TL;DR: A penetration test can cost anywhere from $4,000 for a simple web app test to over $50,000 for a complex environment, and most companies should budget between $10,000 and $30,000. This guide breaks down what drives that price and how to get a fast, affordable pen test without the traditional firm markup.
You’re probably here because someone asked for a pentest. Maybe it’s for SOC 2, PCI DSS, HIPAA, or a security review from a customer who won’t sign until they see a report. Then the quotes start coming in, and suddenly a basic security requirement turns into a bloated consulting project.
That’s the part that irritates me.
A lot of penetration testing firms still sell like it’s 2015. Long scoping calls. Vague proposals. Big logos. Slow delivery. Then you pay a premium and get a report that reads like an exported scanner dump. That’s not what you need. You need a real penetration test, done by certified people, at a price that makes sense, with a report you can put to use.
Why You Need a Pentest Without the High Price
The old model is expensive because it carries expensive baggage. You’re often paying for layers of sales people, project managers, account handoffs, and brand markup. That doesn’t make the actual penetration testing better.
The demand is real. The global penetration testing market is valued at USD 2.74 billion, and a standard penetration test averages around $18,300, while the global average data breach cost is $4.44 million, according to Bright Defense penetration testing statistics. The point is simple. A pentest is usually cheap compared to the damage from getting security wrong.
That still doesn’t mean you should overpay.
What companies actually need
Most buyers are not looking for a giant consulting engagement. They need a few practical things:
- A compliance-ready report that an auditor or customer can review
- Manual validation so the findings are real
- Clear remediation steps so engineers know what to fix
- Fast turnaround because audits and deals don’t wait
- A price they can defend to finance or leadership
If that sounds obvious, good. It should be obvious. But too many firms make it harder than it needs to be.
Practical rule: If a quote is vague, the final invoice usually gets worse.
A good pen test should support broader cybersecurity and data protection work, not become a budgeting headache by itself. Security reviews are supposed to reduce risk, not create procurement drama.
Why high price often means overhead
A higher quote can reflect a larger scope. That’s fair. But a lot of expensive proposals are just padded. You’ll see long timelines, unclear deliverables, and a lot of language that sounds impressive but says very little about what the testers will do.
Here’s my blunt take. If you’re a startup, SMB, or mid-market team with a web app, API, cloud stack, or internal network, you usually don’t need enterprise theater. You need skilled testers with certifications like OSCP, CEH, and CREST, a defined scope, and a report in your hands within a week of testing finishing.
That’s the better path. Less fluff. More signal. Lower cost.
Understanding Common Penetration Test Pricing Models
Pricing is where buyers get trapped. Not because pentesting is mysterious, but because vendors make it sound mysterious. Most quotes fall into a handful of models.
Flat fee pricing
This is the model I trust most for most compliance and SMB work. You agree on scope, deliverables, and price before the test starts. No guessing. No billing surprises halfway through.
Flat fee works best when the target is clear. One web app, one API environment, one internal network segment, one mobile app. If the scope is defined well, this model is simple and fair.
It also makes internal budgeting easier. Finance likes fixed numbers. CISOs like not getting ambushed.
If you want a practical benchmark for how vendors frame these quotes, review this guide on pen testing price models.
Hourly and daily pricing
Regarding pricing, things get slippery. Some firms quote by the hour or by the day, and many sources cite day rates of $1,000 to $3,000, but hidden costs like remediation re-testing or travel fees for internal tests often get left out, as noted by Intruder’s breakdown of pentest pricing.
That means the number you see first is not always the number you pay.
Hourly or daily billing can make sense for open-ended work or unusual environments. But if you’re trying to answer the question “how much does penetration testing cost” before getting internal approval, this model is a pain. The bill can expand as scope expands, and scope almost always expands when nobody locked it down properly.
When a vendor sells time instead of outcomes, you carry more of the risk.
Per target pricing
This model charges by asset. One web app. One mobile app. One external IP range. One API set. It’s easy to understand and often works well when your environment is small and well defined.
