You need a cloud pentest because your auditor is waiting, your customers are asking questions, and your cloud stack probably changed three times this month. Then a legacy firm shows up with a giant statement of work, a long timeline, and a price that feels built for public companies, not startups or SMBs.
That model is broken.
Most smaller teams don't need theater. They need a fast, affordable cloud penetration testing service that finds real issues, gives clear fixes, and produces a report an auditor can use. If a vendor needs forever to schedule, forever to test, and forever to write the report, they're wasting your time.
Stop Overpaying for Slow Cloud Pentesting
Old-school pentesting firms love drag. Long kickoff calls. Bloated scope documents. Weeks of waiting. Then the report lands and says obvious things your own team already suspected. That's not a smart buy. That's just expensive paperwork.
A good cloud pen test should be straightforward. You define the environment. The testers verify the scope. They test what you control. Then you get findings you can act on fast.
Why cloud testing is not optional
Cloud risk isn't slowing down. The cloud security penetration testing segment is projected to grow at the highest CAGR of 15.9% through 2031, and SMEs are driving demand with a 15.4% CAGR, largely because compliance requirements like PCI DSS 4.0 and HIPAA keep pushing cloud pentesting from “nice to have” into “required before the audit” territory, according to MarketsandMarkets on the penetration testing market.
That growth doesn't mean you should accept enterprise pricing or enterprise delays. It means more companies are finally realizing the cloud provider doesn't secure their mistakes for them.
Practical rule: If your team stores customer data in AWS, Azure, or GCP and you're heading into SOC 2, PCI DSS, HIPAA, or ISO 27001 work, stop treating cloud penetration testing like a someday project.
What SMBs should demand instead
You should expect a service model built for speed and clarity:
- Fast scoping: A short call should be enough to define assets, accounts, apps, and goals.
- Human-led testing: Real testers should validate attack paths, not just launch a scanner and leave.
- Useful reporting: Your report should explain impact in plain English and tell your team what to fix first.
- Audit-ready output: Compliance teams need evidence, not a vague summary slide deck.
The biggest scam in this space isn't only price. It's delay. A pentest delivered too late is almost as bad as no pentest at all.
The better way to buy a pentest
When getting your brakes checked, for instance, you don't want a shop that keeps your car for a month and hands you a glossy brochure. You want a mechanic who finds the bad parts, shows you what's broken, and gets you moving again.
That's how cloud penetration testing services should work for startups and SMBs. Fast. Focused. Affordable. No nonsense.
What Is Cloud Penetration Testing Anyway
Cloud penetration testing is an authorized attack on your cloud environment to see how an attacker could break in, move around, steal data, or abuse weak access. That includes your cloud accounts, storage, APIs, workloads, identities, and app-level configurations.
It does not mean attacking AWS, Azure, or GCP themselves. It means testing how you've set things up inside those platforms.

The apartment rental analogy
Cloud security confuses people because they assume the provider handles everything. They don't.
Think of the cloud like renting an apartment. The landlord is responsible for the building structure, the roof, and the main entrance. You're still responsible for locking your own door, managing who gets keys, and not leaving the windows open.
In cloud terms:
| Responsibility | Cloud provider handles | You handle |
|---|---|---|
| Physical infrastructure | Data centers, hardware, base platform | No |
| Core managed platform security | Underlying service operation | No direct control |
| Your identities and permissions | No | Yes |
| Your data exposure | No | Yes |
| Your app logic and APIs | No | Yes |
| Your storage settings and access rules | No | Yes |
That's why a penetration test matters. It checks your locks, not the landlord's concrete.
What a cloud pen test actually looks at
A proper cloud pentest usually focuses on the parts customers misconfigure most often:
- IAM and access control: Who can assume roles, change settings, or reach sensitive systems
- Storage exposure: Buckets, blobs, snapshots, and backups that are too open
- APIs: Endpoints that trust the wrong user, expose too much data, or skip authorization checks
- Serverless functions: Logic and permission mistakes in functions that can be abused
- Containers and orchestration: Weak isolation, exposed secrets, and dangerous runtime settings
If your environment relies heavily on APIs, it helps to review practical API testing strategies so your team understands how auth, input handling, and endpoint behavior affect cloud risk.
A cloud penetration test is less about open ports and more about bad decisions encoded into permissions, workflows, and integrations.
Why this differs from traditional pen testing
Traditional network testing looks for things like exposed services and weak perimeter controls. Cloud testing shifts the focus toward identity, permissions, configuration, and the ways services talk to each other.
