Compliance risk management is your company's rulebook for staying out of trouble. Think of it as finding and fixing problems that could get you fined under rules like HIPAA or PCI DSS. It's like following traffic laws to avoid a ticket, but the real goal is to prevent a huge crash.
Why Compliance Risk Management Matters
Compliance risk management isn't about just checking boxes. It’s a real strategy to protect your company from fines, lawsuits, and a trashed reputation. Ignoring it is like building a house on a swamp. It might look fine for a while, but eventually, it’s going down.
For IT managers and startup founders, this means understanding the specific rules for your industry. Whether you're protecting health records for HIPAA or credit card data for PCI DSS, the job is the same. Find your weaknesses and fix them before they become expensive problems.
A solid compliance program isn't just an expense; it's an investment. It protects your business, builds customer trust, and gives you a real edge over the competition.
The rules are only getting more complex. This isn't just annoying; it can actively hurt your IT systems and data management. To handle this, you need a clear plan. A simple compliance risk management framework helps you organize your efforts so nothing important gets missed.
Your Practical Risk Management Process
Building a compliance risk management program doesn’t require a giant budget. For startups, the secret is a simple, repeatable process. Let's walk through a five-step cycle that any IT manager or founder can use to get started right away.
This visual shows how to turn compliance from a headache into a manageable process.
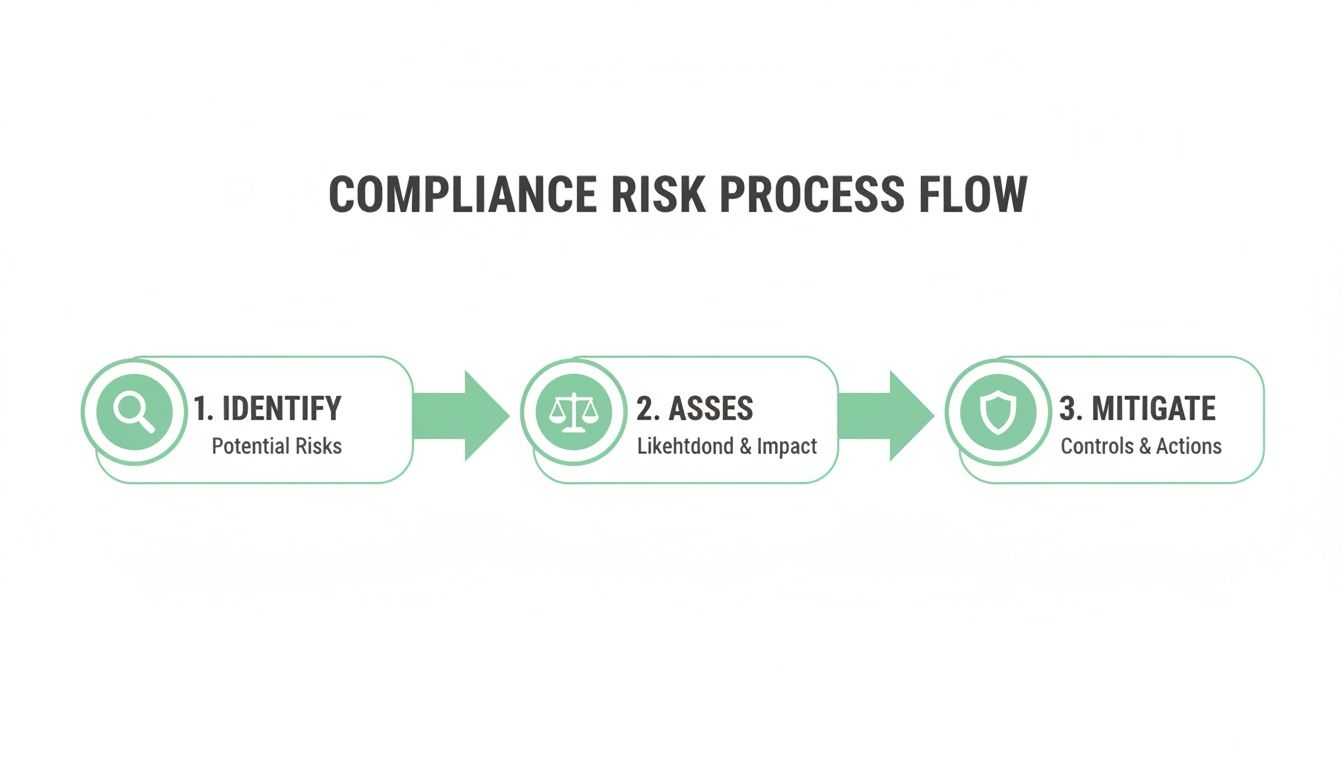
As you can see, it's a continuous cycle. You identify, you assess, and you take action.
