You need a pentest because an auditor asked for it, a customer asked for it, or your team just pushed something public and you don't want to find out about a flaw from an attacker first. Then you start shopping around and hit the usual mess. Bloated scopes, slow timelines, vague promises, and a giant bill for a report that reads like a scanner export.
That's why pen test black box work matters for startups and SMBs. It focuses on the part of your environment attackers can reach from the outside. It's practical, easier to scope, and often the cleanest way to get an audit-ready penetration test without buying a giant enterprise engagement you don't need.
What Is a Black Box Pen Test Really
You pushed a public app, an API, or a customer portal live. Now you need a pentest report fast, and every traditional firm wants weeks of onboarding before they even touch the target. A black box pen test cuts through that nonsense. The tester starts with the same visibility an outside attacker has and works from there.
No source code. No privileged credentials. No internal diagrams. Just the systems a real attacker can reach from the internet.
A black box test gives you the clearest answer to one practical question. What can someone do to your business from the outside, right now?

Why founders start here
For startups and SMBs, black box testing is usually the smartest first buy. You do not waste time feeding a vendor internal docs, setting up endless access, or paying for a giant internal review when the immediate audit scope is external exposure.
The focus is simple. Test the internet-facing assets that affect customer trust, compliance, and protecting public-facing digital perimeters.
That focus is critical because auditors and security questionnaires often care first about what outsiders can hit without logging into your network.
What actually gets tested
A black box pentest usually covers the attack surface an unauthenticated outsider can reach, including:
- Web applications: login pages, registration flows, file uploads, password reset paths, admin panels, and customer-facing features
- APIs: exposed endpoints, authentication, authorization gaps, weak input handling, and insecure object access
- External infrastructure: internet-facing services, open ports, SSL/TLS setup, DNS exposure, and misconfigured hosts
Tools help with reconnaissance and validation. Good testers still have to think. Nmap can identify services. Gobuster or Dirbuster can uncover hidden content. SSLyze and testssl.sh can expose TLS weaknesses. Shodan and SpiderFoot can support recon. True value comes from manual testing that confirms impact instead of dumping noisy scan results into a PDF.
Practical rule: If you need an audit-ready report quickly and your main risk sits on public systems, start with black box testing.
What black box testing does well
It gives you an attacker-view assessment without the delays and cost that come with deeper internal engagements. That makes it a strong fit for compliance deadlines, customer security reviews, and release-driven testing when your team needs answers this week, not next quarter.
It also keeps scope clean. That matters for budget. A focused external test is easier to define, easier to schedule, and easier to defend to an auditor than an oversized engagement full of enterprise extras you do not need.
What it does not do
Black box testing does not show every internal weakness. It will not replace code review, internal network testing, or authenticated role-based testing where a user already has access.
That is not a flaw. It is the point.
You are buying a fast, realistic test of external risk. For a startup trying to satisfy compliance without burning cash on enterprise process theater, that is usually the right place to start.
Black Box Pentest vs White Box and Gray Box
Most buyers get confused because security firms explain these three models like a textbook. The question is easier. How much access does the tester get, and what are you trying to prove?
If you need fast external validation, black box is usually the right call. If you need deep internal review, white box makes more sense. If you want something in between, gray box can be a solid middle ground.

The plain-English difference
| Factor | Black Box Pentest | White Box Pentest | Gray Box Pentest |
|---|---|---|---|
| Tester knowledge | No prior internal knowledge | Full internal knowledge | Partial internal knowledge |
| Main viewpoint | External attacker | Internal reviewer with full visibility | User or attacker with some access |
| Speed | Fastest to start for external validation | Slowest and deepest | Middle ground |
| Realism | Highest external realism | Less attacker-like | Balanced realism |
| Best use | Public apps, APIs, perimeter checks, compliance support | Source code review, internal architecture, deep logic flaws | Authenticated testing and broader efficiency |
According to Cobalt's comparison of black, gray, and white box pentests, black-box is the quickest but least thorough, while white-box is the most time-consuming and deepest, and gray-box sits in the middle with better efficiency than black-box. That lines up with what experienced pentesters see in practice.