That matters because cloud environments change constantly. A new role, a rushed deployment, or one sloppy API permission can create a hole big enough for an attacker to walk through without ever “hacking” the provider.
Why Your Cloud Environment Is So Vulnerable
Most cloud breaches don't happen because AWS or Azure forgot how to secure a data center. They happen because customers misconfigure access, storage, or trust relationships. That's the ugly truth.
The most dangerous cloud weakness is often boring at first glance. A role has too many permissions. A function can assume another role. A bucket is reachable by something that shouldn't touch it. Small mistake, big blast radius.

IAM is where small mistakes become huge breaches
Identity and Access Management, or IAM, controls who can do what in your cloud account. When it's loose, attackers don't need magic. They just follow the permissions you accidentally handed them.
Through 2025, 99% of cloud breaches will stem from customer misconfigurations, and testers often find wildcard-heavy roles that let them pivot from a low-privilege token to full admin access, compromising up to 80% of multi-account AWS environments with poor least-privilege enforcement, according to this breakdown of cloud misconfiguration and IAM privilege escalation.
That looks like this in plain English:
- A tester gets access to a weak user or temporary token.
- That token can list roles or interact with a service it shouldn't.
- A Lambda function, EC2 role, or trust policy lets the tester jump sideways.
- The tester chains those permissions together until they reach sensitive data or admin power.
That's not a movie plot. That's normal cloud abuse.
Common weak spots we see in cloud environments
A specialized pen test for cloud assets should look for issues like these:
- Overpowered roles: Service accounts with broad wildcard permissions
- Loose storage access: Buckets or snapshots exposed to users, apps, or external paths they shouldn't trust
- Bad trust relationships: One role can assume another with almost no restriction
- Serverless abuse paths: Functions with permissions far beyond their real job
- Container mistakes: Secrets in images, weak runtime controls, or paths for breakout and lateral movement
For a broader view of these exposure patterns, this overview of cloud computing and security risks is a useful reference.
Why generic tests miss cloud-specific flaws
A generic network tester might say your perimeter looks fine. Great. Meanwhile, an attacker logs in with stolen credentials, abuses an app role, reads storage through legitimate APIs, and leaves almost no noisy signs behind.
That's why cloud penetration testing services need cloud-native thinking. The tester has to understand role chaining, trust policies, temporary credentials, storage controls, serverless behavior, and how your app uses the platform.
If your vendor treats cloud like “just another network,” expect missed findings.
Cloud environments are vulnerable because they're flexible. Flexibility is great for shipping product. It's also great for shipping mistakes at scale.
How We Scope Your Cloud Penetration Test
Scoping a cloud penetration test shouldn't feel like a legal negotiation. It should feel like a technical planning session with adults. We need to know what you run, what you control, what compliance goal matters, and where an attacker would get value.
The scope changes based on whether you're using infrastructure, platform services, or a SaaS product built on cloud infrastructure. That's why one-size-fits-all pentesting wastes money.
What gets tested in IaaS PaaS and SaaS
Here’s the simple version:
| Model | Typical examples | What usually falls in scope |
|---|---|---|
| IaaS | Virtual machines, storage, security groups, IAM | Configurations, roles, exposed services, storage, workloads |
| PaaS | Managed app platforms, databases, serverless components | App permissions, service integrations, API paths, access controls |
| SaaS you built | Your web app running in the cloud | Tenant isolation, auth flows, APIs, admin controls, storage exposure |
What stays out of scope is just as important. The provider's own underlying infrastructure is off-limits. Your penetration testing service should focus on customer-controlled assets and configurations.
Manual testing is where the value lives
Automation is useful for speed. It is not enough by itself.
Manual penetration testing uncovers up to 2000% more vulnerabilities in cloud configurations and business logic than automated scanning alone, and 68% of cloud attacks involve stolen credentials, which is why human testers are needed to simulate identity-based attacks realistically, according to AppSecure's cloud security statistics for 2025.
That matters because cloud attacks are often chained. A scanner might flag a role. A human tester figures out that role can reach a function, that function can access a secret, and that secret provides access to customer data.
What a practical scope discussion should include
A useful scoping call should answer questions like these:
- Which cloud platforms are involved: AWS, Azure, GCP, or a mix
- What assets matter most: production apps, APIs, admin portals, storage, CI/CD, serverless, containers
- What access model makes sense: black box, gray box, or credentialed review
- Which compliance goal drives urgency: SOC 2, PCI DSS, HIPAA, ISO 27001
- What evidence your auditor expects: executive summary, technical detail, remediation guidance, retest options
If your team is also dealing with credential theft risk on endpoints, it's worth understanding the rising threat of infostealer malware, because stolen session data and credentials often become the starting point for cloud abuse.
