You’re probably here because you need a pen test fast, your auditor is waiting, and the quotes you’ve seen are ridiculous. One firm wants a big kickoff call, another wants weeks of scheduling, and the one with the lowest price looks suspiciously like a vulnerability scan with a nicer PDF.
That old model wastes time and budget. Startups and SMBs don’t need a bloated enterprise engagement to satisfy SOC 2, PCI DSS, HIPAA, or internal risk reviews. They need low-cost penetration testing that focuses on the systems that matter, uses real human testers, and delivers a report quickly enough to be useful.
A good penetration test should help you fix real problems and give your auditor clean evidence. If it doesn’t do both, it’s not a bargain. It’s rework.
Stop Overpaying for Slow Penetration Testing
Traditional penetration testing firms still sell like it’s ten years ago. Long scoping calls. Slow scheduling. Expensive statements of work. Then you wait weeks for a report that tells you things your team already knew.
That model hurts smaller companies most. You’re trying to close a customer, pass an audit, or show your board that security work is moving. You don’t need ceremony. You need a penetration test that targets the right assets and returns a report within a week.
Why the old model keeps failing
A lot of firms price for complexity they haven’t even confirmed yet. They assume broad scope, layer on project management overhead, and hand work to junior staff who follow a checklist. You end up paying for process, not insight.
Worse, many buyers think a high quote means high quality. It doesn’t. A costly engagement can still produce a weak report if the testers don’t spend time manually probing your application, API, or external network.
Practical rule: If a vendor talks more about meetings than testing, keep looking.
What a better pentest looks like
A better approach is smaller, tighter, and faster. Scope one critical web app. Scope the API that handles customer data. Scope the external perimeter your auditor cares about. Then have certified testers work that target hard, write clear findings, and turn the report around quickly.
That’s how you get value from low-cost penetration testing. You cut waste, not depth.
If you want a grounded view of how pricing usually breaks down, review this guide on the cost of penetration testing. It helps separate normal costs from padded proposals.
What matters more than brand names
For startups and SMBs, the primary win is simple. You want manual validation, useful screenshots or proof-of-concept evidence, remediation guidance your developers can act on, and a report your auditor won’t reject.
You do not need a giant consulting logo on the cover.
You need a pen test, pen testing process, and penetration testing report that solve the immediate problem without creating three new ones.
Smart Scoping and Pricing for Your Budget
Most companies overspend on penetration testing because they scope badly. They ask vendors to “test everything,” then act surprised when the quote jumps. If your budget is tight, scope is the lever that matters most.
For small businesses, penetration tests typically range from $2,000 to $10,000, while mid-market organizations spend $20,000 to $50,000 annually. The global average breach cost reached $4.44 million in 2025, which is why even an affordable pen test is still a sensible investment, according to Bright Defense penetration testing statistics.
Start with what an auditor will care about
If you’re doing this for compliance, don’t test random assets just because they exist. Test the systems tied to your compliance boundary.
That usually means one or more of these:
- Customer-facing web app: The login flow, account area, admin panel, and anything that stores or processes sensitive data.
- Public API: Especially if it handles authentication, billing, health data, payment data, or customer records.
- External network exposure: VPN portals, firewalls, remote access services, and internet-facing hosts.
- Compliance-specific assets: The app or segment directly tied to PCI DSS, HIPAA, SOC 2, or ISO 27001 controls.
If you’re not sure whether you need a scanner or a real pen test, this breakdown of DAST vs Penetration Testing is useful. It explains where automated testing stops and where manual testing starts.
Scope small and go deep
A narrow scope doesn’t mean a weak test. It often means a better one.
If you ask a vendor to test one critical application, they can spend time chasing authentication flaws, access control issues, insecure workflows, and logic bugs. If you ask them to “look at our app, API, cloud, and network” on a tiny budget, they’ll spread thin and give you surface-level output.
A lot of SMBs often get burned. They buy breadth and lose depth.
A smaller scope with manual work beats a giant scope with checkbox testing.
Pick the right pricing model
Not every company should buy penetration testing the same way. Match the model to your stage and your compliance pressure.
| Test Type | Typical Scope | Estimated Cost | Estimated Timeline |
|---|---|---|---|
| Automated network scan | Up to 50 internal or external network IPs | $500 | Fast turnaround |
| External network pentest | 10 external IPs or less | $2,000 starting point | About a week |
| API pentest | Up to 25 endpoints | $3,000 starting point | About a week |
| Small business manual pentest | One key app, API, or small external scope | $2,000 to $10,000 | Usually within a week to a short engagement window |
| Mid-market annual program | Multiple recurring tests across the year | $20,000 to $50,000 annually | Ongoing |
Fixed price usually wins for SMBs
A fixed-price penetration test is usually the best option if your scope is clear. One app. One API. One external range. You know what you’re buying, and finance knows what it will cost.
