You can't avoid every risk in business. Trying to would be paralyzing. The real goal is to make smart decisions that protect your company while you grow. A risk management system is the structured process you use to find, analyze, and handle threats before they become disasters, helping you stay compliant with standards like SOC 2, HIPAA, or PCI DSS.
Why You Need a Risk Management System
Think of a risk management system as your business's playbook. It's a clear process for dealing with uncertainty, like a cybersecurity breach or a sudden market shift. Having a system moves you from reacting to crises to planning for growth. This isn't about creating paperwork. It’s about knowing your vulnerabilities and having a plan to deal with them.
Protect Your Business From All Angles
An effective risk management system gives you a complete view of potential threats. It goes beyond firewalls to cover everything that could seriously harm your business. This includes cybersecurity risks like weak passwords, operational risks like supply chain issues, and compliance risks like failing to meet HIPAA requirements. A solid system helps tackle overlooked vulnerabilities, like managing the massive risk of old IT gear, so no single failure can stop you.
Connect Risk Management to Penetration Testing
How do you know which risks are real? That's where penetration testing comes in. A penetration test, or pentest, is a vital part of any modern risk management system. It's the difference between guessing where your weaknesses are and knowing for sure. By hiring certified pentesters with qualifications like OSCP, CEH, and CREST to simulate an attack, you get undeniable proof of your vulnerabilities.
Traditional firms make this process slow and expensive. We provide affordable pentesting with reports in your hands within a week, giving you actionable data fast. A finding from a penetration test turns a potential threat into a documented, high-priority issue. You can learn more about this in our guide on what is compliance management. Regular pen testing makes your risk management an evidence-based tool for protecting your business.
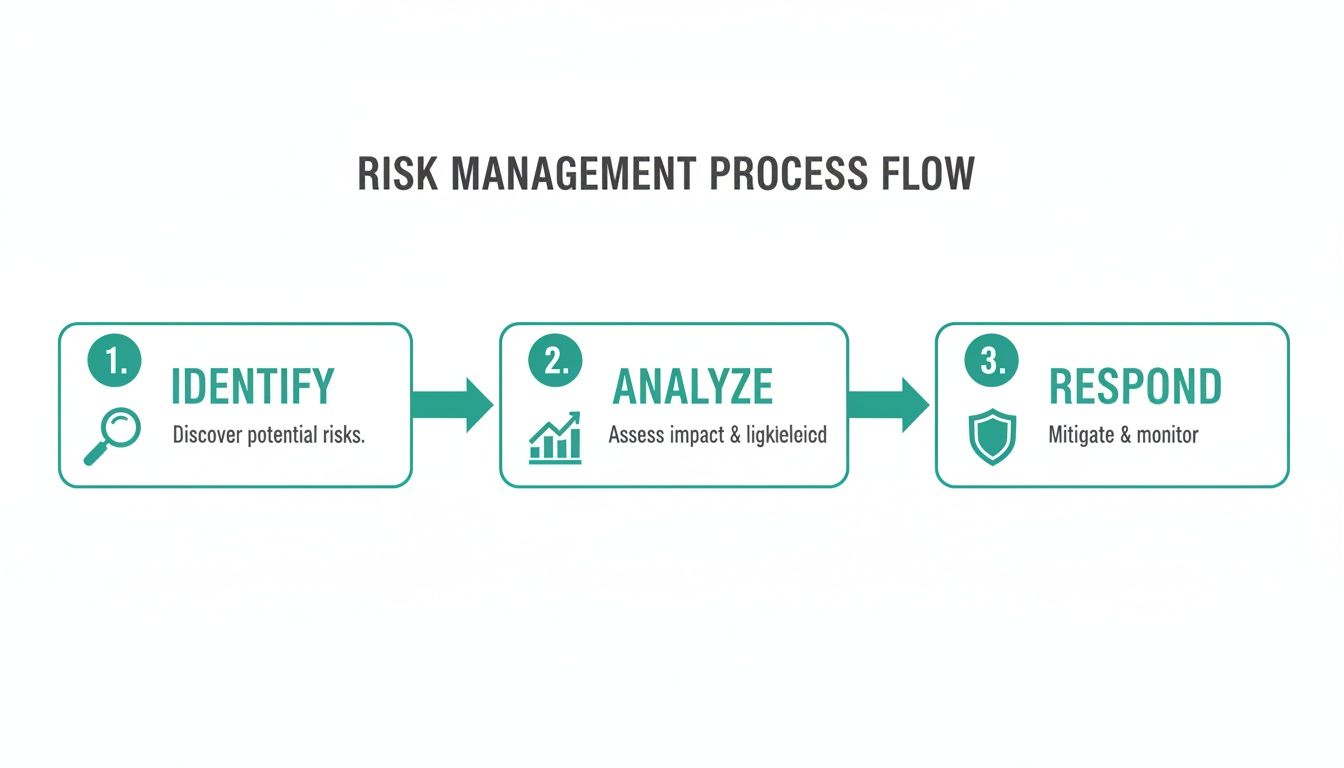
Know the Core Parts of a Risk System
A solid risk management system isn't a theoretical exercise. It’s a practical framework for breaking down the complex problem of securing your business into simple, manageable pieces. Think of it as a continuous loop made of five core steps. Each one feeds into the next, creating a system that gets smarter over time.
