You need a penetration test because an auditor asked for it, a customer questionnaire demanded it, or your team knows your public systems haven't had a security check in too long. Then the quotes come in. High prices, long timelines, junior staff hiding behind templates, and a report that lands weeks later with little you can use.
That's the old enterprise model. It's bloated, slow, and a bad fit for startups, SMBs, and lean security teams.
Good cyber security penetration testing services should do three things well. They should find risk, support compliance, and move fast enough that the report is still useful when you get it. If your vendor can't do that, you're paying for process instead of security.
Your Fast Track to Compliance Pentesting
Most buyers aren't shopping for penetration testing because it sounds fun. They need a pen test now because SOC 2 is moving, PCI DSS is due, HIPAA controls need proof, or a customer won't sign until the security review is done.
That pressure is normal. So is the frustration. Traditional firms often act like every engagement needs layers of calls, scoping workshops, and a month of waiting before anyone tests anything.
Compliance demand is not slowing down
This isn't a niche service anymore. Over 75% of organizations now conduct penetration tests to maintain compliance with regulations such as GDPR, PCI DSS, and HIPAA, and the global penetration testing services market is projected to reach USD 9.95 billion by 2034 according to Intel Market Research.
That's exactly why buyers need to be careful. When demand rises, a lot of vendors sell "compliance pentests" that are just dressed-up scans.
Practical rule: If a vendor promises an audit-ready test without clear manual validation, you're probably buying a scanner with a PDF attached.
Speed matters more than vendors admit
A penetration test tied to compliance should not drag on forever. If your team has to wait weeks for basic findings, that slows engineering, delays audits, and creates more internal work.
A better model is simple:
- Scope fast so everyone knows what's in and out
- Test manually so the results reflect attacker behavior
- Report quickly so your team can fix issues while the context is still fresh
- Package evidence cleanly so auditors can review it without a dozen follow-up emails
If you're also working toward broader governance goals, this guide to ISO 27001 certification is a useful reference because it helps frame where penetration testing fits into a larger compliance program.
What Is A Real Cyber Security Penetration Test
A penetration test is not a software tool running a checklist. It's a person trying to think like an attacker and prove what can go wrong.
That's the difference too many buyers miss.
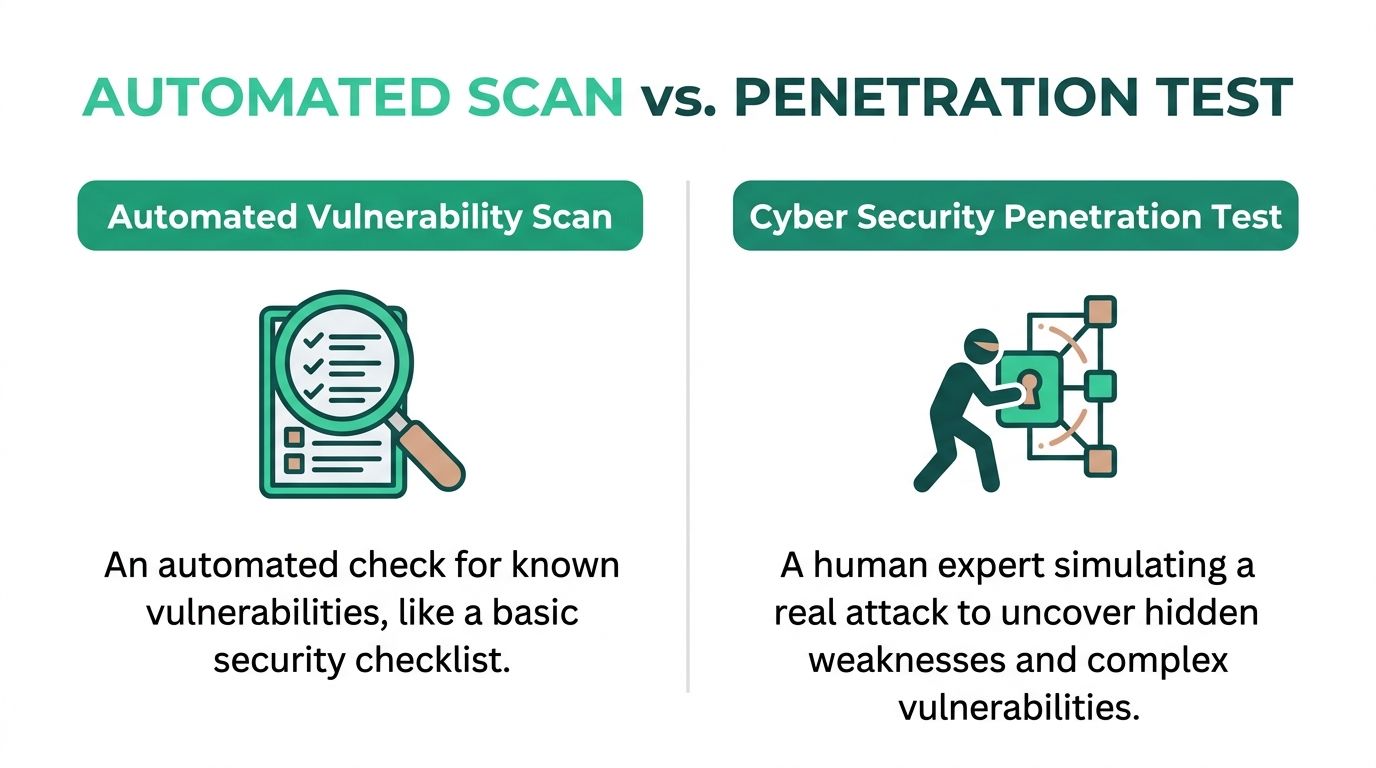
Scan first, test second
An automated vulnerability scan is useful. It checks for known issues, common misconfigurations, exposed software versions, and obvious weak spots. It's like walking around your house to see whether the doors and windows are shut.
A manual penetration test is different. That's like hiring someone to try to get inside, move room to room, and show you which small mistakes combine into a break-in.
Here's the plain-English difference:
| Method | What it does | What it misses |
|---|---|---|
| Vulnerability scan | Finds known issues quickly across systems and apps | Business logic flaws, chained attacks, context |
