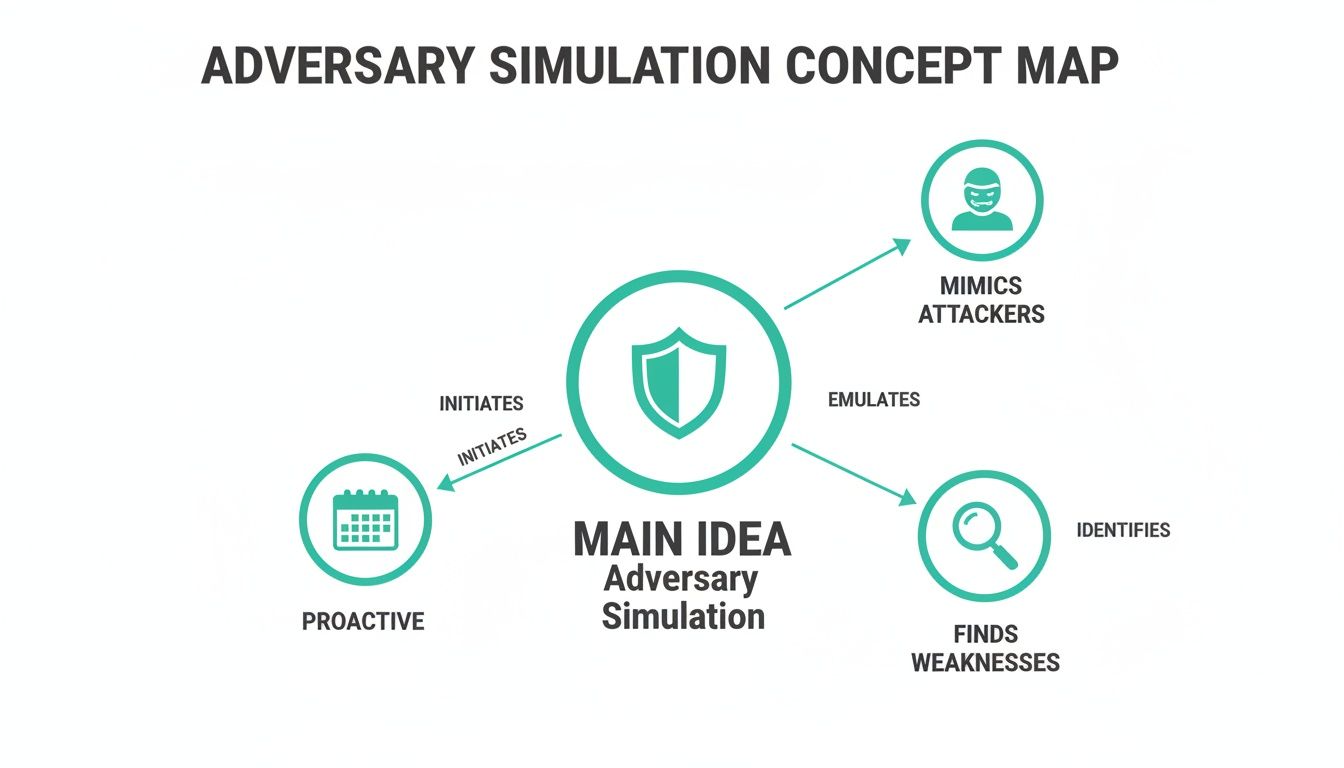
Think of adversary simulation as a fire drill for your digital security. Instead of waiting for a real cyberattack, our certified security experts act like actual attackers to test your defenses in a controlled way. It's a proactive, hands-on approach to find weak spots before criminals do.
What Are Adversary Simulation Services?
Adversary simulation is a security assessment where our ethical hackers mimic the exact tactics of real attackers. This isn't a simple checklist; it's a live exercise where we play the part of a motivated hacker. This is manual pentesting designed to find what automated tools always miss.
Basic scans just flag known issues. Our human-led penetration tests uncover complex vulnerabilities that take creativity to find. This is crucial because attackers are more sophisticated than ever, and you must test your cyber resilience before a real breach happens.
