TL;DR: The average cost of penetration testing in 2026 is typically $5,000 to $50,000, with most companies landing in the $10,000 to $30,000 range. That’s a small price compared with a U.S. data breach costing more than $10 million, which is why a good pen test is risk reduction, not optional overhead.
You’re probably here because you need a penetration test fast. Maybe a SOC 2 auditor asked for one, maybe a customer security questionnaire backed you into a corner, or maybe you finally got a quote from a large firm and nearly threw your laptop.
That reaction is fair.
A lot of penetration testing is overpriced, slow, and padded with process that doesn’t help your security team or your audit. You wait weeks, sit through kickoff calls, and end up with a report that says obvious things your scanner already found. That model wastes money.
Why You Need a Fast and Affordable Pentest
Your auditor wants evidence. Your biggest prospect wants a pentest report before procurement signs. Your team has two weeks, not two months, and the quote from a large security firm looks like it was built for a public company.
That is the core problem for startups and SMBs.
If you need a pentest for SOC 2, PCI, HIPAA, or a customer security review, speed and price are tied directly to revenue. A slow engagement can delay an audit, stall a contract, or force your team to keep answering the same security questionnaire without the document the buyer wants.
You do not need a bloated project plan. You need a real penetration test performed by qualified humans, scoped tightly, delivered quickly, and written clearly enough that an auditor accepts it and your engineers can fix what matters.
Speed matters because compliance deadlines are not flexible. Budget matters because smaller teams cannot burn enterprise money on weeks of meetings, retesting delays, and a report full of low-value filler.
A fast pentest also helps you avoid the wrong shortcut. Plenty of vendors sell automated scans wrapped in pentest language. That may satisfy nobody. Auditors and enterprise buyers often want proof of manual testing, validation of exploitability, and a report that shows actual methodology. If you want to understand where automation helps and where it falls short, read this guide to automated penetration testing and its limits.
The goal is simple. Get a compliance-ready report without paying for enterprise overhead.
Choose vendors that can scope quickly, test the assets that matter, and deliver on a timeline that matches your audit or sales cycle. If they need endless calls to explain the process, they are already wasting your money.
Cheap tests fail in a different way. You get a thin report, recycled scanner output, and findings your team could have pulled from basic tooling. Then you still need another pentest to satisfy the auditor or customer.
Pay for manual validation, clear reporting, and turnaround time you can use. For SMBs and startups, that is the only version of penetration testing that makes business sense.
Understanding Common Penetration Testing Pricing Models
Security firms usually price a pen test in one of two ways. Fixed price or time and materials.
Consider the example of hiring a mechanic. One shop says, “We’ll replace the brakes for a set price.” Another says, “We’ll bill you for however long it takes.” Both can work. One is much easier to budget.
Fixed price works better for most teams
A fixed-price penetration test gives you a defined scope, a clear deliverable, and a known bill before work starts. For startups, SMBs, and compliance teams, that predictability matters.
If you’re testing one web app, one API, or a small network segment, fixed pricing is usually the cleaner deal. It forces the vendor to scope the job properly instead of billing you for every surprise.
Benefits are straightforward:
- Budget control so finance and procurement know the number upfront
- Clear scope boundaries around what assets, roles, and workflows are included
- Fewer billing arguments when the project is done
- Faster approvals because there’s less ambiguity
The downside is also obvious. If you give the vendor bad scope, you’ll get a quote built on bad assumptions.
Time and materials can get messy
Time-and-materials billing sounds flexible. Sometimes it is. If your environment is changing fast, or you do not yet know the test boundary, hourly or daily billing can fit.
But this model also creates scope creep fast. Every new endpoint, admin role, integration, or test scenario can expand the bill.
That doesn’t mean time and materials is wrong. It means you need discipline. Define what matters before testing starts, or you’ll pay for discovery that should’ve happened during scoping.
If a vendor pushes hourly billing but can’t describe a realistic range, they’re asking you to underwrite their uncertainty.
Use automation before manual testing starts
One practical way to control cost is to separate obvious problems from deeper manual work. Run automated scanning first, then have human testers focus on logic flaws, broken access control, risky workflows, and exploit validation.
That’s why it helps to understand the difference between a scanner and a real pen test. This short guide on automated pen testing breaks down where automation helps and where it falls short.
A scanner finds low-hanging fruit. A pentester proves what matters.
Key Factors That Drive Up Your Pentest Cost
You ask for a pentest because a SOC 2 auditor, PCI requirement, customer questionnaire, or investor deadline is staring you down. Then the quotes land, and they are all over the place. One vendor comes in low but vague. Another wants an enterprise budget for a startup-sized scope. The spread usually comes down to a few predictable cost drivers.