The downside is that “target” can get fuzzy fast. Is staging included? Are admin panels included? Are authenticated user roles included? Does one API mean one gateway, or all underlying services?
Per target pricing is only clean when the statement of work is clean.
Subscription or ongoing pricing
Some vendors offer recurring or subscription-style penetration testing. The pitch is predictability. That part is valid. If you release often or need repeated testing for compliance, an ongoing model can be easier to plan around.
The problem is that transparent pricing data is scarce. So while the total cost of ownership may be more predictable, buyers still need to ask hard questions about retests, scope changes, and report updates.
What I recommend
For most startups and SMBs, choose flat-fee manual penetration testing with a very specific scope and explicit deliverables. It’s the easiest model to compare, the easiest to budget, and the hardest for vendors to hide behind.
Ask for these in writing:
- Scope boundaries so everyone knows what is and is not included
- Testing method so you know whether it’s black box, grey box, or white box
- Retest terms so remediation doesn’t trigger surprise fees
- Delivery timeline so the report arrives when you need it
That’s how you stop buying mystery and start buying work.
How Much a Penetration Test Costs By Type
This is often the first question that arises. The answer depends on what you’re testing. A web app pentest is priced differently from an internal network pen test. A cloud review is not the same as a mobile app assessment.
Use this infographic as a quick reference.
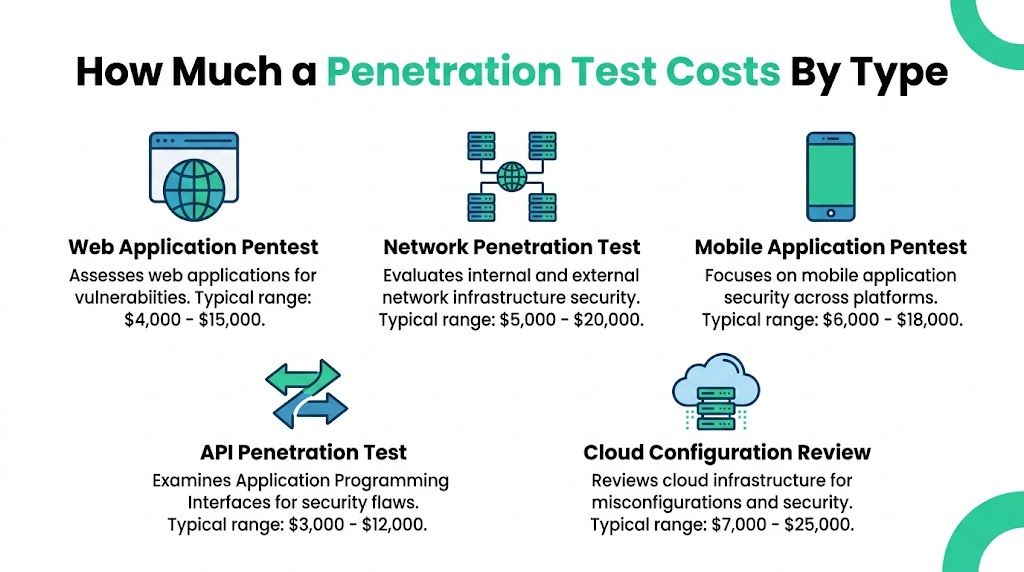
Typical penetration testing costs average $5,000 to $30,000 for web apps, $7,000 to $25,000 for networks, and $5,000 to $30,000 for APIs. Small businesses can find simple web app tests for $4,000 to $10,000, while medium-sized firms should budget $10,000 to $50,000 for broader scopes, according to DeepStrike’s 2025 pen testing FAQ.
Web application pentest cost
This is the most common request. If you sell software, take logins, process customer data, or have a customer portal, this is usually where you start.
For a simple web app, small businesses can often get testing in the $4,000 to $10,000 range. More involved web applications usually land in the broader $5,000 to $30,000 range.
That spread exists for a reason. A five-page marketing site with one login flow is not the same as a multi-role SaaS platform with admin access, complex business logic, and dozens of authenticated features.