| Pen test | Tries to exploit weaknesses the way an attacker would | It takes human time and judgment, so it must be well scoped |
Why manual testing still matters
Attackers don't stop after the first issue. They chain things together.
A scanner might flag a weak login policy, a strange API response, and a permissions mistake as separate low or medium issues. A human tester may discover those three problems lead to account takeover or access to sensitive data.
That's why a proper penetration testing engagement usually includes work like:
- Reconnaissance using public information to see what an outsider can learn
- Validation to separate flaws from noise
- Exploitation where safe, authorized proof shows whether a weakness is dangerous
- Privilege testing to see how far access can spread once someone gets in
- Clear documentation so your developers can reproduce and fix the issue
A scan tells you what's exposed. A pen test tells you what an attacker can do with it.
What auditors expect
For compliance, the difference matters even more. Auditors usually want evidence that someone evaluated your controls in a meaningful way. A spreadsheet of scanner output won't carry the same weight as a report written by certified testers who validated findings.
That doesn't mean automation is bad. It means automation isn't enough on its own.
Good cyber security penetration testing services use both. Tools help testers move faster. Human judgment decides what matters.
Understanding The Different Types Of Pentesting
Not every penetration test is the same. If you ask for "a pentest" without knowing the target, you'll either overbuy or test the wrong thing.
Start with what your business runs. Your website, cloud environment, internal network, APIs, and mobile apps all fail in different ways.
External and internal network tests
An external network penetration test looks at what an attacker on the internet can reach. If you have internet-facing systems, remote access, firewalls, VPNs, or exposed services, you need this.
An internal network pen test asks a tougher question. If someone gets inside through a phishing attack, stolen laptop, or weak credential, how far can they move? That matters because attackers keep abusing credentials. In 2024, successful credential dumping occurred in 28,866 instances across 50,000 penetration tests, and ransomware attacks are rising by over 35% annually according to Horizon3.ai's 2025 cybersecurity report.
If your company has employees, endpoints, shared drives, or internal admin systems, internal testing is not optional forever. It may not be first on your list, but it should be on the list.
Web application and API tests
If customers log in through a browser, store data, pay you online, or use an admin portal, you need a web application penetration test. This checks how the app handles authentication, access control, input, sessions, and data exposure.
An API penetration test focuses on how systems talk to each other. That's critical when your mobile app, frontend, partners, or internal tools rely on APIs behind the scenes. API issues often hide in authorization logic, token handling, and endpoint behavior.
If your team also uses automated checks during development, this overview of dynamic application security testing is worth reading because it helps explain where runtime scanning helps and where manual testing still has to step in.
