Your Active Directory controls everything. It decides who gets in, what they see, and what they can do on your network. An active directory tester is a professional you hire to find weaknesses in those controls before a real attacker does.
One wrong setting can give an attacker full control. This makes a deep Active Directory penetration test a business necessity, not just an IT task.
Why You Need An Active Directory Pen Test

If an attacker gets into your Active Directory, they own your entire network. This makes AD a huge target for attacks. That’s why you need a specialized pen test to keep it secure.
Automated scanners only find basic problems. A real penetration test is different. Our certified testers with OSCP, CEH, and CREST certifications act like real attackers to find the tricky issues that scanners always miss.
These are not small risks. Studies show attackers target Active Directory millions of times every day. That's why leaders are making proactive testing a priority. You can find out more about the increasing AD security investments companies are making.
Get Affordable Pentests Without The Wait
We know the pain of working with old-school pentesting firms. They charge high prices, move slowly, and deliver confusing reports that don't help. We do things differently.
As an IT manager, CISO, or founder, you need an affordable pen test that delivers real results, fast. That's exactly what we provide. Our expert-led, manual penetration testing gets you a clear report within a week.
Stay Compliant And Avoid Breach Fines
If you handle sensitive information, compliance is not optional. Rules like SOC 2, PCI DSS, and HIPAA require strong access control. A weak Active Directory is an easy way to fail an audit and face huge fines.
An Active Directory pen test shows auditors you are serious about security. Having a professional active directory tester check your systems proves you are doing your part. This makes audits smoother and prevents the high costs of a data breach.
How To Prepare For Your AD Pentest
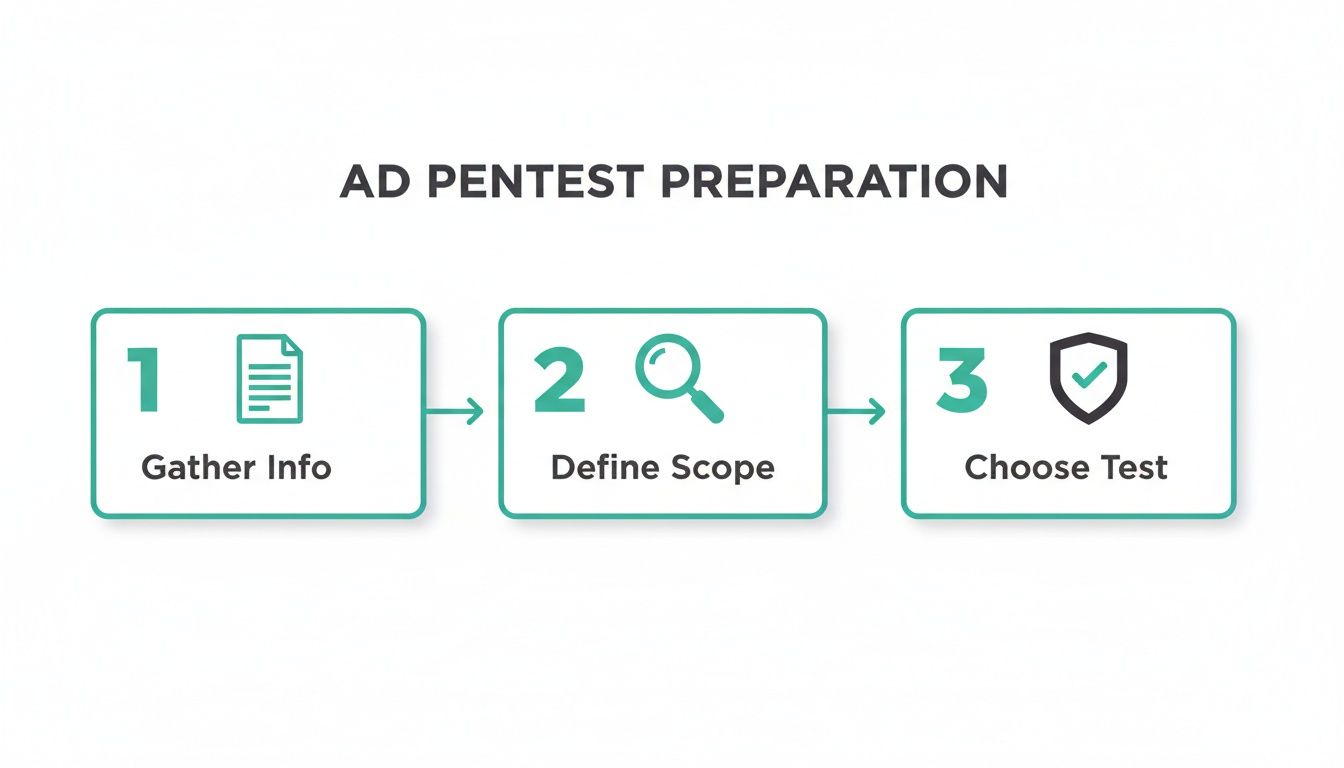
Good preparation leads to a fast and affordable pentest. When you give our team the right information, they work faster. This saves you money and gets you a report within a week.
Think of it like giving an explorer a map. Good prep helps our certified active directory tester find complex flaws instead of wasting time on basics. You can learn more with our guide on how to prepare for a successful pentest.
Gather Info And Define The Test Scope
