What is red team testing? It’s not just another security scan. It's a real-world stress test for your entire organization, showing you exactly how a hacker could break in and what damage they could do.
Imagine you've secured your office. A red team test is like hiring a team of experts to find a way past your defenses. They won't just check for unlocked doors. They’ll use any method a real attacker would, like social engineering or finding a weakness in your network, to achieve a specific goal.
Our OSCP, CEH, and CREST certified pentesters simulate a full-scale attack. We don't just find vulnerabilities; we show you how they can be chained together to steal data or take down your systems. This is the proof you need to show your defenses actually work.

Unlike a standard penetration test that gives you a long list of potential issues, a red team engagement answers one simple question: can a determined attacker achieve their objective? For IT managers, CISOs, and startup founders, this isn't just a compliance task. It's the ultimate fire drill for your security program.
Red Teaming vs Pentesting Explained
People often confuse red teaming with penetration testing, but they have very different goals. A penetration test or pentest is about finding as many security holes as possible within a set scope. A red team exercise tests your ability to detect and respond to a real, goal-oriented attack.
A standard pen test is like an inspection. It gives you a list of problems to fix. A red team test is a live simulation. It shows you if your security team can actually stop an intruder before they cause real damage. This is the kind of practical proof that auditors for SOC 2, HIPAA, and PCI DSS need to see.
How a Red Team Test Actually Works
A red team exercise isn't about running a scanner and handing you a generic report. It's a mission to achieve a specific "trophy," like getting access to your customer database. Our team uses all the same tactics real hackers do to get the job done.
This includes social engineering to trick employees, physical security tests to enter your office, and exploiting custom software. This approach finds attack paths that automated tools and routine pen tests always miss. It’s the best way to see how your security team performs under the pressure of a real attack.
Why Red Teaming vs a Pentest Matters
Many people use "red teaming" and "penetration testing" to mean the same thing, but they are different tools for different jobs. Choosing the wrong one means you waste money on a report that doesn't give you the answers you actually need.
Think of a standard penetration test like a building inspector with a checklist. They check every door and window for weaknesses within a defined area. It's structured, systematic, and gives you a detailed list of every vulnerability they find.
A red team engagement is like hiring spies to breach your fortress and steal the crown jewels. Their goal is to get the prize by any means necessary. They might exploit technology, trick an employee, or sneak in through an unsecured door.
What Is a Standard Penetration Test
A standard penetration test, or pen test, is a broad security audit focused on a specific target. It's designed to answer one question: "What are our known vulnerabilities?" Our certified pentesters probe a defined system, like your web app, to find as many security holes as possible.
The goal is to produce a complete list of flaws for your team to fix. It's a great way to get a security baseline for a specific asset. If you need a deeper dive, our guide on what is penetration testing has you covered.
How Is a Red Team Test Different
A red team test goes much further. It’s a goal-oriented attack simulation designed to test your company’s ability to detect and respond to a real adversary. Instead of just listing vulnerabilities, our OSCP and CREST certified experts chain them together to achieve a specific goal.
The focus shifts from "what's broken?" to "can an attacker cause real damage, and can we stop them?" It tests your entire security program under pressure including your technology, processes, and people. It's exactly the kind of evidence auditors for standards like SOC 2 and HIPAA want to see.
To get a better feel for the methods used, it helps to understand concepts like white-box and black-box testing, which are foundational to all security assessments.
Choosing the Right Test For Your Needs
So, which one do you need? It comes down to your immediate goal and budget. Choose a penetration test if you need to find flaws in a new app or satisfy a specific compliance requirement for one system. Our affordable pentests deliver a report in under a week.
Choose a red team test if you need to prove your security team can detect and respond to attacks. At Affordable Pentesting, we’ve streamlined both services to give you expert results without the high costs and slow timelines of traditional firms.