The whole point is to answer one question: "How would our defenses hold up against a real attacker?" Our affordable pentesting services give you that answer without the sky-high prices and slow timelines of traditional firms.
The Value of a Realistic Security Test
For IT managers, CISOs, and startup founders, the value is clear. You get a real-world look at your security, showing exactly how an attacker could get in and what they could do. This is far better than a standard vulnerability scan that just gives you a long list of low-impact findings.
A hands-on approach delivers benefits that automated tools cannot. Our experts find complex business logic flaws and test your team’s ability to respond to a live threat. You get a clear report showing what we found and the exact steps to fix it, which helps you meet compliance requirements like SOC 2 and PCI DSS.
An Affordable and Fast Security Alternative
We know the frustrations of dealing with old-school pentesting companies: insane prices, slow timelines, and reports filled with fluff. Our model is built for speed and value. We deliver comprehensive reports within a week so your team can start fixing things immediately.
Our pentesters hold top certifications like OSCP, CEH, and CREST, guaranteeing you get expert-level testing without the enterprise price tag. This is similar to red teaming, which you can learn about in our guide on what red team testing is. Our adversary simulation services give you the benefits of advanced testing in an affordable way.
How Simulation Differs From a Pen Test
People use “adversary simulation” and “penetration testing” like they’re the same, but they’re not. While both test your security, they answer different questions. Getting this right is key to spending your security budget wisely.
Think of a standard penetration test like a building inspector checking every window and door for a weak lock. The goal is to find as many potential entry points as possible. It's broad, methodical, and great for general security hygiene and compliance.
Adversary simulation is different. It’s like staging a realistic break-in where our team pretends to be a specific attacker with a single goal, like stealing your customer data. It’s not about finding every flaw, but testing if you can stop a live attack.
Pentesting Finds Flaws, Simulation Tests Response
A traditional pen test gives you a wide-angle view of your security weaknesses. It answers the question, "What are all the ways an attacker could get in?" Our team methodically pokes your systems to create an inventory of every vulnerability we can find.
An adversary simulation answers a more pointed question: "If an attacker came for us today, would we notice?" This approach is narrow but deep. Instead of trying every door, our team might use a single, stealthy technique to achieve an objective, just like a real threat actor would.
A Simple Comparison of Security Tests
So, which one do you need? Your goal determines the right test. Are you trying to find a long list of bugs for your developers, or do you need to know if your team will catch a stealthy intrusion? This table breaks down the core differences.
| Aspect | Penetration Testing (Pen Test) | Adversary Simulation |
|---|---|---|
| Primary Goal | Find as many vulnerabilities as possible. | Test detection and response capabilities. |
| Scope | Broad; covers a wide range of systems. | Narrow; focused on specific objectives. |
| Approach | "Depth-first" or "breadth-first" search for flaws. | Mimics a real attacker's tactics (TTPs). |
| Stealth | Usually noisy and easy to detect. | Stealthy; tries to avoid detection. |
| Deliverable | A list of vulnerabilities and fix recommendations. | A timeline of the attack and response gaps. |
A pen test is about cataloging weaknesses, while a simulation tests your defensive reflexes under pressure. For more on this, see our guide on penetration testing vs. vulnerability assessments.
You Do Not Have to Choose One
For most startups and SMBs, paying for separate pen tests and adversary simulations is too expensive and slow. That’s why our manual pentest services are designed to give you the best of both worlds. We combine broad vulnerability discovery with goal-oriented attacks to test your defenses.
This hybrid approach gives you the comprehensive vulnerability list you need for compliance, plus the real-world context that shows which flaws pose a business risk. You understand which problems matter most because you've seen how a real attacker, played by our OSCP, CEH, and CREST certified professionals, could exploit them.
Real Attack Methods Adversaries Use Now

Forget the Hollywood hacker. Real-world cyberattacks are much sneakier, preying on human trust instead of just software flaws. Attackers know the easiest way into your network is by tricking an employee or using a stolen password. They're not breaking down digital walls; they're walking in through the front door.
Our adversary simulation services focus on these realistic scenarios. We show you how an attacker would use a single compromised account to move silently through your network. This is why a manual penetration test is so vital; it tests your defenses against the actual methods criminals use.
