TL;DR: A solid penetration test for a startup or SMB can realistically land between $4,000 and $15,000 when the scope is tight, even though the broader market for professional tests in 2025 runs from $5,000 to $50,000 and small businesses doing simple web app testing often spend $4,000 to $10,000 (MarketsandMarkets). You also shouldn't wait forever for results. A good provider can turn around a usable report in a week instead of dragging the job through a slow enterprise process.
You're probably here because you got a quote for a pen test, penetration test, or penetration testing engagement and the number looked absurd. Then the timeline looked worse.
That happens all the time. A startup needs a report for SOC 2, PCI DSS, HIPAA, ISO 27001, or a customer security review, and a traditional firm shows up with enterprise pricing, vague scoping, and a delivery date that doesn't match the sales deadline.
My opinion is simple. Most companies don't have a security problem first. They have a buying problem. They buy the wrong kind of pentesting engagement, with the wrong scope, from a firm built for giant enterprises instead of fast-moving teams.
Stop Overpaying for Slow Penetration Testing
A lot of penetration testing firms still sell like it's ten years ago. They schedule too many calls, ask for too little detail, hand you a bloated statement of work, and then take weeks to give you a report that should've arrived much sooner.
That old model is expensive because it carries enterprise overhead. You pay for project management layers, padded timelines, and broad scoping that protects the vendor more than it helps you.
Why founders get burned
Founders and IT managers usually need one of three things:
- A compliance-ready report: You need a pen test to satisfy an auditor or procurement team.
- A real security check: You want a human tester to find what scanners miss.
- A fast answer: You can't wait around while a vendor fits you into next month's calendar.
Traditional firms are weak at all three when you're a smaller company. They often move slowly, charge like a bank, and still return a report with shallow findings because the engagement leaned too heavily on automated scanning.
Practical rule: If a vendor can't explain exactly what they are testing, how long it will take, and when you'll get the report, the quote is already too expensive.
What a fair engagement looks like
A fair penetration test should be tightly scoped, manually validated, and priced around the assets that matter. If you have one web app, one API, or a small external network, you should not be buying the same process a global enterprise uses for a sprawling environment.
You also want certified testers. OSCP, CEH, and CREST matter because they show the people doing the work have been vetted and trained. Certifications don't guarantee quality, but no serious buyer should ignore them.
The direct answer is this. Buy focused manual pentesting, not vague "security assessments." Ask for a fixed scope. Demand a report fast enough to keep your audit or deal moving. If a vendor needs forever to test a modest environment, they're selling inefficiency.
