Intrusion testing tools are what security experts use to find weak spots in your company’s defenses, like a friendly burglar checking your locks. Think of them as a special toolkit for a digital detective. These tools help a penetration testing team scan your networks and apps for holes before real attackers find them.
The real value isn't the tool, it's the certified expert using it. A great tool in the wrong hands just creates noise. A skilled professional, someone with OSCP or CEH certifications, uses these tools to find real risks that automated scans miss. This is why a manual penetration test is so important.
This article cuts through the noise. We will cover effective intrusion testing tools, from free ones like Nmap to pro tools like Burp Suite. Our goal is to help you understand the pen test process so you can make smart decisions without paying for slow, overpriced security audits.
Understand Burp Suite for Web App Pen Testing
Burp Suite Professional is the essential toolkit for web application and API penetration testing. It acts as a middleman, letting you inspect and change the traffic between your browser and a web server. This control is why it's a favorite for pentesters doing manual security checks.
This tool is great at finding problems that automated scanners miss. Professionals use it to manually poke at websites and find complex flaws. These manual techniques are critical for different types of penetration testing needed to meet compliance standards like SOC 2 and PCI DSS.
- Best Use-Case: Detailed manual and semi-automated web application and API pen testing.
- Strengths: Excellent balance between manual control and automated assistance, massive community support, and extensive extensibility. The workflow is fast and intuitive for experienced testers.
- Weaknesses: The tool is desktop-focused and can consume significant system resources when scanning large applications. Enterprise-level orchestration and reporting require a separate, more expensive product.
- Pricing: A single-user professional license costs $449 per year.
Using Metasploit for Vulnerability Exploitation
The Metasploit Framework is the most famous tool for hacking into systems for testing purposes. It’s a huge, free library of exploits that lets security pros prove a vulnerability is real. Instead of just knowing a system has a weak spot, Metasploit lets you show the risk by safely exploiting it.
This framework is a cornerstone for any pen test. Pentesters use it to launch known attacks against targets to confirm they are vulnerable. It’s also a great way to learn what is penetration testing and how hackers turn a weakness into a real problem.
- Best Use-Case: Validating vulnerabilities, developing proofs-of-concept (PoCs), and post-exploitation actions.
- Strengths: Enormous and frequently updated module library supported by a large community. It is an excellent platform for learning exploit development and quickly verifying security findings.
- Weaknesses: Payloads are often flagged by modern EDR and antivirus solutions, requiring significant customization for stealthy operations. Advanced, custom tradecraft may require moving beyond the standard modules.
- Pricing: The core framework is free and open-source. A commercial "Pro" version with additional automation and reporting features is available with custom pricing.
Why Nmap Is Essential for Network Scanning
Nmap is the go-to tool for discovering what’s on a network. For any pentester, it's the first step to answer basic questions like what computers are active and what services they're running. Its speed makes it a must-have for any network penetration test.
Nmap gets even more powerful with its scripting engine. Thousands of community-written scripts can automate tasks from simple checks to finding complex vulnerabilities. This turns Nmap from a simple scanner into one of the most flexible intrusion testing tools out there.
- Best Use-Case: Foundational network reconnaissance, port scanning, and service enumeration for any type of network pen test.
- Strengths: Extremely fast, lightweight, and universally supported across all platforms. The NSE provides immense flexibility for automated vulnerability checks.
- Weaknesses: It is a reconnaissance tool, not a full exploitation framework or vulnerability management solution. Interpreting advanced scan results requires significant expertise.
- Pricing: Free and open-source.
Nessus for Automated Vulnerability Scanning
Nessus is a famous tool for vulnerability scanning. It automatically checks networks and computers for known security problems, like missing patches or bad settings. It’s not for manual hacking, but it gives pentesters the starting points they need to find entryways.
