Need to prove HIPAA compliance for an audit or a client? A HIPAA Security Risk Assessment is a mandatory, in-depth review that healthcare organizations must perform. Its goal is to find and fix security weaknesses that could expose sensitive patient data, fast.
Think of it as a required safety inspection for your systems. It's about protecting electronic protected health information (ePHI) from all threats. It is the absolute first step in building a HIPAA-compliant security program that actually works.
Understanding The Purpose Of A HIPAA Risk Assessment
At its core, the purpose of a HIPAA Security Risk Assessment is simple: protect patient data. This is not just about checking boxes for an audit. It's about proactively defending your organization against real-world threats that lead to data breaches and massive fines.
The process is a non-negotiable requirement of the HIPAA Security Rule. It applies to both Covered Entities like hospitals and their Business Associates like software vendors. Failing to conduct and document one is the fastest way to get hit with penalties from the Office for Civil Rights (OCR).
Who Needs to Conduct This Assessment
The rule casts a wide net. If your organization creates, receives, maintains, or transmits ePHI, you are required by law to conduct a regular HIPAA Security Risk Assessment. This includes Covered Entities like healthcare providers and Business Associates like IT providers or billing companies.
The HIPAA Security Rule specifically mandates an "accurate and thorough assessment" of all potential risks. A proper assessment is the foundation of your security strategy. It shows you where sensitive data lives, what threats could compromise it, and how well your current defenses are actually working.
Core Components of a HIPAA Security Risk Assessment
A risk assessment provides a clear roadmap. It lets you prioritize the biggest risks and implement controls that deliver the most protection. For a deeper look into specific security measures, see our guide on penetration testing for the healthcare industry.
Without this systematic review, you’re just guessing. You could be spending money on expensive security tools that don’t address your biggest vulnerabilities, while leaving critical gaps wide open for an attacker to exploit. This is a common and costly mistake.
How to Conduct Your Security Risk Assessment
Conducting a HIPAA security risk assessment can feel like a huge task. But breaking it down into manageable steps makes it straightforward. The process is built on a simple truth: you can't protect what you don't know you have.
This isn't just a compliance task. It's about methodically securing every corner of your digital world where ePHI is handled. A structured approach turns this complex requirement into an actionable project that genuinely strengthens your organization's security.
Step 1 Define Your Scope
Before you assess any risk, you have to know what you’re assessing. Defining your scope means identifying every single place where electronic protected health information (ePHI) is created, received, stored, or transmitted. You need a complete inventory.
This involves mapping out all systems and applications like EHRs and billing software. It also includes all hardware like servers and laptops, and all data storage locations, from on-site servers to cloud services. Don't forget removable media like USB drives.
Step 2 Identify Threats and Vulnerabilities
Now you know where your ePHI lives. The next step is to brainstorm everything that could go wrong. This means identifying both threats (the "what") and vulnerabilities (the "how"). Ransomware is a threat, but an unpatched server is the vulnerability that lets it in.
You have to think about threats from every angle. Consider natural disasters, system failures, and human actions, both malicious and accidental. This infographic shows how the three core HIPAA safeguards work together to counter these threats.