First, decide what you want us to test. A clear scope keeps our OSCP, CEH, and CREST certified experts focused on your most important systems. This is the best way to control costs and get a useful report.
Start by collecting this information:
- A simple diagram of your network.
- A list of user roles and their permissions.
- Details about your Active Directory domains.
With this info, our team can start analyzing your setup right away. This is how you get a fast and insightful penetration test.
Choose Your Pentesting Test Approach
Next, choose the type of pen test you need. The two main options are a grey-box or black-box test. Your choice affects the speed and cost of the test.
A black-box penetration test is when we start with no information. This is like a real external attack, but it takes more time and money.
A grey-box penetration testing approach is usually better for Active Directory. We start with a normal user account and basic information. This is like an insider threat or an attacker who has already phished a user. It lets us find high-impact problems much faster.
Common Attack Paths An AD Tester Finds
An expert AD tester knows exactly where to find weak spots in your Active Directory. Our OSCP and CREST certified pentesters often find the same issues. These simple mistakes can give an attacker full control of your network.
These are not complex hacks. They are usually simple misconfigurations and bad permissions that create easy paths for attackers. Knowing these common problems helps you fix them for good.
Kerberos and NTLM Authentication Flaws
Let's talk about Kerberos and NTLM. These are the systems that check user logins on your network. Kerberos is like a secure ticket system. NTLM is older and much easier for an attacker to trick.
AD testers often find older NTLM systems still in use. This lets an attacker steal password information and crack it. A common attack is "pass-the-hash" where an attacker uses a stolen password file to log in without knowing the actual password.
Abusing Access Control Lists (ACLs)
Everything in Active Directory has an Access Control List, or ACL. An ACL is just a list of who can do what. Over time, these lists get messy and create security holes.
Our pentesters often find normal users with dangerous permissions they shouldn't have. For example, a user might be able to reset an admin's password. Scanners almost never find these problems. Many of these issues can appear even in systems using Role Based Access Control (RBAC).
A professional penetration test is the only way to find these hidden permission problems. This process is a key part of any internal network pentest.