What qualified testers should know
Don't hire a vendor that only knows old network gear. Cloud work needs testers who understand:
- IAM attack paths
- Serverless services like Lambda
- Containers and orchestration
- Infrastructure as Code
- API authorization logic
OSCP, CEH, and CREST certifications don't guarantee quality, but they do show the tester took the craft seriously. If a provider can't explain how they test cloud-native risks and only talks about scanners, keep walking.
A practical place to compare methodology against tooling is this guide to cloud security assessment tools.
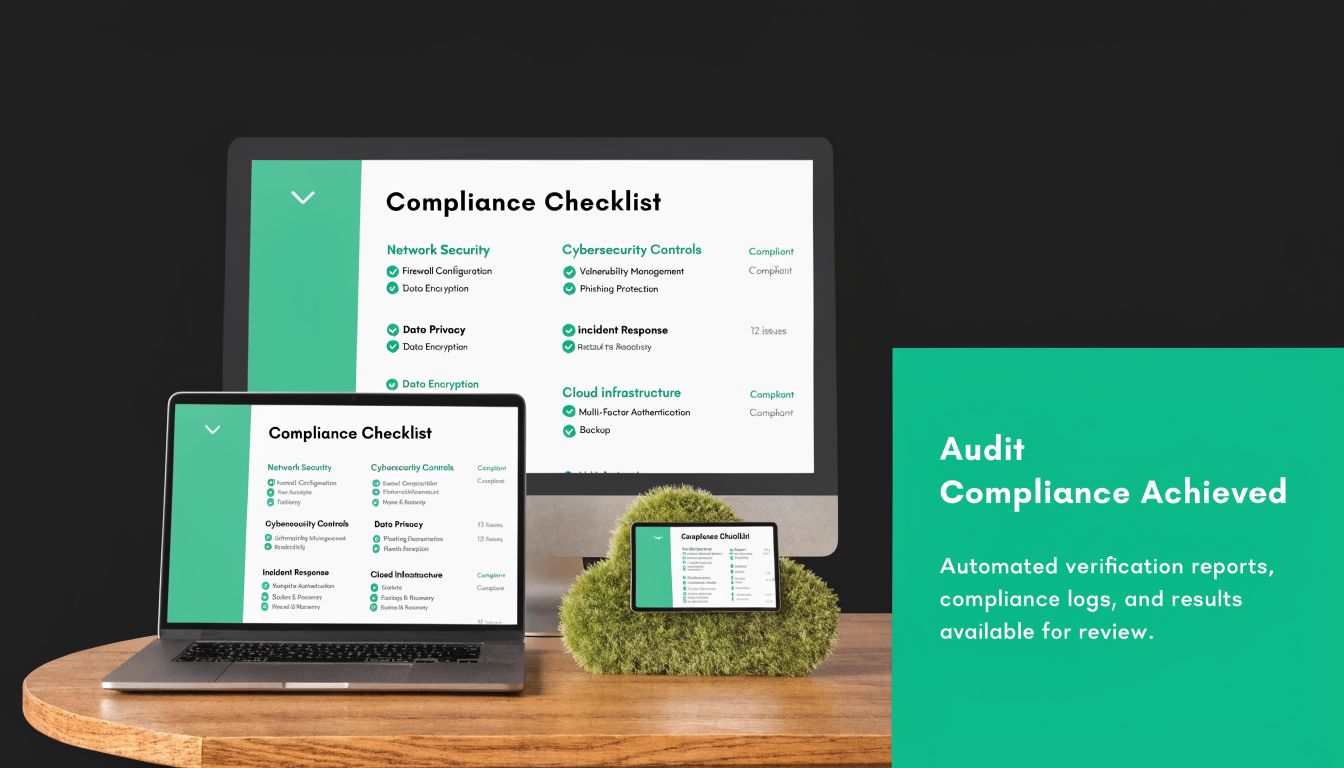
Passing Your Audit With Cloud Pentesting
A lot of teams buy a penetration test for one reason. An auditor asked for it. That's fine. Compliance pressure is real. The mistake is treating the pentest like a check-the-box PDF instead of evidence that your controls work.
Auditors don't want a dramatic story. They want proof that you tested the environment, identified weaknesses, rated the risk, and fixed what matters.