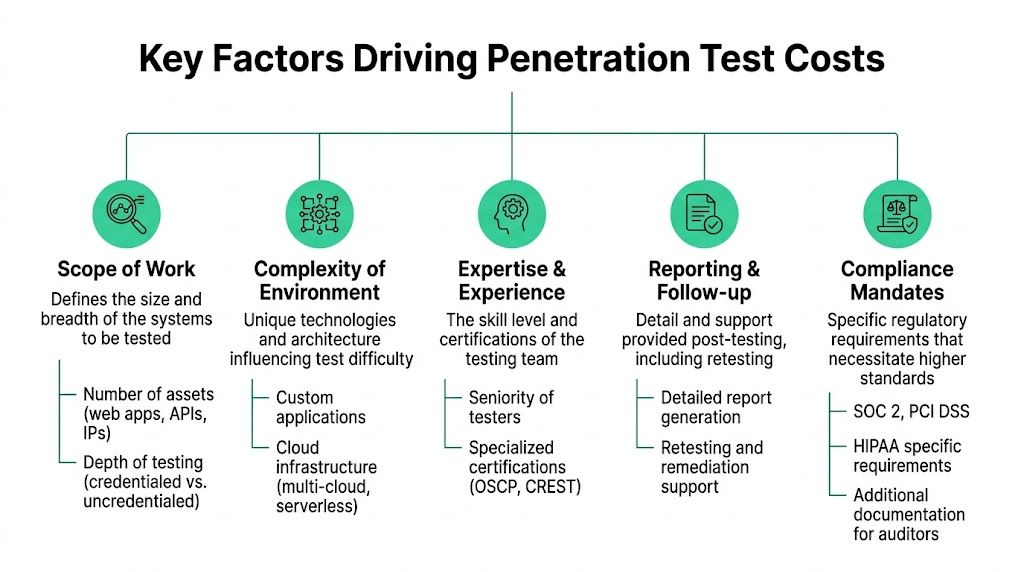
Scope drives the bill first
Scope is the first thing that moves the price. A small authenticated web app with a few user roles is one job. A SaaS product with admin panels, customer tenants, APIs, SSO, and cloud-connected workflows is a different job entirely.
SMBs lose money in this situation. They ask for "a pentest" instead of defining what needs to be tested for compliance or customer assurance. That forces the vendor to pad the quote for uncertainty, or it leads to change orders later.
Good scoping answers a few plain questions fast:
- Which assets are in scope
- Which user roles matter
- Whether testing includes authenticated access
- Whether APIs, mobile apps, or cloud components are included
- Whether retesting is included
- Whether the goal is broad risk discovery or a compliance-ready report
If you are not sure how to separate a web app test from an API, network, mobile, or cloud review, this guide to the different types of penetration testing services will help you scope the right work instead of buying too much.
Complexity increases manual effort
Complexity is what makes two similar-looking applications price very differently. Custom authorization rules, multi-tenant isolation, payment flows, file uploads, privileged admin actions, and sensitive data handling all require deeper manual testing.
Company size does not set pentest cost. Attack surface and application logic do.
That matters for startups chasing SOC 2, PCI, or HIPAA. A small team can still have a complicated product. If the app has risky workflows, a tester needs time to verify access control, business logic, and exploitability. Cheap vendors cut corners here first.
Test method changes the amount of work
Black-box, gray-box, and white-box tests produce different costs because they require different levels of setup, validation, and analysis.
- Black-box testing starts with little or no internal knowledge
- Gray-box testing uses partial access, such as user accounts or limited documentation
- White-box testing includes deeper visibility into code, architecture, or config details
For compliance-focused testing, gray-box is often the right balance. It is usually faster than pure black-box work and more realistic for finding issues that matter to auditors and customers. If a vendor pushes the most expensive method by default, ask why. You should pay for the testing approach your requirement needs.
Tester quality affects price, and bad quality costs more
Experienced testers cost more. They also waste less time, write better findings, and find the issues that turn into failed audits, delayed sales, or emergency fixes.
That pricing logic is not unique to security. The same basic labor math shows up in other service businesses. This breakdown of how security guard services determine a bill rate explains it well. Labor quality, oversight, and delivery discipline all affect the final price.
Paying less for weak testing is a false saving. You end up buying the pentest twice.
Reporting, retesting, and compliance evidence add cost
A compliance pentest is not just testing time. It also includes the report format, remediation detail, evidence quality, and retest process.