Step 1: Identify Your Security Risks
It all starts here. Risk identification is where you actively hunt for potential threats. You can't protect against a risk you don't know exists. This means looking everywhere—your applications, your network, your internal processes—to find weaknesses before an attacker does. This isn't guesswork; it's a proactive search for everything that could go wrong.
Step 2: Analyze Your Potential Risks
Once you’ve found a potential risk, you need to figure out how serious it really is. That's risk analysis. You determine the likelihood of the threat happening and the potential impact if it does. Is a vulnerability a minor annoyance or something that could kill your company? This step gives you the data to tell the difference.
Step 3: Evaluate and Prioritize Each Risk
You can't fix everything at once. Risk evaluation is all about prioritization. You take your analyzed risks and stack them up, deciding which ones are critical enough to handle right now and which ones can wait. This is where you separate the urgent fires from the slow burns, focusing your resources where they’ll have the biggest impact.
Step 4: Create Your Risk Treatment Plan
Now it's time to act. Risk treatment is your action plan. Based on your evaluation, you decide how to handle each high-priority risk. You can mitigate it by patching a vulnerability, transfer it by getting insurance, avoid it by stopping the risky activity, or accept it if the fix costs too much. This plan is your roadmap for action.
Step 5: Monitor Your Risks Continuously
A plan is only good if it works. Risk monitoring is the final, ongoing step. You have to constantly watch your security controls to see if they're still effective and scan the horizon for new threats. A risk management system isn't a one-time project; it's a continuous cycle that makes your business more resilient over time.
Make Your Risk Management System Real
How do you stop this from being a theoretical checklist? You inject real-world data into it with a penetration test. Instead of wondering if a vulnerability is a threat, a professional pentester proves it. Our OSCP, CEH, and CREST certified testers think like attackers to find flaws that scanners miss.
We deliver affordable penetration testing reports within a week, so you’re not waiting months for results. This speed allows you to feed real, timely data directly into your risk management system. A finding from our report immediately helps you prioritize what to fix. The risk management market is growing because of rising cyber attacks, and you can review the full market research about these trends to understand what’s driving this growth.
Choose the Right Risk Management Framework
Think of a risk management framework as a proven recipe for your security program. It’s a blueprint trusted by thousands of organizations that gives you a solid structure for managing risk. The right one for you depends on your business. A healthcare startup has different needs than a financial firm.
Compare Popular Risk Management Frameworks
While there are many frameworks, most businesses land on one of three: COSO, ISO 31000, or the NIST Cybersecurity Framework (CSF). COSO is great for large public companies focused on financial controls. ISO 31000 is a flexible, universal standard for any organization. The NIST CSF is a practical, cost-effective approach for US businesses focused on cybersecurity. You can get more details in our guide to cybersecurity risk management frameworks.
Align Your Framework With Your Goals
Let's get practical. If your goal is a smooth SOC 2 audit, the NIST CSF is a great starting point. If you do business internationally, the ISO family is your best bet. An ISO 27001 ISMS certification is often a non-negotiable requirement for landing enterprise deals. The best framework is the one that directly supports your business objectives.
The pressure is on to integrate real-world security validation, like a penetration test, to satisfy compliance demands. The global risk management market is exploding, and you can discover more insights about risk management market growth on datainsightsreports.com. This shows how critical it is to get your security right.
Integrate Penetration Testing Into Your Framework
A framework is just a structure. A penetration test provides the hard evidence to fill it out. Your chosen framework will say "identify vulnerabilities," and a penetration test is how you actually do that. Our certified pentesters, holding credentials like OSCP, CEH, and CREST, actively hunt for and exploit security holes.
When we deliver your pentest report in a week, you get a prioritized list of verified findings. This report feeds directly into your risk management system. A theoretical risk just became a tangible vulnerability, allowing you to prioritize fixes based on real-world evidence, not a checklist. This is how you turn a risk management system into a tool that actually improves your security.
Integrate Pen Testing Into Your Strategy
A risk management system is great at telling you where your weaknesses might be, but a penetration test is how you prove it. Think of it this way: a risk register is a map of potential landmines. A pentest is the expert who walks the field and shows you which ones are actually live. This step turns your risk analysis from an educated guess into an evidence-based defense plan.

Regular, affordable pen testing provides the hard data needed to make your risk management work. When a pentest report lands on your desk in just one week showing a verified vulnerability, a theoretical risk becomes a tangible threat. This is how you stop guessing and start prioritizing fixes that matter.
Why Theoretical Risk Is Not Enough
A risk register filled with "what ifs" is a decent start, but it doesn't give you certainty. You might identify a risk like "potential SQL injection," but how do you know if it's a real threat? Without validation, your team could waste time and money fixing the wrong things.
A penetration test delivers critical clarity. Instead of listing possibilities, a pentest delivers concrete proof. Our certified professionals, with credentials like OSCP, CEH, and CREST, simulate an attack to see if a vulnerability can be exploited. This moves your security from theory to reality.
