Let's be direct. The phrase "information security audit" probably makes you think of a slow, expensive headache. That’s the old way of thinking. An information security audit is just a health checkup for your company's digital security. It’s not about passing or failing. It’s about finding and fixing security problems before they become business-ending disasters.
For IT managers and startup founders, the fear is always the same: audits are slow, complicated, and will destroy your budget. But a good audit is your best tool for protecting your business and building trust with customers.
Your Guide to Fast and Affordable Security Audits

So what is an information security audit? It's a review of your company's security rules and tech setup. The auditor's job is to check that your defenses actually work and that you're protecting sensitive data. For CISOs, this is how you prove your security works to the board and regulators.
For a startup founder, a clean audit report is how you prove to investors and big clients that you're a safe bet. It’s the difference between saying you're secure and proving it. This guide shows you how to get through an audit efficiently, without the high prices and long waits.
Why Audits Are a Business Necessity
If you see an audit as just another box to check, you're missing the point and taking a huge risk. The real goal of an information security audit is to prevent a data breach that could ruin your company's finances and reputation. It’s a smart investment in your future.
The numbers are scary. Cybercrime costs are expected to hit $10.5 trillion a year by 2025. A single data breach now costs an average of $4.88 million. These facts make it clear that a good audit isn't just paperwork, it's a vital business strategy.
Connecting Audits to Real Security
So, what does an auditor actually look at? Pretty much everything. They will review your password rules, your plans for handling a breach, and the settings on your servers. The goal is to get a complete picture of your security.
But let's be real, policies and interviews only tell part of the story. This is where a penetration test becomes a key part of any serious audit. A penetration test, or pen test, is where an ethical hacker tries to find and use weak spots in your systems, just like a real attacker. It provides solid proof of your security gaps.
Overcoming Common Audit Frustrations
We hear the same complaints all the time from startups and IT managers frustrated with traditional firms. The problems are always the same: sky-high prices, painfully slow timelines, and reports with no useful findings. You get a huge bill for a report that arrives months later and is filled with junk from an automated scanner.
We solve these problems. We offer affordable, manual penetration testing with clear reports delivered in under a week. Our pentesters are certified experts (OSCP, CEH, CREST) who find the real-world vulnerabilities that matter. An audit shouldn't be a painful, check-the-box exercise.
Choosing The Right Audit For You
Not all security audits are the same. Knowing the difference helps you get what you need without wasting time and money. Are you just trying to improve your own security, prove your defenses to a client, or meet a strict deadline like SOC 2? Each goal needs a different type of audit.
Think of it like this. Sometimes you check your car's oil yourself. Other times, you need a mechanic for a full inspection. Let's break down which is which.
Internal Audits for a Security Health Check
An internal audit is when your own team checks your security. You're basically grading your own homework. The goal is simple: find and fix your own weaknesses before they become a real problem.
This kind of information security audit is a great, cheap way to see where you stand. It’s perfect for getting your house in order before a formal audit. The only downside is that because your own team does it, the results don't have the independent validation that customers or regulators demand.
External Audits for an Unbiased Opinion
This is when you hire an independent, third-party firm to review your security. Their job is to give an unbiased opinion, which is why their findings carry so much weight with customers and investors. This is how you build trust.
An external audit is required when you're aiming for a certification like SOC 2 or ISO 27001. The final report is the independent proof that your security controls are actually working.
Compliance Audits for Following The Rules
A compliance audit has one single goal: to check if you're following the specific rules of a law or industry standard. This isn't about general security advice; it's a pass/fail test against a strict checklist.
Are you protecting credit card data according to PCI DSS? Safeguarding patient records as required by HIPAA? These audits are mandatory for businesses in regulated industries. Failing them can lead to huge fines and a total loss of customer trust.
How Audits Help Meet Compliance Frameworks
Let's connect an information security audit to your compliance goals. Frameworks like SOC 2, PCI DSS, and HIPAA all require you to prove your security controls work. An audit, especially one that includes a penetration test, delivers that proof.
Think of it this way. Compliance frameworks are the rulebook. A security audit is how you prove to the referee that you're playing by the rules. Instead of just saying you're secure, you hand over a report from an expert who tried to break in and couldn't.