The New Frontline Is Employee Identity
The game has changed. Attackers have largely abandoned noisy attacks in favor of stealthy intrusions that abuse legitimate access. Shockingly, most intrusions now rely on abusing valid credentials and tools already on your systems. This makes identity the new security perimeter, and it's where most companies fail.
Attackers are no longer just hacking systems; they are logging in.
Common Tactics We See and Simulate
Attackers love the path of least resistance. Our OSCP, CEH, and CREST certified pentesters mimic these simple but effective techniques during a manual pen testing engagement to see if your team can spot them. A few common tactics include credential stuffing, password spraying with passwords like "Winter2026!", and phishing for credentials.
These methods are all designed to steal one thing: a valid set of credentials. Once an attacker has those, they look just like a regular employee to your security tools. This makes them incredibly difficult to detect without a trained human eye. For more foundational knowledge, you can read about What Is Encryption and its role in data protection.
Why Your Security Tools Are Not Enough
Your security software is important, but it often looks for loud, obvious attacks. It struggles to identify an attacker who is using legitimate login credentials and your own internal tools against you. This is a massive blind spot for automated tools.
An automated scanner can't tell you if "Bob from accounting" is actually an attacker using his stolen password. A manual penetration testing engagement can. Our adversary simulation services are designed to expose these exact gaps by testing your team's ability to detect suspicious behavior, not just known malware.
When Your Business Needs This Service
Thinking about a pen test is a business decision, not just a technical one. It's not a question of if you need to test your security, but when it makes sense for your budget and risk. For most, the first push comes from a looming compliance audit.
Frameworks like SOC 2, HIPAA, and PCI DSS demand security testing. A manual penetration test is what auditors look for as proof you've protected sensitive data. Skip it, and you're looking at failed audits, big fines, and a huge loss of customer trust.
Compliance Is a Major Security Trigger
Meeting regulatory requirements is the number one reason companies seek our adversary simulation services. In many industries, it's a non-negotiable part of staying in business. A thorough pen test is the fastest way to give auditors the third-party validation they need.
Our affordable, manual pentests check those compliance boxes quickly. Our OSCP, CEH, and CREST certified team delivers the detailed reports auditors require in about a week. Key frameworks that require a penetration test include SOC 2, PCI DSS, HIPAA, and ISO 27001.
Protect New Products and Major Updates
Another critical time to get a penetration test is right before you launch something new. Rolling out a new app, moving to the cloud, or pushing a major update can create unexpected vulnerabilities. Think of it as security quality assurance.
An affordable pen test before you go live gives you confidence that your cool new features didn't accidentally create a backdoor for attackers. Since we work fast, you won't have to delay your launch for months waiting on a security report. Proactive testing is far cheaper than cleaning up after a data breach.
The Financial Case for Proactive Testing
Getting a pen test is about managing financial risk. Data breaches are expensive, and as recent cybersecurity threat reports show, attacks are on the rise. Waiting for an attack to happen is a gamble most businesses can't afford to lose.
A manual penetration testing engagement is a smart, affordable way to check your security without the catastrophic price tag of a real breach. When you invest in our fast and affordable adversary simulation services, you aren't just buying a report; you're protecting your bottom line.
Choosing The Right Simulation Partner
Finding the right security partner is the difference between getting actionable insights and wasting your budget on a useless report. Too many firms are slow, overpriced, and deliver little more than a PDF of scanner results. This isn't about finding the biggest brand name; it's about finding a team that is fast, affordable, and delivers real value.
We understand that for a startup or SMB, a security engagement has to move quickly.
Look For Speed and Transparent Pricing
The biggest headache with traditional penetration testing firms is the waiting. An eight-week turnaround for a report is a joke when you have a compliance deadline looming. Delays kill momentum and waste money. A fast report means your developers can start patching vulnerabilities immediately.
Next, demand clear, upfront pricing. Surprise fees and vague "consulting hours" are common traps. A partner you can trust will give you a flat, affordable price for the pen test so you know exactly what you're paying before work begins. A great partner respects your time and your budget.