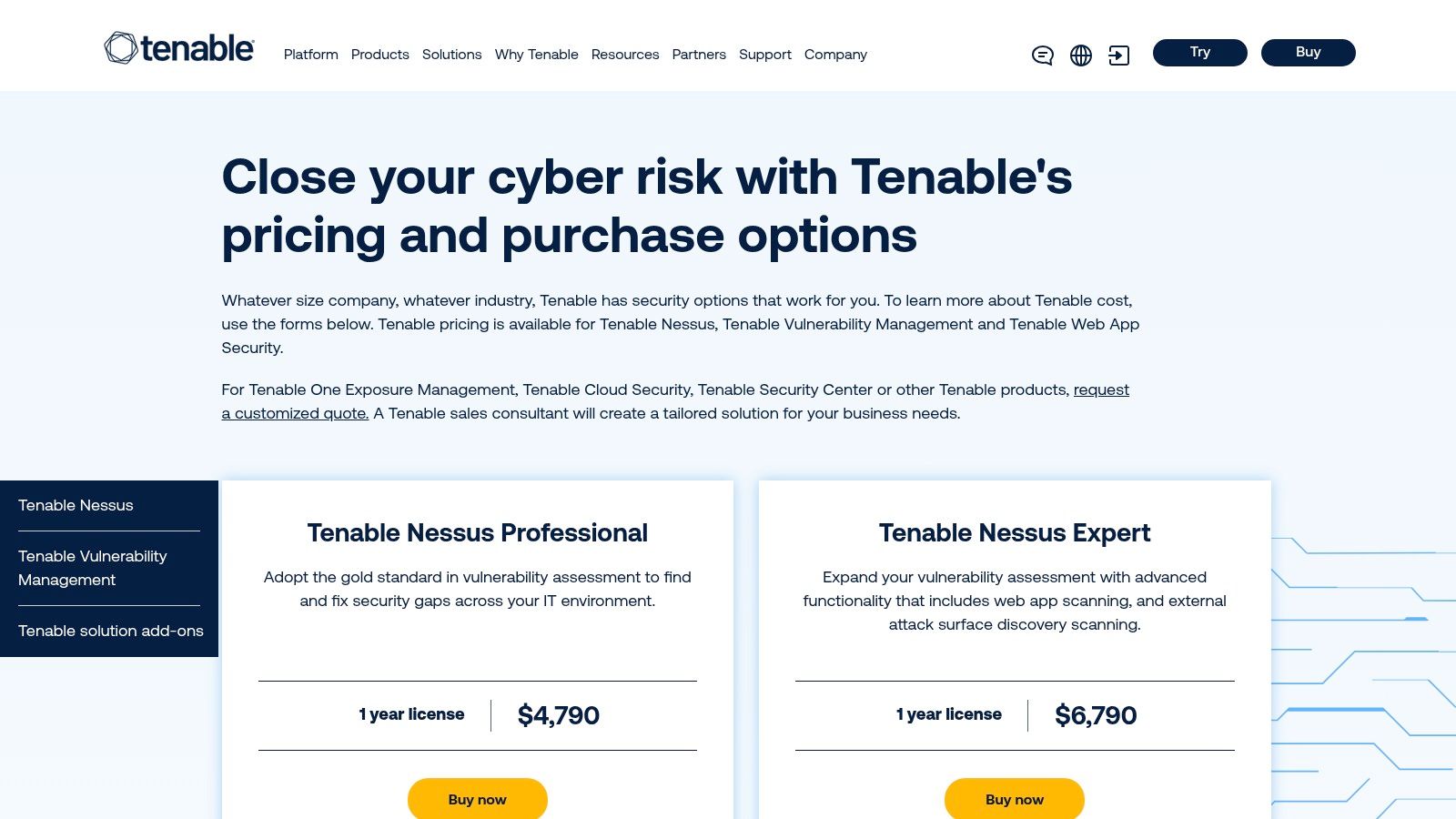
This tool is often used to get a baseline for security and is critical for compliance audits like SOC 2 and HIPAA. A Nessus scan tells you what might be wrong. A full penetration test confirms if those weaknesses can actually be exploited to cause a breach.
- Best Use-Case: Automated vulnerability scanning and compliance auditing for on-premise and cloud infrastructure.
