Your login page is probably throwing off more failed sign-in alerts than it used to. Support tickets are creeping up. Your team is seeing weird lockouts, but nobody can tell if it's a real attack or just users forgetting passwords again.
A lot of the time, that noise has a name. It's credential stuffing.
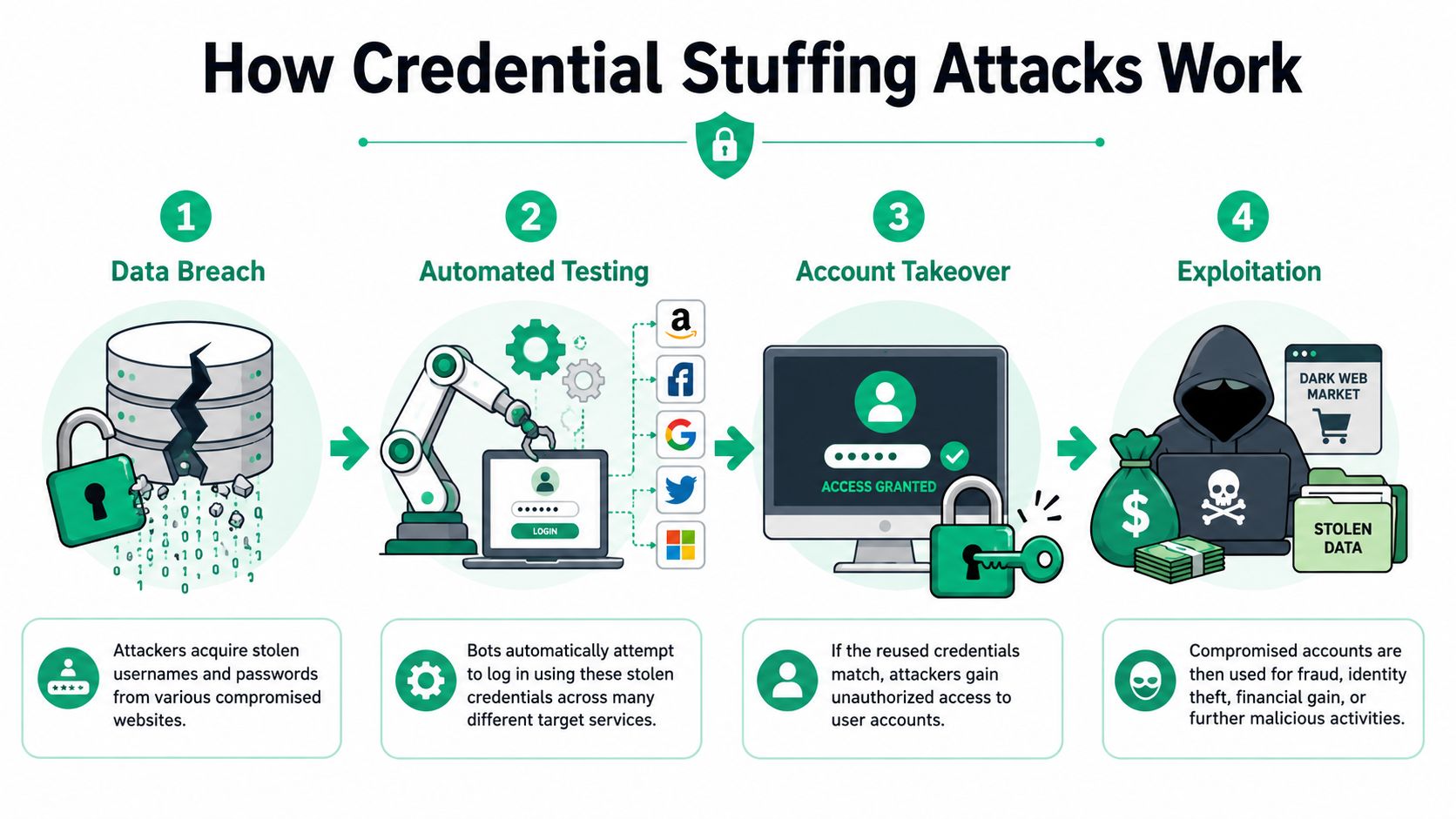
If you're asking what is credential stuffing attack, the plain-English answer is simple. Attackers take usernames and passwords stolen from some other breach, then use bots to try those same logins against your app, portal, VPN, or admin page. They bet that your users reused a password somewhere. Too often, they're right.
