What is an application penetration test? Think of it like hiring a locksmith to check your digital doors for weaknesses before a real burglar tries to break in. It’s a simulated cyberattack on your software to find security flaws hackers could exploit.
This process is critical for protecting sensitive data. It's also a must-have for meeting compliance standards like SOC 2 and HIPAA.
What Is An Application Penetration Test?
Imagine your app is a fortress. A penetration test or pen test is how you check for forgotten tunnels or weak spots in the walls. It’s a controlled attack by certified ethical hackers who think like real adversaries.
Their job is simple: find security weaknesses before bad guys do. For IT managers, CISOs, and startup founders, this isn't just a tech checkup. It's a critical safeguard for your business and customer data.
Why Do I Need An Application Pentest?
A pen test finds vulnerabilities that automated scanners can't. Scanners spot common issues but don't understand context. They can't chain together small flaws to create a massive security breach.
That’s where our expert pentesters holding OSCP, CEH, and CREST certifications come in. They manually probe your application to find complex issues and answer critical questions. Can an attacker steal customer data? Is it possible to gain admin-level control?
Why Is This Security Process So Important?
For many businesses, a penetration test is not optional. It’s a hard requirement for compliance frameworks like SOC 2, HIPAA, and PCI DSS. A clean report from a pen test proves you are proactively managing security risks.
This proactive approach is more important than ever. The demand for application penetration testing is surging as threats grow. Proactive testing is just one of several critical security measures, so it is worth exploring other essential cyber security assessments as well.
Why Your Business Needs This Security Testing
Many people think a vulnerability scan is enough. That’s like having a security camera that only looks for known criminals. An application penetration test goes much deeper by simulating a real-world attack.
Automated scans find obvious issues. But a human pentester thinks creatively, uncovering complex business logic flaws that automated tools will always miss. For companies needing to meet compliance standards, manual penetration testing is non-negotiable.
Go Beyond Simple Automated Security Scans
Automated scanners just match patterns. They check your app against a big database of known security problems. It’s a useful first step, but it's not a complete security check.
A manual pen test is a different game entirely. It’s run by a certified expert who thinks like an attacker to find unique vulnerabilities. Our pentesters hold certifications like OSCP, CEH, and CREST.
Protect Your Customer Data and Build Trust
A security breach isn't just a technical problem. It's a business disaster that can cause massive financial and legal penalties. Proper application penetration testing is one of the most effective ways to stop that from happening.
By proactively finding and fixing weaknesses, you protect customer data. You also prevent costly breaches and maintain compliance. It lets you operate with confidence, knowing your defenses have been battle-tested.
How Proactive Pentesting Makes Financial Sense
Investing in a proper penetration test is a smart financial move. The cost of a security breach is much higher than the expense of a proactive test. Waiting for an attack to happen is a gamble most businesses can't afford.
Our whole model is built to make this essential service accessible. We provide affordable manual pentests with quick turnarounds. You get a comprehensive report in your hands within a week. You can discover insights on pentesting statistics to learn more about industry trends.
The Simple Step-By-Step Penetration Testing Process
What happens during a penetration test? The old-school model is slow and complicated. We make it simple and fast, with your report ready in about a week.
Our high-quality application penetration test breaks down into three core stages. Each step is clear and straightforward. This lets our certified pentesters work effectively while you stay focused on your business.