- Strengths: Mature and reliable with a massive library of vulnerability checks. It's simple to set up for recurring scans and generates detailed reports for compliance evidence.
- Weaknesses: Web application scanning is basic compared to dedicated tools like Burp Suite. Licensing is per scanner, and managing scans across many assets requires more expensive Tenable products.
- Pricing: Nessus Professional starts at $3,390 for a one-year subscription.
Kali Linux is an All-in-One Pentesting OS
Kali Linux isn’t just one tool, it’s a complete operating system built for penetration testing. It comes loaded with hundreds of intrusion testing tools already installed and ready to go. For security professionals, it saves hours of setup time and provides a standard environment.
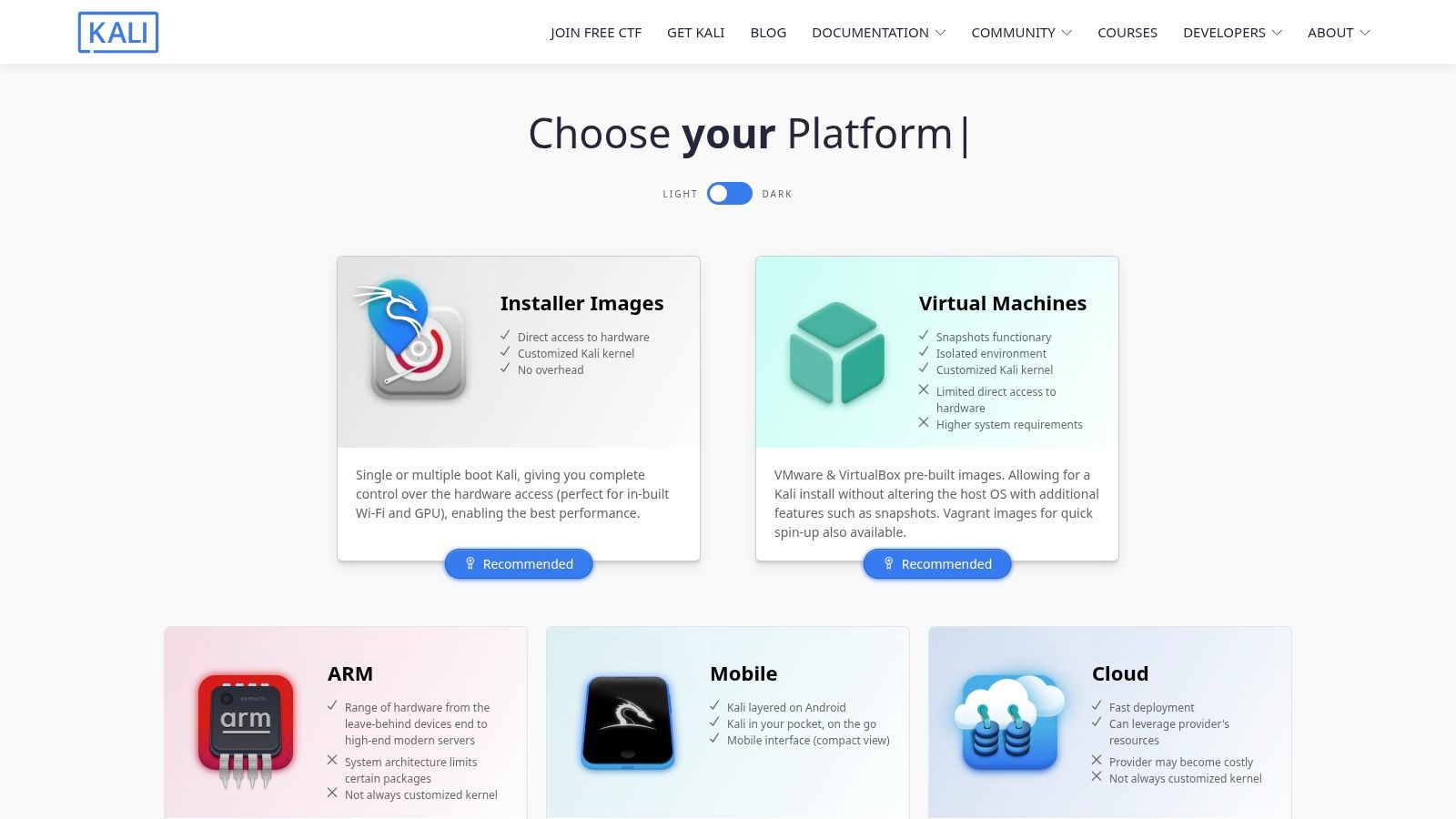
The main benefit of Kali is having everything in one place. Whether you're doing a network pen test or checking a web app, the right tools are already there. This makes it a great platform for both learning and professional security work.