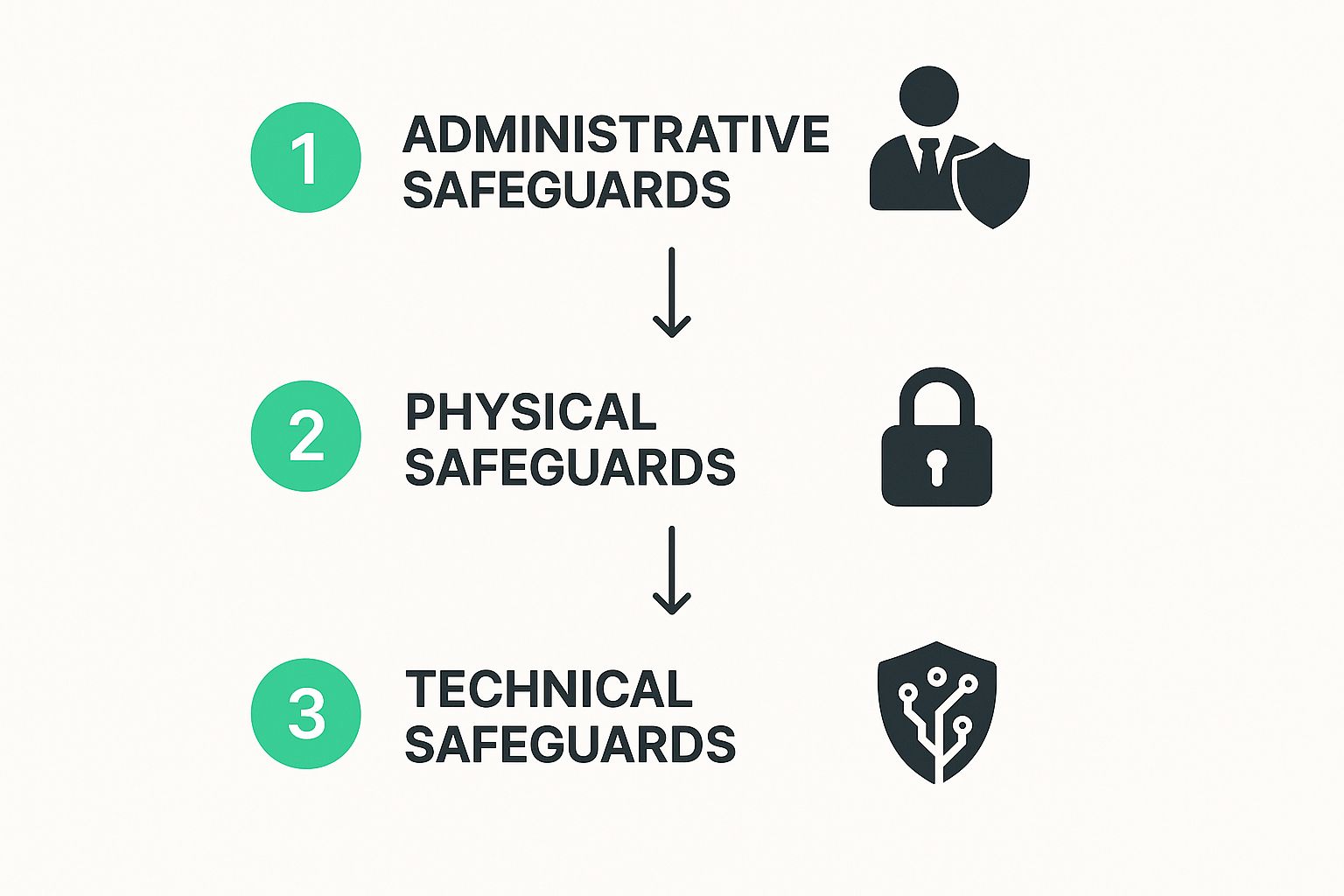
Security is all about layered defense. It starts with your policies (Administrative), moves to physical access controls (Physical), and finishes with your digital protections (Technical). A strong defense addresses all three areas.
Step 3 Assess Your Current Security Measures
With a picture of your assets and dangers, it's time to review the protections you already have. This step is about reviewing your existing security controls to see how well they stack up against the threats and vulnerabilities you identified.
Your review must cover all three HIPAA safeguards. This includes Administrative Safeguards like training and incident response plans. It also covers Physical Safeguards like locked server rooms and Technical Safeguards like encryption and firewalls.
Step 4 Determine Likelihood and Impact
Not all risks are created equal. In this step, you analyze the likelihood that a specific threat will happen and the potential impact it would have if it did. This analysis helps you prioritize what to fix first.
The likelihood of a major earthquake might be low, but the impact would be catastrophic. The likelihood of an employee clicking a phishing link is probably high, but the impact could range from minor to a full-blown data breach. For more on security strategies, see these penetration testing best practices.
Step 5 Calculate and Document Your Risk Level
Finally, you put it all together. Combine the likelihood and impact assessments to assign a risk level (low, medium, high) to each threat-vulnerability pair. This scoring system gives you a prioritized to-do list.
A high-risk item, like unencrypted patient data on laptops, demands immediate action. The most important part? Document everything. This documentation is your proof of compliance for HIPAA auditors and the roadmap for your future risk management.
Identifying and Categorizing Risks to Patient Data

Before you conduct a HIPAA security risk assessment, you must know what you’re looking for. Risks aren't just about hackers; they’re hiding in your daily operations. The best way to find them is to break them down into three categories: Technical, Physical, and Administrative.
A threat is the potential storm, like a hacker. A vulnerability is the leaky roof, like an unpatched system. Your job in a HIPAA security risk assessment is to find and fix those leaky roofs before the storm hits.
Common Threats and Vulnerabilities in Healthcare
Technical risks are weaknesses in your technology. Common examples include unpatched software, weak passwords, lack of encryption, and improper access controls. These are common, dangerous, and can be exploited by an attacker anywhere in the world.
Physical risks involve tangible threats to your hardware. This includes unlocked server rooms, unsecured workstations, lost devices, and improper device disposal. Physical security is just as important as digital security.
Administrative Risks in Your Policies
Administrative risks are gaps in your policies and procedures. These are often the most overlooked vulnerabilities but frequently cause major security incidents. A great firewall is useless if your team isn't trained to spot a phishing email.
The huge increase in ransomware breaches shows that administrative gaps are being exploited. These attacks often succeed because organizations have outdated HIPAA risk analyses. You can learn more about this increased focus on security risk analysis and what it means for you.
Building Your Risk Management Action Plan
Finding risks is only half the battle. A completed HIPAA security risk assessment is just a list of problems until you create a plan to solve them. This is where you turn findings into real security improvements.
The goal is to create a living document that guides your security efforts. It should clearly prioritize which issues to tackle first based on risk scores. This ensures you address the most critical threats to patient data before they become breaches.