Why Your Login Page Is Suddenly So Busy
Credential stuffing isn't some fringe issue anymore. It has become the top initial access vector for enterprise breaches, accounting for 22% of confirmed data breaches in 2025 according to Verizon's DBIR research on credential stuffing attacks.
That matters even if you're not a giant enterprise. Startups, SaaS companies, clinics, fintech shops, and ecommerce teams all expose the same basic thing to the internet. A login form. If you have users, you have a target.
What the attack really is
This isn't brute force in the old-school sense where somebody guesses password after password for one account. Credential stuffing is different. The attacker already has a giant pile of stolen username and password pairs from breaches elsewhere, and they test them against your systems.
A thief steals a bucket of keys from other buildings, then walks down your hallway trying each key once on each door. If one works, they get in without kicking anything down.
Practical rule: If you see steady failed logins spread across many accounts, don't assume it's harmless background noise.
Why founders and IT teams miss it
Many organizations focus on product uptime, customer onboarding, and audit prep. Login noise gets pushed into the "we'll tune alerts later" pile. That's a mistake.
Credential stuffing often looks boring until it turns into account takeover, fraud, or an auditor asking whether your controls around authentication have been tested. If you're preparing for SOC 2, HIPAA, or PCI DSS, your answer can't be "we turned on a plugin and hoped for the best."
A fast way to validate your real exposure is to scope affordable external pentesting against the systems attackers first touch. That's the internet-facing reality, not the polished diagram in your compliance folder.
How Credential Stuffing Attacks Actually Work
Attackers don't need a genius exploit for this. They need leaked credentials, cheap automation, and a login form that trusts passwords too much.
The four-step flow
Credentials get stolen somewhere else
Your company may have done nothing wrong at this stage. A user reuses the same password on another service, that service gets breached, and now the login pair is circulating in breach dumps or criminal forums.Bots test those logins against your app
The attacker points automated tools at your login page, SSO portal, VPN, or customer account area. They aren't trying random passwords. They're trying real username and password combinations that worked somewhere else.A reused password opens the door
If your user recycled credentials, the attacker gets valid access. No malware. No dramatic exploit chain. Just a successful login.They cash in
That account might be used for fraud, data theft, privilege escalation, or pivoting deeper into your environment.
Why attackers keep doing it
Because the math works.
According to credential stuffing data summarized here, former Google click fraud czar Shuman Ghosemajumder documented success rates of up to 2%, while other data shows about 0.1% of breached credentials can work on another service. At that scale, one million stolen credentials can lead to roughly 1,000 to 20,000 successful account takeovers.
That range is all an attacker needs. Even the low end can be profitable.
A startup founder hears "0.1%" and thinks that's tiny. An attacker hears it and sees a business model.
Why your current controls may not be enough
A lot of teams think rate limiting alone solves this. It doesn't. Modern attacks spread attempts across accounts, devices, IP addresses, and time windows so they don't look like the classic movie version of a bot storm.
If you want a useful technical explainer on the broader class of login issues, this deep dive into authentication security flaws is worth reading. It helps frame credential stuffing as one piece of a bigger broken-authentication problem, not an isolated oddity.
Why Attackers Love This Low-Cost Attack
Credential stuffing is attractive for the same reason spam is attractive. It's cheap, repeatable, and somebody always clicks.
Attackers don't need to burn time finding a rare zero-day when ordinary password reuse keeps paying out. They buy or trade stolen credentials, run automated checks, and sort the winners from the losers. That's not elite wizardry. That's efficient abuse of weak authentication habits.
Real money follows valid logins
The business impact gets obvious when the target holds money, health data, or anything tied to identity. In late March 2025, coordinated attacks hit five major Australian superannuation funds, compromising over 20,000 accounts and causing losses exceeding AUD 500,000 for some victims, according to Check Point's research on the surge in compromised credentials.