- Best Use-Case: A standardized, all-in-one operating system for conducting any type of security assessment or penetration test.
- Strengths: Saves significant setup time by providing a consistent and comprehensive environment. It receives strong community support, frequent updates, and excellent documentation.
- Weaknesses: It is not a single tool but a collection, meaning the user still needs expertise to select and operate the right programs. Hardware-specific configurations, like for certain GPUs, can sometimes require manual setup.
- Pricing: Completely free and open-source.
OWASP ZAP for Free Web Security Scanning
OWASP ZAP is the world's most popular free web application security scanner. It’s a great starting point for developers and security teams on a budget. Like other professional tools, it lets you intercept traffic for manual inspection alongside powerful automated scanning.
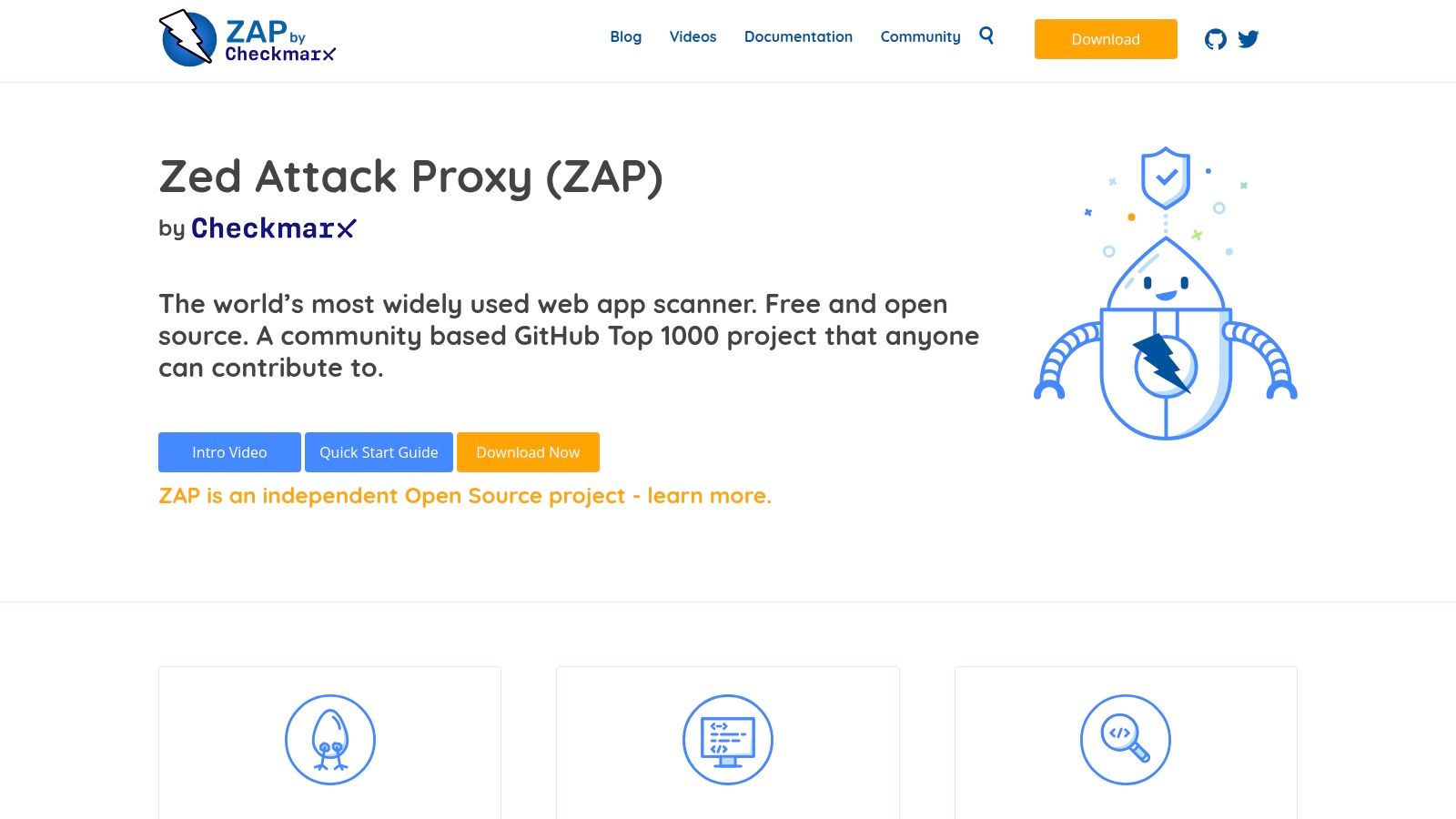
ZAP is built to be automated, making it a favorite for adding security checks into the development process. Its manual features also allow for hands-on penetration testing. It’s a very flexible tool thanks to community-contributed add-ons that extend its features.
- Best Use-Case: Automated web security scanning in CI/CD pipelines and manual pen testing for individuals or teams on a budget.
- Strengths: Completely free and open-source, strong community support, and designed for easy automation and API-based integration.
