You’re probably here because someone dropped a compliance requirement on your desk, asked for a pen test report, and the firms you contacted responded with a big quote and an even bigger timeline.
That’s the part of this industry that deserves criticism. Too many network penetration testing services are built for giant enterprises with giant budgets, giant meetings, and giant delays. SMBs and startups get stuck paying for overhead instead of useful testing.
A network pentest should not feel like buying a car from a dealership that won’t show you the price. It should be clear, fast, manual where it matters, and easy to act on. If your provider can’t explain what they’ll test, who’s doing it, when you’ll get the report, and what happens after the findings land, keep looking.
Why You Need a Faster Pentest
It’s Friday afternoon. A customer asks for your pentest report, your auditor wants proof that the network was tested, and the firm you contacted says they can start in three weeks after a discovery call, a scoping workshop, and procurement review. That is exactly how SMBs and startups lose time and money in this market.
You need a pentest that starts quickly, tests the right systems, and gives your team a report they can use immediately. Anything slower is overhead dressed up as rigor.
Slow testing creates business risk
A slow pentest does more than frustrate your team. It holds up audits, drags out customer reviews, delays deals, and leaves known exposure sitting in place while a provider works through its own process.
That enterprise model is a bad fit for smaller companies.
If your goal is to satisfy a requirement, validate internet-facing assets, or check whether internal access controls hold up, speed matters. Waiting weeks to begin a standard network test is usually a sign of the same problem later. Slow reporting. Slow retesting. Slow answers when your team has remediation questions.
Teams also waste money by buying oversized engagements. A provider hands them a bloated proposal, the scope gets padded, and they end up paying for meetings and paperwork instead of focused testing. In many cases, the right answer is narrower and faster: an external network pentest, an internal test after assumed compromise, or a segmentation assessment tied to a specific control.
If you want outside perspective on why a serious security review matters, read Bolstering Your Defense: The Vital Role Of A Thorough Security Assessment. Then keep your buying criteria simple. Choose the test that answers the actual risk or compliance question.
What fast should look like
Fast testing still needs skilled humans and a clear method. It does not need weeks of administrative drag.
A provider built for SMBs should give you:
- Clear scope up front so you know exactly what is being tested
- Manual verification so findings are not just scanner noise pasted into a template
- A short delivery timeline because standard network pentests should not sit in a queue forever
- A report your IT team can act on with clear severity, evidence, and remediation steps
- Plain pricing so you can approve the work without a drawn-out sales process
That is the common-sense model. It is also the affordable one.