Network penetration test cost
Network testing usually sits in the $7,000 to $25,000 range. That can cover internal or external infrastructure depending on scope.
For SMBs, this often means validating firewalls, exposed services, weak credentials, segmentation, and lateral movement risk. For bigger environments, complexity rises quickly because the testers have more systems, trust paths, and access controls to map.
API penetration test cost
API testing is often underestimated, which is a mistake. A lot of modern apps are mostly APIs with a user interface attached.
Typical API penetration testing falls in the $5,000 to $30,000 range. The price depends heavily on endpoint count, authentication flows, user roles, and whether the testers need to validate business logic flaws instead of just input handling.
If your app is mobile-first, SaaS, or partner-integrated, don’t treat the API as optional scope.
Mobile app and cloud testing cost
Mobile app testing and cloud testing are usually more specialized. The verified pricing data puts mobile apps at $12,000 to $35,000 and cloud at $10,000 to $50,000 in common 2025 cost guides. Mobile costs are often per platform, so iOS and Android can affect scope differently. Cloud costs rise when IAM, storage, containers, and multiple services are involved.
A lot of buyers miss this. The app may look simple from the outside, but if the security risk sits in the cloud environment or API layer, the cheap quote for “just the frontend” won’t help much.
Ballpark costs by test type
| Test Type | Typical Range for SMBs | Key Focus Area |
|---|---|---|
| Web application pentest | $4,000 to $10,000 for simple scope, broader web app testing often falls in $5,000 to $30,000 | Authentication, access control, business logic, input handling |
| Network penetration test | $7,000 to $25,000 | External exposure, segmentation, weak credentials, lateral movement |
| API penetration test | $5,000 to $30,000 | Authorization, token handling, endpoint abuse, data exposure |
| Mobile application pentest | $12,000 to $35,000 | Local storage, transport security, app logic, backend interaction |
| Cloud penetration testing | $10,000 to $50,000 | IAM, storage access, configuration weaknesses, cloud attack paths |
What most companies should budget
If you’re a startup or mid-sized company with one primary customer-facing product, budget in the $10,000 to $30,000 band unless your environment is unusually simple or unusually complex. That’s the zone where you can usually get a real manual penetration test instead of a dressed-up scan.
If you’re not sure which kind of testing you need, this breakdown of penetration testing types is a useful way to map the test to your environment before you ask for quotes.
The biggest pricing mistake I see is buying the wrong test, not just paying too much for the right one. Companies ask for a network pentest when the actual risk is in the app. Or they buy a web app pentest while leaving the API out of scope. Then they wonder why the report doesn’t answer the questions their auditor or customer asked.
Buy the right test first. Then optimize price.
Key Factors That Influence Your Pentest Price
Two quotes can look wildly different even when both say “penetration test.” That’s because the label is broad, but the work underneath it changes a lot. Scope, method, environment, and reporting requirements all move the price.

Internal network penetration testing typically costs $6,000 to $20,000, while external tests usually fall between $4,000 and $15,000, because internal work often requires on-site presence and deeper manual analysis to uncover issues like misconfigured Active Directory, according to Strike Graph’s pentest cost guide.
Scope drives most of the cost
This is the biggest lever. More pages, more endpoints, more user roles, more environments, more infrastructure. All of that means more tester time.
A narrow scope keeps cost in check. A sloppy scope does the opposite. If you say “test our app,” that could mean almost anything. If you say “test production web app with admin and user roles, plus authenticated API endpoints used by the app,” you’re giving the vendor something that can be priced.
Here’s the blunt version:
- Small scope usually means one app or one target with limited complexity
- Medium scope often includes multiple roles, more workflows, or connected services
- Large scope brings several assets together, such as app, API, cloud, and internal network
Methodology changes effort
The testing method matters. Black box means the tester starts with little or no internal information. Grey box means they get some access or context. White box means they get deeper visibility, such as credentials, architecture details, or source material.
That affects price because it affects effort.