Mobile app and cloud tests
A mobile app pen test checks what happens inside the app and in the traffic it sends. If you ship iOS or Android apps, especially for finance, healthcare, or customer accounts, this matters.
A cloud penetration test looks at the way your hosted environment is configured and accessed. If you're running in AWS, Azure, or another cloud platform, weak permissions and exposed services can turn into major problems fast.
How to choose the right one
Use this quick filter.
- You run a company website with logins or customer data. Get a web application pen test.
- You expose services to the internet. Get an external network penetration test.
- Your staff uses internal systems and shared access. Add an internal network pen test.
- Your product depends on backend endpoints. Add API penetration testing.
- You ship a mobile product. Include mobile testing.
- You rely heavily on cloud infrastructure. Scope a cloud review into the engagement.
If you want a deeper breakdown of options, this guide on types of penetration testing is a practical starting point.
Buy the test that matches your attack surface, not the one with the fanciest proposal deck.
How Pentesting Helps Meet Compliance Mandates
A lot of security teams treat compliance and security as separate jobs. That's a mistake. A good penetration test does both when it's scoped correctly and reported properly.
Compliance frameworks don't just want policies. They want evidence that your controls work in practice.

Why third-party testing is so common
For many organizations, compliance is the main reason they bring in outside testers. 58% of organizations use third-party pentesters to meet mandates like PCI DSS, SOC 2, and HIPAA, and the most common assessments are network testing at 81% and application testing at 68% according to Pentest-Tools.com.
That's sensible. An external team gives you independent validation, and auditors usually prefer that over a self-assessment with weak evidence.
What the test proves to an auditor
A penetration test helps in a few concrete ways.
For SOC 2, the report shows that your organization tested whether security controls hold up under attack. Auditors and customers want proof, not promises. If your systems include a web app, API, or cloud environment, a pen test helps support that story.
For PCI DSS, penetration testing is tied directly to checking the security of cardholder-related systems and segmentation. If your payment environment is supposed to be isolated, testing can help show whether that separation is real or just assumed.
For HIPAA, the value is practical. If you store or process protected health information, testing helps demonstrate risk analysis and technical safeguard validation. That's especially important when patient data sits in web portals, mobile apps, or cloud systems.
For ISO 27001, a penetration test supports the broader requirement to assess and treat information security risk with evidence, not guesswork.
What a compliance-ready pen test should include
If you're buying for compliance, don't settle for vague language. Ask for these deliverables:
- Defined scope that names the systems tested and the test boundaries
- Manual validation so the findings reflect risk, not scanner noise
- Clear severity ratings that help teams prioritize fixes
- Evidence for each issue such as screenshots, request and response details, or proof-of-concept notes
- Remediation guidance your engineers can follow
- Retest support if the framework or auditor expects proof that fixes were verified
A lot of teams get stuck because they buy a technical exercise when they need audit evidence. Those are not the same thing.
If SOC 2 is your immediate concern, this page on SOC 2 penetration testing is a useful reference for lining up the test with what auditors usually ask for.
Compliance doesn't need a flashy report. It needs a credible one.
Our Fast And Simple Pentesting Process
Most pentest engagements waste time before anyone even starts testing. Sales hands off to a project manager. The project manager schedules a call. Then another call. Then a scope document bounces around for days while your deadline gets closer.
That approach exists because big firms built their process around internal bureaucracy. It doesn't help your security team.
Step one is quick scoping
A good process starts with a short conversation and a clear asset list. What are you testing, what are the goals, what are the constraints, and what does the auditor or customer need to see?
That's enough to get moving in most SMB and startup cases.
The best scoping conversations answer practical questions fast:
- What is in scope such as a web app, API, cloud tenant, or external network
- What access is provided for black box, gray box, or authenticated testing
- What timing matters such as a customer security review or audit window
- What deliverables are needed including retesting or compliance wording
Then the testers should test
Once scope is approved, the work should go directly to the people doing the penetration testing. Not through layers of account managers.
Here, certifications matter. If a provider says the team includes OSCP, CEH, and CREST certified pentesters, ask whether those are the people doing the test. The answer should be yes.
A strong team usually combines tools and manual work. They may use scanners, intercepting proxies, cloud review tools, and custom scripts to move quickly, but value comes from what they validate, chain together, and explain.
If your pentester can't talk plainly about what they found and how they found it, you may be dealing with a report assembler, not a security tester.
Findings should not disappear into a black hole
One of the biggest frustrations clients have is silence. The test happens, then nothing, then eventually a PDF shows up.