- Weaknesses: The user interface can feel less polished than commercial alternatives. Automated scan speed and accuracy on very complex, modern applications may require significant tuning to reduce false positives.
- Pricing: Free.
Using Wireshark for Deep Network Analysis
Wireshark is the world's top tool for looking at network traffic up close. It doesn’t scan or hack, but it gives you a perfect view of what’s happening on your network. During a penetration test, it's used to see exactly what data is moving back and forth.
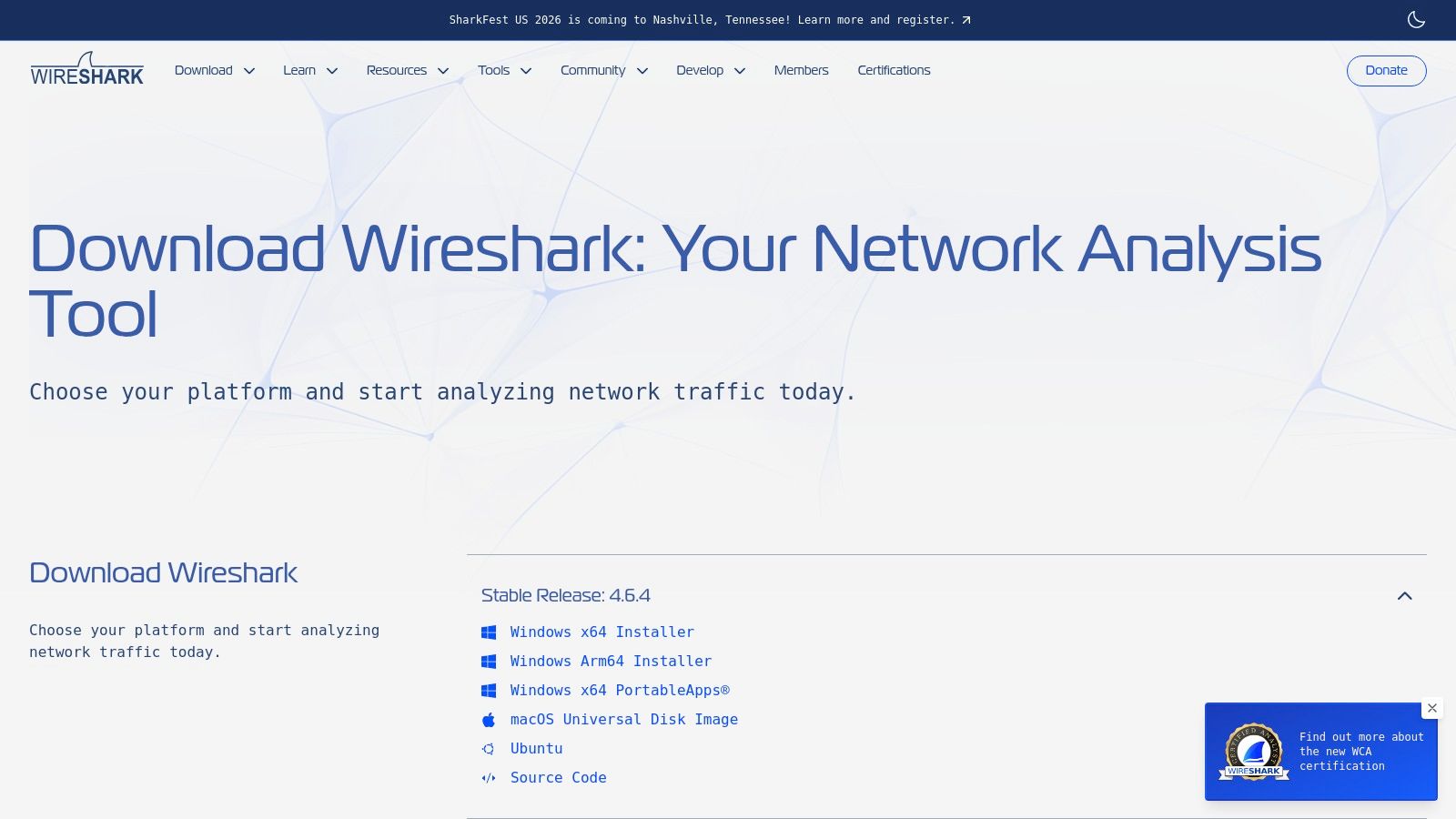
This level of detail is critical for deep-dive intrusion testing. A pentester might use Wireshark to confirm an attack worked or to find unencrypted passwords being sent over the network. Understanding its output is a core skill for anyone doing serious pen testing.
- Best Use-Case: Deep network traffic analysis, exploit validation, and protocol-level troubleshooting.
- Strengths: Essential for validating exploit traffic and investigating edge cases. It is mature, stable, and widely taught with strong documentation.
- Weaknesses: It is not a vulnerability scanner and requires significant expertise to interpret results for security purposes. Capturing traffic requires privileged access, which can be complex to set up securely.
- Pricing: Free and open-source.
Cobalt Strike for Advanced Red Team Operations
Cobalt Strike is a top tool for simulating a real hacker attack. It helps security teams pretend to be an advanced attacker inside a network to test the company's defenses. It's designed to be stealthy, making it a powerful tool for testing security against sophisticated threats.
This platform is made for team-based security tests where multiple people work together. It allows testers to disguise their traffic to look like normal activity, which helps them avoid detection. Because it’s so powerful, Cobalt Strike has a strict vetting process to keep it out of the wrong hands.
- Best Use-Case: Advanced adversary simulation, red team operations, and testing security incident response capabilities.
- Strengths: Standardized and effective tradecraft for post-exploitation, excellent for collaborative team-based operations, and a strong ecosystem of community-developed extensions.
- Weaknesses: Premium pricing and a strict buyer verification process make it inaccessible for many. If operational security (OPSEC) is not properly managed, its signatures are well-known to modern EDR and antivirus solutions.
- Pricing: Pricing is not public; it requires a direct sales inquiry and is sold via annual license.
Core Impact for Repeatable Penetration Testing
Core Impact is a commercial tool designed for security teams that need a structured and repeatable pen testing process. It offers guided workflows and automated attacks, making it easier for teams with different skill levels. It helps confirm if vulnerabilities found by scanners are truly exploitable.
