Policy as Code (PaC) means turning your security and compliance rules into code. Instead of hoping a person manually checks everything, you build automated guardrails that enforce policies 24/7. This stops common but expensive mistakes before they become a real problem.
What Is Policy As Code Explained Simply

Think of a simple rule: "All new cloud storage must be private." The old way required someone to remember to check this every time. For a fast startup, that manual process is slow and full of human error.
Policy as Code flips this around. That rule becomes a script. Now, when a developer tries to create a new storage bucket, the script runs automatically. If the bucket is public, the action is blocked, and the developer gets an instant alert. It's like having a security expert built into your workflow.
This is a huge part of modern cloud security and works with Infrastructure as Code (IaC). As more companies define their infrastructure in code, they need a way to govern it with code too.
Move From Manual Policies To Automated Guardrails
Let's look at the difference between the old way and the modern approach with Policy as Code. The shift is all about moving from slow, error-prone manual checks to fast, consistent enforcement. For any startup that needs to move quickly without sacrificing security, Policy as Code is essential.
Why Policy As Code Matters For Compliance
For startups facing compliance like SOC 2 or HIPAA, PaC is a game-changer. Manual compliance management is a huge drain on time and money. Policy as Code automates a huge piece of the puzzle, helping you build a secure and compliant company from day one.
The real win is catching issues early. Fixing a security mistake before it goes live is cheap and easy. Finding it after a data breach or during a failed audit is a total nightmare.
This proactive approach perfectly complements a manual penetration test. While our OSCP and CEH-certified team uncovers complex flaws that automated rules miss, Policy as Code helps you codify the fixes. We deliver our pentest reports in under a week, giving you the fast findings you need to build better policies.
How PaC Helps You Catch Problems Early
The magic of Policy as Code is how it plugs directly into your development pipeline. This is called “shifting left” and it’s a simple idea: find and fix problems at the beginning. It's like spell-checking a document as you write it, not after you send it to the printer.
Let's say a developer writes code to spin up a new server. Before that code can touch your production environment, your PaC tool automatically scans it. It can instantly catch critical mistakes like a database that isn't encrypted or a server accidentally exposed to the public internet.
The developer gets instant feedback and can fix the issue in minutes. Without PaC, that same mistake could sit there for months, waiting to be found by an attacker. Policy as Code sets a programmatic new standard in compliance risk management software, forcing security to be proactive, not reactive.
Go From Manual Guesswork to Automated Confidence
Let's be honest: the old way of enforcing security policies is broken. Relying on people to manually check everything is a recipe for failure. With Policy as Code, you embed those rules into your CI/CD pipeline.
In industries like healthcare, where a HIPAA breach can cost millions, this automated approach shrinks your risk. You're not just hoping you're secure; you're proving it with every code commit. This gives leaders real confidence that security is being built in from the start.
This strategy gets even more powerful when you pair it with a professional pentest. Our affordable penetration testing services find the complex vulnerabilities automated tools miss. Our OSCP, CEH, and CREST certified pentesters deliver your report in under a week, so you can turn findings into new policies and lock down security gaps for good.
