ISO 27001 certification cost for a small startup usually lands between $43,450 and $78,333 in the first year. If you want to stay near the lower end, you need to control scope, cut internal busywork, and use security testing to catch problems before the auditor does.
A lot of teams start this process thinking the audit is the big bill. It isn't. The audit matters, but the bulk of the cost disappears into prep work, staff time, tool decisions, and rework after weak controls get exposed late.
That’s why smart teams treat iso 27001 certification cost as a budgeting problem, not just a compliance problem. If you make the right moves early, you don't just spend less. You get certified faster, with fewer painful surprises.
Deconstructing Your ISO 27001 Certification Cost
ISO 27001 isn't something you buy off a shelf. It's a management system you build. That system is your ISMS, which is just a structured way to decide what information matters, what can go wrong, and how your company will protect it every day.
Consider home security as an example. Buying one camera is simple. Building locks, alarms, access rules, motion sensors, and response procedures for the whole house is different. ISO 27001 is the second one.

What you are actually paying for
Most companies pay for four things:
- Audit fees: The certification body reviews your documents and then checks whether your controls work.
- Internal labor: Your team writes policies, maps assets, runs risk assessments, collects evidence, and fixes gaps.
- Outside help: Consultants, internal audit support, and technical testing can all show up here.
- Tools and maintenance: Compliance platforms, logging tools, and training usually become part of the budget.
The first mistake SMBs make is asking, "What does the certificate cost?" The better question is, "Which parts of this project can I control?"
Practical rule: You usually can't avoid audit fees. You can absolutely avoid bloated prep work, vague consulting scopes, and expensive rework.
Why the total swings so much
The price moves because your scope moves. A small, focused ISMS covering a web app, cloud infrastructure, and a tight team costs less to prepare than a sprawling scope that includes every department, every vendor, and every legacy process.
Your maturity also matters. If you already have decent access control, logging, vendor review, and incident response habits, you're not building from zero. If your team is still tracking security in spreadsheets and Slack messages, the cost goes up fast.
If you're still trying to get your bearings, this primer can help you understand ISO 27001 for SMEs without drowning in jargon. If you want a practical view of the process from a testing and compliance angle, this expert ISO 27001 guidance is also useful.
The parts you can influence
You can usually bring costs down by doing three things well:
- Keep the initial scope tight. Certify what matters to customers and revenue first.
- Use tools where they remove manual evidence gathering. Don't make your team act like a compliance data-entry department.
- Test controls before the audit. A good penetration test, pen test, or penetration testing engagement gives you proof that parts of your security program function effectively.
That last point matters more than is often acknowledged. Auditors don't like wishful thinking. They like evidence.
Calculating Your Audit and Certification Body Fees
A founder gets a certification quote, sees a number that looks tolerable, and assumes the hard part is under control. Then the certification body adds audit days, follow-up review time, and extra scrutiny because the scope is bloated and the evidence is messy. That is how a reasonable audit fee turns into an avoidable bill.
Audit and certification body fees are the most visible part of iso 27001 certification cost. They cover Stage 1 and Stage 2. Stage 1 checks whether your ISMS documents exist, fit the scope, and reflect how the business operates in practice. Stage 2 checks whether your team is following those controls in practice.
What the auditor is actually charging for
The certification body is pricing time. More sites, more people, more systems, and more complexity usually mean more audit days. If your evidence is disorganized, you also pay for the auditor to wait, chase clarifications, and review corrections.
Hightable's cost analysis notes that audit costs are only one part of the first-year spend, and that preparation often outweighs the audit invoice itself. That point matters because companies fixate on the auditor's quote and ignore the cheaper way to control it. Show up cleaner, and the audit usually stays smaller.
A lot of SMBs make the same mistake. They try to impress the auditor with a wide scope before they are ready. That does not make you look mature. It makes the audit longer and increases the odds of findings.
What makes the fee go up
Certification bodies do not guess. They calculate effort based on how much they have to review and how hard your environment is to verify.