Proving Your Security for PCI DSS
If you handle credit card payments, you must follow the Payment Card Industry Data Security Standard (PCI DSS). Its whole purpose is to protect card data. To stay compliant, PCI DSS requires regular vulnerability scans and an annual penetration test.
This is not optional. A pen test satisfies this requirement by actively looking for holes an attacker could use to steal card data. Our certified testers simulate those attacks, giving you the exact report your PCI auditor needs to see.
Meeting HIPAA Requirements for Health Data
For any organization that handles patient data, the Health Insurance Portability and Accountability Act (HIPAA) is the law. The HIPAA Security Rule requires you to conduct regular risk analyses to find threats to patient information. An information security audit is the perfect way to do this.
A penetration test takes it a step further. It proves you not only found risks but also tested your defenses against a real-world attack. This shows regulators you are serious about keeping patient records safe.
Demonstrating Trust with SOC 2
A SOC 2 report is now essential for closing deals with large companies. It tells clients you have solid controls for security, availability, and privacy. A huge part of earning that trust is showing that your security has been independently tested.
This is where a manual pen test is critical. It gives your SOC 2 auditor hard evidence that your systems can fight off an attack. We deliver this proof in a week, so you never miss a deadline. Achieving and maintaining compliance brings huge advantages, as explained in articles like Top 5 Benefits of Meeting Security Compliance in Your Business.
The Growing Focus on Cybersecurity
This demand for technical testing is now the central focus for auditors. Cybersecurity is the number one concern for internal audit teams everywhere. In fact, 69% of internal auditors say cybersecurity is where they spend the most time and effort.
This means a solid pen testing report is no longer a "nice to have," it's essential. It gives modern auditors the technical proof they need to sign off. If you're struggling to understand all this, our guide on what is compliance management can help.
The Security Audit Process Explained
An information security audit can feel like a mystery. The good news is, most audits follow four predictable steps: planning, fieldwork, analysis, and reporting. Once you understand the process, you can focus on getting compliant and securing your business.
Let's break down each step. We’ll show you what to expect and how our fast penetration testing gets you clear results that satisfy auditors without the frustrating delays.
Stage 1: Planning and Scoping the Audit
The first step is about getting everyone on the same page. You and the auditor will define exactly what’s being tested. This is called the audit "scope." A clear scope ensures the audit focuses on what’s truly critical to your business.
This is where you decide which systems and applications are being tested. You'll also clarify your compliance goal, whether it’s for SOC 2, HIPAA, or PCI DSS. Getting the scope right from the start prevents confusion and wasted time later.
Stage 2: Fieldwork and Technical Testing
This is where the real work begins. The auditor starts gathering evidence by interviewing your team and checking your system settings. This part can feel intimidating, but it's just about proving your security controls are working.
This is also where our manual pen test happens. Our OSCP, CEH, and CREST certified pentesters simulate a real attack on the systems you defined in the scope. Unlike automated scanners, our team hunts for high-impact vulnerabilities that pose a genuine threat. Our guide on IT audit checklists can help you prepare.
Stage 3: Analysis of the Audit Findings
Once testing is done, the auditor analyzes all the evidence. They take everything they’ve collected—from interviews, documents, and our penetration testing report—and look for gaps between your security and the compliance rules.
A good auditor assesses the real-world impact of their findings. Our pen testing reports feed directly into this analysis, giving your auditor a clear, prioritized list of vulnerabilities with steps for fixing them. This saves everyone time.
Stage 4: Reporting and Getting Results
The final stage is the report. The auditor puts everything into a formal document that serves as the official record of your information security audit. Traditional firms often take weeks or months to deliver this report, which can stall your sales deals.
We change the game here. We deliver our detailed pen test report within one week of the test finishing. This gives your auditor the critical technical evidence they need, without the wait. You get clear findings fast, so you can start fixing things and finalize your audit without delay.
Why Penetration Testing Is Your Superpower
So, what makes a penetration test the secret weapon for your audit? Think of a standard information security audit as someone checking your building’s blueprints. They confirm you have locks on all the doors and windows.
A pen test is when a security expert actually shows up and tries to pick those locks or find an open door. This hands-on approach finds the critical vulnerabilities that interviews and automated scans always miss. It shows you what a real attacker could actually do.