Identify All of Your Potential Risks
You can’t fix what you don't know is broken. The first step is discovery. This means taking an honest look at your systems, data, and processes to find the weak spots that could lead to a compliance failure.
Start by asking some basic questions: What rules apply to us, like HIPAA or SOC 2? Where is our most sensitive data stored? Who has access to that data? Answering these gives you a map of your potential compliance landmines.
Assess and Prioritize Your Biggest Threats
Okay, you have a list of potential risks. Now you need to figure out which fires to put out first, because not all risks are equal. Assess them by looking at how likely something is to happen and how bad the damage would be.
A high-impact risk that's very likely to happen, like a customer database with weak passwords, should jump to the top of your list. This practical approach ensures you’re spending your time and money where it matters most. For more detail, our guide on a cybersecurity risk assessment can help.
Mitigate and Fix All The Problems
Mitigation is just a fancy word for fixing things. This is where you implement controls to reduce or eliminate your biggest risks. A "control" can be a new policy, a security tool, or even just employee training.
Examples include enforcing multi-factor authentication (MFA) or encrypting sensitive data. This is also where a penetration test becomes your most important tool. A pentest is a control that proves all your other controls are actually working, not just checking a box.
Monitor and Test Your Defenses Continuously
Compliance isn't a one-and-done project. Threats change, systems get updated, and new weak spots appear all the time. You need to keep an eye on your controls to make sure they're still doing their job.
This is where regular, affordable security testing makes all the difference. Instead of a painful annual audit, a fast pen test gives you real-time feedback. Our team of OSCP, CEH, and CREST certified pentesters delivers reports in under a week, so you can find and fix issues fast.
Report and Improve Your Security Program
The final step is to document everything. Reporting your findings, the actions you took, and the results creates a clean audit trail. This is exactly what auditors for frameworks like SOC 2 or ISO 27001 want to see.
This documentation isn't just for them, it's for you. It helps you track your progress and continuously improve your compliance risk management program. By making affordable penetration testing part of this cycle, you get the proof you need, fast.
The Top Compliance Risks Businesses Face
Let's talk about the real threats. While compliance can feel like a maze, most of the danger boils down to a few key areas. For modern businesses, these risks almost always circle back to cybersecurity and data privacy.
A single security incident can trigger painful audits and huge fines under frameworks like SOC 2, HIPAA, or ISO 27001. Understanding what’s at stake is the first step in building a defense that works.
Why Data Breaches Are Your Top Threat
Cybersecurity and data privacy are the biggest compliance challenges for businesses today. A recent analysis shows that 68% of compliance professionals see these as their top hurdles. You can learn more about the 2025 global compliance outlook to see why this is so important.
A data breach isn't just about losing files. It’s a direct violation of customer trust. For auditors, a breach is clear evidence that your security controls failed, making it much harder to prove you are compliant.
The question is no longer if you will face a cyber attack, but when. Regular testing is the only reliable way to manage this risk and satisfy compliance rules.
This is where a penetration test becomes a non-negotiable part of your compliance risk management strategy. It's the only way to find out if your defenses will hold up against a real attacker.
The Hidden Dangers of Insider Threats
Not all threats come from outside. Sometimes, the biggest risk is an employee who makes an honest mistake, like clicking a phishing link or using a weak password. This is called an insider threat.
Whether it’s on purpose or by accident, the result is the same: a potential data breach and a major compliance violation. Strong access controls and security training are your first line of defense, but you need a way to test if they are working. A thorough pen test helps identify weaknesses that could be exploited by an insider.
Why Third-Party Vendor Security Matters
Your security is only as strong as your weakest link, and often, that link is one of your vendors. If your cloud provider gets breached, your data is still at risk. This is known as third-party risk.
Compliance frameworks like SOC 2 hold you accountable for the security of your entire supply chain. This is why affordable and fast penetration testing is so valuable. It provides the assurance you need to prove your own systems are secure. Our OSCP, CEH, and CREST certified professionals can give you a clear report in under a week.
