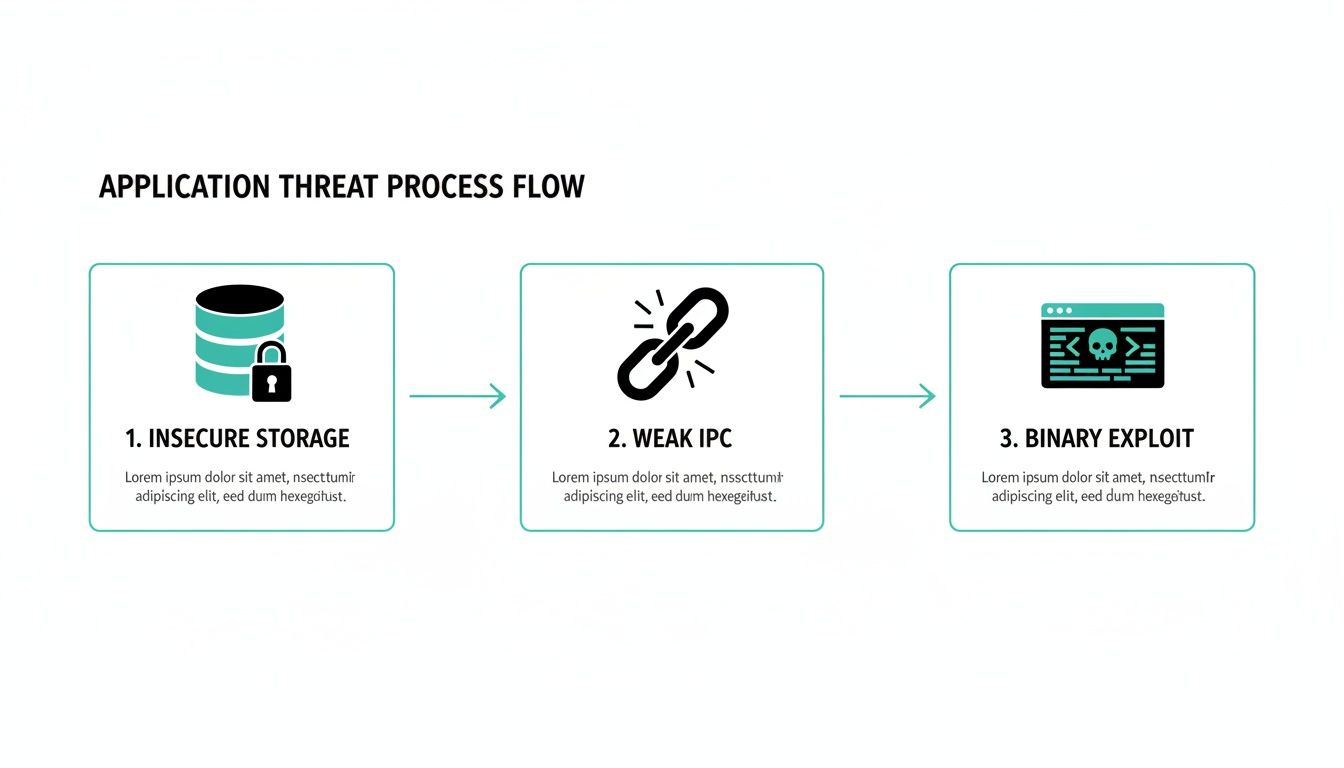
Discover Key Threats In Desktop Apps
When our certified pentesters conduct a desktop application pen test, they act like real attackers trying to break your software. They focus on the unique attack paths that desktop programs present.
Some of the most common threats we hunt for include insecure data storage, where apps leave API keys or credentials in plain text. We also check for weak Inter-Process Communication (IPC), where an attacker could listen in or send malicious commands. Our team also performs binary manipulation to find hardcoded secrets or backdoors before attackers do.
How App Frameworks Change The Game
The technology your app is built on completely changes its security profile. A one-size-fits-all approach to penetration testing is lazy and ineffective. We tailor our entire methodology based on your specific tech stack.
For example, a .NET or Java app is still a target for attacks like insecure deserialization, where crafted data can trick the app into running bad code. Electron apps are different; they can be vulnerable to web-style attacks like Cross-Site Scripting (XSS) that could let an attacker read local files. Our goal is to find the vulnerabilities that actually matter and deliver a high-quality pen test report in about a week.
Our Fast Manual Penetration Testing Process

We built our process for speed and depth, getting you a detailed report in about a week. We skip the enterprise fluff and focus on a transparent, manual penetration testing methodology that uncovers the critical risks other firms miss. This is the playbook our certified experts use to break down your app.