That is lazy service.
A better process shares meaningful findings as they come up, especially if something urgent appears. Your developers shouldn't have to wait until the end to start fixing obvious problems.
That also helps with speed. When the report arrives within a week, your team can already be working through the fixes instead of starting from zero.
The report needs to land while it still matters
A fast final report matters for two reasons. First, engineers still remember the release, endpoint, or configuration that caused the issue. Second, auditors and buyers hate stale evidence.
The simplest process usually looks like this:
| Stage | What should happen |
|---|---|
| Scoping and quote | Clear boundaries, fast turnaround, no bloated discovery phase |
| Kickoff and testing | Direct access to testers, fast start, minimal handholding |
| Live findings | Important issues shared quickly so remediation can begin |
| Final report | Audit-ready document delivered fast enough to act on |
That isn't a luxury. It's how cyber security penetration testing services should work for businesses that need answers now.
Making Sense Of Your Pentest Report
A penetration test report should help two groups at once. Leadership needs the business story. Technical teams need exact steps to reproduce and fix the issue.
If the report fails either group, it failed the job.
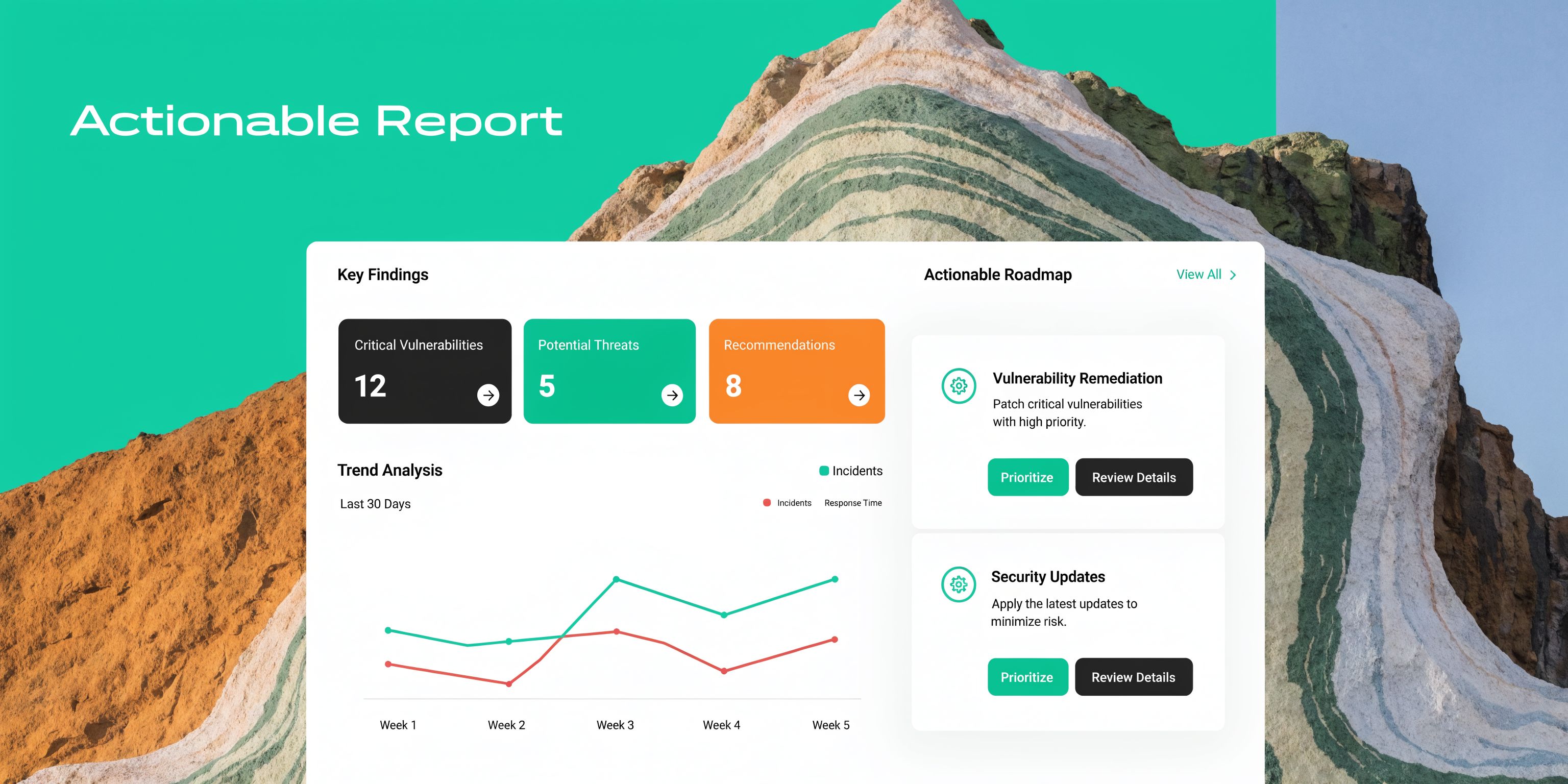
What a useful report contains
Professional penetration testing reports use the CVSS v3.1 scale to grade vulnerabilities and should include proofs-of-concept, business impact analysis, and step-by-step remediation guidance, which also helps teams track Mean Time to Remediate (MTTR) according to VikingCloud.