How Penetration Testing Proves Compliance
Compliance frameworks like PCI DSS and SOC 2 demand proof that your security works. A penetration test is that proof. It’s the difference between saying your house has locks and having an expert try to pick them.
Think of a pentest as a fire drill for your cybersecurity. We ethically hack your systems to find the same holes a real attacker would. This is how you show auditors you've done your due diligence and moved your compliance from paper to reality.

This process is a non-negotiable part of modern compliance risk management. It provides the independent validation that turns your security claims into credible evidence.
Why Auditors Require Penetration Test Reports
When an auditor shows up, they want objective evidence that your security is effective. A detailed penetration testing report from a certified professional is one of the strongest things you can hand them.
A good report shows you aren't just guessing about security; you're actively trying to break your own defenses to make them stronger. Our reports are built for this, clearly laying out the scope, our methods, our findings, and simple steps to fix every issue. This gives auditors everything they need to verify your security.
Moving Your Business Beyond Checkbox Compliance
Let’s be honest, many companies treat compliance as a checklist. They do the bare minimum to pass an audit, but this leaves them wide open. A real attacker doesn't care about your checklist; they only care about finding a way in.
A pen test forces you to move beyond that flimsy mindset. It asks, "Can an attacker get past our firewall?" instead of just, "Do we have a firewall?" It’s a proactive approach that focuses on real-world security.
True compliance isn't about having security on paper. It's about having security that works under pressure. A penetration test is the only way to prove it.
Our entire approach makes this step fast and affordable. We deliver detailed reports from our OSCP, CEH, and CREST certified experts in under a week. This gets you what you need to satisfy auditors and harden your defenses without the slow timelines and high costs of traditional firms.
Why Pentests Matter For Every Framework
Different compliance standards have unique rules, but they all point to one thing: the need for regular security testing. A penetration test is a versatile tool that helps you meet the demands of virtually any framework, including PCI DSS, SOC 2, HIPAA, and ISO 27001.
For example, our services help you meet key requirements, like the SOC 2 rule (CC7.1) that requires you to manage vulnerabilities. This detailed guide on SOC 2 penetration testing requirements provides an excellent overview of what auditors expect. Our team makes sure your testing aligns with these and other compliance needs.
Making Penetration Testing Fast and Affordable
For too long, startups and small businesses have been priced out of high-quality penetration testing. Old-school firms charge a fortune and take months to deliver a report. We built our service to fix this broken model.
We focus on delivering exactly what you need for compliance, without the enterprise overhead. By keeping our process lean, we provide comprehensive pen test reports that are both affordable and fast. You get the documentation you need for your auditors in under a week. If you are preparing for an audit, check out our guide on SOC 2 penetration testing.
Using Technology For Better Compliance
Let’s be honest, businesses are drowning in compliance paperwork. That’s why so many are turning to Governance, Risk, and Compliance (GRC) tools to automate the tedious stuff. They promise a clearer, more efficient way to manage your risk.
But here’s the trade-off: every new piece of software is another potential door for an attacker. As you use technology to streamline your compliance risk management, you also have to secure it. This makes fast, affordable security testing an absolute must.
The Double-Edged Sword of Compliance Tech
On one hand, technology is a huge help. Recent data shows that 82% of companies plan to invest more in tech to automate their compliance work. But a stunning 42% of leaders admit their current GRC systems need serious improvement. You can discover more insights about these compliance trends to see the full picture.
This means that while tools are being adopted quickly, they aren't always being implemented securely. A poorly configured GRC platform can become your biggest compliance failure. Your solution can quickly become your next problem.
Technology doesn't eliminate risk; it just moves it. Your compliance software is now a critical asset that needs to be protected just like your customer database.
A fast, affordable penetration test is a no-brainer here. It lets you validate the security of new tools before they're deeply embedded in your workflow. You can find and fix weak spots in your compliance stack without slowing down operations.
Validating Your Compliance Tools With Pentests
Imagine you just bought a new system to manage employee compliance training. It holds sensitive data about your team and their progress. How do you know this new platform is secure? You test it.
A manual pen test by our OSCP, CEH, and CREST certified professionals simulates a real-world attack on that software. We hand you a report in under a week with clear instructions on how to fix every issue. This proactive approach helps you hold your software vendors accountable for their security promises.