The main advantage of Core Impact is its ability to produce consistent results for compliance reports like PCI DSS and HIPAA. It can take results from a vulnerability scan and try to exploit the findings automatically. This provides clear proof of risk for auditors.
- Best Use-Case: Internal security teams performing routine penetration tests and validating scanner results for compliance reporting.
- Strengths: Structured workflows support both junior and senior testers. The reporting capabilities are strong and designed for audit purposes.
- Weaknesses: Quote-based pricing and a formal sales process can be a barrier. Advanced users may prefer the flexibility of open-source tools for custom attack development.
- Pricing: Available via quote-based licensing in Basic, Pro, and Enterprise tiers.
Acunetix for Web App and API Security
Acunetix is a tool that automates security scanning for web applications and APIs. It crawls a website and runs tests to find common problems like SQL Injection. For companies with many websites, Acunetix provides a way to get a baseline of security before a manual pen test.
This tool is great for adding security checks into the development cycle. It can automatically create tickets for developers when it finds a problem, helping teams fix bugs faster. While it's great for catching easy-to-find issues, it’s not a substitute for a manual penetration test.
- Best Use-Case: Automated DAST scanning for web applications and APIs within a CI/CD pipeline.
- Strengths: Scales continuous scanning across many applications, provides clear dashboards for remediation owners, and integrates well with development tools.
- Weaknesses: Not a replacement for expert manual penetration testing on complex business logic. Target counting and scoping require careful planning to manage costs.
- Pricing: Pricing is quote-based and varies depending on the number of target websites and applications.
OpenVAS for Open Source Vulnerability Scanning
OpenVAS is a powerful, free solution for network vulnerability scanning. It checks systems against a huge list of known security problems to find holes and misconfigurations. It automates the first step of a pen test, giving security teams a clear map of potential weaknesses.
This platform is valuable for setting up an ongoing vulnerability management program. Regular scans can help meet compliance rules like PCI DSS by finding old software and missing patches. Running an OpenVAS scan first helps pentesters focus their manual effort on more complex problems.
- Best Use-Case: Automated network and server vulnerability scanning to identify known security issues and misconfigurations.
- Strengths: The Community Edition offers a powerful, no-cost entry point for vulnerability management. It has a comprehensive feed of vulnerability checks and provides a clear upgrade path to supported enterprise products.
- Weaknesses: The community version can be complex to set up and maintain, often requiring solid Linux administration skills. Its community feed and features may also lag behind the commercial Greenbone offerings.
- Pricing: The OpenVAS scanner and community feed are free. Commercial solutions (Greenbone Enterprise Appliance) are available with enterprise-level features and support.
Using Nuclei for Fast, Custom Security Scans
Nuclei is a fast, template-based vulnerability scanner that is great for automating custom checks. It uses simple files to define security tests, allowing teams to quickly write and share checks for new vulnerabilities. Its speed makes it perfect for adding security scanning into development pipelines.
The real power of Nuclei comes from its huge library of community-written templates. This allows companies to quickly scan for specific problems at a massive scale. It is one of the most effective intrusion testing tools for teams that want to turn their security knowledge into code.
- Best Use-Case: Fast, large-scale scanning for known vulnerabilities and custom misconfigurations, especially within CI/CD pipelines.
- Strengths: Extremely fast and highly customizable due to its YAML template engine. The community provides rapid updates for emerging threats.
- Weaknesses: Scan output requires significant triage and manual validation to confirm findings and eliminate false positives. Crafting effective custom templates requires technical skill.
- Pricing: The core scanner is open-source and free. ProjectDiscovery offers a paid Cloud Platform for team collaboration and management.