How Penetration Testing Pricing Models Work
You get a pentest quote for $8,000. That looks manageable. Then the report shows up three weeks late, your team burns another sprint fixing issues, and the vendor charges again for re-testing. Your real cost was never $8,000.
That is why pricing models matter. The quote is only the first number. The bigger question is how much time, delay, and follow-up cost the model creates after testing starts.
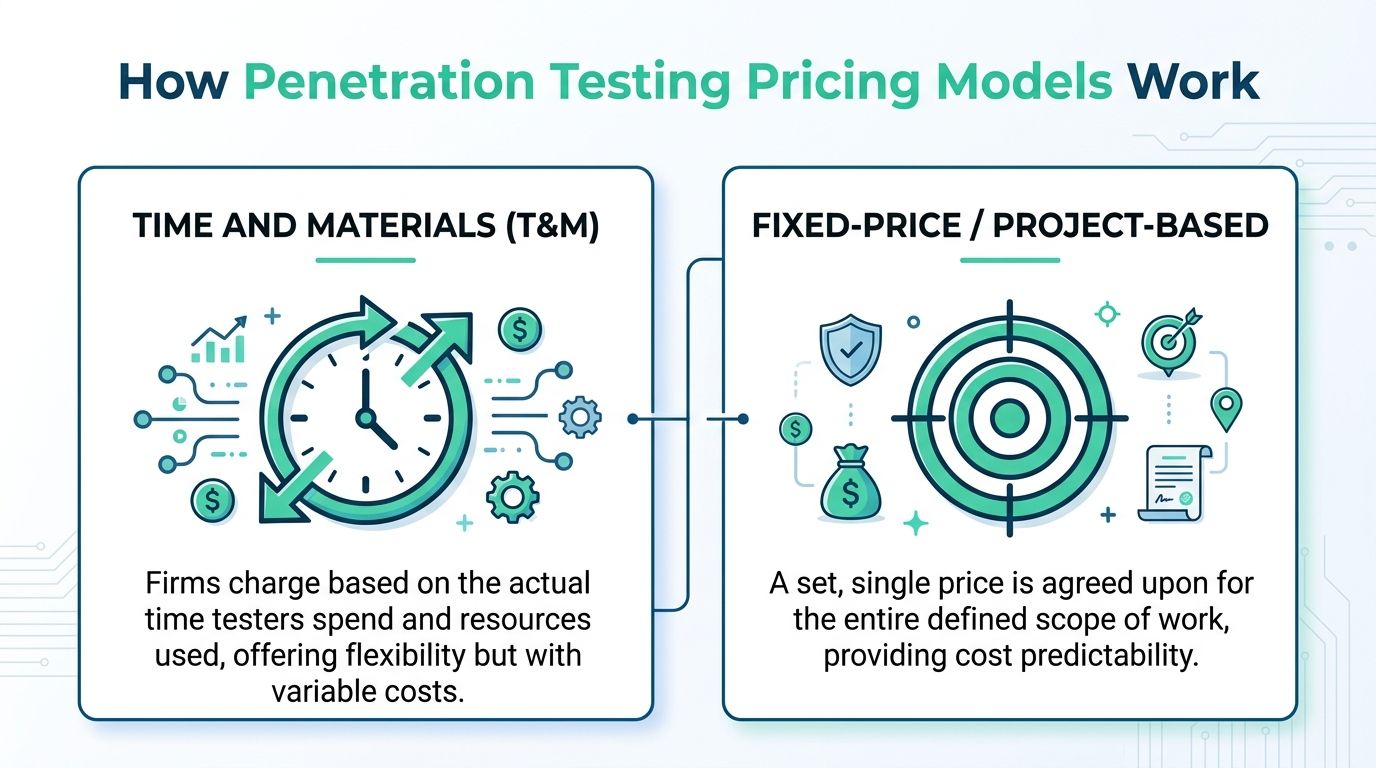
Time and materials pricing
This is hourly or daily billing. It favors the vendor.
If the scope is loose, you pay more. If the tester finds extra complexity, you pay more. If the firm underestimated the job, you still pay more. Startups rarely win with this model because budget certainty disappears the moment the engagement gets messy.
It also creates a time problem. Slow testing, slow reporting, and extra back-and-forth can all stretch the project while the invoice keeps growing.
Fixed price projects
Fixed-price testing is the right choice for most startups and SMBs. You agree on the scope, deliverables, timeline, and cost before kickoff.
That structure forces the vendor to scope the work properly. It also protects you from the classic pentest billing trick where a modest project turns into a bigger invoice because the firm asked weak questions up front.
The best fixed-price engagements also define what happens after the initial report. Ask whether remediation review is included. Ask whether one re-test is included. Ask how fast the final report lands after validation. If those details are missing, the quote is incomplete.
Subscription and recurring testing
A retainer or subscription can work if you ship often, maintain several assets, or need regular validation across the year.
But be strict here. Some vendors sell recurring scans and call it pentesting. That is not the same as manual testing by an actual operator. If you want the difference spelled out, read this guide to automated pen testing.
Recurring testing only makes financial sense when the service includes real human testing, clear turnaround times, and a defined process for remediation and re-testing. Otherwise you are just paying monthly for noise.
My recommendation
For a defined app, API, or external network, buy fixed-price testing with remediation validation baked into the deal. Use time and materials only for unusual research-heavy work where nobody can reasonably lock the scope in advance. Use subscriptions only if you release often enough to justify ongoing manual testing.
| Pricing model | Good for | Main risk |
|---|---|---|
| Fixed-price | Defined scope, compliance work, budget control | Weak scoping if the vendor rushes discovery |
| Time and materials | Open-ended research, complex edge cases | Budget creep and slower decisions |
| Subscription | Frequent releases, ongoing validation | Scan-heavy service dressed up as pentesting |
A good quote is simple. Clear scope. Clear price. Clear report date. Clear re-test terms.
If any of that is vague, the pentest will get expensive fast.