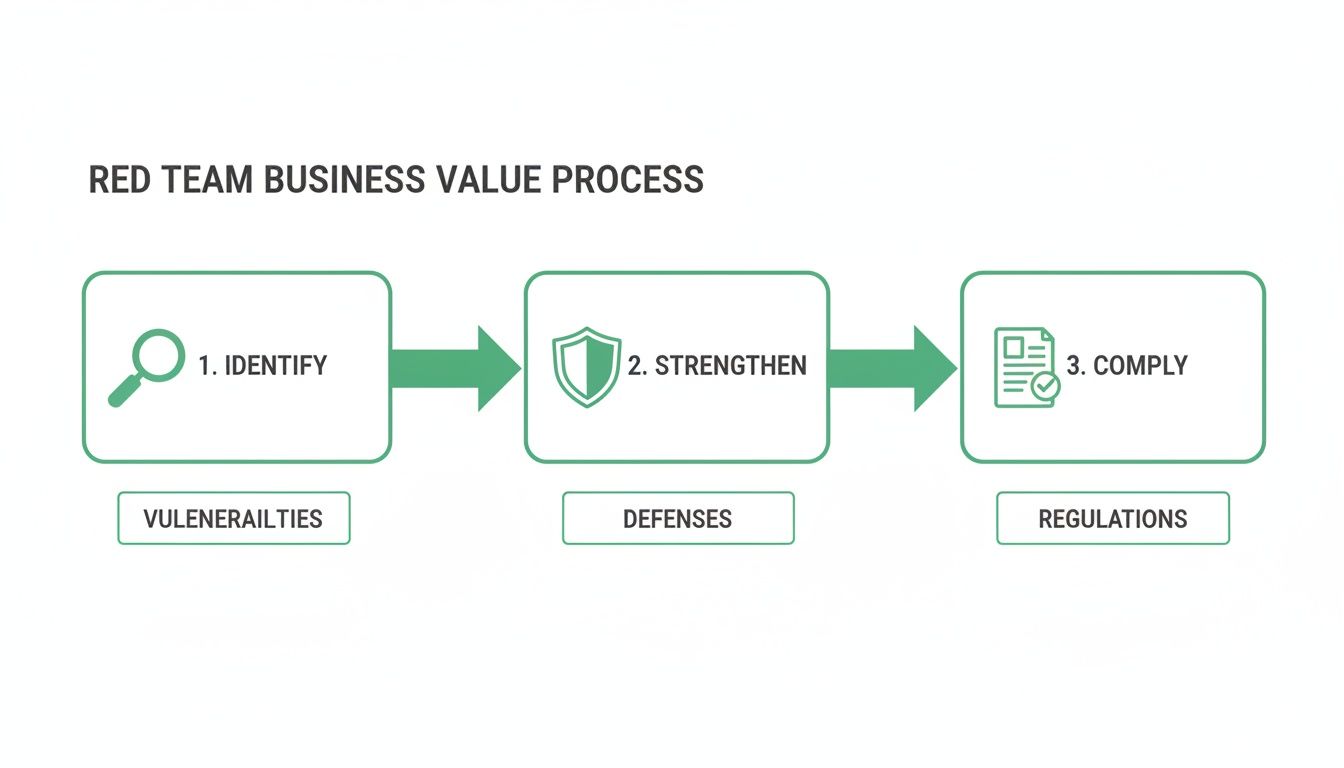
The Business Value of Red Teaming
A red team engagement answers a critical question: what’s the real-world business impact of your security flaws? It delivers a realistic measure of your readiness, showing exactly how an attacker could cause serious damage. This is the powerful evidence that auditors for SOC 2, HIPAA, or ISO 27001 love to see.
They want proof that your security controls can withstand a real attack. A red team report, detailing a simulated breach from start to finish, is the most compelling proof you can offer. This moves way beyond the generic checklists you get from a basic pen testing service.
Beyond Vulnerabilities to Real Intel
Automated scanners and basic pentests miss the big picture. They can't tell you how a creative attacker would chain minor issues together to achieve a full-blown breach. A red team exercise uncovers the critical weaknesses that scanners just can't see.
We find gaps in your human firewall by testing how easily your team can be phished. We test your incident response plan to see how quickly your team detects and shuts down an attack. You get real intelligence that helps you stop a breach, not just a list of generic problems.
Understanding the concrete risks, such as the rising threat of infostealer malware, makes the case for this level of testing clear. These examples prove that an affordable red team engagement can prevent a multi-million dollar data breach.