If you want a practical example of that buying approach, this overview of an affordable pentest approach shows what faster, tighter-scoped delivery should look like for SMBs and startups.
The point is simple. You are not buying theater. You are buying evidence, speed, and useful findings. If a provider cannot deliver those without enterprise delays and enterprise pricing, keep looking.
The Different Types of Network Pentests Explained
Most buyers don’t need more jargon. They need to know which test matches the problem in front of them.
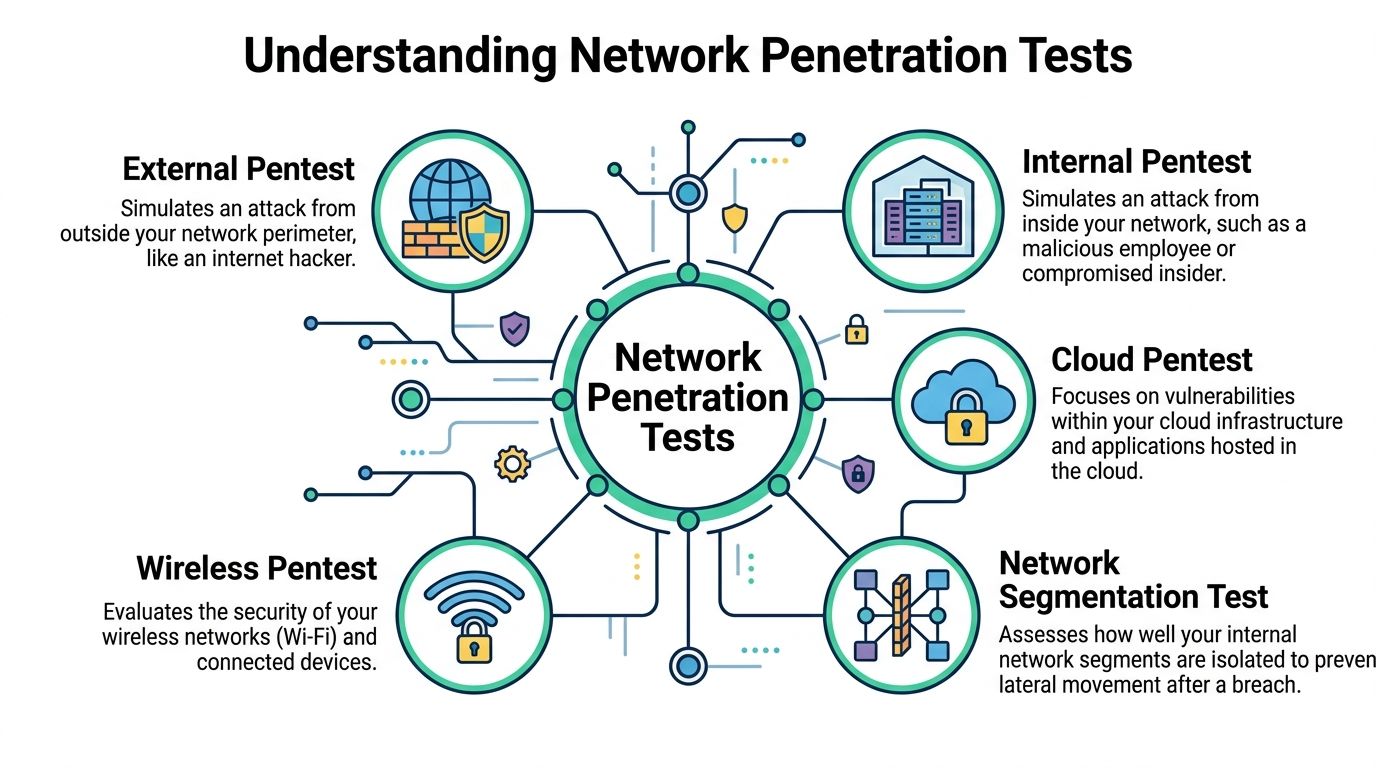
External network pentest
This is the outside-in test, similar to checking every door, window, and garage entrance from the street.
An external penetration test looks at internet-facing systems such as VPNs, firewalls, remote access portals, email gateways, and public services. If an attacker has no employee account and starts from the public internet, this is the test that mirrors that scenario.
You need this if you have:
- Public-facing infrastructure like remote access or hosted services
- Customer security reviews asking for an external pen test
- Compliance requirements that expect internet-exposed assets to be tested
Internal network pentest
This is the “someone got inside” test. Maybe it’s a stolen laptop, a phished employee, a rogue insider, or a contractor on the wrong network.
Internal pentesting shows what happens after that first foothold. Can the attacker move around, find weak permissions, dump credentials, or reach systems that should’ve been isolated?
For many companies, much damage often originates here. Perimeter controls get attention. Flat internal networks get ignored.
If you’re evaluating options, this guide on an internal network pentest is useful for understanding what the engagement should cover.
Cloud pentest
A cloud pen test focuses on hosted infrastructure and the services connected to it. The exact details vary, but the simple version is this: you’re checking whether your cloud setup exposes things it shouldn’t.
That includes access paths, security group mistakes, exposed management interfaces, and weak separation between systems. If your company runs core workloads in a cloud environment, skipping this is asking for trouble.
Wireless pentest
If you run office Wi-Fi, guest Wi-Fi, warehouse wireless networks, or device-heavy environments, wireless testing matters.
This kind of penetration testing checks whether someone nearby could abuse weak wireless security, gain unauthorized access, or pivot from a lower-trust network into something more sensitive. It matters more than many teams think, especially in shared office setups.
Segmentation test
A segmentation test answers a blunt question. If one part of the network gets compromised, do your internal boundaries stop movement?
This matters for environments that separate finance, production, engineering, cardholder data, healthcare systems, or operational technology. A lot of companies say they have “segmentation.” Then testing shows users or systems can still cross boundaries too easily.
Segmentation is not what the diagram says. It’s what the attacker can reach.