Verify Their Expertise and Certifications
Your security is only as strong as the experts testing it. A skilled human attacker finds the complex business logic flaws and chained exploits that lead to catastrophic breaches. Don't be shy about asking for proof of their skills; your business depends on it.
Ask any potential provider if their testers hold these top-tier certifications: OSCP (Offensive Security Certified Professional), CEH (Certified Ethical Hacker), and CREST (Council of Registered Ethical Security Testers). If a company gets evasive about certifications, they’re likely just reselling automated scans. Real adversary simulation services are driven by certified experts.
Demand a Manual, Not Automated, Pentest
Many firms will sell you a "penetration test" that is really just a prettied-up vulnerability scan. A scan is like a spell-checker; it catches common mistakes. A manual penetration testing engagement is like a professional editor digging in to find subtle flaws that software misses.
Ask them to walk you through their methodology. Is it a manual, hands-on process that simulates a real attacker, or do they just click "run" on a tool? Choosing the right partner means you’re investing in actual security. Get in touch with us through our contact form to see how our certified experts can help.
What To Expect From Your Final Report
A pen test is useless if the final report is a confusing mess of jargon that arrives weeks late. You paid for a roadmap to fix your security, not a phonebook of problems you can't act on. What good are findings if your technical team can't use them while they're still relevant?
We know you need insights fast. That’s why we deliver your final report within a week. This speed lets your team start patching vulnerabilities immediately. Our entire focus is on clear, actionable results, without the enterprise fluff.
A Report Built for Two Main Audiences
A great report gives leadership the business context they need and gives your technical experts the exact details they need to fix things. Your report should be split into two clean sections: an Executive Summary for your CISO and management, and a Technical Deep Dive for your IT and development teams.
The Executive Summary translates technical findings into business risk in plain English. The Technical Deep Dive provides step-by-step instructions showing how our OSCP, CEH, and CREST certified testers got in and, more importantly, precise guidance on how to fix every single vulnerability.
What a Good Security Report Includes
A valuable penetration testing report does more than just list what's broken; it gives you context and a clear path forward. It's the difference between a doctor saying "you're sick" and one who gives you a diagnosis, a prescription, and a full recovery plan.
A strong pen test report is a practical guide. It must detail not just what we found, but how we found it, why it matters, and exactly what your team needs to do to fix it. To see what that looks like, check out our guide on penetration testing report examples. This is how you ensure your investment delivers real value.
How Much Does a Penetration Test Cost?
The cost of any penetration test comes down to scope: how big and complex your systems are. Traditional firms will quote you massive fees. We don’t do that. Our business was built to offer affordable, flat-rate pricing for startups and SMBs, with a clear, fixed price upfront. No surprises.
Our goal is to make real, manual penetration testing accessible to everyone, not just large enterprises with huge budgets.
How Long Does a Pentest Take?
This is where we really stand out. A typical engagement with us, from kickoff to final report, is finished within one week. That’s our promise. We know you need to move fast, and waiting months for findings from a traditional firm isn't an option.
We deliver a comprehensive, actionable report in days, not months. This allows your team to start fixing vulnerabilities immediately, dramatically reducing your window of exposure. This rapid turnaround is essential for hitting a tight compliance deadline or securing a new product before it goes live.
What Certifications Do Your Pentesters Have?
Our pentesters are certified experts who think like attackers. Every member of our team holds top-tier industry certifications, which is your guarantee that you're getting a professional, expert-level assessment.
Our team's key certifications include OSCP (Offensive Security Certified Professional), CEH (Certified Ethical Hacker), and CREST (Council of Registered Ethical Security Testers). These aren't just letters after a name. They're your assurance that our adversary simulation services are performed by true professionals.
Is This a Real Manual Pen Test?
Yes, this is 100% manual penetration testing. We don't just run an automated scanner and send you a branded PDF of the results. That's not a real pentest, and auditors know the difference.
Our certified experts use their skills and creativity to mimic a real-world attacker, uncovering the complex flaws that automated tools always miss. You're getting a genuine, hands-on pen test focused on finding and validating risks that actually matter. Ready to secure your business? Contact us today by filling out our contact form to get a clear, upfront quote at https://www.affordablepentesting.com.
.svg)