Prioritizing Your Findings
Your risk assessment likely uncovered a mix of high, medium, and low-risk issues. You have to prioritize. Focus your immediate attention and resources on the vulnerabilities with the highest risk scores.
An unencrypted database holding thousands of patient records is a top priority. A missing policy for a rarely used app is not. This prioritized list becomes your roadmap, telling your team exactly what to work on and in what order.
Choosing Your Risk Treatment Strategy
For every risk you’ve identified, you have four strategies to choose from. You can remediate the problem by fixing it directly, like patching a server. You can mitigate the risk to reduce its impact, such as through employee training.
Another option is to transfer the risk, often by buying cyber liability insurance. Finally, for very low-impact risks, you might accept them. This must be a conscious, documented decision, not an oversight. Your plan should document which strategy you'll apply to each risk.
Creating a Living Document
Your Risk Management Plan is not a one-and-done document. It's a dynamic tool that should be reviewed and updated constantly as your environment changes. It should detail the risk, strategy, action steps, owner, timeline, and status for each item.
This structure creates accountability and proves your due diligence to regulators. It shows your HIPAA security risk assessment was the start of an ongoing process. Integrating regular checks, like automated penetration testing, helps you validate that your fixes are working.
The Real Costs of an Inadequate Risk Assessment

Failing to perform a proper HIPAA security risk assessment isn't a minor slip-up. It's a massive business risk with severe consequences. Skipping or rushing this process is one of the most expensive gambles a healthcare organization can take.
The Office for Civil Rights (OCR) does not take kindly to willful neglect. One of the most common and heavily penalized violations is the failure to conduct a thorough and accurate risk assessment. Penalties can easily climb into the millions of dollars.
Corrective Action Plans and Ongoing Scrutiny
The financial penalties are just the beginning. The OCR often imposes a multi-year Corrective Action Plan (CAP). A CAP is an expensive and intrusive process where the government dictates your security program, involving mandatory audits and training.
This isn't just a slap on the wrist. A CAP can divert critical resources and staff attention for years. An inadequate risk assessment signals to auditors that security is not a priority, making your organization an easy target for enforcement.
The True Financial Impact
The direct costs are just one piece of the puzzle. HHS and the OCR launched a 'Risk Analysis Initiative' specifically targeting these failures. This led to penalties ranging from $25,000 to as high as $3 million for a supplier that failed to assess its risks. You can read more about these HIPAA penalties and the enforcement trends on Ogletree.com.
Beyond the fines lies a cost that's much harder to measure: the loss of patient trust. When a breach happens because you neglected your HIPAA security risk assessment, it sends a clear message that you were careless. Once that trust is broken, it's nearly impossible to get back.
Common Questions About HIPAA Risk Assessments
The details of a HIPAA security risk assessment can be tricky. Getting these details right is crucial, since a misunderstanding can create a serious compliance gap. We’ve pulled together the most common questions and answered them directly.
A proper risk assessment is a foundational part of any compliance effort, whether for HIPAA, SOC 2, or ISO 27001. Understanding these requirements is key to avoiding fines and protecting your business from expensive breaches.
How Often Do We Need a HIPAA Risk Assessment?
The official HIPAA answer is "periodically," but best practices set a much clearer standard. Your organization should conduct a full HIPAA security risk assessment at least once per year. This annual review ensures your security keeps up with new technology and threats.
You also need to perform an assessment whenever your environment changes significantly. This includes implementing a new EHR system, migrating to a new cloud provider, or after a major security incident. Think of it as an ongoing process, not a one-time task.
What Is the Difference Between a Risk Assessment and a Gap Analysis?
These two terms are often confused, but they are completely different. A HIPAA security risk assessment is a deep-dive discovery process to find all potential threats and vulnerabilities to your ePHI. It’s an investigation to find where your problems are hiding.
A gap analysis compares your existing security controls against a specific standard, like the HIPAA Security Rule, to see what you’re missing. A gap analysis tells you if you have the right controls. A risk assessment tells you if those controls actually work against real-world threats.
Can We Just Use a Template for Our Assessment?
Using a template can be a solid starting point. It gives you a structured framework and helps make sure you don’t miss major risk categories. But you can't only use a generic template.
A true HIPAA security risk assessment must be tailored to your specific organization. Every provider has different systems and unique vulnerabilities. Your final assessment must reflect your organization, not just the boxes on a form.
When Should We Hire a Third-Party Expert?
It’s possible to conduct a HIPAA security risk assessment with your in-house team, but hiring a third-party expert is often a smart move. Consider an expert when you don't have the in-house expertise, need an objective viewpoint, or are preparing for an audit.
Hiring an expert doesn’t mean you have to break the bank. Traditional firms charge $25,000-$50,000 for these services. At Affordable Penetration Testing, our certified experts can provide the help you need without the high price tag, often as part of our penetration testing services.
At Affordable Pentesting, we know that a comprehensive security posture includes more than just a risk assessment. We provide fast, affordable, and certified penetration testing services to validate your security controls and find vulnerabilities before attackers do. Get started in 24-48 hours and receive your full report in just 5 days.
.svg)