Key Benefits For Fast Growing Startups
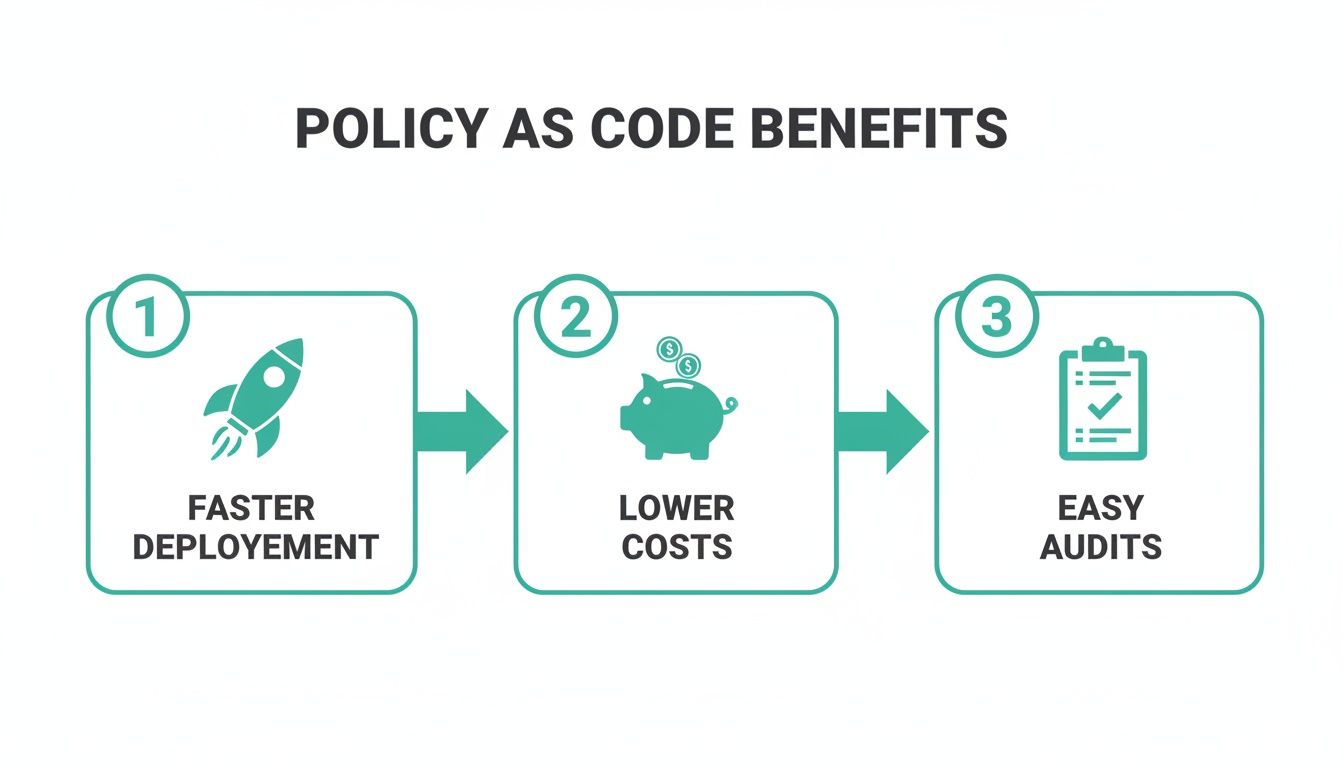
Adopting Policy as Code (PaC) isn't just about ticking a compliance box. For a fast-moving startup, it’s about survival. The real wins are speed, cost savings, and scalability. When your security rules are automated, your developers can ship code faster without getting stuck waiting for a slow, manual security review.
This is a game-changer for growing teams. Instead of pulling your best engineers off product development to do repetitive checks, you let the code do the policing. That frees up your senior talent to build features that matter.
How To Integrate Policy As Code
So you’re sold on the concept, but how do you actually make Policy as Code work? The good news is that PaC bolts directly onto your development pipeline, especially if you're already using Infrastructure as Code (IaC).
Think of it this way: Your IaC tools, like Terraform, are the blueprints for building your cloud infrastructure. PaC engines, like Open Policy Agent (OPA), act as the automated city inspector. This catches costly mistakes before they happen, not after.
The whole process plugs right into your CI/CD pipeline, making security feel like a helpful teammate. It creates a tight feedback loop that developers actually appreciate. This kind of integration delivers faster deployments, lower costs, and almost painless audits.
Choosing Your Policy Engine And Tools
The most common open-source policy engine is Open Policy Agent (OPA). It has quickly become the go-to standard for enforcing policies in modern, cloud-native environments. To get the most out of PaC, it's worth exploring the different cloud infrastructure automation tools available to see how they fit together.
The real power of PaC is turning dense compliance requirements into simple, enforceable code. Instead of hoping your team follows a 100-page document for SOC 2, you have a script that automatically checks for compliance every time. You can check out our guide on the best compliance management software to see how these systems can work together.