A lightweight findings memo is cheaper than an auditor-friendly report with screenshots, risk ratings, attack paths, affected assets, and clear remediation steps. If you need a letter of attestation, executive summary, or documentation mapped to a compliance requirement, expect the quote to rise.
SMBs should be strict. Do not pay enterprise pricing for bloated reporting you will never use. Do pay for a report your auditor, customer, or internal team can act on immediately.
Before you sign, confirm three things in writing:
- What report format is included
- Whether retesting is included or billed separately
- What the vendor will deliver for SOC 2, PCI, HIPAA, or customer due diligence requests
That is where a lot of "cheap" pentests get expensive.
Average Cost by Penetration Testing Type
Budgets get blown here because companies buy the wrong test first.
A startup preparing for SOC 2 often asks for a "pentest" as if that is one standard service. It is not. A web app test, an internal network test, and a cloud review answer different questions, require different skills, and produce very different invoices. If you need a fast compliance win, picking the right test type matters as much as negotiating the price.
| Test Type | Average Cost Range | Typical Duration |
|---|---|---|
| Web application pen test | $5,000 to $25,000 | 1 to 3 weeks |
| External network pen test | $4,000 to $15,000 | 1 to 2 weeks |
| Internal network pen test | $6,000 to $20,000 | 1 to 3 weeks |
| API penetration test | $5,000 to $18,000 | 1 to 2 weeks |
| Mobile app penetration test | $7,000 to $35,000 per platform | Varies by scope |
| Cloud penetration test | $10,000 to $50,000+ | Varies by scope |
Use these ranges as planning numbers, not purchase approvals. The key question is which test will satisfy your auditor, customer, or procurement team without dragging you into enterprise pricing.
Web application testing
This is the standard choice for SaaS companies, B2B software teams, and startups chasing SOC 2, PCI, or customer security reviews. It focuses on login flows, access control, session management, input handling, and business logic flaws that scanners miss.
For many SMBs, this is the best value per dollar. If your product is a browser-based app and your buyers want proof of testing, start here before paying for a broader engagement you may not need yet.
Cost rises fast when the app has multiple user roles, admin functions, payment flows, tenant separation, or a long list of authenticated pages.
Network testing
External network testing checks what an attacker can reach from the public internet. Internal network testing checks what happens after an attacker, contractor, or compromised device gets inside.
Internal work usually costs more because it involves more hosts, more trust relationships, and more coordination with your IT team. It also tends to uncover messy realities like flat networks, inherited permissions, and old systems nobody wants touched during business hours.
If your compliance requirement is tied to the product you sell, a network test may not be the first thing to buy. If you store sensitive data on internal systems or need broader infrastructure assurance, it moves up the list.
API testing
API testing is often the most underbought service in modern software companies. That is a mistake.
A clean front end does not protect you from broken object-level authorization, weak token handling, or role-based access flaws in the API. If customers integrate directly with your platform, or your mobile and web apps both rely on the same backend, API testing deserves its own budget line.
Costs increase with endpoint volume, auth complexity, tenant separation, and business rules. If you are still deciding what scope fits your environment, this guide to types of penetration testing can help you narrow it down before you ask vendors for quotes.
Mobile app testing
Mobile testing gets expensive because the app is only one layer of the problem. The tester may need to assess the client, local storage, authentication flows, API calls, and backend behavior together.
Platform count matters. Testing iOS and Android usually means paying for both because they have different codebases, different protections, and different failure points.
For SMBs under time pressure, ask a hard question first. Do you need a full mobile assessment now, or will a web app plus API test satisfy the compliance or customer requirement faster and for less money?
Cloud testing
Cloud testing starts higher because cloud environments are easy to scope badly and expensive to review well. Identity and access management, exposed services, storage configuration, account boundaries, and risky permissions all need attention.
This category gets overpriced more than almost any other. Vendors love broad language like "AWS security assessment" because it gives them room to expand scope later. Force specificity. Name the accounts, services, environments, and objectives before you sign anything.
For teams shipping AI-assisted products or relying heavily on generated code, adjacent reviews may also make sense. A Claude Code security audit can help if your exposure sits in AI-driven development practices rather than only in traditional web infrastructure.
Why Compliance Pentesting Costs More Money
You finally get serious about SOC 2, PCI, or HIPAA. Then the pentest quote shows up and it is far higher than the basic web app test you expected. That price jump is usually real, and for SMBs it hurts because compliance work lands on the same budget as product, hiring, and customer deadlines.