Common Active Directory Vulnerabilities and Business Impact
| Vulnerability Type | Simple Explanation | Potential Business Impact |
|---|---|---|
| Kerberoasting | An attacker requests a service ticket for a user account with a weak password, then cracks it offline. | Gain initial access or escalate privileges, leading to data theft or further network compromise. |
| Weak Password Policies | Allowing simple or short passwords (e.g., "Spring2026!") that are easy for attackers to guess or crack. | Widespread account compromise, making it easy for attackers to move through the network undetected. |
| NTLMv1/LM Hashes | Using outdated and weak authentication protocols that can be cracked in seconds. | Attackers can easily impersonate users and gain access to sensitive systems and data. |
| ACL Misconfigurations | Granting excessive permissions to standard users, allowing them to modify critical groups or reset passwords. | A low-level user account can become a Domain Admin, leading to a full network takeover. |
| Unconstrained Delegation | A server is trusted to impersonate users to access any other service, a highly risky setting. | An attacker who compromises the server can steal credentials and impersonate any user, including admins. |
Exploitation And Post-Exploitation Tactics
Finding a problem is only the first step. The real work starts when we show you what an attacker could do with it. This is where our pentesters show you the actual business risk of a security weakness.
We don't cause damage. We show you the impact. We move from finding a flaw to showing how it can be used to take over accounts and access your company's private data. This turns a technical issue into a clear business problem.
Proving The Business Risk For You
What does a finding really mean for your business? A finding like "NTLMv1 is enabled" means nothing without context. Our job is to show you why it matters by acting like an attacker after they get in.
We answer the important business questions:
- Can a normal user become a powerful admin?
- How fast can an attacker spread across the network?
- Can they steal your customer data?
- Could this lead to a ransomware attack?
By showing you these attack paths, we turn confusing problems into real business risks. This helps you decide what to fix first based on what could hurt your business the most.
Simulating Real-World Attack Methods
Our OSCP, CEH, and CREST certified pentesters use the same methods as real attackers. For example, once we get in, we might use a "pass-the-hash" attack. This lets us act like another user without needing their password.
From there, we might find a way to change a Group Policy Object, or GPO. This is a huge win for an attacker. It lets us create a new admin account on every computer in the network. This step-by-step process shows you a clear attack chain your team can understand and fix.
From Findings To Fixes In Your Pentest Report
A pen test is useless if the report is confusing and months late. We deliver a clear, actionable report to you within one week of the test.
Our reports are written for everyone from the CISO to the IT admin. We rank every finding by business risk. We also give you exact instructions your team needs to start fixing things right away.
What To Expect In Your Pentest Report
We get straight to the point. Your report starts with a simple summary for leaders. It gives a clear view of the test results and the biggest risks we found.
Then, we dive into the details. Each finding has a risk score, a simple explanation, and proof of how our active directory tester used it. You will see the screenshots and commands that show the entire attack path. You can see a penetration testing report example to understand our approach.
Prioritizing Findings Based On Real Risk
Not all problems are equal. A critical issue can give an attacker full control of your network. We use a simple risk rating system to help you focus on what matters most.
- Critical: These are "fix now" problems that could lead to a huge data breach or ransomware.
- High: These are serious gaps that help an attacker move through your network.
- Medium: These are important security issues that weaken your defenses.
- Low: These are small issues that should be fixed to improve your overall security.
This clear ranking helps your team focus on fixing the problems that pose the biggest threat.
Clear Remediation Guidance Your Team Can Use
The fix-it plan is the most important part of the report. We don't just say "patch the server." Our certified OSCP, CEH, and CREST testers give you specific, step-by-step instructions.
You get the exact commands to run and settings to change. We take the guesswork out of fixing security problems. Your team can close gaps quickly and with confidence.
Mapping AD Pen Test Findings To Compliance
A pen test is often a key requirement for your compliance audit. An Active Directory pen test is a direct way to prove to auditors you are protecting your network. It connects a technical security finding to a specific compliance rule.
When an auditor for SOC 2, PCI DSS, or HIPAA asks about access control, you can give them our report. It shows you test your security and fix what you find. This makes your audit much easier. Check out these SOC 2 penetration testing requirements to learn more.
At Affordable Pentesting, we deliver fast, affordable, and actionable AD penetration testing that helps you meet your compliance goals. Get a comprehensive report within a week. Contact us through our form to learn more.
.svg)