Going Beyond the Standard Audit Checklist
Auditors are great at checking that your policies exist, but their job isn't to think like a hacker. They check for compliance, not for exploitability. A penetration testing engagement fills that gap by actively simulating an attack.
Our OSCP, CEH, and CREST certified pentesters use their skills to find high-impact issues that deliver real value. We focus on finding the one unlocked window instead of just counting all the locks. This gives your auditor powerful, undeniable proof of your security.
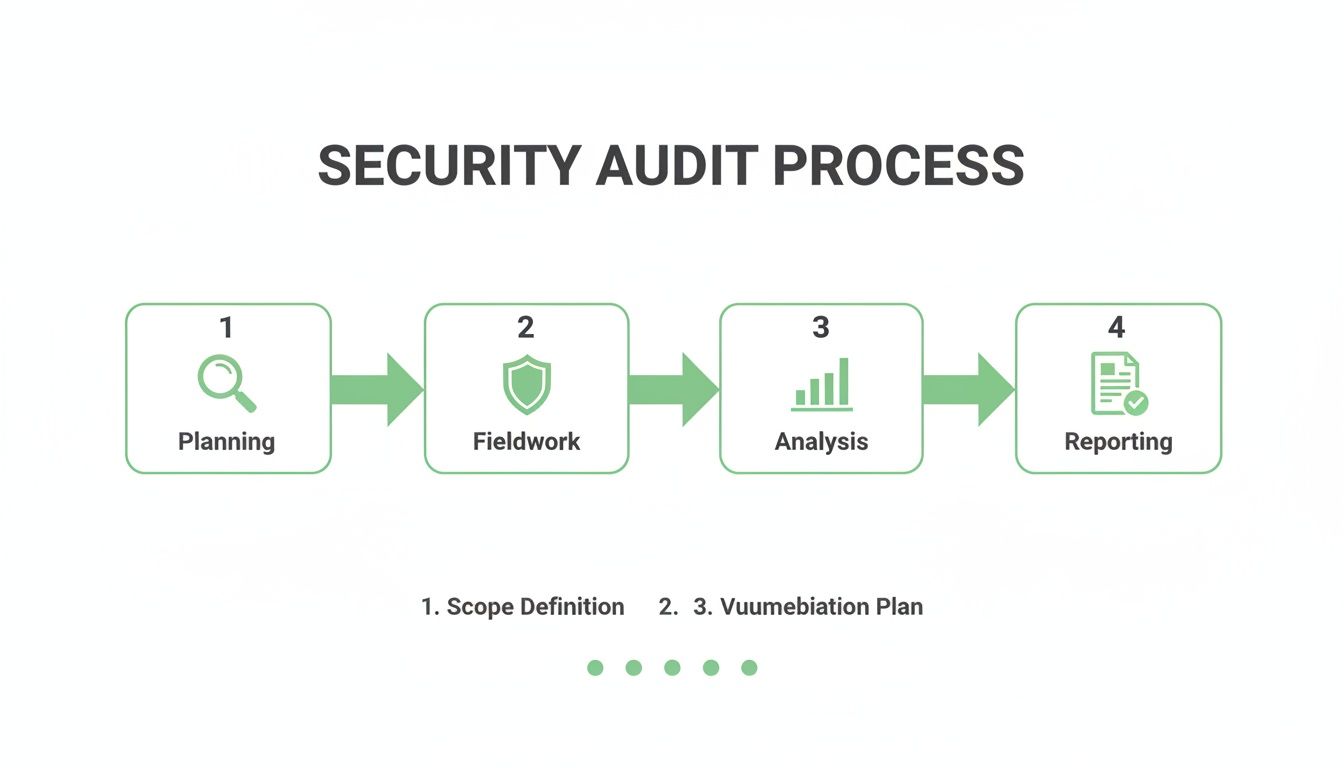
As you can see, a pen test is the core of the "Fieldwork" phase. It provides the real-world data needed for the analysis and reporting that will satisfy your auditor.
Delivering Fast and Affordable Results
We know you're tired of traditional firms that charge a fortune for slow, generic reports. We built our service for IT managers, CISOs, and startup founders who need a high-quality pen test without the enterprise price tag or the long wait.
Our promise is simple: we provide affordable, expert-led penetration testing with meaningful results. You get your report within a week, not months. This speed and affordability mean you can fit a powerful pen test into your audit cycle without wrecking your budget or timeline.