A compliance pentest is not just a normal pentest with a nicer PDF. The vendor has to test the right assets, map the work to the control framework, document scope clearly, and produce evidence an auditor can use. That means more coordination, more reporting time, and less room for vague findings.
You are paying for evidence, traceability, and audit-ready reporting
Many companies often overpay. They buy an enterprise-style engagement when all they really need is a fast, well-scoped test that satisfies a customer questionnaire or an upcoming audit.
Compliance raises cost for three practical reasons:
- Scope gets wider. PCI, SOC 2, and HIPAA often pull in more assets, user roles, and data flows than a standard product security test.
- Documentation gets stricter. Auditors want clear methodology, dates, targets, findings, severity ratings, and remediation guidance.
- Retesting and validation often matter more. If the report is going to support an audit, weak evidence creates delays and repeat work.
That last point is where cheap vendors waste your money. A low quote means nothing if the report gets rejected by your auditor or customer.
PCI and HIPAA usually create the biggest pricing jump
PCI work gets expensive fast because cardholder data environments are easy to scope badly and expensive to test correctly. HIPAA-related testing also takes more effort because the vendor has to pay closer attention to how protected health information is accessed, exposed, stored, and moved through the app and backend.
As noted earlier from TCM Security's penetration testing cost breakdown, compliance requirements can push pricing well above a baseline web application engagement. That tracks with what buyers see in the market. More reporting and more evidence means more hours.
SOC 2 is different. It does not always require the same kind of rigid prescriptive scope as PCI, but buyers still get stuck paying too much because vendors bundle in broad testing they do not need. If your audit deadline is close, ask a simpler question. What exact systems and evidence does your auditor or customer expect this quarter?
Fast compliance testing matters because delays cost more than the test
Founders and lean security teams rarely need a six-week consulting exercise. They need a credible report, a clean scope, and a turnaround that does not stall a deal or audit.
That is why affordable compliance pentesting should be built around speed and scope discipline, not bloated discovery phases. For teams planning the full audit budget, it also helps to review the broader cost of a SOC 2 audit. The pentest is only one line item, but it is the one that often blocks the rest if the vendor moves slowly or writes a weak report.
A good compliance pentest costs more because it has to stand up to scrutiny. A bad one costs even more because you pay twice.
How to Budget and Reduce Your Pen Test Costs
You don’t reduce pen test costs by pretending scope doesn’t exist. You reduce them by scoping better, preparing better, and using automation where it helps.

The easiest way to waste money is to hand a tester a messy environment, vague goals, and no priority list. They’ll still do the work. You’ll just pay more for less clarity.
Scope only what matters now
Not every asset deserves equal attention in the first engagement. If budget is tight, start with the systems that matter most to attackers, auditors, and customers.
That usually means:
- Internet-facing web apps customers log into
- APIs that expose data or account actions
- Admin panels with higher privileges
- Payment or PHI workflows tied to compliance risk
A focused pen test beats a broad, shallow one every time. You can always phase additional assets later.
Clean up easy problems before humans start
Don’t pay senior pentesters to find what a basic scanner or internal review would’ve caught. Run your own checks first. Fix stale libraries, obvious misconfigurations, test accounts, and known issues.
That prep shortens the manual effort and gives your pentesters more time for the flaws that scanners miss. Broken access control, privilege escalation, and logic abuse usually live there.
Use hybrid testing the smart way
AI-driven tools can reduce cost when used properly. The current data is meaningful. AI agents can automate up to 60 percent of reconnaissance and vulnerability scanning, and they can cut SMB pentest costs by 25 to 40 percent, according to Intruder’s analysis of penetration testing cost.
The same source says a 10-day, $15,000 web app test can drop to 5 to 6 days and around $7,500 to $9,000 when AI handles a large chunk of early recon and scanning.
That’s useful. It is not a replacement for human testing.
Use AI to clear brush. Use certified testers to find the path attackers will actually take.
Pick the right delivery model
For many SMBs, a boutique provider with certified testers is the practical middle ground. Some providers, including Affordable Pentesting, offer fixed-scope web, internal, and external penetration testing options aimed at startups and SMBs that need compliance-ready results without enterprise consulting overhead.
You should still ask the same questions no matter who you hire:
- What exact assets are included
- How much testing is manual
- Whether retesting is included
- How quickly the report arrives
- Which certifications the testers hold
Don’t buy coverage you can’t act on
If your engineering team can only remediate one app this month, don’t buy a giant multi-environment engagement because it sounds thorough. Buy the test that matches your actual remediation capacity.