Fees usually rise when you have:
- A broad certification scope: More departments, assets, and processes create more audit work
- Higher headcount: More users usually means more samples, interviews, and access reviews
- Complex infrastructure: Multi-cloud environments, custom applications, and regulated data flows take longer to assess
- Weak audit readiness: Incomplete policies, unclear ownership, and missing evidence create delays and follow-up work
The last point is where smart teams save money.
If you run a focused penetration test before Stage 2, you can validate technical controls early, fix obvious weaknesses, and organize stronger evidence for the auditor. That does three useful things at once. It reduces rework, supports multiple ISO 27001 control areas, and lowers the risk that the audit turns into a long remediation cycle. Cheap testing is expensive when it produces noise. Affordable penetration testing with a clear scope is different. It cuts wasted effort and keeps the certification body from spending billable time discovering problems you should have found first.
How to keep mandatory fees under control
You cannot eliminate audit fees. You can stop inflating them.
| Decision | Cost effect | Practical advice |
|---|---|---|
| Keep the initial scope narrow | Reduces audit days | Certify the systems tied to revenue, customer commitments, or the sales process first |
| Clean up evidence before Stage 1 | Cuts back-and-forth | Put policies, risk records, asset lists, and control evidence in one place and make sure they match reality |
| Use pre-audit penetration testing strategically | Reduces findings and follow-up | Test exposed systems and key control areas before the auditor does, then fix what matters |
| Resolve obvious gaps early | Avoids extra review time | Close known issues before the certification body has to document them |
The cheapest audit is the one that stays boring. Auditors like clear scope, clean records, and proof that controls work. Give them that, and you keep the bill under control.
The Hidden Internal Effort and Labor Costs
This is the part most companies miss, and it’s usually the part that hurts the most. DIY feels cheap because nobody sends you a big invoice for your own team's time. But your payroll is still real money.
When an IT manager, security lead, or senior analyst gets dragged into ISO work for months, that time isn't free. It’s budget. It’s delayed projects. It’s burned-out staff.

DIY is often the expensive option
The readiness stage alone can cost $24,583 to $39,333 in internal time from a single senior analyst, often making DIY the most expensive option in reality even when it looks free on paper, according to OneTrust's review of ISO 27001 costs.
That should reset your thinking. If one person is carrying policy work, risk reviews, evidence collection, meeting coordination, and control mapping, you've already spent a lot before the external auditor even shows up.
Where the hours actually go
Internal hours disappear into boring but necessary work:
- Policy drafting: Access control, incident response, vendor management, acceptable use, and more
- Asset and risk mapping: Figuring out what systems matter and what could go wrong
- Evidence gathering: Pulling screenshots, approvals, logs, training records, and review notes
- Control remediation: Fixing what the gap assessment exposes
- Audit support: Answering auditor questions and finding supporting records
None of this is glamorous. Most of it gets dumped on people who already have full-time jobs.
Teams don't fail ISO because the standard is impossible. They fail because they underestimate the amount of human effort required to prove they are doing the work.
What to do instead
You don't need to outsource everything. You do need to stop treating your internal team like free labor.
A better approach looks like this:
- Assign one owner: Someone has to drive decisions, but they shouldn't write and chase every artifact alone.
- Use specialists for specialist work: Don't make internal generalists fake expertise in auditing or technical validation.
- Protect engineering time: Engineers should fix meaningful gaps, not spend weeks formatting evidence.
- Set hard boundaries on scope creep: Every extra system and exception creates more internal drag.
If your team is already stretched, forcing a DIY compliance build usually costs more than it saves. It just hides the spending inside salaries and missed priorities.
Smart Spending on Consultants and Penetration Testing
You hire a consultant to help with ISO 27001. Three months later, you have polished policies, recurring status calls, and a growing invoice. Then someone asks a simple question. Have your controls actually been tested? That is where a lot of SMBs realize they bought paperwork before proof.