What auditors are actually looking for
For SOC 2, PCI DSS, and HIPAA, the specifics differ, but the practical expectation is similar. You need evidence that your organization proactively assessed cloud risk and didn't just assume your provider handled it.
A report that helps with audits should include:
- Clear scope: What accounts, apps, APIs, and cloud assets were tested
- Method summary: Enough detail to show the work was real and relevant
- Findings with risk ratings: Not just a list, but a prioritized list
- Proof of impact: Screenshots, reproduction notes, or attack paths where appropriate
- Remediation guidance: Concrete fixes your engineers can apply
- Retest option: Useful when the auditor wants closure on major findings
Why generic reports create audit pain
Bad vendors produce reports that sound technical but answer none of the auditor's real questions. They use vague language, shallow findings, and generic remediation like “improve security posture.” That's useless.
Your compliance team needs a report that bridges technical evidence and business control language. If your pentest report can't support a discussion with your auditor, you paid for noise.
Audit shortcut: Ask vendors to show a sample report before you sign. If it reads like a scanner export, it's not audit-ready.
How cloud pentesting supports common frameworks
Different standards ask the same basic question in different ways. Have you tested for exploitable weaknesses, and can you prove you addressed them?
For teams preparing for SOC 2 specifically, this resource on SOC 2 penetration testing gives a useful picture of the evidence auditors usually expect. In practice, a strong cloud pentest helps you show that your access controls, application boundaries, and cloud configurations weren't left to guesswork.
That matters even more in cloud-heavy environments because control failures tend to stack. One bad permission can undermine several written policies at once.
The report should help engineers too
Compliance officers need evidence. Engineers need fixes. Good cloud penetration testing services support both.
The best reports don't drown your team in theory. They say what was found, why it matters, how it could be abused, and how to fix it without wasting a sprint arguing about wording.
How To Choose The Right Pentest Vendor
Most buyers ask the wrong opening question. They ask, “How much does a pentest cost?” The better question is, “How quickly can you test our actual cloud risk and give us a report our auditor won't reject?”
A cheap but shallow pen test is a waste. A premium but slow penetration testing engagement is also a waste. You need the middle path. Fast enough to matter, deep enough to catch real issues, and clear enough for compliance.
The vendor checklist that actually matters
Use this list before you sign anything:
- Speed of delivery: Ask how soon testing can start and when the report lands. If the timeline sounds bloated, it probably is.
- Cloud-specific experience: Ask how they test IAM, storage exposure, APIs, serverless functions, and containers.
- Human expertise: Verify the team includes testers with OSCP, CEH, or CREST backgrounds.
- Report quality: Ask for a sanitized sample. You want business impact, technical proof, and remediation steps.
- Scoping sanity: The provider should define in-scope assets clearly without burying you in process.
- Retesting process: If you fix critical issues, there should be a simple path to validate closure.
Don't buy scanner theater
Some vendors basically sell a tool with a consultant attached. They run automated checks, pad the report, and call it a cloud pentest service. That's not enough for modern cloud risk.
As of 2026, many firms still struggle to combine AI-driven tools with human oversight, and over-reliance on automation can miss up to 15% of human-discoverable logic flaws, which makes a hybrid model far more useful for cost-effective compliance validation, according to SentinelOne's look at cloud penetration testing tools.
That finding matches what buyers already feel in the field. Tools are good at breadth. Humans are good at judgment. You want both, but not in the wrong order.
Good vendors use tools to move faster. Bad vendors use tools to avoid thinking.
Questions to ask on the first call
Try these and see how the vendor responds:
- How do you test IAM privilege escalation in AWS, Azure, or GCP?
- How do you validate API authorization flaws manually?
- What parts of serverless and container environments do you include?
- How quickly do we get the draft report?
- Can your report support SOC 2, PCI DSS, or HIPAA review?
- Who is doing the testing, and what certifications do they hold?
If the answers are vague, salesy, or loaded with buzzwords, move on.
One practical option for SMBs
For smaller teams that need cloud testing tied to compliance, Affordable Pentesting offers cloud penetration testing for AWS, Azure, and GCP delivered by OSCP, CEH, and CREST certified testers, with services aimed at frameworks like SOC 2, HIPAA, PCI DSS, and ISO 27001. That's the kind of direct alignment buyers should look for whether they choose that provider or another one.
The point is simple. Buy expertise and clarity. Don't buy brand theater.
