US Based Pentesting vs Offshored Guide
Your audit deadline is close. The board wants proof. Your customer wants a penetration test report. Then the quotes land in your inbox and they are either overpriced, painfully slow, or so vague you can already tell the final report will be useless.
Many teams encounter difficulty at this stage.
The primary choice in US based pentesting vs offshored pentesting is not just price. It is whether you want a report that helps you pass compliance, fix real issues, and move on, or a cheaper project that eats your team’s time with delays, weak findings, and rework.
Why Your Pentest Choice Matters Now
If you are an IT manager, founder, or CISO, you probably need one of three things right now. You need a clean compliance pentest, a fast report, or a vendor that does not waste your budget.

The cheap option often gets expensive
A penetration test is one of those purchases where buying wrong hurts twice. First, you pay for the test. Then you pay again when your team has to explain vague findings, chase clarifications, and redo evidence for an auditor.
The stakes are not small. US breaches average between $9.36 million and $10.2 million, and US organizations spend an average of $187,000 annually on penetration testing, about 10.5% of their IT security budgets according to DeepStrike’s 2025 penetration testing statistics. That tells you something simple. US companies spend real money on pentests because the cost of getting security wrong is far worse.
Compliance buyers do not need fluff
Most frustrated buyers are not asking for a heroic red team story. They want a solid pen test that assesses the environment properly, gives them actionable findings, and gets the report back fast enough to hit an audit date.
That is why this decision matters now:
- Budget pressure: You need something affordable.
- Deadline pressure: You need the report quickly.
- Audit pressure: The report has to make sense to an auditor.
- Security pressure: The findings have to be real, not scanner noise.
Practical rule: If the penetration testing vendor cannot explain who is doing the work, how manual the test is, and how fast you get the report, keep looking.
What good pentesting looks like
A good pentest is not mysterious. It should feel organized and simple.
You define the scope. The pentesters test what matters. They communicate during the engagement. You get a report your engineers can use and your auditor can accept.
For most compliance-driven SMBs, the winning setup is straightforward. Pick a US based penetration testing provider that uses certified testers, keeps communication in your business hours, and delivers a manual report fast. That is usually the quickest path to a finished audit and fewer internal headaches.
US Based vs Offshored Pentesting Models
A lot of confusion starts because buyers compare these models like they are the same service with different hourly rates. They are not.
What US based pentesting means
With US based pentesting, the company operates in the United States, the legal contract sits under US jurisdiction, and the team handling your engagement works in a US business context. That matters when you are sharing credentials, internal docs, staging access, and sensitive app behavior.
Communication is also simpler. When your developer has a question at 10 a.m., the pentester is available to answer it. That cuts friction during scoping, testing, and remediation.
What offshored pentesting means
With offshored pentesting, some or all of the testing work is handled outside the US. The upfront quote often looks attractive. That is why many teams consider it.
But the operating model changes fast. You are dealing with different time zones, different legal environments, and often more back-and-forth just to clarify scope, reproduce findings, or retest fixes.
Why the operating model matters
This is not unique to security. The same tradeoff shows up in software delivery, support, and engineering staffing. If you want a broader business view of that tradeoff, mastering staff augmentation vs outsourcing is useful because it shows how lower sticker prices can create extra management overhead.
That pattern applies directly to pen testing.
Here is the simple version:
| Model | How it feels day to day | Best use case |
|---|---|---|
| US based pentest | Faster replies, easier meetings, cleaner audit alignment | Compliance work, sensitive systems, fast deadlines |
| Offshored penetration testing | Lower initial quote, more coordination work, slower clarifications | Lower-risk assets where speed and audit fit matter less |
The legal and practical difference
If your team handles healthcare data, payment data, or customer data under strict security review, jurisdiction is not a side issue. It affects contracts, data handling comfort, and auditor expectations.
That is why buyers should stop asking only one question, which is “What is the hourly rate?” Ask the better question. “Which model gets me a usable report with the least rework?”
For most US compliance projects, that answer is not offshore.
Analyzing The True Cost Of Penetration Testing
The offshore quote looks cheaper because it hides the expensive parts.
That is the whole game.