What I'd recommend
Pick black box when:
- Your main concern is external exposure: Public apps, APIs, and internet-facing systems
- You need audit evidence quickly: Especially for frameworks that care about realistic external attack simulation
- You don't want to pay for unnecessary depth: Early-stage and lean teams usually need focused risk reduction, not a months-long deep dive
Pick gray box when:
- You want better coverage with less guesswork: A test account or limited documentation helps uncover more in less time
- You care about authenticated user risk: This is useful when customer or employee roles matter
Pick white box when:
- You need deep code and design review: This is the right choice for mature programs, high-risk systems, or internal secure development work
- You're chasing hard-to-find logic flaws: Full visibility helps, but it takes longer and usually costs more in effort
Black box is the best first buy for many startups because it tests the exposed surfaces attackers will hit first.
The trade-off nobody should sugarcoat
Black box gives you realism. It does not give you full coverage. That's the trade. If a firm sells it as complete security assurance, they're overselling.
Still, for a startup trying to pass an audit, validate perimeter defenses, and stay within budget, black box penetration testing is often the best return on effort. It addresses the most immediate risk without dragging you into a giant consulting project.
Our Five Phase Black Box Attack Process
A real black box penetration test should follow a disciplined process. If someone says they can do it by pointing a scanner at your app and emailing a PDF, that's not serious pentesting. That's noise.
The work should move through a clear attack flow, and the tester should manually validate what matters.
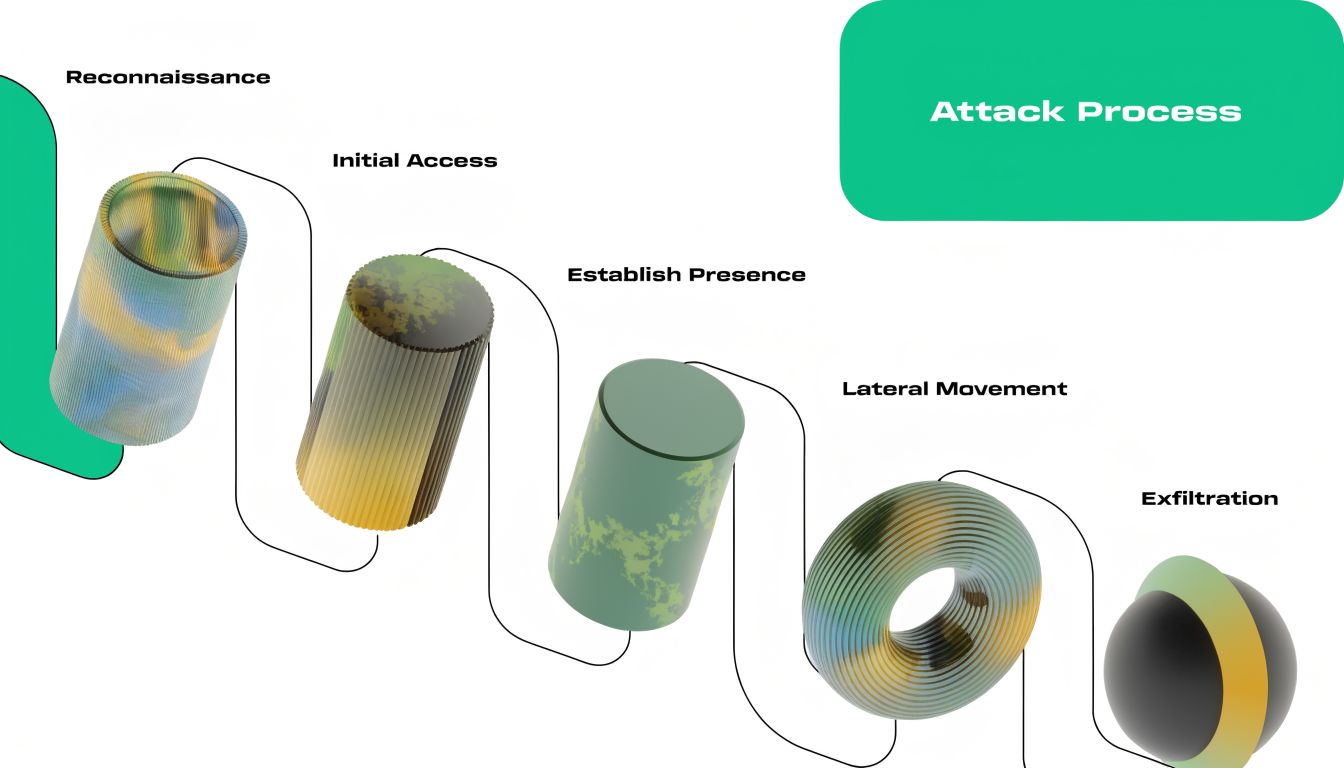
Phase one and two
A professional black box penetration test follows a five-phase lifecycle: reconnaissance, scanning, vulnerability discovery, active exploitation, and reporting, as outlined by IS Partners' overview of black box vs white box penetration testing.