Key Factors That Drive Your Pentest Cost
Pentest cost comes down to one thing. How many hours of real manual work your scope creates.
A founder asks for “a pentest for our app,” gets a quote that looks manageable, then loses two extra weeks clarifying scope, waits again for the report, fixes issues, and gets hit with a re-test fee. That is how a “reasonable” pentest turns expensive. The quote is only the starting number. The actual cost is the total effort, total delay, and total back-and-forth.
Scope drives the bill
Vague scope is expensive scope.
“Test our app” tells a tester almost nothing. Is it a brochure site with login, a SaaS app with tenant separation, an API with privileged endpoints, or an internal admin panel tied to billing and user management? Those are completely different jobs.
The same problem shows up in network testing. A small external footprint is one project. An internal environment with workstations, servers, VPN access, and privilege escalation paths is another. More assets usually mean more time, but asset count is not the main issue. Complexity is.
Complexity is what slows everything down
Two apps can look similar on paper and cost very different amounts to test.
The expensive one usually has more states, more trust boundaries, and more ways to break business rules. That means more manual validation, more edge cases, and more retesting after fixes.
Here is what pushes time up fast:
- User roles and permissions: admin, customer, support, partner, and reseller paths all need separate testing
- Authentication flows: SSO, MFA, password reset, invite flows, session handling, and account recovery add work
- Business logic: billing, approval chains, tenant isolation, discount abuse, and workflow bypasses take real analyst time
- Connected systems: APIs, mobile apps, cloud storage, webhooks, and third-party integrations expand scope
- Environment sprawl: staging, production, regional deployments, and separate admin interfaces create more to verify
Startups often get burned when traditional firms quote the initial test, then charge more when hidden complexity appears, remediation drags out, or the re-test falls outside a narrow window.
Test type changes effort
The access you give the tester affects both price and timeline.
| Test type | What it means | Cost impact |
|---|---|---|
| Black box | Little or no internal knowledge provided | More time spent on discovery and setup |
| Grey box | Limited context or user access provided | Usually the best balance of depth and speed |
| White box | Broad access, documentation, or code context provided | Faster validation of deeper areas |
If your goal is practical risk reduction, grey box is usually the smart buy. You get more test depth per hour because the tester spends less time guessing how your system works and more time breaking it.
Network size matters, but not in the way buyers think
Founders often focus on IP count because it is easy to count. That is not enough.
An external test on a clean, well-defined set of internet-facing systems is usually straightforward. An internal test takes longer because the tester has to establish attack paths, verify access controls, and prove how far compromise can spread. Flat networks, legacy systems, weak segmentation, and shared admin access all increase effort. They also increase remediation time afterward, which increases your total cost even if the quote looked fine on day one.
If you want a cleaner breakdown of how vendors turn scope into dollars, read this guide to pen testing price and quoting factors.
The report process affects cost too
This part gets ignored far too often.
A slow report is expensive. If findings arrive late or come back vague, your engineers spend longer figuring out what to fix. If remediation guidance is weak, you burn more time in Slack threads and follow-up calls. If re-testing is billed separately or scheduled weeks later, the pentest keeps dragging and your compliance deadline gets closer.
That is why the total cost of a pentest is not just the testing fee. It is the testing fee plus reporting delay, remediation friction, and re-test terms.
What to do before you ask for a quote
Show the vendor exactly what needs testing. Name the asset. State the environment. List the user roles. Flag the risky workflows. Call out any APIs, admin panels, or third-party integrations.
Do that, and you get a tighter quote, a faster test, and fewer surprise costs later. Skip it, and you will probably pay for confusion twice.
Typical Price Ranges for Different Pen Tests
A founder gets a quote for $28,000 to test one web app and a small API, signs it, then learns the report will take two weeks and re-testing costs extra. That is how an average pentest turns into an expensive one.
Price ranges matter, but only if you use them to spot bad fit and bloated scope.
What the market looks like
As noted earlier, penetration testing prices span a wide range. Small, focused engagements sit at the low end. Large environments with multiple apps, cloud assets, internal networks, and complex user roles sit at the high end.
For practical budgeting, many startups and SMBs will see quotes somewhere in the mid four figures to low five figures for a tightly scoped test. Bigger multi-scope engagements can climb fast. The mistake is treating all of those numbers as comparable. They are not buying the same amount of work, and they rarely include the same reporting speed or re-test terms.