Your First Steps With Policy As Code
Jumping into Policy as Code doesn't have to be a huge project. You don't need to rewrite your entire security program on day one. Let's walk through simple, high-impact rules that actually matter for startups.
The best advice is to start small. Pick one or two major security controls, write them as simple code, and run them in 'audit' mode. This lets you spot violations without blocking your team's work.
Start With Common Cloud Security Risks
For a startup, the biggest threats often come from simple, preventable mistakes. Your first policies should go after this low-hanging fruit. We're talking about the kinds of slip-ups that lead to expensive data breaches but are easy to stop with an automated rule.
Here are a few high-impact policies you can start with today. These rules are straightforward to write and fix the exact kind of findings our certified pentesters find during a penetration test. This helps you build a much stronger foundation from the start.
From Audit Mode to Full Enforcement
Once you have your first policies written, the trick is to roll them out without wrecking productivity. Running your policies in audit mode is the perfect way to do this. The policy engine just flags violations without stopping the deployment.
This gives your team visibility into where the issues are without creating a bottleneck. Once everyone gets used to the new rules, you can flip the switch to enforcement mode, where violations will block a deployment. This proactive approach complements the findings from a manual penetration test. A pen test from our OSCP and CEH-certified team uncovers hidden flaws, while Policy as Code lets you codify the fixes so those vulnerabilities never happen again.
Our affordable pen test services help you find the gaps, and Policy as Code helps you close them for good. Get in touch through our contact form to learn how we can help.
Combine PaC With Manual Penetration Testing

Policy as Code is great for stopping known bad configurations, but it can’t find every vulnerability. Automated policies are fantastic at catching common mistakes, but they don’t think like a creative attacker. This is where a manual penetration test becomes the perfect partner to your PaC strategy.
A professional pentest simulates a real-world attack to uncover the complex flaws automated tools will always miss. For startups, this combination is how you build a truly strong defense without the outrageous cost and slow timelines of traditional security firms.
Why You Need Both PaC And A Pentest
Think of it like this: Policy as Code is your automated security guard, checking IDs and locking doors. A penetration test is an expert trying to find a clever way to sneak past that guard or climb through an open window you didn't know you had. You need both.
Our pentesters are experts with certifications like OSCP, CEH, and CREST. They go beyond simple scanning to find real-world risks that could damage your business. We deliver our penetration test reports in under a week, giving you the fast insights you need to improve your defenses.
Turning Pentest Findings Into New Code
Here’s how it works. Our team performs a thorough pen testing engagement and gives you a clear, no-fluff report. You then use those findings to write new policies. For example, our pentest might find a way to chain together several low-risk flaws to gain admin access.
You can then write a new, specific policy to block that exact attack path. This turns your penetration testing investment into a long-term asset. Instead of just a one-time fix, you're improving your automated defenses for the long haul. Learn more about setting up a robust penetration testing program.
Is Policy As Code Hard To Learn?
The word “code” can sound intimidating, but you don’t need to be a senior developer. Many policy engines use simple languages that are easier to learn than Python or Go. The trick is to start small with one or two high-impact rules to build momentum.
What Policy As Code Tools Should I Use?
The open-source leader is Open Policy Agent (OPA). It’s flexible and works across your entire stack, from Kubernetes to your Terraform plans. But OPA isn't the only option; the best choice depends on your team's skills and where you need to enforce rules.
Can Policy as Code Replace a Pentest?
No, and it's dangerous to think it can. Policy as Code is fantastic at enforcing known rules and catching common mistakes. But it can't find complex business logic flaws or the creative attack paths a skilled human hacker would exploit.
Think about it this way. Policy as Code is your system that ensures doors and windows are locked. An affordable pentest is when a certified expert checks if those locks can be picked. They work together perfectly. Our affordable penetration testing services, conducted by OSCP and CEH certified professionals, find those hidden vulnerabilities. You then use Policy as Code to ensure that specific issue can never happen again.
At Affordable Pentesting, we deliver fast, actionable pentest reports in under a week, giving you the insights to build better policies without the high costs of traditional firms. Secure your startup and prove your compliance with a practical, affordable approach. Learn more at https://www.affordablepentesting.com.
.svg)