Here's what that looks like in plain English.
Reconnaissance
The tester gathers public information about your targets. That can include subdomains, exposed login pages, known technologies, public files, metadata, and employee-related OSINT that helps map the attack surface.Scanning
Next comes active mapping. Tools like Nmap, Gobuster, SSLyze, and web proxies help identify reachable systems, exposed directories, service behavior, and configuration issues.
Phase three and four
Vulnerability discovery
During this stage, findings start to form. The tester checks authentication, session handling, access control, input validation, file handling, business logic, and exposed components. Automated checks can help, but they don't replace manual analysis.Active exploitation
This step matters most. The tester safely proves whether an issue is exploitable. That manual validation is what separates a useful penetration test from a bloated list of false positives.- Reporting
The report should explain what was found, how it was validated, what the risk is, and what to fix first. Good reports also include reproduction guidance and remediation advice your developers can effectively use. - SOC 2: External attack simulation helps support trust service criteria around risk management and security controls
- PCI DSS: External penetration testing is a direct concern for payment-related environments
- HIPAA: Public-facing systems tied to healthcare data need realistic external validation, not just internal assumptions
- Defined scope: What was tested and what was out of scope
- Validated findings: Not just tool output, but manually confirmed issues
- Evidence: Screenshots, request and response proof, or clear technical notes
- Remediation guidance: What to fix first so your team can act fast
You send the target
Share the hostname, app URL, API docs, or external IPs that need testing.Scope gets approved fast
You confirm what is in scope, what is excluded, and who can authorize testing. This should take hours, not a week of meetings.Testing starts right away
The tester begins external recon, targeted scanning, and manual validation against the approved surface.You receive a final report
The report should be ready for engineers, leadership, and auditors. It should not require another round of “report polishing” before anyone can use it.- Clear severity and business impact: Your team needs to know what to fix first
- Evidence for every finding: Screenshots, request and response details, or reproduction notes
- Specific remediation guidance: Actionable fixes your engineers can use
- Clean structure: Easy to review under deadline pressure
- Scope carefully: Include every important public app, API, and internet-facing service
- Ask how findings are validated: Manual proof matters
- Match the method to the risk: Use black box for external assurance, then expand later if needed
- Demand remediation clarity: Developers need actions, not theory
- Executive summary: Plain-English explanation of overall risk, what was tested, and what needs attention first
- Technical findings: Each issue with evidence, affected assets, impact, and reproduction notes
- Remediation guidance: Direct fixes your dev or ops team can implement without guessing
- Who performs the manual validation: You want named humans, not only a platform
- What certifications do the testers hold: OSCP, CEH, and CREST are useful trust signals
- How is severity explained: Your team should understand business impact, not just labels
- Will the report work for audits: It should support compliance review without extra cleanup
What auditors care about: confirmed, evidence-backed findings are far more useful than raw scanner output.
Phase five
Why the manual step matters
A lot of cheap-looking pen testing is just automated scanning dressed up as consulting. That creates two problems. First, it wastes your team's time chasing junk. Second, it gives auditors weak evidence.
Manual exploitation and validation fixes that. It proves the issue is real, shows the impact, and gives your team a clean list of actions instead of a pile of guesses.
If your pentesters hold certifications like OSCP, CEH, or CREST, that usually signals they've been trained to do more than push buttons. Certifications don't guarantee quality on their own, but they're a useful filter when you're trying to avoid low-effort firms.
Meeting Compliance With Black Box Pen Testing
If you need a pentest for compliance, keep this simple. Auditors want evidence that you tested your defenses against a realistic threat. A black box penetration test does exactly that for external attack paths.
That's why this approach fits startups and SMBs so well. It focuses on your exposed systems, keeps the scope practical, and produces the kind of documentation audit teams expect to review.