Black box can require more time for recon. White box can uncover deeper issues more efficiently. Grey box is often the practical middle ground for compliance work because it mirrors a realistic attacker who already has some access.
A good quote should tell you which method is included. If it doesn’t, ask before you sign.
Internal work costs more for a reason
Internal pen testing is not just external testing from a different seat. Testers need to understand trust relationships, user permissions, network paths, and what an attacker could do once inside.
That’s why internal tests usually cost more than external ones. There’s more manual work, more context to build, and often more coordination.
Certifications and experience matter
You are paying for judgment, not just time. A certified tester with OSCP, CEH, or CREST credentials is more likely to separate real risk from noise and produce a report your team can trust.
That doesn’t mean you should blindly pay any premium attached to those letters. It does mean the people doing the work should be qualified, and the vendor should say that clearly.
A cheap quote from junior staff using mostly automated tools is how companies end up with low-value reports and almost no meaningful findings.
Compliance reporting affects the quote
Some buyers only need a technical report for internal remediation. Others need a report that stands up in a SOC 2, PCI DSS, HIPAA, or ISO 27001 context. That usually means more structure, more evidence, and cleaner documentation.
If compliance is your reason for testing, say that upfront. The report format matters just as much as the testing itself.
Timeline can raise or lower the pain
Urgent requests are common. Audits move. Customer deals stall. Boards ask questions late. A vendor that can test quickly and deliver within a week is valuable because speed solves a real business problem.
But speed should come from an efficient process, not from cutting corners. You want focused manual testing with a clear scope, not a rushed scan attached to a polished PDF.
What to Expect in Your Pentest Deliverables
If you’re paying for a penetration test, the report is not an afterthought. It is the product. The testing matters, of course, but what your team receives at the end determines whether the work helps engineering, satisfies compliance, and answers customer questions.
What a useful report includes
A solid penetration testing report should include:
- Executive summary that explains the main risks in plain English for leadership and auditors
- Scope and methodology so reviewers know what was tested and how the testers approached it
- Detailed findings with proof, impact, and enough context for engineers to reproduce or understand the issue
- Risk ratings to help the team prioritize fixes
- Remediation guidance that tells your people what to change, not just what went wrong
If those pieces are missing, the report loses value fast.
What a bad report looks like
You’ve probably seen these. Fifty pages of screenshots. Generic vulnerability names. No explanation of business impact. No clear next step. Half the “findings” are informational noise from automated scanning tools.
That is not a real deliverable. That is evidence that someone pressed a button.
A proper pen test report should feel human. The tester should clearly understand your environment, validate findings manually, and explain risk in language your engineering and compliance teams can use.
The best report is the one your developers can act on without scheduling three follow-up meetings.
Why remediation detail matters
A finding without remediation is just an alarm bell. Engineers need to know whether the issue is in access control, session handling, cloud configuration, API authorization, or something else. They also need enough detail to confirm the fix later.
That’s why manual penetration testing still matters. A person can verify exploitability, cut false positives, and write findings that are useful. An automated output usually cannot.
Fast delivery is part of the value
A lot of firms drag out reporting. That’s wasteful. If testing is scoped properly, you should not be waiting forever to see results. A fast turnaround is especially important when the report is tied to an audit, insurance request, procurement review, or customer questionnaire.
You’re not paying for a document to sit in a queue. You’re paying for clarity and next steps. Good vendors know that and move quickly.
Negotiation and Smart Procurement Tips for Pentesting
A lot of bad pentest buying happens before testing even starts. The quote is fuzzy, the scope is vague, and everyone assumes the other side means the same thing. Then the bill grows, the report disappoints, and the deadline still doesn’t move.
You can avoid most of that with better procurement discipline.
Ask sharper questions
Don’t start with “What’s your cheapest pentest?” Start with “What exactly is included?” You want the vendor to explain scope, method, deliverables, retesting, and timeline in writing.