Gray box usually beats pure black box
For network penetration testing services, I usually prefer gray box testing over a pure black box exercise. The reason is practical. It wastes less time and finds more meaningful issues inside authenticated systems.
Gray box tests, which simulate an attacker with some internal knowledge, detect 30 to 50 percent more critical vulnerabilities than pure black box tests because testers can move past blind perimeter fumbling and probe real paths faster (White Knight Labs network penetration testing services).
Here’s the plain-English version:
| Test style | What tester gets | Best use |
|---|---|---|
| Black box | Almost no internal info | Outside attacker simulation |
| Gray box | Limited access or partial knowledge | Most SMB and compliance-driven network tests |
| White box | Deep internal detail | Highly targeted validation |
For most SMBs, a gray box penetration test is the common-sense option. It gets to the point faster, gives you better findings, and avoids paying someone to rediscover things your team already knows.
Our Penetration Testing Process From Start to Finish
A good pentest process should be easy to follow. If a provider makes it sound mysterious, they’re usually hiding slow delivery or weak execution.

Kickoff and scope lock
First, we define exactly what’s being tested. That means assets, access method, testing window, rules of engagement, and who to contact if something unusual shows up.
This part should be short and disciplined. Not a parade of meetings. If the provider can’t scope a standard network penetration test efficiently, expect drag later.
A lot of the same principles show up in strong guidance on thorough network security audits. The best teams keep the scope clear so testing time goes into finding issues, not chasing paperwork.
Recon and scanning
Now the tester maps the environment. In plain terms, they identify what’s reachable, what services are exposed, and where the likely weak points are.
This includes things like:
- Host discovery to see what’s alive
- Port and service identification to understand what’s listening
- Version checks and enumeration to gather details that matter later
Tools help here. They should. But this stage only matters if a human knows what the results mean.
Exploitation and validation
Weak providers get exposed at this point. Plenty of firms stop at “scanner says maybe.” That’s not enough.
A proper penetration test tries to verify whether a weakness is exploitable and what access it gives an attacker. That may include weak credentials, exposed services, poor permissions, insecure remote access, or trust relationships that let one compromise spread.
The goal is not chaos. It’s proof.
A pentest confirms what can be abused. It doesn’t just dump suspected issues into a PDF.
Post-exploitation without the drama
Once access is gained, the tester checks what an attacker could do next. Could they escalate privileges. Reach sensitive systems. Move laterally. Access data they shouldn’t touch.
That’s the part business leaders care about, even if they don’t know the technical terms. A medium-looking issue can become a serious problem when it leads to broad access.
A useful provider will explain that chain in simple language:
- Initial foothold where access started
- Privilege increase how more power was gained
- Movement what else became reachable
- Business impact why this matters to your company
Reporting within about a week
This shouldn’t take forever. For many SMB network penetration testing services engagements, the path from kickoff to final report can fit inside about a week when the scope is focused and the process is mature.
That speed comes from discipline:
- No bloated scoping cycle
- No outsourcing confusion
- No report-writing theater
- No waiting for someone to “translate” scanner output
Certified testers such as OSCP, CEH, and CREST professionals should be able to move through this process without turning it into a month-long consulting project.
A good process also leaves room for questions and retesting. If your team fixes the issues quickly, you should be able to get validation without starting from scratch. That’s how pentesting should work in the world.
Mapping Your Pentest to Compliance Requirements
A lot of buyers don’t want a network penetration test because they suddenly love offensive security. They want it because an auditor, customer, or security questionnaire requires proof.
That’s fine. Compliance is a valid reason to test. You still need the test to be useful.

What auditors want
Auditors want independent evidence that your controls work in practice. Not that you bought a firewall. Not that someone checked a box in a policy. They want proof that somebody tested the environment and documented the results.
That’s why manual work still matters so much for audit readiness. For compliance purposes, organizations are rapidly adopting testing tools, with AI-driven penetration testing adoption reaching 80%, but auditors still value manual testing because it finds business logic flaws and complex weaknesses that automated tools often miss (AppSecure cloud security statistics 2025).
If you’re preparing for an audit, this page on SOC 2 penetration testing gives a straightforward view of what reviewers usually expect from the deliverable.
Which test maps to which framework
Different frameworks ask the same basic question in different language. Have you tested your systems in a credible way, and did you fix what mattered?