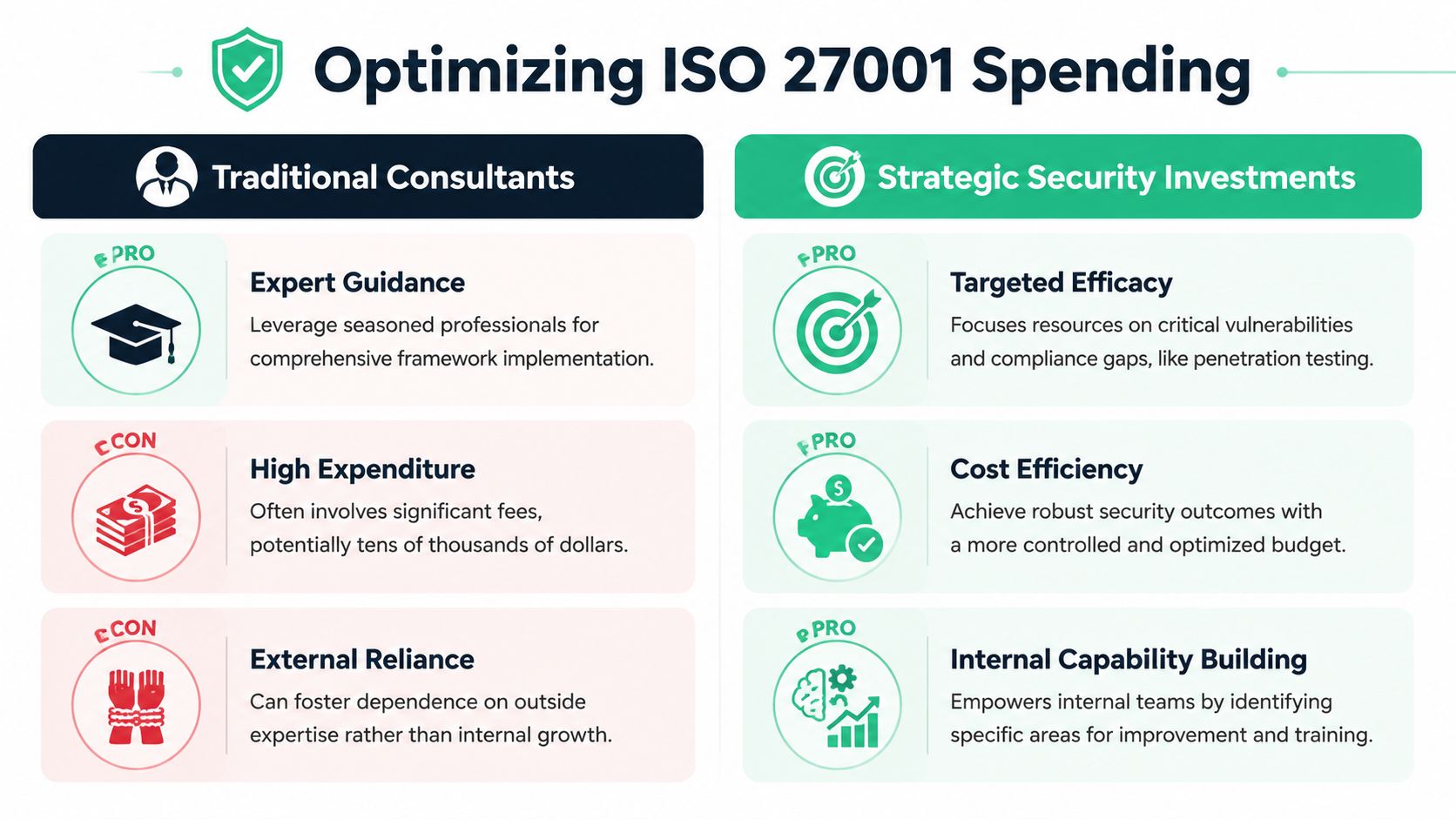
If you want to control ISO 27001 certification cost, spend less on generic advisory time and more on targeted technical validation. A good penetration test does more than find bugs. It gives you evidence for the audit, narrows remediation to real problems, and keeps the project from stalling on avoidable failures.