That predictability matters when you’re trying to pass an audit without budget creep.
Subscription works when releases never stop
If your team ships often, a recurring model can make more sense. Instead of re-buying one-off tests every time something changes, you schedule testing as part of your release rhythm.
This works well for SaaS teams with frequent updates, but only if the vendor can keep pace and doesn’t bury you in coordination overhead.
Ad hoc testing still has a place
Sometimes you just need one clean report now. Maybe a customer asked for it. Maybe a PCI deadline landed. Maybe the board suddenly cares.
That’s fine. Just don’t let “urgent” become “vague.” Give the vendor a clear target, user roles, test window, and compliance goal.
A scoping checklist that saves money
Use this before you ask for quotes:
- Name the target clearly: One app, one API, or one external environment.
- Define the purpose: Audit evidence, release validation, investor diligence, or internal risk review.
- List user roles: Anonymous, normal user, admin, and any privileged workflows.
- Call out sensitive functions: Payments, file uploads, password reset, SSO, account recovery, health data access.
- Set the deadline upfront: If you need the report in a week, say it immediately.
Do this work before procurement gets involved. It cuts wasted back-and-forth and makes vendor quotes easier to compare.
Get Manual Testing Without Enterprise Prices
The biggest lie in this market is that low-cost penetration testing must mean automation only. That’s nonsense. Cheap automation-only work exists, yes. But affordable manual pentesting is possible when the scope is focused and the testers know what they’re doing.
Here’s the simple version. Scanners are good at finding obvious technical issues. Human testers find the problems that matter when a real attacker chains small weaknesses together.
Why manual work still matters
In 77% of external pentesting cases, the primary attack vector involved poorly protected web applications, and effective low-cost pentesting must combine scanning with manual exploitation, which uncovers 81% of high or critical findings, according to Zerothreat penetration testing statistics.
That should tell you exactly where to focus. If your vendor mostly talks about scanner coverage, but your risk lives in a web app or API, the test is already off track.
What certified testers do that tools miss
An OSCP, CEH, or CREST-certified tester doesn’t just run Burp Suite, Nmap, or Metasploit and dump the output. They ask basic attacker questions that tools can’t reason through well on their own.
Can a user move sideways into another account?
Can a normal user trigger an admin-only action?
Can a workflow be abused even when every individual request looks valid?
Can weak business rules be chained into something serious?
That’s where manual testing earns its keep.
If you need a plain-English explanation of testing approaches, this guide to black box testing vs white box testing is worth reading. It helps non-specialists understand why access level changes the test.
Two ways to keep manual testing affordable
The first is limited-scope testing. Pick the single app or API your auditor, biggest customer, or internal security review cares about. Give the tester credentials. Let them spend their time going deep instead of spreading wide.
The second is sprint-based pentesting. This works well when your team releases often. Test one feature set or one application area in a short engagement, fix issues, then retest in the next cycle. It’s practical and doesn’t force you into giant annual projects that age badly the moment code changes.
Manual pentesting doesn’t have to be huge. It has to be focused.
What fast, affordable manual pentesting should include
Look for a workflow like this:
- Targeted recon: The tester maps the attack surface and identifies likely weak points fast.
- Guided scanning: Tools support the work, but they don’t replace judgment.
- Manual exploitation: The tester validates findings and looks for chained attack paths.
- Usable reporting: Developers get clear reproduction steps and remediation advice.
- Retest support: Fixes get checked so the final report holds up in front of an auditor.
One option in this category is affordable manual pentesting, which describes a model built around focused, budget-conscious manual assessments rather than oversized enterprise engagements.
The standard you should demand
Ask for named certifications. Ask whether the people testing are the same people writing the report. Ask how they handle business logic flaws, authentication, access control, and remediation validation.
If the answer sounds like “our platform covers that,” you’re not buying a real penetration test. You’re buying software plus sales language.
Connecting Your Pen Test to Compliance Needs
Most buyers aren’t shopping for penetration testing because they woke up excited about attack simulation. They need evidence. An auditor asked for it, a customer questionnaire requires it, or a compliance program can’t move forward without it.
That changes how you should buy the test. A good pen test for compliance isn’t just technically sound. It’s also documented in a way an auditor can follow without dragging your team into three extra meetings.

What auditors usually want to see
Auditors usually care about a short list of basics. What was tested. When it was tested. Who performed it. What methodology was used. What was found. What got fixed.
If your report doesn’t answer those clearly, it creates friction. Your security team may understand the details, but your auditor wants a clean trail from scope to findings to remediation.
Match the test to the framework
For SOC 2, the pentest usually supports your broader security control story. It shows that you validate the security of systems in scope and that you respond to findings.