Here’s the simple mapping:
| Framework | What matters most | Typical pentest focus |
|---|---|---|
| SOC 2 | Evidence of security control validation | External and internal testing tied to scoped systems |
| PCI DSS | Testing around cardholder-related exposure and segmentation | External, internal, and segmentation validation |
| HIPAA | Risk to systems handling protected health information | Network and application paths to sensitive data |
| ISO 27001 | Demonstrable security assessment and remediation process | Scope-based testing with documented findings and follow-up |
The mistake I see all the time is buying the wrong engagement. A startup needing audit evidence for a limited environment does not need the same pentest package as a huge enterprise with sprawling infrastructure.
Compliance doesn't require bloated testing
Some firms sell fear. They imply your audit will fail unless you buy a massive custom engagement full of extras you didn’t ask for.
That’s nonsense.
You need testing that matches:
- Your scoped environment
- Your framework requirements
- Your deadline
- Your remediation capacity
Audit reality: a concise, credible report with clear evidence is more useful than a giant report no one can explain in the audit meeting.
Manual testing matters here because auditors and customers often ask follow-up questions. They want to know what was tested, what was found, how severity was assigned, and whether remediation was verified. A human tester can answer those questions. A scanner export can’t.
If your provider understands compliance, the report won’t just describe flaws. It will make sense to both technical reviewers and non-technical auditors. That’s what gets deals unstuck and audits closed.
What a Useful Pentest Report Looks Like
Most bad pentest reports share the same flaw. They are long, noisy, and hard to use.
A useful report does two jobs at once. It tells leadership what the business risk is, and it tells the technical team exactly what to fix. If it fails either group, it’s not a good report.
The executive section should be plain English
Your CEO, founder, or compliance lead doesn’t need pages of tool output. They need a clear summary of what was tested, what was found, how serious it is, and whether the environment appears reasonably controlled.
That summary should answer basic questions fast:
- What was in scope
- What attack paths were confirmed
- What issues need immediate attention
- Whether the results affect compliance or customer trust
If a report can’t explain the risk without security slang, it’s lazy writing.
The technical section should be fixable
Here is where the most value sits. Every finding should include enough detail for your IT or engineering team to reproduce the issue, understand the impact, and remediate it without guessing.
A good technical finding includes:
- What the issue is
- Where it was found
- How it was validated
- Why it matters
- What to do next
Screenshots, proof of concept notes, affected assets, and step-by-step remediation guidance matter more than report length. More pages do not equal more value.
Prioritization matters more than volume
If everything is labeled critical, nothing is. A useful penetration test report tells you what to fix first and what can wait.
Industry data shows that without a clear, actionable plan, 70% of identified vulnerabilities remain unpatched after 90 days, which is why structured reporting and prioritized findings matter so much (NetSPI penetration testing as a service).
That means the report should separate:
- Immediate fixes that block obvious attacker paths
- Important fixes that reduce exposure but may take planning
- Hardening items that improve resilience over time
The report is not the end of the engagement. It’s the handoff that decides whether the security gap gets closed or ignored.
What to reject immediately
If you’re reviewing vendors, push back on reports that look like this:
- Scanner dumps with little or no manual validation
- Generic remediation advice that says “update system” and nothing else
- No proof of impact so your team can’t judge urgency
- No clean executive summary for leadership or auditors
- No retest path after fixes are made
A pentest report should reduce work for your team, not create a second project just to interpret what the consultant meant. If the document doesn’t help people act, it failed.
How to Choose an Affordable Pentesting Provider
You need a pentest this month. Sales wants the security review done. A customer wants proof. Compliance is waiting. Then a big-name firm shows up with a long scoping call, a slow start date, and a price that makes no sense for a focused network assessment.
That is where many SMBs waste time and money.
An affordable pentesting provider should give you clear scope, qualified testers, a firm timeline, and a report your team can act on. If a vendor cannot do that without layers of process and vague pricing, keep looking.
Start with who will test your network
Buyers get distracted by brand names and polished sales decks. Ignore that. Ask who is performing the work, what their background is, and whether the provider uses staff testers or rotates unknown subcontractors into client environments.
Certifications like OSCP, CEH, and CREST are useful screening tools. They do not prove the tester is great, but they do help you filter out providers that treat offensive security like a commodity service.