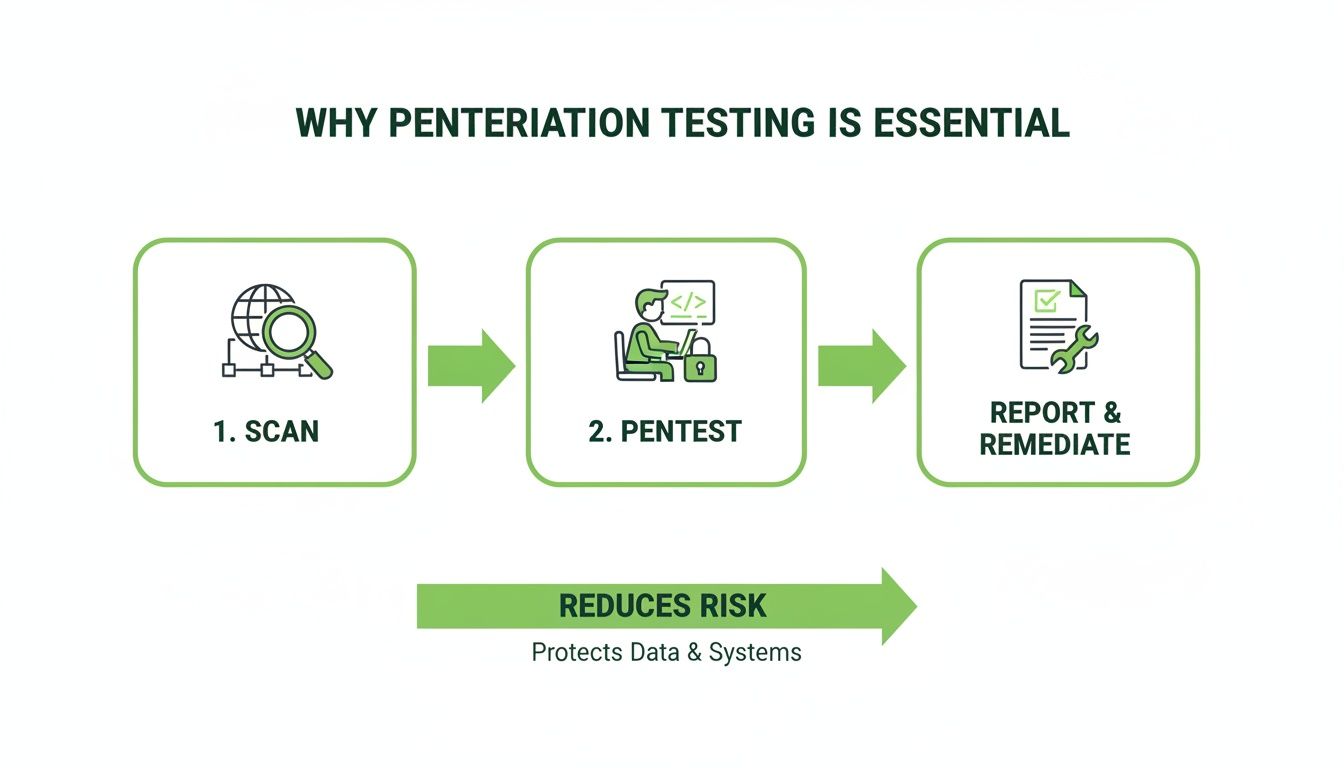
This is the key to a fast and affordable pentest.
Stage 1: Planning The Pentest Scope
This first step is about setting the ground rules. We work with you to define the scope. That just means we agree on what parts of your application we will test.
During this phase, we'll ask for things like test account credentials. Getting this right from the start ensures the test is focused and efficient. Clear planning helps us deliver your results within our one-week timeline.
Stage 2: Active Testing And Exploitation
Once the plan is locked in, our certified ethical hackers get to work. Experts holding OSCP, CEH, and CREST certifications start probing your application for weaknesses. They use a mix of automated tools and manual techniques to find vulnerabilities.
This manual approach is what separates a real penetration test from a basic scan. Our pentesters creatively chain together small flaws and test your business logic. This is where we uncover critical risks that automated tools always miss. You can learn more about this in our guide on web application penetration testing.
Stage 3: Clear Reporting And Fixes
The final stage is the most important. After testing, we compile all findings into a clear, actionable report. We don't just give you a long list of technical jargon.
Each finding includes a simple explanation, the potential business impact, a risk rating, and step-by-step guidance on how to fix the issue. Because our process is so efficient, you get this comprehensive report in about a week.
Common Security Flaws We Discover For You

Our ethical hackers are experts at finding the security gaps that automated tools overlook. During an application penetration test, we simulate real-world attacks. We use frameworks like the OWASP Top 10 to focus on the most critical risks.
Understanding these risks shows why a manual pentest is so important. You need an experienced human to spot business logic flaws and complex attack chains. This is where you get the real value from a penetration test.