For PCI DSS, the focus is tighter. The test needs to align with systems and applications tied to the cardholder data environment or the controls protecting it.
For HIPAA and ISO 27001, the value is similar. You’re showing that the organization identifies weaknesses in relevant systems and takes remediation seriously.
What matters most is that the report maps cleanly to the environment you say is in scope. If your compliance boundary includes a patient portal or payment workflow, that asset should not be missing from the penetration test.
Ask for audit-ready reporting
The best low-cost penetration testing providers understand that the report is part security document, part audit artifact. That means it should include:
- Scope summary: Apps, APIs, network segments, and user roles tested
- Testing dates: Clear engagement window
- Methodology summary: Human-readable explanation, not just a tool list
- Risk-ranked findings: Organized so remediation can be prioritized
- Evidence: Enough detail to validate the issue without turning the report into a puzzle
- Retest notes: Clear status after fixes, when applicable
Your auditor doesn’t want a giant theory document. They want proof that the right systems were tested and the results were handled.
Keep the language simple inside the report
This part gets ignored too often. If your developers can’t understand the findings, remediation drags. If your compliance lead can’t summarize the report, audits drag.
Push vendors to write clearly. “Improper authorization lets a standard user access another customer’s records” is useful. Dense jargon with no business context is not.
If SOC 2 is your immediate problem, this guide on SOC 2 penetration testing gives a practical view of how to align the test to the audit requirement without making the engagement bigger than it needs to be.
Don’t buy findings your auditor can’t use
A report full of low-value scanner output might look busy, but it won’t help much in a compliance review. You want evidence tied to meaningful risk, clear scope, and remediation follow-through.
That’s the difference between buying a test for security theater and buying one that helps the business move.
Your Checklist for Picking a Pentest Vendor
Most low-cost penetration testing failures happen before testing even starts. The buyer picks the wrong vendor, usually because the proposal looked polished or the price looked easy to approve.
A cheap quote is not the problem by itself. The problem is buying from a vendor that can’t prove quality.
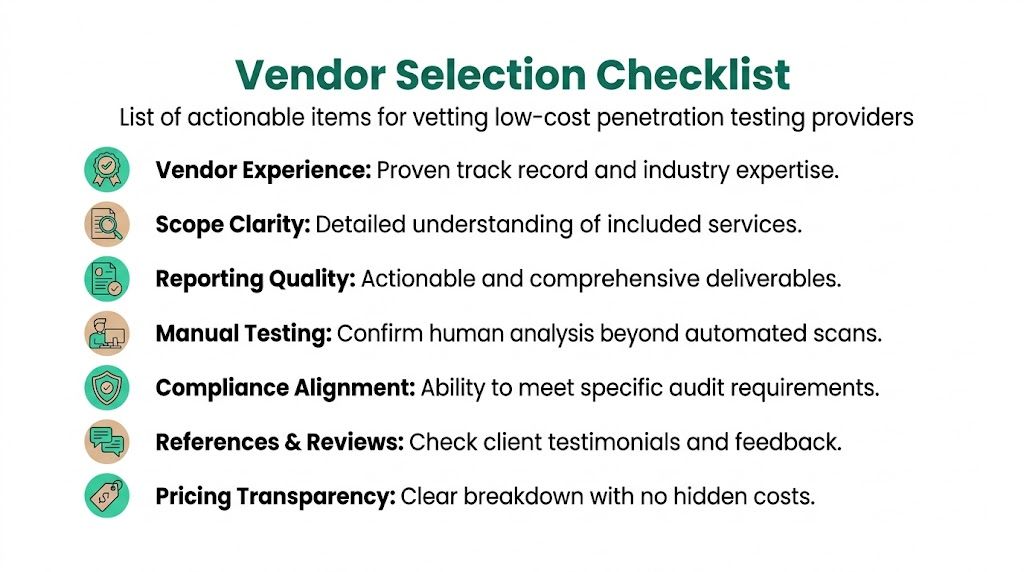
Start with proof of human expertise
A key challenge in low-cost penetration testing is evaluating quality. Cheap tests under $2,000 often skip manual validation and miss critical business-logic flaws. To assess ROI, IT leaders should demand proof of tester certifications like OSCP and review sample reports for depth, not just finding counts, as noted by Cyber Protection Group on low-cost penetration testing quality.
That’s the baseline. If a vendor can’t show who is doing the work and what qualifications they hold, stop there.
Questions every buyer should ask
Use these in your first call or email. They cut through marketing fast.
- Who will perform the test: Are they full-time staff or rotating contractors?
- What certifications do they hold: OSCP, CEH, CREST, or similar?
- How much of the work is manual: Not “supported by automation,” but actual human validation and exploitation.