Sticker price is not total cost
An offshored penetration test may come in with a lower rate. Fine. But your real cost is not just the invoice. It is the invoice plus your team’s time plus the cost of delays plus the cost of cleaning up a weak report.
If your internal engineer spends days answering overnight questions, chasing context, and disputing false positives, that labor is part of the pentest cost. If your GRC lead has to rebuild evidence for the auditor, that is part of the pentest cost too.
The hidden costs buyers ignore
The biggest hidden costs usually show up in four places:
- Project management drag: Your team becomes the translator between the environment and the tester.
- Report cleanup: Developers waste time trying to understand vague findings.
- Compliance rework: Audit reviewers ask for missing detail or clearer evidence.
- Missed issues: A weak penetration test can miss the flaw that matters.
The last one is the killer. Breaches in the US average $9.36M, and insider threats average $4.99M, according to ZeroThreat’s emerging penetration testing statistics. A cheap penetration test that misses a serious weakness is not affordable. It is a bad transfer of risk back onto your business.
Key takeaway: A pentest is cheap only if the report is usable and the findings are real.
Offshore savings can evaporate fast
Some buyers focus on labor arbitrage and stop there. That is too shallow.
Offshored pentesting can cost less on paper, but if the final output creates confusion, your team pays the difference in engineering time and compliance friction. That is why the “cheaper” option often ends up costing more in practice for SMBs.
A manual US based pen test often gives you better total value because the work moves faster and the reporting is clearer. If you want a baseline for budgeting before you compare vendors, this breakdown of how much a pentest costs is a practical place to start.
What to pay for instead
Do not pay for a famous logo. Do not pay for a long PDF filled with scanner output. Pay for outcomes.
Look for this:
- Manual testing by certified people
- Clear scope and fixed pricing
- Fast report delivery
- Retest support
- Findings written so developers can fix them
Here is the blunt recommendation. If your pentest is tied to SOC 2, PCI DSS, HIPAA, or a customer security review, stop chasing the lowest bid. Buy the test that saves internal time and reduces the chance of audit rework.
That is the cheaper option in practice.
Why Pentest Report Speed Is So Important
Your auditor asks for the pentest report on Friday. Your vendor says it will be ready next week. Then the draft comes in late, the findings are vague, and your team burns more time translating the report than fixing the issues. That is how cheap pentests turn into expensive compliance projects.
Slow reporting creates direct business friction for SOC 2, PCI DSS, and HIPAA buyers. Audits stall. Remediation drags out. Security exceptions stay open longer than they should. If you need a clearer picture of SOC 2 penetration testing requirements, start there before you compare vendors.
Slow communication creates compliance rework
The schedule problem with offshored pentesting usually starts after kickoff. Scope questions sit overnight. Login issues wait a day for clarification. Developers ask whether a finding is exploitable in their environment and lose momentum while they wait for an answer.
That delay matters because compliance pentests are not just technical exercises. They are documentation exercises too. If the tester misses context, writes a muddy finding, or needs multiple rounds to explain impact, your team pays for it in remediation meetings, audit follow-up, and report rework.