How a Red Team Operation Unfolds
So what does a red team operation look like? It’s not random hacking. It’s a methodical strike designed to think and act exactly like a real-world attacker, but in a controlled and safe way. The whole process is built to be fast, productive, and to give you an actionable report within a week.
The first phase is reconnaissance. Our OSCP and CREST certified experts quietly gather public information about your organization to build a map of your digital footprint. This information becomes the blueprint for the attack, just as a sophisticated adversary would prepare.
Next is the initial compromise. Using the intel gathered, our team executes a targeted attack to get a foothold. This might be a carefully crafted phishing email or exploiting a subtle vulnerability in a public-facing app. The objective is to get that first piece of access.
Once inside, our red team establishes persistence to make sure they can stay there. Then comes lateral movement, where our testers move through your internal network, escalating privileges and getting closer to the target. Our guide on the internal network pentest breaks this down in more detail.
The engagement ends when our team achieves the predefined objective. We then pull everything together into a clear, no-nonsense report delivered to you within one week. Research shows that companies using red teams experience fewer breaches, and you can learn more from a report on AI Red Teaming about the effectiveness of these simulations.
Choosing an Affordable Red Team Provider
For too long, real red team testing has been out of reach for anyone without an enterprise budget. But you don't have to choose between your budget and your security. The secret is finding a partner built for speed and affordability.
You can get a high-impact red team exercise that satisfies auditors for SOC 2 or HIPAA. It all comes down to picking a provider with proven skill. Modern, agile security firms like ours have cut the overhead, allowing us to offer expert-led exercises at a fraction of the cost.
Why Pentesters Certifications Are Critical
When you're looking for a provider, demand proof of certifications. These are your guarantee that the testers have legitimate, hands-on hacking skills. Look for these top-tier certifications as a non-negotiable baseline for quality.
Our team holds the certifications that matter: OSCP (Offensive Security Certified Professional), CEH (Certified Ethical Hacker), and CREST. These prove our pentesters can compromise systems in a live environment, a true test of practical skill. If a potential provider can't show you these, walk away.
A red team report that arrives three months after the test is useless. Threats change daily, and your team needs actionable intelligence now. We deliver a comprehensive, easy-to-understand report within a week, so your team can start fixing critical issues immediately. You can learn more about how to select the right pentest vendor in our guide.
The Red Team as a Service (RaaS) market is growing fast because it solves a critical problem for companies that need to meet ISO 27001 or PCI DSS requirements. You can find more on the growth of the RaaS market on 360iResearch.com.
Your Red Teaming Questions Answered
We get it. You have questions about red team testing and need clear answers. This section tackles the most common questions we hear from IT managers, CISOs, and startup founders who need to make smart security decisions on a budget.
A penetration test (or pentest) is a focused audit on a specific scope, like your web app, to find as many vulnerabilities as possible. Red team testing is a mission where our ethical hackers act like real adversaries to achieve a specific goal, testing your entire defense.
A vulnerability scan is an automated tool that checks for known flaws. A red team test is a manual, human-driven simulation where our OSCP or CREST certified experts think like a real cybercriminal. A scanner can’t tell you if your team will fall for a phishing link, but a red team will find out.
With traditional firms, red team engagements can drag on for months. Our entire model is built to be fast. A typical red team engagement with us is wrapped up in one to two weeks, delivering the actionable results you need right away.
Safety is our top priority. Before the test, we work with you to establish strict rules of engagement that define what's in scope and what's off-limits. Our certified professionals are experts at operating within these boundaries to ensure the test is controlled and non-disruptive.
You won't get a 500-page document full of jargon. Within a week, you'll receive a concise report with an attack narrative, business impact analysis, and prioritized recommendations. It’s all part of our mission to deliver effective security without the high costs and long waits.
At Affordable Pentesting, we believe every business deserves access to high-quality, manual penetration testing and red teaming. If you’re tired of high prices and slow timelines, get a no-nonsense quote from us today. Visit us at https://www.affordablepentesting.com to see how we can help you secure your business and meet your compliance goals.
.svg)