Comparing the Top Intrusion Testing Tools
| Tool | Core focus ✨ | Quality / UX ★ | Price / Value 💰 | Target audience 👥 | Best for 🏆 |
|---|---|---|---|---|---|
| Burp Suite Professional (PortSwigger) | Intercepting proxy, DAST, extensions | ★★★★★ fast manual + assisted workflows | 💰 Paid (pro license) | 👥 Web pentesters, bug bounties, SMB security teams | 🏆 Manual + automated web testing balance |
| Metasploit Framework (Rapid7) | Exploitation & post-exploitation framework | ★★★★ PoC validation & exploit dev | 💰 Free core; paid addons | 👥 Red teams, exploit developers, pentesters | 🏆 Exploit development & validation |
| Nmap | Host discovery, port/service enumeration, NSE | ★★★★ Lightweight, scriptable | 💰 Free/open-source | 👥 Network assessors, internal/external scans | 🏆 Fast network discovery & enumeration |
| Nessus (Tenable) | Vulnerability scanning & compliance checks | ★★★★ Mature scanner with reporting | 💰 Commercial (per-instance licensing) | 👥 Compliance teams, IT ops, SMBs | 🏆 Compliance-focused vulnerability baselines |
| Kali Linux (Offensive Security) | Preloaded pentest toolset & images | ★★★★ Consistent pentest environment | 💰 Free distro (paid training optional) | 👥 Consultants, red teams, learners | 🏆 Turnkey pentesting workstation |
| OWASP ZAP (Zed Attack Proxy) | Free DAST + proxy with CI integration | ★★★★ Good for automated CI/CD testing | 💰 Free/open-source | 👥 Developers, security teams on a budget | 🏆 Cost-effective web scanning for pipelines |
| Wireshark | Packet capture & deep protocol analysis | ★★★★ Essential for traffic forensics | 💰 Free/open-source | 👥 Network engineers, IR, testers | 🏆 Protocol-level traffic investigation |
| Cobalt Strike (Fortra) | Adversary simulation, Beacon C2 | ★★★★ Powerful but high-risk if misused | 💰 Premium, vetted licensing | 👥 Mature red teams, advanced operators | 🏆 Realistic red-team tradecraft |
| Core Impact (Fortra) | Guided exploitation, reporting & modules | ★★★★ Structured workflows for testers | 💰 Quote-based commercial | 👥 Enterprise testers, audit-focused teams | 🏆 Repeatable, audit-ready penetration testing |
| Acunetix (Invicti) | DAST + API scanning, CI/CD integrations | ★★★★ Scales across many apps | 💰 Commercial / quote-based | 👥 App owners, remediation teams | 🏆 Scalable web & API scanning for teams |
| Greenbone / OpenVAS | Vulnerability scanning engine (CE & enterprise) | ★★★★ (CE) solid community tooling | 💰 Free CE; paid enterprise support | 👥 SMBs, ops teams on budget | 🏆 No-cost entry for credentialed scans |
| Nuclei (ProjectDiscovery) | Template-driven fast scanning (YAML templates) | ★★★★ Extremely fast, customizable | 💰 Free OSS; optional Pro/cloud | 👥 Engineering-heavy teams, automation | 🏆 High-speed, template-based detections |
Why Tools Alone Are Not Enough for a Pen Test
We’ve covered a lot of powerful intrusion testing tools, but no single tool is a magic bullet. A real security assessment is more than just running a scanner. Automated tools are great at finding known problems, but they lack the creativity and intuition of a human expert.
A certified penetration tester can chain together small risks to create a big problem. They find flaws in your business logic that a scanner would never understand. This human element is what separates a basic scan from a true pen test that gives you real value and protects your business.
Manual Pentesting for Speed and Affordability
Many businesses know they need a high-quality penetration test but get stuck. Traditional firms are often slow, expensive, and deliver reports filled with low-impact findings. This process is frustrating and doesn't work for fast-moving companies like yours.
We believe security testing should be fast, affordable, and accessible. We combine the best intrusion testing tools with certified OSCP, CEH, and CREST professionals. Our approach allows us to deliver a comprehensive, actionable report in about a week, not months, at a price that makes sense.
Ready to see how a fast, affordable, and expert-led manual pentest can help? Affordable Pentesting combines top tools with certified ethical hackers to deliver high-quality reports in about a week. Visit us at Affordable Pentesting and fill out our contact form to get started.
.svg)