Retirement accounts were a strong target for a reason. High balances. Infrequent user logins. Historically inconsistent MFA enforcement. That's not unique to that sector either.
The attacker playbook is boring on purpose
This attack is dangerous. It doesn't need to be flashy.
- Low setup cost because the attacker can buy access to credential lists and automation tools without building much from scratch
- Broad target set because almost every business has a login page, partner portal, or admin panel
- Good downstream value because one compromised account can expose money, personal data, support workflows, or internal access
- Blame confusion because your team may argue over whether the root cause was your app, the user's password habits, or a third-party breach
That confusion is exactly why many SMBs underinvest in testing login defenses. They treat account takeover like a user problem instead of a business problem. Auditors won't see it that way.
If your revenue, customer data, or regulated workflows sit behind a password, credential stuffing is your problem.
Key Signs Your Business Is Under Attack
You usually won't get a giant flashing warning that says credential stuffing. What you get is a messy pile of symptoms.
Modern attacks are built to look normal enough that your team shrugs and moves on. According to this explanation of credential stuffing evasion techniques, attackers often modify HTTP headers and limit attempts to a single submission per account so they blend into ordinary traffic. That matters because credential stuffing still accounts for 19% of all authentication attempts in the median organization.

What to watch in your logs
Start with patterns, not single events.
Failed logins across many accounts
One user failing to log in isn't interesting. Many users failing in a similar window is.Lockouts that don't fit user behavior
If support starts hearing "my account got locked and I wasn't even trying to sign in," pay attention.Logins from all over the place
A user appearing in one city and then another far away minutes later is suspicious. That's the plain-English version of impossible travel.Weirdly even distribution
Attackers often spread attempts thinly so one account doesn't get hammered enough to trigger simple lockout rules.
Why basic alerting misses it
A lot of login defenses were built for noisy brute-force attacks. Credential stuffing is quieter. The attacker may only try one stolen password per user, then move on.
That means you should look for combinations of weak signals instead of waiting for one giant red flag.
| Signal | What it usually means |
|---|---|
| Broad failed login spread | Automation testing many accounts |
| Sudden support complaints about lockouts | Users being hit individually |
| Mixed IP and device patterns | Distributed bot traffic |
| Valid logins followed by unusual account actions | Account takeover after a successful stuff |
Questions to ask your team today
- Can we tell which failed logins are clustered by username, IP, device, or time window
- Do we alert on successful logins that follow unusual failure patterns
- Can we separate customer mistakes from bot-driven abuse
- Do we review admin and staff portals differently from ordinary user accounts
If the answer is "not really," that's your starting point.
Practical Ways to Stop Credential Stuffing
You do not need a giant enterprise budget to make this attack much harder. You need the right order of operations.
Start with controls that actually change outcomes
MFA comes first. If an attacker has the right password but can't satisfy the second factor, the attack gets a lot less useful. If you only do one thing this week, enforce MFA on staff, admins, finance users, and any customer roles with sensitive access.
Then clean up password hygiene. Push users toward unique passwords and support password managers instead of pretending everyone will invent good passwords on their own.
Field advice: MFA is the fastest win against credential stuffing. Fancy bot tooling without MFA is backwards.
Build a layered defense
Attackers are getting stealthier. As Imperva's explanation of modern credential stuffing notes, they increasingly target high-value and niche platforms with smaller botnets that rotate IPs and user-agent strings, which makes basic IP blocking and simple bot detection weaker than many teams assume.
That means you need layers:
Adaptive rate limiting
Don't rely on a flat threshold. Tune it around behavior, account sensitivity, and repeated patterns.CAPTCHA in the right spots
Use it on suspicious flows, not everywhere. If you put friction on every user all the time, people work around it and support tickets climb.Device and behavior checks
Watch for abnormal login behavior, not just obvious bad IPs.Credential exposure monitoring
If user credentials show up in public dumps or code repositories, act fast. Waiting gives attackers free time.
Have a response plan before you need one
A lot of companies only think about response after customer accounts start getting hijacked. That's late. You need a playbook for resets, session invalidation, user notifications, and log review before the incident starts.