Common price ranges by test type
Use these ranges as a rough filter, not a buying decision:
| Pen test type | Typical range |
|---|---|
| Web application testing | $5,000 to $30,000+ |
| Network assessments | $5,000 to $40,000+ |
| API testing | $6,000 to $30,000 |
| Mobile application testing | $7,000 to $35,000+ per platform |
| Cloud environment testing | $10,000 to $50,000+ |
Small business projects usually land near the bottom of those bands when the scope is narrow and the environment is clean. Mid-sized companies pay more because they usually have more authenticated workflows, more integrations, and more assets to validate. Enterprise pricing is a different category entirely.
Do not let enterprise pricing distort your expectations.
What this means for startups and SMBs
If you have one customer-facing app, one API, and a limited external footprint, you should be buying a focused test, not an enterprise engagement. Careful scoping is essential here.
A lot of firms still sell by throwing extra days at the project, then charging again for the retest. That old model looks fine in the quote and gets expensive later. Slow reporting delays fixes. Weak remediation guidance burns engineering time. Separate re-testing fees stretch the whole project out and push up total cost.
The cheaper quote is often not the cheaper pentest.
A blunt way to judge quotes
If a vendor prices your small app like a complex enterprise program, push back hard. Ask what in your scope drives the number.
Good answers are specific. Number of roles. Authenticated areas. API endpoints. Admin functions. Cloud accounts. Segmented networks. Required deliverables. Report turnaround. Retest policy.
Bad answers are vague. "Full coverage." "Best practice methodology." "Thorough assessment."
A fair quote maps to real assets and real effort. If it does not, you are paying for overhead, delay, or both.
Budgeting for Pentesting and Maximizing ROI
You sign a $12,000 pentest. Two weeks later, engineering is still waiting on the report, sales cannot send the security package to a prospect, and the vendor wants another fee to validate fixes. That is how a "reasonable" quote turns into an expensive project.

ROI comes from reducing loss and reducing drag
A pentest earns its keep in two ways. It lowers the chance of a costly security failure, and it keeps your team from wasting weeks on a slow, messy remediation cycle.
Analysts cited by DeepStrike report breach costs in the millions and note that annual pentesting spend is usually modest by comparison. That gap is the easy part of the ROI argument.
The harder part, and the one buyers miss, is operational cost. A slow engagement ties up engineers, delays compliance work, and creates extra review cycles with customers and auditors.
The real budget is bigger than the quote
Founders should budget for the full lifecycle, not just the kickoff invoice.
A weak report costs money because engineers spend more time figuring out what went wrong and how to fix it. A separate retest fee costs money because every round trip adds another approval step, another invoice, and another delay. A late final report costs money because customer security reviews and audit deadlines do not wait for your vendor.
GetAutonoma notes that quoted prices often leave out remediation time, retest fees, and the cost of audit disruption. That is exactly why cheap pentests often end up expensive.
Buy speed and clarity
I push buyers toward fast manual testing with clear findings, concrete remediation guidance, and a defined retest path. That is what improves ROI.
If your team gets a useful report quickly, fixes start sooner. If retesting is built into the process, you close findings faster. If the final deliverable lands on time, you keep the audit, launch, or sales cycle moving.
That is the part traditional firms undersell. They quote the test. You pay for the waiting.
Use a budget model that matches reality
Build your pentest budget around four costs:
- Initial test fee: The scoped assessment itself
- Internal remediation time: Engineering hours to fix validated issues
- Validation or retest: Confirming fixes and updating the report
- Timing risk: Delays that affect audits, renewals, launches, or deals
If you want to cut wasted time before the engagement starts, use this guide on how to prepare for a penetration test.
For teams that need to line up security work with broader risk priorities, the Cyber Security Risk Assessment Template is a practical starting point.
A fair pentest budget covers the test, the fixes, and the path to a clean final report. Anything less is wishful thinking.
Scoping Your Pentest and Getting a Fair Quote
The fastest way to waste money is to ask for a broad quote with a fuzzy scope. The fastest way to get a fair quote is to define exactly what should be tested and what should stay out.
That sounds basic, but it's where most buying mistakes start.