Ask these directly:
- Who is doing the testing and what certifications do they hold
- Whether the work is manual or mostly automated
- What report format you’ll receive for compliance or customer review
- Whether retesting costs extra after your team fixes findings
- How long report delivery takes after testing ends
If the answers are soft, the quote is soft.
Compare proposals the right way
A lower quote isn’t always cheaper if it excludes the part you require. One vendor may include manual validation, remediation guidance, and compliance-ready reporting. Another may give you a lower price because they stripped all of that out.
Compare proposals side by side by asking:
| What to Compare | Why It Matters |
|---|---|
| Scope detail | Stops surprise expansion later |
| Methodology | Tells you whether the test is realistic and useful |
| Deliverables | Determines whether the report helps audit and engineering |
| Retest terms | Prevents hidden costs after remediation |
| Timeline | Keeps audits and deals moving |
Don’t ignore ROI
Most pentest cost guides still fail to show ROI clearly. But the value is not just the test itself. It’s avoiding failed audits, compliance friction, and the average $10.22 million cost of a data breach in the U.S., which makes a $10,000 to $30,000 test a strong investment, as noted in VikingCloud’s discussion of pentest cost and ROI gaps.
That’s the frame leadership should understand. Not “security spend.” Risk reduction with business consequences.
Buy the pentest that answers the business need. Don’t buy the one that just looks cheapest on page one.
My procurement advice
Put the scope in writing first. Force clarity before pricing. Then insist on a flat-fee quote unless the engagement is open-ended.
Also, don’t get dazzled by a giant consulting brand. A lean firm with certified testers, clear scoping, and fast reporting often gives you better value than a large shop selling overhead.
How We Provide Affordable Manual Pentests
Traditional pentesting is often expensive for the wrong reasons. Too many layers. Too much process. Too much waiting. That’s how a straightforward penetration test turns into a bloated engagement.
The better model is lean. Keep the scope clear, keep the pricing flat, and put certified testers on the work. That’s how you cut waste without cutting quality.
What a lean model looks like
Affordable Pentesting offers manual pentesting services for companies that need compliance-focused testing without enterprise overhead. The focus is on manual testing by certified professionals, including OSCP, CEH, and CREST, with transparent pricing and reports delivered within a week.
That approach makes sense for startups, SMBs, and teams preparing for SOC 2, PCI DSS, HIPAA, or ISO 27001 reviews. You don’t need a month of ceremony. You need a real pen test, usable findings, and a report that helps you move.
My recommendation
If you’re evaluating vendors, favor the one that gives you these things plainly:
- A fixed quote
- A clearly defined scope
- Manual testing by certified pentesters
- A report your auditor and engineers can both use
- Delivery fast enough to match your business timeline
If a vendor can’t do that, keep looking. Use the contact form and get a quote from a team that respects your time and budget.
Common Questions About Penetration Testing Costs
Is a vulnerability scan the same as a pentest
No. A vulnerability scan is mostly automated and usually flags possible issues. A pentest goes further by having a human tester validate findings, follow attack paths, and show what an attacker could do. If you need evidence for compliance or customer trust, that difference matters.
Why does manual penetration testing matter
Because scanners don’t think. They miss business logic flaws, chained weaknesses, and context-specific abuse paths. Manual pen testing is what turns a pile of alerts into real security analysis.
How often should we get penetration testing
That depends on your compliance obligations, release cycle, and customer expectations. Many teams test before audits, after major changes, or when launching new products and features. If your environment changes often, one test a year may not be enough.
Can a cheap pentest still be good
Yes, if the price is low because the vendor cut overhead instead of cutting the actual testing. No, if the low price means you’re getting an automated scan dressed up as a penetration test.
What’s the safest buying decision
Choose a provider that scopes tightly, prices clearly, uses certified testers, and delivers quickly. That’s how you control cost without gambling on quality.
If you need a fast quote for a manual pen test, Affordable Pentesting is built for teams that want clear pricing, certified testers, and compliance-ready reports without the usual consulting overhead. Use the contact form to get a straightforward quote and stop wasting time on vague proposals.
.svg)