Where it fits best
The primary objectives of black-box pentesting include identifying exploitable vulnerabilities from an external perspective and evaluating security controls, which directly supports readiness for frameworks like SOC2, HIPAA, and PCI DSS.
That matters because compliance isn't just about checking a box. You need to show that someone tested whether an outsider could get in.
What auditors usually want to see
A useful compliance-friendly penetration test report includes:
If you're trying to prepare for an audit, it helps to spend a few minutes understanding SOC 2 pen tests so you know what your auditor is likely to expect from the engagement and final report.
A black box test is often the cleanest answer when the audit question is, “Did you test your internet-facing systems the way a real attacker would?”
Teams that need a more specific path for audit readiness usually start with targeted SOC 2 penetration testing services built around public applications and APIs rather than oversized enterprise scopes.
Get Your Pentest Report In One Week
You have an audit date on the calendar, an engineer who can spare maybe two hours to answer scope questions, and a security firm trying to turn a simple external test into a month-long sales process. That is the exact problem black box testing should solve for a startup or SMB.
If the scope is a public app, API, or internet-facing service, one week is realistic. Longer timelines usually come from bloated intake, slow scheduling, or firms selling enterprise process to teams that do not need it.

What a one-week engagement should look like
A good provider keeps this tight:
What actually causes delays
Bad scope causes rework. Unclear ownership causes approval stalls. Overbooked firms push your test into a queue and call it normal.
Speed does not reduce quality. Sloppy execution reduces quality.
A strong black box engagement moves quickly because the provider knows how to scope external targets, assign a tester fast, and keep admin overhead low. That matters if you are trying to satisfy an auditor without burning half your month on calls and paperwork.
What the report needs to include
A one-week report still has to do the job:
If you need to get a high-quality pentest report without paying for enterprise theater, choose a provider built for fast external testing and audit-ready reporting.
Fast works when scope is tight and findings are manually verified. Fast without manual validation is just a scanner with a PDF.
Common Black Box Pentesting Mistakes to Avoid
Black box testing works well, but teams still mess it up in predictable ways. Usually it's not because the method is bad. It's because the engagement was scoped badly or executed lazily.
Mistake one and two
The first mistake is testing too little. If the scope ignores a critical subdomain, admin path, or API surface, the final report may look clean while significant risk sits just outside the boundary.
The second mistake is buying a scanner report dressed up as pentesting. Automated tools are useful for coverage, but they don't prove impact. If nobody manually validates findings, your team will waste time sorting real issues from junk.
Mistake three and four
Another problem is expecting black box testing to find everything. It won't. A key limitation of black-box testing is that it can miss vulnerabilities exposed by insider threats, and time-bound engagements can't match the unlimited research time a real attacker might use. That's why it's most effective for validating external security posture, as noted earlier in the comparison section.
The last big mistake is treating compliance as the only goal. Passing the audit matters, but your report should still help engineers fix real exposure. If the report only exists to satisfy paperwork, you missed the point.
The best black box pentest doesn't pretend to be everything. It does one job well. It tells you what an outsider can reach, exploit, and abuse right now.
Your Fast and Actionable Pentest Deliverables
The report is the product. If the report is weak, the whole penetration test was a waste of time.
A useful black box pentest report should be short enough to read and detailed enough to act on. Leadership needs the headline risk. Engineers need evidence. Auditors need proof the work was real and scoped correctly.
What a strong report includes
The best deliverables usually have three layers:
What bad reports look like
Bad reports are bloated, generic, and weirdly hard to use. They bury the important findings under template language, dump scanner output into appendices, and tell your team to “improve security posture” instead of fixing a specific weakness.
That's not helpful when your developers are busy and your audit clock is ticking.
What to ask for before you buy
Ask these questions before you approve any pentest:
A black box penetration test earns its value when the deliverable helps two groups at once. Your technical team gets a prioritized fix list. Your auditor gets evidence that an external attack simulation happened and produced defensible results.
That's the standard. Anything less is just paperwork.
If you need a fast, affordable, audit-ready penetration test for a public app, API, or external environment, Affordable Pentesting is built for exactly that. Their team focuses on practical manual pentests for startups and SMBs, with certified pentesters and clear reports that help you fix real issues and move your compliance work forward. Use the contact form to scope the test and get started quickly.
.svg)