Our process isn't a black box. It's a systematic approach where each phase builds on the last. We ensure every angle is covered, from initial discovery to deep binary exploitation.
Phase 1: Reconnaissance And Information Gathering
Every solid pen test starts with good recon. Our team creates a detailed map of your application's attack surface before launching any exploits. We gather public information, analyze the tech stack, and identify potential entry points, just like a real attacker would.
This initial phase is critical. It helps us understand everything from your application's framework to the third-party libraries it uses. This allows us to tailor our attack strategy specifically to your software, making our desktop application penetration testing ruthlessly efficient.
Phase 2: Static And Dynamic Analysis
Next, our pentesters dive into the app using static and dynamic analysis. Static analysis is like reading a building's blueprints to find weaknesses. We examine your app's code without running it.
Dynamic analysis is testing the app while it's running. Our team interacts with it, feeding it unexpected inputs and monitoring its behavior under pressure. This is where we often uncover logic flaws that automated scanners are completely blind to, including how desktop apps talk to backend services. For a deeper look at securing those connections, you can explore resources on REST API testing.
Phase 3: Exploitation and Deep Analysis
This is where our OSCP, CEH, and CREST certified experts get to work. We go beyond surface-level checks and dig into your app's core to find hidden vulnerabilities that could lead to a major breach. It’s what separates a real security assessment from a check-the-box pen test.
Our advanced techniques include binary reversing, where we deconstruct your app’s code to hunt for secrets and logic flaws. We also search for privilege escalation weaknesses that could give an attacker administrative control. Finally, we meticulously check how and where your app stores sensitive data to ensure it is properly encrypted.
How Pentesting Supports Your Compliance Goals
For a CISO or founder, a desktop application penetration test isn't just another security task. It's a direct line to hitting your compliance goals. Facing an audit for SOC 2, HIPAA, or PCI DSS can feel like a final exam you can't afford to fail. Our pentest gives you the answers ahead of time.
Think of it this way: your auditor wants you to prove you're protecting sensitive data. A simple promise won't cut it. Our penetration test report is the hard evidence you need. It shows you’ve looked for weaknesses, found them, and have a clear plan to fix them.
Connecting Pentesting To Your Compliance Needs
You’re not just buying a test; you’re buying confidence for your next audit. We designed our process to map directly to the controls in major compliance frameworks. When our pentesters find a vulnerability, we don't just point it out—we explain why it matters for your audit.
This turns a technical chore into a business advantage. Instead of scrambling to check boxes for an auditor, you’re building real, defensible security into your application. That proactive stance is what auditors, and more importantly, your customers, want to see.
How A Desktop Pen Test Helps You Pass Audits
Every compliance standard has its own rules, but they all share one core principle: protect the data. A desktop application pen test provides the tangible proof you need to show you’re meeting that obligation. It's the difference between telling an auditor you’re secure and showing them.
For SOC 2, our report details issues like insecure local data storage, directly addressing the Security Trust Services Criteria. For HIPAA, our penetration testing checks if your app stores ePHI insecurely, helping you satisfy technical safeguards. For PCI DSS, a thorough pen test uncovers coding flaws that could lead to a payment card breach.
An Affordable Path to Passing Your Audits
We know the pain of dealing with old-school pentesting firms. Their sky-high prices and slow turnarounds make compliance feel impossible, especially for startups. Our model was built to fix that.
Our team of certified experts—holding certifications like OSCP, CEH, and CREST—delivers a high-quality, manual pen test at a fraction of the cost. You get a detailed, audit-ready report in about a week. Don't let compliance be a roadblock; use our affordable pentest service to fast-track your next certification.
Frequently Asked Questions
Got questions about desktop application penetration testing? We have direct, no-nonsense answers to help you make a decision without the usual sales fluff.
How much does a desktop pen test cost?
The cost of a desktop application penetration test really comes down to the app's complexity, but our entire model is built to be affordable. We give you a fixed-price quote that actually fits a startup or SMB budget. You get pentesters with top certifications, just without the enterprise price tag.
How long does a desktop pentest take?
We're built for speed. While other firms might take weeks or even months to get you a report, we complete most desktop application pen tests and deliver the final report in about one week. This quick turnaround means you can start fixing things right away and speed up your compliance timeline.
What kind of report will I get?
You'll get a clear, actionable report written for everyone—from your developers to your management team. It breaks down every vulnerability our OSCP, CEH, and CREST certified pentesters found, with risk ratings and simple, step-by-step instructions for fixing them. Our reports are designed to be audit-ready from day one.
Ready to secure your desktop application without the high costs and long waits? The team at Affordable Pentesting delivers fast, thorough, and affordable manual penetration testing. Get a clear, actionable report in about a week. Get started by visiting https://www.affordablepentesting.com.
.svg)