Stuck on a big deal because a client asked for your SOC 2 report? For startups and IT managers, this question can stop a sale cold. You need SOC 2 to grow, but traditional security firms make it slow, confusing, and expensive.
We get it. That's why we offer fast, affordable manual penetration tests that get you a report in one week. Our certified experts help you find and fix issues so you can pass your audit and get back to business.
Why SOC 2 Is a Sales Enabler
Most companies see compliance as a painful cost. But a SOC 2 report is one of your best sales tools. It answers the tough security questions enterprise buyers have to ask, cutting down your sales cycle time.
Instead of your team getting stuck filling out long security forms, you just provide your SOC 2 report. This shows you're a mature and trustworthy partner, putting you ahead of competitors who haven't done the work.
Building a Foundation of Trust
SOC 2 is all about proving you can manage your customer's data safely. It's not a strict checklist. It's a framework that lets you build security controls that actually fit your business.
Think of a SOC 2 report as your company's security story, told by an independent auditor. It confirms that you're keeping your promises about keeping data safe. This is where a professional penetration test becomes so important to prove your controls work.
The New Baseline for Security
A SOC 2 report has gone from a "nice to have" to a must-have. Today, companies aren't just getting one audit. They are building entire compliance programs to meet customer demands and stay competitive.
This shift shows that proven security is the minimum expectation now. It’s a basic cost of doing business, no matter your company's size or industry. For a closer look, you can explore the specifics of SOC 2 edge security for fintech startups.
Explaining The Five Trust Services Criteria
Think of the SOC 2 Trust Services Criteria like subjects on a report card. You only get graded on the subjects that matter for your business. These five areas give an auditor a clear way to measure how well you protect client data.

The Foundation Of Every SOC 2 Report
Every SOC 2 audit must include the Security criteria. It’s the foundation of the whole report. It covers the basic controls you need to protect your systems from unauthorized access, like firewalls and access controls.
This is also where a penetration test is essential. A pentest is like a fire drill for your security. It finds weaknesses an auditor will look for. Getting a fast, affordable pentest early gives you a clear list of what to fix before your audit begins.
Choosing Your Additional SOC 2 Criteria
Beyond Security, you can add any of the other four criteria. Only add the ones that relate to the promises you make to your customers. Adding extra criteria just creates more work and cost for no reason.
Here's what the other four are for. Availability is for when you promise near-perfect uptime. Processing Integrity applies if you handle transactions, like an e-commerce store. Confidentiality is for protecting secret business data, and Privacy is for protecting personal customer information like under GDPR.
SOC 2 Trust Services Criteria At a Glance
CriteriaWhat It CoversIs It Required?SecurityProtecting systems from unauthorized access (both physical and logical).Yes, always.AvailabilityEnsuring the system is operational and usable as promised in your contracts or SLAs.No, only if you make specific uptime guarantees.Processing IntegrityVerifying that system processing is complete, valid, accurate, and timely.No, only if you process transactions (e.g., e-commerce, financial).ConfidentialityProtecting sensitive information (e.g., IP, trade secrets) from unauthorized disclosure.No, only if you handle data your clients deem confidential.PrivacyProtecting Personally Identifiable Information (PII) according to policies and regulations.No, only if you handle personal customer data.