Why penetration testing is one of the best cost controls in the project
Consultants are useful when they close a specific gap. They are expensive when they stretch basic work into a long engagement. Penetration testing usually has a clearer return because it helps you answer several auditor questions at once.
A well-scoped test can support your risk treatment decisions, show that security weaknesses are identified and acted on, and give auditors something stronger than policy language. That matters because ISO 27001 rewards evidence. Auditors want to see that controls operate in practice, not just that they exist in a document set.
That is also why pentesting often cuts total cost instead of adding to it. You find issues before the certification audit. You avoid rework on controls that looked fine on paper but fail under testing. Your engineers fix confirmed problems instead of chasing generic consultant recommendations.
Where companies waste money
The usual mistake is obvious. They buy strategy before they buy validation.
Here is the spending split I recommend:
| Spend type | Usually worth it | Usually wasteful |
|---|---|---|
| Focused gap review tied to ISO scope | Yes | |
| Manual penetration test on in-scope systems | Yes | |
| Remediation guidance that maps to real findings | Yes | |
| Weekly consultant calls with vague action items | Yes | |
| Generic policy bundles with light editing | Yes | |
| Expensive testing with delayed reporting | Yes |
The best spend produces proof your auditor can review and your team can act on. The worst spend produces admin overhead.
What a good test changes
A strong penetration test earns its place in the budget because it improves several parts of the project at once:
- It finds real weaknesses early: You fix exploitable issues before they become audit findings or customer concerns.
- It creates usable evidence: A report shows that technical controls were tested and reviewed.
- It sharpens remediation: Engineers spend time on confirmed risks, not checklist theater.
- It supports multiple workstreams: The same findings and remediation records can help with customer due diligence and other compliance requests.
That makes pentesting a cost-reduction tool, not a side purchase.
Speed and scope matter
Cheap testing is not always affordable. If the provider relies on scanners, hands you vague findings, or takes weeks to deliver the report, your ISO timeline slips and internal costs rise. The invoice may look small. The delay is what gets expensive.
Ask direct questions. Is the test manual? What systems are in scope? How fast do you get a report? Will the findings include reproduction steps and remediation advice your engineers can use immediately?
If your audit scope includes customer-facing apps, APIs, or cloud infrastructure, keep the engagement tight and relevant to those systems. This article on Server Scheduler for cloud risk management is a useful reference for framing cloud risk, and this guide to fast and affordable SaaS security is a practical benchmark for teams that need useful testing without enterprise consulting prices.
What to look for in a provider
Do not overcomplicate vendor selection. Look for a firm that offers:
- Manual testing: Not just automated scans and exported screenshots
- Qualified testers: Certifications help, but the report quality matters more
- Fast turnaround: You need findings while remediation can still stay on schedule
- Clear reporting: Engineers should know exactly what to fix
- Reasonable pricing: ISO 27001 already has enough cost centers
My advice is simple. Buy consulting in narrow doses. Buy penetration testing that produces evidence, confirms risk, and helps close controls faster. That is how SMBs keep ISO 27001 certification cost under control without cutting corners.
Budgeting for Essential Tools and Staff Training
A lot of teams try to muscle through ISO with spreadsheets, shared folders, and a mess of screenshots. That works right up until someone asks for evidence, version history, ownership, or proof that a review happened. Then the whole thing becomes a scavenger hunt.
Tools aren't the whole answer, but good tools stop your team from doing compliance admin by hand. That’s a real cost saver.

Manual tracking versus automation
SaaS automation platforms can cut total ISO 27001 costs by 40% over three years, reaching $50K vs. $85K manual, and startups using these tools can get certified 3 to 6 months faster with a typical year-one cost of around $18,000, including software and audit, according to Sprinto's ISO 27001 certification cost review.