Our Simple Cloud Pentest Engagement Workflow
A good engagement should feel easy to follow. No black box. No mystery delays. No endless project-management overhead. Just a clean sequence from scope to report.
This is the workflow most buyers should expect from a modern cloud penetration testing service.
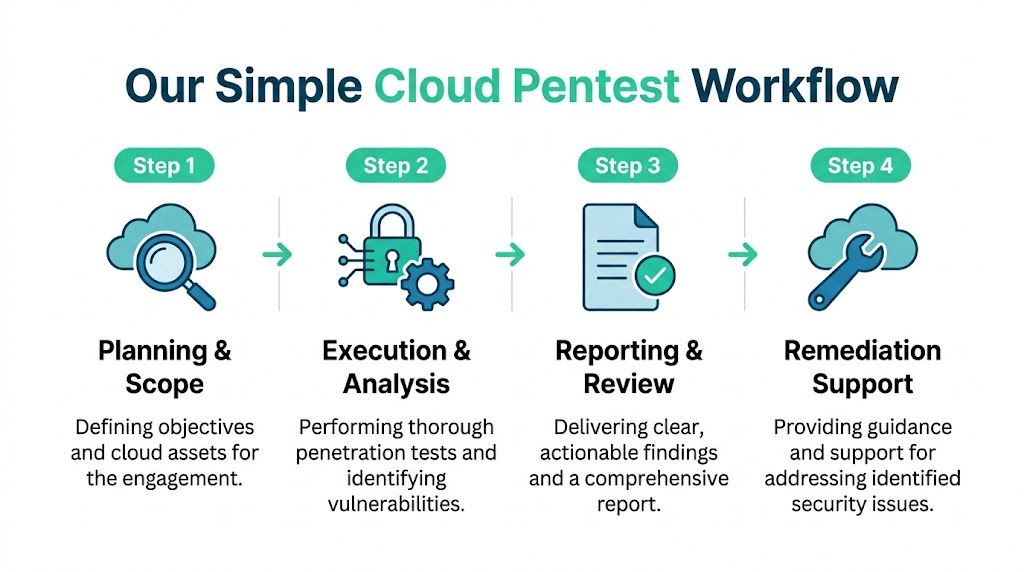
Step one and step two
First comes the scoping call. You share the cloud platforms, target assets, compliance driver, and any known constraints. The provider confirms what is in scope and what access is needed.
Next comes kickoff. You meet the testing team, exchange the required details, and lock in the test window. This should be organized and short, not a calendar-eating ritual.
Step three and step four
Then the penetration test starts. Testers review the environment, simulate realistic attack paths, validate exposures manually, and collect proof for every meaningful finding.
After that, reporting happens fast. You get a draft report, a review discussion, and a final version your engineering and compliance teams can use. The right provider should also answer remediation questions instead of disappearing after sending the PDF.
What a clean workflow feels like
Here are the signs the process is healthy:
- You know who is testing: Not just the sales rep, the actual testers
- You know what is being tested: Accounts, apps, APIs, storage, identities, and boundaries
- You get updates without chasing: Important if deadlines are tight
- You receive a usable report quickly: Especially when an audit is close
Slow communication during scoping usually predicts slow communication during remediation.
If a vendor makes a simple pen testing engagement feel complicated, the rest of the project won't improve.
Get Your Cloud Pentest Started This Week
If you're dealing with a customer questionnaire, an upcoming audit, or a growing cloud stack, waiting doesn't help. Cloud problems don't get smaller with time. They spread insidiously through roles, functions, APIs, and storage settings until someone finally looks closely.
You also don't need to accept the old enterprise model to get competent testing. You can get a fast, affordable cloud penetration testing service that uses certified humans, focuses on real findings, and gives your team a report they can use right away.
The short version
Here’s what matters most:
- Cloud risk is your responsibility: The provider secures the platform. You secure your use of it.
- Manual testing still matters: Especially for IAM, API abuse, and chained logic flaws.
- Compliance needs evidence: A real report helps auditors and engineers at the same time.
- Vendor choice matters: Buy speed, clarity, and certified expertise. Skip fluff.
If your current option is overpriced, slow, or vague, pick a different vendor. This market is crowded enough now that you don't have to settle for bad service.
Security work shouldn't feel like buying a luxury car when you just need reliable brakes. Get the test done. Get the report. Fix what's broken. Move on with your business.
Need a fast, affordable, audit-ready cloud pen test? Contact Affordable Pentesting through the contact form to scope your cloud penetration testing services this week and get a clear path to findings, remediation, and compliance evidence.
.svg)