If you’re choosing tools, our guide on the best compliance management software can help. The best tool is both effective and secure, a fact you can only confirm through testing. Fill out our contact form to learn how a fast, affordable pen test can secure your tech.
Building A Real Culture Of Security
Your tools and policies are only half the battle. The strongest defense is a culture where every employee understands their role in protecting the business. It’s about making security and compliance everyone’s job, not just a task for IT.
This is where your compliance risk management program stops being a document and starts being a shared responsibility. When security is part of your company’s DNA, your team becomes your first and best line of defense.

Shifting From Annoying Mandate to Mindset
Let's be honest. For many employees, security feels like a set of annoying rules that get in the way. The goal is to flip that perception from a forced mandate to a protective mindset. This shift has to start at the top.
When leadership talks about why security matters, it sends a powerful message. It shows everyone that protecting the company is a core value. This helps your team see security for what it is: something that enables the business, not something that slows it down.
Practical Steps For Real Security Awareness
Building a strong culture doesn't need a massive budget. It’s about consistent, practical actions that reinforce good habits. Small, repeated efforts have a much bigger impact than a single, boring training session nobody remembers.
Here are a few simple but effective tactics. Use short, monthly security reminders that focus on one topic, like spotting a phishing email. Make it relatable by showing how a simple mistake can impact the company. And publicly recognize employees who report suspicious emails.
How A Pentest Serves As A Training Tool
A penetration test is more than a technical audit; it's one of the best educational tools you can have. When our OSCP, CEH, and CREST certified pentesters find a real vulnerability, it creates a powerful learning moment for your whole organization.
A pen test report turns a theoretical risk into a real, understandable problem. It shows your team exactly how an attacker could get in, making the threat feel immediate.
This context is invaluable. Instead of just telling your developers to "write secure code," you can show them a specific weakness found during a pen test and walk them through the fix. This turns a security finding into a hands-on lesson. Our affordable pentests deliver these learning moments fast, with reports in under a week.
Your Pentesting and Compliance Questions
Got questions about compliance risk management and penetration testing? We have direct answers. We’ll skip the jargon and focus on what matters to founders and IT leaders: getting a high-quality pentest that’s fast, affordable, and proves your security.
How Often Should My Business Get Pentested?
Most compliance frameworks like PCI DSS and SOC 2 say you need a penetration test at least once a year. But treating this as a simple annual chore is a mistake, especially for fast-moving companies.
If your product is constantly changing, your security risks are, too. That's why quarterly testing is becoming the new standard. The right frequency depends on your risk. Our affordable model makes it possible to test more often without draining your budget.
What Is A Manual Pentest And Why Does It Matter?
A manual penetration test means a real human expert, a certified ethical hacker, tries to break into your systems. It’s not just an automated scanner. Our pentesters have top certifications like OSCP, CEH, and CREST, and they use creativity to find flaws scanners miss.
An automated scanner checks if your doors are unlocked. A manual tester jiggles the handles, checks the windows, and looks for a key under the mat. They find complex flaws that only a human can, which is the kind of deep proof auditors want for your compliance risk management program.
Is A Pentest The Same As A Vulnerability Scan?
No, and this is a critical distinction your auditor understands. A vulnerability scan is an automated, surface-level check for known weaknesses. It's fast, but it’s noisy and often reports things that aren't real problems. It's a decent start, but it's not enough to prove you're secure.
A penetration test goes much deeper. Our experts don't just find a weakness; they try to exploit it to see if it's a real-world threat. This provides actionable proof of risk, which is why serious frameworks like SOC 2 require a true pentest.
How Do You Deliver A Pentest Report In One Week?
Frankly, traditional firms are slow because their processes are bloated with overhead. We built our service around speed because we know startups can't wait months for a report.
Our certified pentesters focus on two things: rigorous manual testing and clear, actionable reporting. We've stripped out all the corporate fluff that slows things down and inflates prices. You get exactly what you need for compliance risk management: a high-quality pen test report, fast.
At Affordable Pentesting, we deliver the fast, manual penetration testing you need to satisfy auditors and prove your security. We do it without the sky-high costs and frustrating delays of traditional firms. Our certified experts deliver actionable reports in under a week.
Ready to secure your compliance? Get a quote today from Affordable Pentesting.
.svg)