That doesn't mean every company should buy software on day one. It means you should compare subscription cost against internal drag. If your team is spending endless hours collecting evidence manually, automation is usually the cheaper route.
What tools are worth considering
Different teams need different stacks, but these categories usually matter:
- Compliance automation platforms: Useful for policy tracking, evidence collection, and control mapping
- Logging and monitoring: Tools like ELK stack can help you support event visibility without buying a massive enterprise platform
- Password and access management: Auditors expect you to show control, not improvisation
- Training systems: You need a repeatable way to show staff awareness and participation
Training doesn't need to be fancy. It needs to be documented, understandable, and repeated. If you need a plain-language starting point, GoSafe's guide to security training is a solid reference for structuring awareness work without overengineering it.
Spend where labor drops
A simple rule works here. Buy tools when they remove repetitive work from your team. Skip tools when they just create another dashboard nobody maintains.
Good tooling helps with:
- Collecting evidence automatically
- Assigning ownership clearly
- Keeping policy versions organized
- Making audit prep less chaotic
Bad tooling creates more admin than it removes. If a platform needs constant babysitting, it's not saving you money. It's just relocating the pain.
Planning for Surveillance Audits and Ongoing Maintenance
A lot of companies treat certification like a finish line. It isn't. ISO 27001 is a system you maintain, and the maintenance budget is where bad planning shows up later.
Once you're certified, you still have to keep the ISMS active, respond to findings, and go through surveillance audits. If your controls drift, the cost goes up and the audit gets uglier.
What ongoing maintenance really costs
Ongoing ISO 27001 maintenance for a mid-sized firm costs $10,000 to $25,000 annually, including surveillance audits of $5,000 to $15,000 and internal work, according to Thoropass on ISO 27001 maintenance costs.
Those costs surprise companies because they assume year one was the expensive part and the rest is minor upkeep. In reality, ongoing work is manageable only if you maintain discipline. If you let evidence go stale, skip reviews, or ignore technical weaknesses, your maintenance bill stops being predictable.
How to keep maintenance near the low end
The same habits that help you get certified also help you stay certified:
- Keep evidence current: Don’t wait until audit season to prove work happened.
- Run internal checks regularly: Small reviews beat big surprises.
- Fix issues while they're small: Minor gaps are cheaper than audit findings.
- Retest important systems: A recurring pen test or penetration test gives you current proof that controls still hold.
Thoropass also notes that integrating affordable, bi-annual pentesting can preempt 25% of audit findings, which is exactly why I treat penetration testing as maintenance, not a one-time project.
Certification is easier to keep when your team treats security evidence like ongoing hygiene instead of annual homework.
What the three-year cycle means in practice
You need to budget with a multi-year mindset. That means planning for annual surveillance activity and knowing that recertification will come around again. If you only fund the initial push, the program weakens fast.
A sensible maintenance rhythm usually includes:
| Activity | Why it matters |
|---|---|
| Internal audit work | Finds drift before the certification body does |
| Policy and risk reviews | Shows your ISMS is alive, not frozen |
| Regular penetration testing | Validates technical controls over time |
| Surveillance audit prep | Keeps external reviews routine instead of disruptive |
If you're mapping the bigger process from certification through maintenance, Affordable Pentesting's ISO 27001 guide gives a practical overview.
The main budgeting mistake is simple. Teams fund the certificate, then underfund the system behind it. That guarantees stress later.
If you want stable costs, keep your scope realistic, your evidence current, and your technical testing consistent. That’s how you stop surveillance audits from turning into emergency projects.
If you need a pen test, penetration test, or penetration testing partner that won't drag out timelines or charge like a giant enterprise consultancy, Affordable Pentesting is built for that. Their certified pentesters, including OSCP, CEH, and CREST professionals, deliver affordable manual testing with reports in about a week, which makes them a practical fit for SMBs trying to control iso 27001 certification cost without sacrificing real security.
.svg)