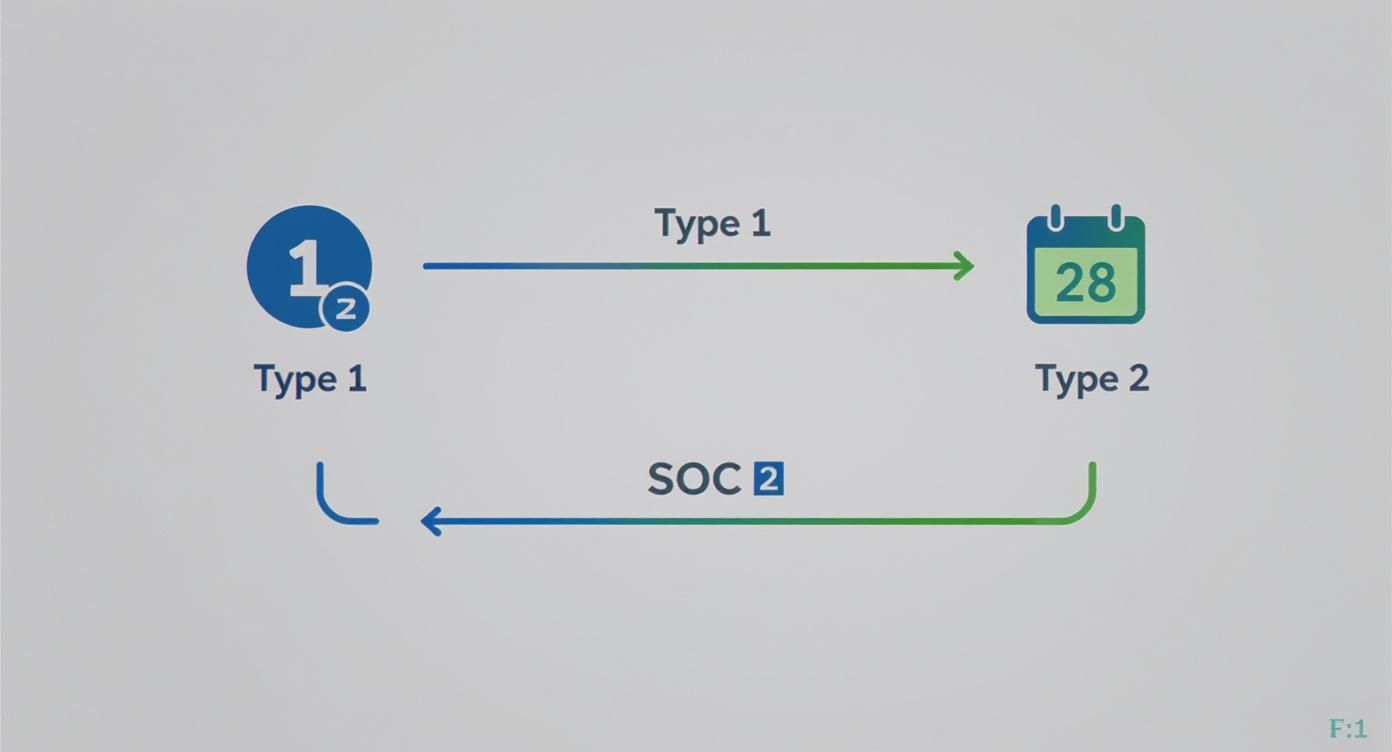
Choosing Between SOC 2 Type 1 And Type 2 Reports
Let's make this simple. A SOC 2 Type 1 report is like a blueprint for a security system. It shows you have a good plan on a single day. A SOC 2 Type 2 report is like security camera footage recorded over several months, proving the system actually works.
Customers want to see the footage, not just the blueprint. It gives them real proof that your security is effective over time. That's why the Type 2 report is what most enterprise clients will ask for.
What Is a SOC 2 Type 1 Report?
A Type 1 report is a quick snapshot. An auditor checks if your security controls are designed correctly on a specific day. It's faster and cheaper, making it a great first step for a startup that needs to show progress to a client quickly.
The problem is, it doesn't prove you're actually following your own rules every day. That’s why a Type 1 is usually just a temporary solution while you prepare for the more detailed Type 2 audit.
What Is a SOC 2 Type 2 Report?
A Type 2 report is much more thorough. An auditor tests your controls over a period of three to twelve months. They look for real evidence that your security has been working consistently, not just that you have good policies written down.
Because it's so in-depth, the Type 2 report is the gold standard. It gives customers the confidence they need to trust you with their data. This is the report that helps you close the biggest deals.
Making The Right Business Decision
So, which report should you get? If you're on a tight deadline and a big client is waiting, a Type 1 can buy you time. It shows you're serious while you prepare for the real thing.
But your long-term goal should always be the Type 2 report. It's what enterprise customers expect and what truly proves your security is solid. Getting a Type 2 can take 6 to 12 months, so it's important to plan ahead. This guide to SOC 2 compliance companies can help you budget.
Your Actionable SOC 2 Readiness Checklist
Getting ready for a SOC 2 audit doesn't have to be overwhelming. Just break it down into simple steps. This checklist is your roadmap to a smooth audit.
Following these steps helps you find problems early and organize your work. Most importantly, it shows you where a critical pentest fits into the process.
Define Your SOC 2 Audit Scope
First, decide what your audit will cover. You must include the Security criteria. From there, only add the other criteria if they match what you promise your customers. Don't add extras just to look good. It only adds cost and work.
Perform a Thorough Risk Assessment
Next, figure out what could go wrong. A risk assessment is just a structured way of finding threats to your systems. Think like a hacker. Where are your weak spots? Documenting these risks helps you decide what to fix first.
Document All Your Controls
Now, write down exactly how you manage those risks. These written procedures are your "controls." For example, your control for an employee leaving is a documented process to remove all their access within 24 hours. Auditors need to see everything in writing. An ultimate compliance audit checklist can give you a good starting point.
Conduct Vendor and Third Party Reviews
Your security depends on your vendors too. You need to review the security of any third-party service that handles your data, like your cloud provider. Ask them for their own SOC 2 reports. This shows the auditor you are managing security across your entire supply chain.