Use a scoping checklist first
Before you contact any vendor, write down the essentials:
- Asset type: Web app, API, mobile app, cloud environment, external network, internal network
- Target name: The exact product, app, or environment
- Access level: Black box, grey box, or white box
- User roles: Admin, standard user, guest, support, or any other role that changes permissions
- Critical workflows: Login, checkout, billing, file upload, password reset, admin actions
- Environment: Production, staging, or a dedicated test instance
- Compliance need: SOC 2, PCI DSS, HIPAA, ISO 27001, or customer due diligence
- Report deadline: When you need the final deliverable
If you need help documenting risk before you scope the test, this Cyber Security Risk Assessment Template is a practical resource for organizing what matters and why.
Good scope versus bad scope
Bad scope: "Test our website."
Good scope: "Test the authenticated web app used by customers and admins, including login, password reset, billing, file upload, and role-based access controls."
The second version gives the tester enough detail to estimate effort. The first one invites padding.
Ask yourself one blunt question. If a tester found a serious issue tomorrow, where would it hurt your business most? Start there.
Sample pentest scopes and estimated costs
Below is a simple way to think about realistic scope.
| Business Profile | Scope of Work | Estimated Cost Range |
|---|---|---|
| Early-stage startup | One small web application, limited authenticated area, a few user roles | $4,000 to $10,000 |
| SaaS startup preparing for compliance | Main web app plus core authenticated workflows and a focused API review | $5,000 to $15,000 |
| SMB with internet-facing infrastructure | External network assessment of a limited number of critical assets | $5,000 to $20,000 |
| Mid-sized company with internal risk concerns | Internal network test with user access paths and privilege review | $10,000 to $30,000+ |
These ranges are grounded in the verified market figures already discussed earlier. Your actual quote should depend on the specifics, not on a generic package name.
Questions every buyer should ask
Don't overcomplicate vendor selection. Ask these direct questions:
- Who is doing the testing? Ask whether the testers hold certifications like OSCP, CEH, or CREST.
- Is the work manual, automated, or mixed? You want human validation, not just scanner output.
- What is included in the report? Ask for executive summary, technical findings, evidence, and remediation guidance.
- How fast will the report arrive? If speed matters, get the answer in writing.
- What happens after we fix issues? Ask whether retesting is included, limited, or separately priced.
- What is out of scope? This prevents arguments later.
- Do you provide prep guidance? A useful provider should help you get ready before kickoff.
For teams that want a practical prep list before engaging a vendor, this guide on how to prepare for a penetration test is worth reviewing.
One sensible buying approach
My advice is to buy in stages. Start with the asset that blocks revenue, compliance, or creates the highest risk. Then expand.
That approach works well for startups because it keeps the first project affordable and useful. It also gives you a better signal on whether the provider delivers clear findings, a useful report, and a sane retest process.
This is also the right place to mention one option in the market. Affordable Pentesting provides scoped services for web apps, networks, and cloud environments aimed at startups and SMBs, with work aligned to frameworks like SOC 2, PCI DSS, HIPAA, and ISO 27001. That's the model I recommend in general. Focused scope, certified testers, and fast delivery.
Red flags that should kill a deal
Walk away if you see any of these:
- No scoping questions: They can't price accurately if they don't understand the target.
- A giant quote for a small app: That's usually overhead, not depth.
- No clear report timeline: Delay is a real cost.
- No retest explanation: You'll feel that later.
- Only scanner language: A vulnerability scan is not the same as a penetration test.
Fair pricing starts with sharp scoping. Most overpayment problems disappear when the scope gets specific.
Your Next Steps to an Affordable Pentest
At this point, the path is straightforward. Define a narrow scope, ask for fixed pricing, confirm the report timeline, and make sure certified testers are doing manual work.
That's how you keep the cost of penetration testing under control without buying junk.
If you want another outside view of what a modern service engagement looks like, this overview of Penetration Testing gives a broad picture of how organizations approach these assessments.
The old way is slow because it was built for large enterprise buying cycles. Startups and SMBs don't need that. They need a clean scope, a fair quote, strong findings, and a report quickly enough to keep business moving.
If a provider can't do that, keep looking. Security matters, but so does time.
If you need a fast, straightforward quote, contact Affordable Pentesting through the contact form. You can get a scoped pen test, penetration test, or penetration testing engagement without the bloated process, and get an audit-ready report within a week.
.svg)