A report with ten meaningful findings you can fix is worth more than a giant report that sits untouched in a ticket backlog.
Choosing the Right Penetration Testing Vendor
You need a SOC 2 or PCI pentest this month. Sales is waiting on the report. Your auditor wants clear evidence. Then the quotes come in. One is suspiciously cheap, one looks like enterprise consulting theater, and one hides the actual cost behind vague language about methodology and delivery.
Pick the wrong vendor and you pay twice. First for the test. Then again in delays, weak findings, unclear reporting, and remediation support that disappears once the invoice is paid.
For SMBs and startups, vendor choice is usually the biggest pricing mistake.
Choose for fit, not brand
A freelancer may work for a very small, low-risk scope. A large consultancy may make sense if you have multiple business units, a long stakeholder chain, and a procurement process built for six-figure projects. Most SMBs need neither.
The practical middle ground is a boutique firm that handles compliance-driven pentests every week. That model usually fits startups and lean security teams better because the work is scoped tighter, communication is faster, and the report is built for auditors and engineers, not just procurement.
Here is the tradeoff:
| Vendor type | Typical fit | Main risk |
|---|---|---|
| Freelancer | Small one-off test, very limited budget | QA varies a lot, reporting may not satisfy auditors |
| Boutique compliance-focused firm | SMBs, startups, SOC 2, PCI DSS, HIPAA work | You still need to confirm tester experience and report quality |
| Enterprise consultancy | Large programs, complex environments, many stakeholders | Higher cost, slower scheduling, more process overhead |
If your goal is a fast compliance report without enterprise pricing, start with boutique providers and make them prove they can deliver.
Ask questions that expose weak vendors fast
Polished sales calls hide weak delivery. Direct questions do not.
Ask these before you sign:
Who will perform the testing
Get the names or roles of the actual testers, not just the account team. Ask what certifications they hold, such as OSCP, CEH, or CREST.What is tested manually
If the answer sounds like mostly automated scanning, keep looking. A compliance pentest still needs human validation and attack-path testing.What is the report delivery date
Get a firm timeline in writing. “A few weeks” is how deadlines slip.Is retesting included
Many low quotes leave this out, then charge extra when you need validation for auditors or customers.Will the report satisfy our audit requirement
Ask whether the report format is regularly used for SOC 2, PCI DSS, or HIPAA evidence requests.Who answers remediation questions after delivery
Your team may need clarification on exploitability, compensating controls, or fix priority. Make sure that support is part of the engagement.
One weak answer is a warning. Three weak answers means move on.
Cheap pentests often get expensive later
A low quote looks good until the report lands and it reads like scanner output with screenshots. That does not help your engineers fix the right issues, and it does not help when an auditor asks what was manually validated.
The opposite problem is common too. Large firms sell process, meetings, and layers of review that smaller teams do not need. You are buying a security assessment, not a consulting roadshow.
Good vendors are specific. They define scope clearly, explain the manual testing approach, commit to a report date, and tell you exactly what happens after remediation. If they cannot do that before the sale, do not expect discipline after it.
What good value actually looks like
For a startup or SMB, a strong vendor usually does four things well. They scope tightly. They test the assets that matter for compliance. They deliver on a schedule your audit or sales process can use. They give you a report that is clear enough for both engineers and reviewers.
That is the bar.
The right vendor is the one that finds real issues, documents them clearly, and gets your team to a usable compliance outcome without wasting a month or a large chunk of your security budget.
Get the Pentest Report You Need Without Overpaying
The average cost of penetration testing isn’t mysterious. What confuses buyers is the gap between a fair quote and a bloated one.
A solid pen test usually lands in a normal market range, but your final price depends on scope, complexity, compliance requirements, reporting quality, and who you hire. If you’re careful about those inputs, you can keep costs under control without settling for weak testing.
That’s the part too many firms ignore. You do not need to choose between affordability, speed, and quality. You need a vendor that knows how to scope tightly, test manually where it matters, and deliver a report your engineers and auditors can both use.
If you’re buying penetration testing for SOC 2, PCI DSS, HIPAA, or a customer requirement, keep it simple. Define the assets. Cut unnecessary scope. Ask hard questions. Prioritize certified testers. Demand a timeline you can realistically work with.
A fast, affordable penetration test is possible. Overpaying for slow security theater is optional.
If you need a straightforward quote for a web app, API, cloud, internal, or external Affordable Pentesting engagement, use the contact form and ask for a scoped proposal with timeline, deliverables, and retest details upfront. That’s the fastest way to get a report you can use without paying enterprise prices.
.svg)