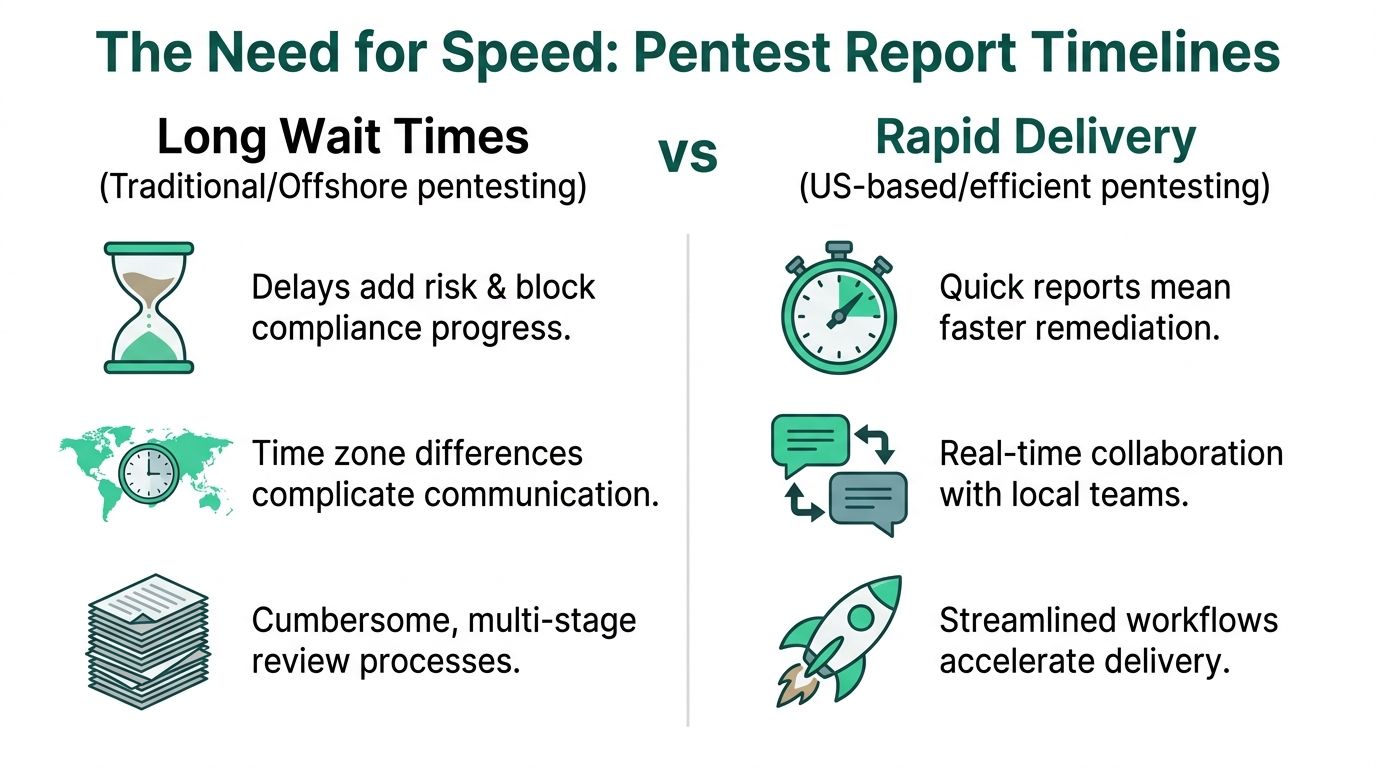
Delay shows up after testing
A compliance pentest only helps once your team has a report they can act on. Clear findings let engineers fix the issue fast. Clear evidence lets auditors close the control review fast. Offshored teams often stretch that cycle because every clarification takes longer and every weak finding needs translation.
For SMBs, the supposed savings often fall apart. The invoice may be lower, but the total cost climbs once your internal team starts doing project management for the vendor.
US based timelines are easier to control
An efficient US based manual pentest usually fits the way your team already works. The tester can validate scope during business hours, answer developer questions quickly, and turn around a draft report without losing days to handoffs.
Here is the practical difference:
| Factor | US-Based Pentesting | Offshored Pentesting |
|---|---|---|
| Scope clarification | Same-day answers during normal business hours | Delayed by time zone gaps |
| Finding validation | Faster access to the tester for follow-up questions | Slower back-and-forth and more context loss |
| Report turnaround | Shorter path from testing to draft report | More review lag and coordination overhead |
| Retest scheduling | Easier to book and complete quickly | Slower validation cycles |
Fast reports produce better ROI
Speed matters because report quality and report timing are tied together. A good pentest firm does not disappear after testing ends. It gives your team a draft quickly, explains the findings in plain English, and helps confirm fixes without dragging the project into another week.
That is the standard you should buy.
If your environment includes customer-facing applications, APIs, or AI-assisted development workflows, pair the pentest with an AI code security audit so you catch code-level issues before they turn into another compliance delay.
Set the expectation before you sign
Ask direct questions.
When do we get the draft report? How many business days after testing ends? Who explains findings to our developers? How fast can you retest remediated issues?
If the answers are vague, the delivery will be vague too.
For a focused manual pentest, a useful report should arrive fast enough to keep your audit moving and your remediation team engaged. That is why US based pentesting usually delivers higher ROI for compliance-driven SMBs. You are not just buying labor. You are buying speed, clarity, and fewer rounds of expensive rework.
.svg)