Uncovering Critical Injection Security Flaws
One of the most dangerous vulnerabilities we find is SQL Injection. Think of it like a trick question you ask a database. An attacker can slip malicious code into a form on your website to fool your database into giving up secrets.
This could be anything from customer usernames to credit card details. Our certified pentesters manually test every input field to ensure your application keeps your data safe.
Finding Broken Authentication and Access Control
Another huge problem is Broken Authentication and Access Control. This is like having a key for the front door that also unlocks the CEO's office. This flaw allows a regular user to access admin functions or another user's private data.
This often happens when an app doesn't correctly check a user's permissions. Our manual testing process focuses heavily on finding these logic flaws that scanners can't possibly understand.
The Dangers Of Cross-Site Scripting (XSS)
We also uncover Cross-Site Scripting (XSS) vulnerabilities regularly. Imagine someone could secretly add their own lines to a play being performed. XSS allows an attacker to inject malicious scripts into your website that run in your users' browsers.
This can be used to steal their session cookies or redirect them to phishing sites. It shatters the trust between you and your users. Our pentesters are skilled at finding all types of XSS. Our OSCP, CEH, and CREST certified experts look for these flaws and many more, including in our specialized API security test.
How To Choose The Right Pentesting Vendor
Not all penetration testing services are the same. Many providers are slow, overpriced, and deliver confusing reports. Choosing the wrong partner can be a frustrating and expensive mistake.
Choosing a vendor for your application penetration testing shouldn't feel like a gamble. The right partner gets you clear, actionable results fast and affordably. It’s about finding a team that understands your need for speed.
Focus On Speed and Affordable Pentesting
The old model of waiting months for a penetration test report is broken. Your security testing needs to keep up with your business. Look for vendors who deliver a fast turnaround, with a comprehensive report within a week.
Affordability is just as critical. A high price tag doesn't guarantee a better pentest. Often, you're just paying for a firm's bloated overhead. A valuable pen test shouldn't break your budget.
Verify Pentesters Have The Right Certifications
Certifications matter. They prove a pentester’s skill and professionalism. Ask any vendor about their team’s qualifications. You want to see industry-recognized certifications that prove they have hands-on expertise.
Here are the key credentials to look for: OSCP (Offensive Security Certified Professional), CEH (Certified Ethical Hacker), and CREST. These certifications tell you the pentesters have a verified, expert-level ability to perform a thorough security assessment.
Finding The Best Vendor For Your Needs
When you're up against a deadline, you need speed and value. The old way is slow and expensive. The modern approach is fast and affordable, delivering clear, actionable findings. We are built for speed and value.
The market for application testing services is growing fast. You can read the full research on the penetration testing service market to see industry trends. To understand your options, research the Top Web Application Penetration Testing Providers. Fill out our contact form to get a quote and see how we can help.
Get Your Team Ready For A Fast Pen Test
A little prep work makes a huge difference. When you have everything ready, our OSCP, CEH, and CREST certified pentesters can jump right in. That's how we deliver a detailed report within one week at a price that makes sense.
Just gather the basics before we kick off. Having clear access details and dedicated test accounts ready means we can get straight to testing. This cuts down on delays and keeps your costs lower.
Gather Key Application Access Details
Collecting all the environment specifics upfront keeps the process moving quickly. Let us know if a VPN or single sign-on is needed. This helps our team hit the ground running without burning time just trying to get access.
Toss everything into a single document so your IT manager can share it in one go. A simple spreadsheet with URLs makes our initial work super efficient. This prep helps us stick to our promise of fast, affordable penetration testing.
Define Clear Roles And Communication Paths
Assigning clear roles is crucial. When everyone knows who to contact for questions, things run smoother. Loop in your CISO, compliance officer, and an application owner.
A clear point of contact can easily cut pentest time in half. This ensures any questions are answered quickly. It helps us avoid delays and deliver your report on time.
Set a Realistic and Efficient Timeline
Once you have the access details sorted, book the test window. Try to pick a time when your development team has some bandwidth to address findings. Smart planning is how we're able to deliver on our one-week turnaround.
Make sure it aligns with your release cycle to avoid headaches. Running a pen test right before a major launch can create a bottleneck. It’s better to choose a quieter period to knock out any high-risk findings right away.