Perform a Fast Penetration Test
This is one of the most important steps. A penetration test is a simulated attack by ethical hackers. It finds the same security holes an auditor looks for. But traditional pentesting is slow and expensive, which can ruin your audit schedule.
We are the affordable alternative. We deliver fast pentest reports within one week. Our testers are certified experts (OSCP, CEH, CREST), giving you the proof you need without the high price tag. Finding and fixing these issues before the audit is key to passing.

Fast Pentesting for SOC 2 Success
A pentest is required for your SOC 2 audit, but it's often the biggest headache. Traditional firms are slow and expensive. They can delay your audit timeline and add surprise costs right when you can't afford them.
This old way of doing things is a huge risk for any company on a deadline. It's frustrating to wait weeks for a report only to find major problems you have to scramble to fix.
Why Speed Gives You Time to Fix Issues
This is where we change the game. We are built for speed. We deliver a complete, easy-to-understand pentest report within one week. This speed is your biggest advantage during a SOC 2 audit.
Getting a report that fast gives your team time to actually fix any problems we find. Instead of panicking right before the audit, you have a clear plan. A fast pentest report helps you pass your audit the first time.
Get Affordable Pentesting Without Low Quality
Many people think affordable means low quality. That's not us. We are the affordable alternative because we cut out the waste of traditional firms, like big offices and sales teams. We focus only on what matters: expert testing by certified professionals.
Our pentesters hold the certifications auditors respect, including OSCP, CEH, and CREST. You get the same expert quality you would from a big firm, but at a price that makes sense for your budget. Learn more in our guide on SOC 2 penetration testing.
The Power of a Clean Re-Test for Your Audit
Our service includes a free re-test. After your team fixes the issues we found, we will test those specific vulnerabilities again. This confirms that the problems have been solved properly.
This gives you a "clean" report to show your auditor. It proves you not only found your weaknesses but also fixed them. This is exactly what auditors want to see and it helps ensure a smooth audit.
How SOC 2 Fits With Other Frameworks
As you grow, customers might ask for other certifications like ISO 27001. Understanding how SOC 2 relates to these frameworks helps you stay ahead of future requests. You can build a security program that turns compliance into a strength, not just a chore.
SOC 2 and ISO 27001 The Powerful Combination
The most common framework you'll see besides SOC 2 is ISO 27001. SOC 2 is most popular in North America, while ISO 27001 is recognized all over the world. A customer in Europe will likely ask for ISO 27001.
The good news is that they are very similar. Both are based on managing risk and require strong security controls. If you've already prepared for SOC 2, you are well on your way to being ready for ISO 27001.
The Growing Trend Toward Multiple Frameworks
Having both SOC 2 and ISO 27001 certifications is a huge advantage. It shows you take security seriously on a global scale. More companies are adopting multiple frameworks to meet the demands of different customers.
Recent compliance statistics and trends show a clear shift towards this approach. Building a security program just for SOC 2 may not be enough to stay competitive for long.
Building a Unified Security Program
The smart move is to build one strong security program that can meet different compliance needs. You can map your SOC 2 controls to other frameworks like ISO 27001. This stops you from reinventing the wheel for every new audit.
This strategy is much more efficient and saves money. It ensures your security efforts are consistent. It's about working smarter to meet the security expectations of any customer, anywhere.
Your Top SOC 2 Questions Answered
Let's get straight to the questions we hear most often about the SOC 2 process. Here are some simple, no-nonsense answers.
How Much Does a SOC 2 Audit Cost?
The cost of a SOC 2 audit varies a lot. A simple Type 1 for a small startup could be around $10,000. A complex Type 2 for a larger company can easily go over $50,000. The final price depends on your company's size, complexity, and audit scope.
You also need to budget for your team's time and security services like penetration testing. Our model is built to make sure the pentest part of your budget is affordable, while still giving you the expert quality you need to pass.
What Happens If We Fail Our SOC 2 Audit?
Don't panic. Failing an audit is not the end of the road. Your auditor will give you a list of "findings," which are just the areas where you failed. Your job is to create a plan to fix these issues.
This is exactly why getting a penetration test before your audit is so important. It lets you find and fix problems before the auditor even sees them. This greatly increases your chances of passing the first time.
How Long Is a SOC 2 Report Valid?
A SOC 2 report is generally considered valid for 12 months. This means you can't just get one and be done. Your customers will expect you to have an updated report every year.
It's better to think of SOC 2 as an ongoing commitment, not a one-time project. It's about maintaining strong security all year long to prove you are always protecting customer data.
Ready to secure your systems and prepare for your SOC 2 audit without the high costs and long waits? At Affordable Pentesting, we deliver expert, certified pentesting with reports in under a week. Get the actionable insights you need to pass your audit with confidence.
Fill out our contact form to get started with a fast, affordable pentest today at https://www.affordablepentesting.com.
.svg)