Then ask the question that exposes weak vendors fast. How much of the engagement is manual?
Manual testing is what separates a real pentest from a dressed-up scan. You are paying for judgment, validation, and attack-path testing. If the provider relies on tools first and analyst review later, you are probably buying less than you think.
Screen out scanner-first vendors early
A vulnerability scan has value. It just is not the same service.
Some providers use pentest language to sell an automated scan with a little commentary added at the end. That model is cheap for them, easy to scale, and often useless for the client once real questions start coming in from auditors, customers, or engineers.
Ask these questions before you sign anything:
- Will you manually validate findings
- Will you attempt exploitation where appropriate
- Will you test for privilege escalation and lateral movement
- Will the report show attack paths, not just a list of possible issues
- Will I be able to talk to the tester, not only an account manager
If the answers are vague, the service will be vague too.
Push for simple pricing
A lot of pentest pricing is inflated by process, not technical depth.
Traditional firms often wrap a straightforward network test in enterprise scoping workshops, project management overhead, and padded delivery timelines. SMBs and startups end up paying for ceremony they did not ask for. As noted earlier, pricing in this market can vary wildly. That is exactly why you should force providers to explain what drives cost.
Use this comparison when you evaluate quotes:
| What to ask | Good answer | Bad answer |
|---|---|---|
| How is price set | Scope is defined clearly and priced plainly | “We’ll know after discovery” |
| What’s included | Testing, report, debrief, retest terms | Vague bundle language |
| How long to deliver | Specific turnaround window | “It depends” with no bounds |
| Who tests | Named or clearly qualified team | Hidden subcontractors or generic “resources” |
Affordable does not mean low-effort. It means the provider removed waste, kept the test focused, and did not bury a small engagement under enterprise process.
Speed is part of the service
A pentest that arrives after your deadline is a reporting exercise, not a security service.
For SMBs, speed matters because the trigger is usually immediate. A customer questionnaire, an upcoming audit, a renewal, a board request, a product launch. Waiting weeks just to get started is hard to justify when the scope is narrow and the environment is ready.
Ask how the provider handles:
- Scope changes
- Access issues
- Daily communication
- Report review
- Retesting after remediation
Fast providers usually answer in concrete terms. Slow providers hide behind process language and call it maturity.
Check whether the provider fits your company size
Here, smaller companies often get burned. They hire a firm built for large enterprises and get treated like a miniature version of a Fortune 500 client.
That usually means more meetings, more handoffs, slower scheduling, and a bigger invoice. It does not usually mean a better test.
A startup, lean SaaS team, regional healthcare group, or SMB with a small IT function usually needs a provider that can do five things well:
- Keep the scope focused
- Do real manual testing
- Communicate directly
- Deliver quickly
- Price the work plainly
That is the common-sense model. It is also the model many traditional firms are not built to deliver.
Ask how they support closure, not just discovery
You are not buying a list of problems. You are buying an engagement that helps your team close risk.
That means you should ask what happens after the report is sent. Can your engineers ask remediation questions? Is retesting included or available? Will the provider document revised evidence clearly enough for auditors and customer reviews?
A cheap test becomes expensive when your team has to chase clarifications for two weeks after delivery.
The checklist I’d use
If I were advising an SMB CISO, founder, or IT lead, I’d use this shortlist before hiring any pentesting provider:
Certified testers only
Ask who is doing the work and what qualifications they hold.Manual-first methodology
Tools support the test. They should not be the test.Clear scope and fixed expectations
You should know what is in scope, what deliverables you get, and when you get them.Fast turnaround
If the provider cannot move at SMB speed, they are the wrong fit.Useful reporting
The deliverable should help leadership, auditors, and technical teams without extra interpretation.Retest path
You need a clean way to validate fixes and close the loop.No enterprise baggage
Do not pay for layers of process that add cost without improving the outcome.
The right provider is usually obvious once you ask direct questions. Choose the team that tests manually, communicates clearly, delivers fast, and charges for the work itself, not for theater.
If you need a network pen test, penetration test, or ongoing penetration testing support without the usual delays and bloated pricing, use the contact form at Affordable Pentesting. Ask for a scoped quote, expected turnaround, and sample deliverable structure first. That will tell you quickly whether the service fits your deadline, budget, and compliance needs.
.svg)