Prepare Your Team For Quick Remediation
Knowing who is going to fix what makes things faster. We recommend creating a small task force on standby. When our report lands, this group can take immediate action.
Map out a simple workflow so your team can jump straight into fixing any flaws. This keeps the momentum going and helps you avoid paying for extended retesting. Want a deeper dive? Learn more in our guide on preparing for a pen test.
Real-World Consequences Of Skipping Application Security Testing
Understanding why application pentesting matters becomes clearer when you look at the actual cost of getting it wrong. The consequences of unpatched web application vulnerabilities extend far beyond technical problems.
Financial Impact Of Application Breaches
When an attacker exploits an application vulnerability, the financial damage starts immediately and keeps growing. Direct costs include incident response, forensic investigation, legal fees, and regulatory fines. Indirect costs include customer churn, brand damage, and lost future revenue. For a small or mid-sized business, a single application breach can cost hundreds of thousands of dollars. Many companies never fully recover.
The irony is that most of these breaches are preventable. A single penetration test costing a few thousand dollars could have identified the vulnerability before an attacker did. The return on investment for proactive application security testing is enormous compared to the alternative.
Compliance Failures And Their Fallout
Skipping application pentesting does not just put your data at risk. It puts your compliance status in jeopardy. SOC 2 auditors specifically look for evidence of regular security testing. HIPAA requires covered entities to conduct periodic technical evaluations. PCI DSS has explicit penetration testing requirements for any application that handles cardholder data.
Failing a compliance audit means more than just a bad report. It can mean losing customers who require compliance as a vendor prerequisite. Enterprise buyers routinely drop vendors who cannot demonstrate adequate security controls. For SaaS companies, losing SOC 2 compliance can directly translate to lost enterprise contracts worth millions.
The Human Factor In Application Security
Automated scanners are useful tools, but they miss the vulnerabilities that matter most. Business logic flaws, chained attack paths, and authentication bypasses require a human tester who understands how applications actually work. A scanner might miss that your password reset flow lets an attacker enumerate valid email addresses, or that your API endpoint returns more data than it should when given a slightly modified request.
This is why manual application pentesting delivers better results than automated scanning alone. A certified ethical hacker thinks like a real attacker, testing edge cases and creative attack paths that machines simply cannot replicate. The combination of automated tools and human expertise is what produces a truly comprehensive security assessment.
Your Quick Pentesting Questions Answered
Got questions about application penetration testing? We have direct answers. This is the quick breakdown for IT managers, CISOs, and startup founders who need to make smart security decisions without the fluff.
What's The Difference Between A Scan and A Pen Test?
This is a big one. A vulnerability scan is like an automated guard checking for known unlocked doors. A pen test is like hiring a clever human to actually jiggle the handles and pick the lock.
Scans are fast but can't think creatively. A manual penetration test is done by a certified expert who finds the complex flaws that automated tools will always miss. For real-world security assurance, you need a human.
How Often Should We Get A Penetration Test?
For compliance like SOC 2 or HIPAA, an annual application penetration test is usually the minimum. But waiting a full year is risky. A good rule of thumb is to test at least once a year, after any major updates, and before launching a new application.
This proactive rhythm keeps your security strong as your product evolves. Regular testing is far more affordable than cleaning up after a breach.
What Should We Do With The Report Findings?
Think of your penetration test report as a roadmap to a tougher application. Get your technical team together and review the findings. Our reports prioritize vulnerabilities by risk, so you know what to fix first.
Create a plan to tackle the high-risk issues immediately. The report includes clear, step-by-step guidance to make this simple for your developers. Once the fixes are deployed, we can run a quick retest to confirm the vulnerabilities are gone.
Why Is Manual Testing So Important For Security?
Automated tools don't understand context. They can't tell if a flaw lets a user get a product for free. That’s where a human expert is irreplaceable.
Manual penetration testing is about understanding business impact. Our OSCP, CEH, and CREST certified testers analyze your application's logic to find unique risks. This human-led approach provides assurance that automated scans simply can't match.
At Affordable Pentesting, we deliver fast, expert-led manual penetration testing designed for your budget and timeline. Secure your application and meet compliance without the high costs and slow reports of traditional firms. Get your quote today.
.svg)