If your team wants a practical outside perspective on response planning, this guide to Canadian SMB incident response is a useful read. It keeps the discussion grounded in what smaller teams can execute.
Your app surface matters too. Login defenses fail all the time through connected services, mobile backends, and exposed endpoints. If you want a practical companion topic, learn how to protect your APIs from hacks, because attackers don't care whether the weak spot is the web form or the API behind it.
How Penetration Testing Finds These Flaws Fast
A lot of audit prep dies in a spreadsheet. Someone lists MFA, rate limiting, SSO, lockouts, and monitoring, then checks the box and moves on. That's not proof. That's paperwork.
A real penetration test, pen test, or penetration testing engagement answers a tougher question. Do those controls hold up when somebody attacks your login surface the way criminals do?
What a good pentest checks
A solid tester doesn't stop at "login page exists." They look at the full authentication path.
That includes:
- User login workflows across web apps, mobile APIs, admin panels, VPNs, and SSO portals
- Rate-limiting behavior to see whether controls trigger in useful ways or can be dodged
- MFA enforcement gaps such as optional flows, weak recovery paths, or admin exceptions
- Session handling issues that let an attacker keep access after login succeeds
- Account enumeration clues that tell attackers which users are valid
A manual tester also notices the dumb stuff automation misses. Different error messages. Weak password reset paths. Support workflows that can be abused. Admin portals hidden in plain sight.
Why manual testing matters for compliance
SOC 2, HIPAA, and PCI DSS aren't impressed by empty reports. You need evidence that your controls were assessed in a way that maps to real risk.
That's where certified testers matter. An OSCP, CEH, or CREST pentester knows how attackers chain weak controls together. They don't just run a scanner, export a PDF, and call it a day.
Here's the blunt truth. Traditional firms often move slowly, cost too much, and return thin findings because they over-automate the work and bury you in process. Startups and SMBs usually need the opposite. Clear scope, manual validation, and a report fast enough to help this quarter's audit.
A pen test should tell you where an attacker gets in, how far they get, and what to fix first. If it doesn't, you bought paperwork.
What to test first
If budget is tight, don't boil the ocean. Start with your highest-risk internet-facing assets, especially user logins, admin panels, SSO, and connected application endpoints.
For most SMBs, affordable web application pentesting is the right first move because that's where credential stuffing risk turns into account takeover and audit pain fastest.
Your Actionable Security Checklist For 2026
If you want the short version, here it is. Skip the theory and do the work.
The checklist that matters
Enforce MFA on every external account that matters
Start with admins, employees, finance users, and customer roles with sensitive data or transaction access.Review login telemetry weekly
Look for failed login spread, account lockouts, odd device patterns, and suspicious successful logins after failures.Tune rate limiting beyond basic IP blocks
Attackers rotate infrastructure. Your controls need to watch behavior, not just source addresses.Support unique passwords
Use password managers internally and encourage them for customers where practical.Harden password reset and account recovery
A strong login flow is pointless if support or recovery flows hand the account right back.Segment high-value portals
Admin panels, finance systems, clinical portals, and partner dashboards deserve stricter authentication and closer monitoring.Test your APIs and login-connected services
Attackers don't care which endpoint gives them access.Run a recurring penetration test
Not just when an auditor asks. Test after meaningful auth changes, product releases, or SSO updates.
What not to do
Don't trust a WAF alone. Don't assume low login volume means low risk. Don't wait for customers to report account takeover before you investigate.
Don't confuse "we bought a security tool" with "we verified the control works." Those are different things.
If your team needs a fast path to audit readiness, start with the internet-facing authentication surface and validate it with real testing. That's cheaper than explaining a preventable account takeover to customers, your board, and your auditor.
If you need a fast, affordable way to validate your login security before SOC 2, HIPAA, or PCI DSS deadlines hit, talk to Affordable Pentesting. Their certified pentesters, including OSCP, CEH, and CREST professionals, focus on practical manual testing, useful findings, and reports delivered within a week. Use the contact form, get a clear scope, and find the weak spots before an attacker or auditor does.
.svg)