Real-World Threats Need Real-World Testing
The threat from hackers isn't theoretical, and your testing shouldn't be either. Recent data shows 44% of cybersecurity professionals see social engineering as the top attack they face. A solid pen test can expose risks from attacks like phishing websites.
The same survey found that while many pros expect an attack, fewer than half feel confident in their ability to handle it. A good pen test helps close that confidence gap. You can learn more by checking out our guide on penetration testing best practices. A manual pen test from a certified expert transforms your information security audit from a checkbox exercise into a real security improvement.
Picking the Right Partner for a Fast Pentest
When your information security audit requires a penetration test, you have to choose the right partner. Traditional firms are often slow and expensive. They seem built for giant companies, not startups or businesses trying to manage a budget.
We see things differently. Our model is built on three promises: speed, affordability, and quality. You shouldn't have to wait months for a test or a report. We deliver reports within a week at a price that makes sense.
Questions to Ask Any Pentest Provider
To make a smart choice, you have to ask direct questions. Your security and compliance are on the line. Before you sign anything for a pen test, get clear answers to these questions.
Ask them how fast you'll get your final report. If they say "weeks," they will slow you down. You should demand a report in one week or less. Also ask what certifications their pentesters have. You need to hear names like OSCP, CEH, and CREST. This proves they have real hacking skills. Finally, ask if their pricing is built for a company your size. You need affordable, transparent pricing.
Speed and Quality Are Not a Trade-Off
Many people think a fast penetration test means you lose quality. That's a false choice. An experienced team delivers high-quality results quickly because they know what to look for. They don't waste time with noisy, automated scanners that produce thousands of useless findings.
Our certified ethical hackers focus on manual penetration testing to find the high-impact vulnerabilities that matter. That efficiency is how we deliver actionable findings fast without cutting corners. Your information security audit needs real proof of security, not a fluffy report. Ready for a fast, no-nonsense quote for your next pen test? Reach out through our contact form.
Your Security Audit Questions Answered
Have questions about information security audits and pentesting? We have direct answers. We hear these questions all the time from IT managers, CISOs, and founders who just want to get compliant without the drama.
Let's clear things up so you can move forward with confidence. Our goal is to give you practical information that shows our commitment to speed, affordability, and real expertise.
How Much Does a Pen Test for an Audit Cost?
This is the big one. Traditional firms love to quote prices that feel out of reach for anyone but a huge corporation. We built our pricing for startups and SMBs. A penetration test for your audit does not have to break the bank.
The final cost depends on the scope, like how many systems you need tested. But our approach is affordability first. We give you transparent, upfront pricing so you know exactly what you’re paying for. You get a high-quality, audit-ready pen test at a price that works for your budget.
How Long Does a Penetration Test Take?
The other major frustration is the wait. Old-school firms can take months to schedule you, then weeks to deliver a report. This is a huge problem when a compliance deadline or big sales deal is on the line.
We do things differently. Our focused penetration testing process is built for speed. The testing itself usually takes a few days. The best part? We deliver your final, comprehensive report within one week of completion. No more waiting.
What is the Difference in a Vulnerability Scan vs a Pen Test?
This question confuses a lot of people, but it’s an important difference. Think of it this way: a vulnerability scan is like an automated security camera that spots an unlocked door. It’s a good start, but it’s just a list of potential problems with no context.
A manual pen test is when one of our certified ethical hackers (OSCP, CEH, CREST) actually tries to open that door and see what’s inside. It’s a hands-on test of your real-world defenses. It provides the kind of human-driven analysis that auditors value far more than an automated list.
Do I Need a Pen Test for My SOC 2 Audit?
Let’s be direct. A penetration test may not be explicitly required in the SOC 2 standard, but it has become a practical necessity for passing your audit. Your auditor needs proof that your security controls are effective. There is no better evidence than a report from an independent expert who tried to break them.
Handing over a solid pen test report proves your commitment to security and dramatically speeds up the audit process. It gives your customers the confidence they demand. It’s the fastest way to prove your security posture is more than just words in a policy.
At Affordable Pentesting, we provide fast, high-quality, and affordable manual penetration testing to get you compliant. If you're ready for a no-nonsense quote for your next audit, reach out to us through our contact form. https://www.affordablepentesting.com
.svg)