That sounds technical, but the idea is simple.
A useful report should include:
- Executive summary for leaders who need the risk in plain English
- Scope and methodology so auditors know what was tested
- Finding details with evidence showing the issue is real
- Business impact explaining what could happen if the issue is abused
- Fix guidance written so developers and admins can act on it
- Retest results when you need proof that the issue was resolved
CVSS without the nonsense
CVSS is a scoring method from 0 to 10. Higher means more severe. That's helpful, but scores alone can mislead teams.
A finding with a lower score can still be urgent if it affects admin access, customer data, or a critical workflow. A good report doesn't dump scores and walk away. It explains priority in context.
For example, a report should say something like this in plain terms:
An attacker with a normal user account could access another customer's records because the application doesn't properly check ownership on a specific request.
That is far more useful than a generic label and a number.
What your team should do after reading it
Do not treat the report like a trophy for procurement or compliance. Use it as a work plan.
Start here:
- Fix critical and high-risk issues first
- Confirm ownership so each finding has a person responsible
- Track remediation dates inside Jira, ServiceNow, or your existing workflow
- Retest important fixes instead of assuming they worked
- Keep the report for auditors and customers because they'll ask for it again
The best reports reduce confusion. They don't bury your team in screenshots with no explanation.
Why Our Manual Pentesting Is So Affordable
Most companies don't need a giant consulting firm. They need competent testers, a clean process, and a fair price.
The problem is that many buyers assume expensive means thorough. In penetration testing, that's often false.
Where the cost usually comes from
Big firms charge for a lot of things that don't improve the test. Office overhead, extra management layers, brand markup, slow procurement motions, and too many meetings all get baked into the quote.
You shouldn't fund that just to get a basic pen test.
A lean provider can keep pricing lower by doing the opposite:
- Remote-first delivery instead of expensive travel and office overhead
- Small, experienced teams instead of large account structures
- Direct tester access instead of salespeople relaying technical questions badly
- Focused scope control so you test what matters first
- Fast reporting so the work doesn't sprawl into avoidable cost
The ROI question most vendors dodge
This part gets ignored far too often. A key gap in the market is the lack of practical ROI guidance for buyers. As Bridewell notes, security content often says penetration testing prevents financial loss but fails to give budget-conscious SMBs a clear way to compare the cost of a test against the impact of a breach.
That means you need your own common sense.
If a penetration test helps you close an audit, satisfy a customer review, catch a serious flaw before release, or avoid paying for a report rewrite, it already has business value. You don't need fake ROI math to see that.
What you do need is a provider that doesn't waste your budget.
Questions to ask before you buy
Use this checklist when comparing cyber security penetration testing services.
- Who performs the test. Ask whether certified pentesters with OSCP, CEH, or CREST credentials do the work.
- How much is manual. If they can't explain the human testing portion clearly, keep looking.
- How fast is the report. Long delays make findings less useful.
- What does the report include. You want evidence, business impact, and fix guidance.
- Is retesting included. Many firms treat retesting like a surprise upsell.
- How simple is scoping. If getting a quote feels painful, delivery usually will too.
If you want a grounded view of pricing factors, this breakdown of how much penetration testing costs is worth reviewing.
Cheap junk is a bad buy. Overpriced slow testing is also a bad buy. The sweet spot is manual, certified, fast, and clearly scoped.
If you need a penetration test that is affordable, manual, fast, and built for compliance, talk to Affordable Pentesting through the contact form. You'll get direct answers, certified testers, and a report your team can use without waiting around for enterprise nonsense.
.svg)