Connect Pen Testing to Your Risk Process
Integrating a pen test into your risk management system is straightforward and makes every step more accurate. A penetration testing report uncovers vulnerabilities that scanners miss, providing direct inputs for your risk register. Every finding comes with a clear severity rating, helping you analyze and prioritize risks with precision.
This approach ensures you focus resources on threats that pose a genuine danger. To build a robust strategy, consider developing a formal penetration testing program that schedules these assessments regularly. A pen test is the ultimate reality check for your risk management system, which is essential for meeting compliance standards like SOC 2 and HIPAA.
The Value of Speed and Affordability
Traditional penetration testing firms are a roadblock. Their high prices and slow timelines make it impossible for startups and SMBs to integrate testing effectively. Waiting six weeks for a report that finds nothing useful doesn't help anyone.
Our focus on affordability means you can conduct a pentest more frequently without blowing your budget. Our speed is a strategic advantage. You get a clear, actionable report back within a week, allowing your team to act on findings while they are still relevant. This agile approach makes your entire security posture stronger and more responsive.
A Practical Roadmap to Implement Your System

Building an effective risk management system doesn't require a giant budget. You can get started with a practical, step-by-step approach. This roadmap is for busy IT managers, CISOs, and founders who need to move fast. Frame it as a strategic investment to protect revenue, enable growth, and meet compliance goals like SOC 2 or HIPAA.
Step 1: Get Leadership Buy-In First
First, you need support from the top. Explain that a risk management system isn't about creating rules; it's about making smarter business decisions. Ditch the jargon and focus on how it protects customer data, prevents downtime, and makes compliance audits less painful. You’re selling a competitive advantage.
Step 2: Assemble Your Small Risk Team
You don't need a formal committee. Start with a small team of people from IT, operations, and leadership who know how the business works. Getting different perspectives is key. Your IT manager sees technical holes, but your operations lead knows where business processes are fragile. Together, you get a complete picture.
The global risk management market is exploding because businesses are finally getting serious about protection. You can learn more about these risk management market findings on grandviewresearch.com. This shows that managing risk is no longer optional.
Step 3: Conduct Your First Risk Workshop
Once the team is set, get a risk workshop on the calendar. The objective is simple: brainstorm all the things that could go wrong. Get everything out on a whiteboard to create a master list of potential risks. Afterward, you can go back and estimate how likely they are and how bad the damage would be.
Step 4: Create a Simple Risk Register
A risk register doesn't need to be complex. A simple spreadsheet is all you need to start. For every risk, create columns for a description, likelihood (High, Medium, Low), impact (High, Medium, Low), an owner, and a treatment plan. Start by focusing on your top 3-5 highest-scoring risks. Trying to fix everything at once is the fastest way to get nowhere.
Step 5: Integrate a Real-World Pentest
This is the step that makes your risk management system real. Theoretical risks are just talk. Verified vulnerabilities are a ticking clock. This is why you need to integrate a penetration test. A pentest gives you undeniable proof of where your security is weak.
Our certified pentesters (OSCP, CEH, CREST) find security holes that scanners miss. We deliver our reports in a week, so you get actionable data you can use right away. This lets you feed real-world findings straight into your risk register. Our affordable penetration testing services make this a no-brainer for any SMB.
Frequently Asked Questions About Risk Management
We get it. Building a risk management system can feel overwhelming, especially for a startup or SMB. Here are direct answers to the questions we hear all the time from IT managers, founders, and compliance officers.
How Can I Start Risk Management on a Tight Budget?
You don’t need pricey software. The best first step costs nothing. Just get the right people in a room and talk about what could go wrong. Use a simple spreadsheet for your first risk register and focus on the top 3-5 most serious threats. A great, budget-friendly next step is an affordable penetration test, which quickly uncovers your most critical security risks without the high price tag.
What Is the Difference Between Risk Management and Compliance?
Think of it like this: compliance is following rules someone else set for you. Risk management is about protecting your own business. Compliance is checking boxes for standards like PCI DSS or HIPAA. A risk management system looks at all threats—cybersecurity, operational, financial—and builds a strategy to deal with them. Good risk management gets you to compliance, but its real purpose is to keep your business resilient.
How Often Should We Conduct Risk Assessments?
You should do a full risk assessment at least once a year. But your risk management system is a living process. You have to update it whenever something important changes, like launching a new product, integrating a new service, or after a security incident. A fast penetration testing report delivered in a week gives you fresh, real-world data you can act on immediately.
How Can I Measure the ROI of Risk Management?
Measuring the ROI for risk management is about demonstrating the bad things that didn't happen. It’s about cost avoidance. You can calculate the potential financial hit of a data breach and show how your investments helped prevent it. Passing a compliance audit on the first try or using a clean pen testing report to win a major client are also clear, measurable wins. Risk management isn't a cost center; it's a business enabler.
Stop wondering if your applications are secure. At Affordable Pentesting, our certified ethical hackers (OSCP, CEH, CREST) will find your vulnerabilities and deliver a clear, actionable report within a week. Get the peace of mind you need to grow your business. Find out more by visiting our website.
.svg)