- Can you share a sample report: You’re checking clarity, evidence, and remediation guidance.
- How fast is report delivery: You need dates, not vague promises.
- Do you offer retesting: If fixes land quickly, the vendor should have a path to validate them.
What a good sample report looks like
You don’t need to be a security consultant to review a sample report. Check for plain things.
Does it explain impact in simple language?
Does it show how the finding was verified?
Does it tell your developers what to fix?
Does it separate important issues from noise?
If the report reads like raw tool output pasted into a template, move on.
Ask for one redacted report before you sign anything. If they refuse, assume the deliverable is weak.
Red flags that usually mean trouble
Some warnings are obvious. Others are subtle.
- Too much platform talk: They keep demoing dashboards instead of describing test methodology.
- No tester visibility: Sales won’t say who performs the work.
- Vague scope language: Phrases like “best effort review” or “standard package coverage” without specifics.
- No compliance discussion: They don’t ask what framework or auditor requirement you’re trying to satisfy.
- Instant fixed quote without questions: Fast quoting is fine. Blind quoting is not.
- Report delays built into the process: If the report takes forever, the engagement won’t help much.
A simple vendor comparison format
Send every vendor the same short request. That forces apples-to-apples answers.
Asset in scope
Name the app, API, or external target.Test objective
State whether this is for SOC 2, PCI DSS, HIPAA, ISO 27001, customer due diligence, or internal validation.Access provided
Say whether it’s black box, gray box, or authenticated user testing.Required deliverables
Ask for an executive summary, technical findings, remediation guidance, and retest confirmation if needed.Timeline requirement
State that you need the report within a week if that’s your deadline.
Buy clarity, not theater
The right vendor should explain the engagement so clearly that a founder, IT manager, and compliance lead all understand it. If only the sales engineer can decode the proposal, that’s a problem.
Good vendors make the buying process simpler. Bad vendors make it sound mysterious so you won’t question the invoice.
Cost-Saving Pitfalls That End Up Costing More
The fastest way to waste money on a pen test is to buy the cheapest thing that sounds close enough. That usually means an automated scan sold as penetration testing, a report nobody can use, or a scope so sloppy that you have to pay for another engagement right away.
Many startups encounter this pitfall. They’re trying to save money, but they end up buying the same service twice.

The fake bargain test
Tests under $4,000 typically use only automated scanning tools and miss complex vulnerabilities. The long-term cost can be severe because IBM’s 2024 reporting estimates the average data breach cost at $4.88 million, as explained in Deepstrike’s review of penetration testing cost.
That's the ultimate calculation. Saving a little up front doesn’t help if the test misses the issue that later causes the incident.
The report that fails twice
A bad report creates two separate costs. First, your developers can’t use it because the findings are vague, duplicated, or unsupported. Second, your auditor or customer rejects it because it doesn’t clearly show scope, methodology, and remediation.
Then you pay again. Either the same vendor charges for retesting and cleanup, or a new vendor has to redo the whole thing.
The scope that got lazy
Another common mistake is asking for a broad engagement when the actual need is narrow. A company needs one internet-facing app tested for compliance, but the proposal expands into side systems, internal assets, and wish-list targets.
That sounds thorough. It usually just drains budget and slows delivery.
A clean, focused penetration test of the right asset is better than a sprawling test that gives every target shallow coverage.
The no-retest problem
Some buyers stop at the first report. That’s shortsighted.
If your team fixes the issues but never gets validation, you still have a gap. Internally, nobody knows whether the remediation worked. Externally, your auditor may ask for confirmation that the findings were addressed.
The certification blind spot
Plenty of vendors say they do manual testing. Fewer will show who does it and what qualifications those people hold.
If you don’t ask about OSCP, CEH, CREST, and actual tester experience, you leave quality to chance. That’s not frugal. That’s reckless procurement.
A low price is fine. A low standard is expensive.
The compliance mismatch
Sometimes the pen test is technically valid but operationally useless. The vendor tested the wrong target, wrote the wrong style of report, or ignored the compliance context completely.
That happens when buyers focus only on price. If the result doesn’t support the audit, it failed its main job.
The safer way to save money
If you want to control spend without getting burned, do the boring things well:
- Reduce scope intelligently: Test the app, API, or external environment tied to actual risk or compliance.
- Insist on manual validation: Especially for web apps and APIs.
- Review a sample report first: Don’t buy blind.
- Confirm turnaround in writing: If timing matters, make it contractual.
- Plan for remediation and retest: The first report is not the end of the process.
That’s how you keep low-cost penetration testing low cost in reality, not just on the invoice.
If you need a fast, affordable pen test that’s built for SOC 2, PCI DSS, HIPAA, or a practical security review, Affordable Pentesting is one option to consider. Use the contact form to share your scope, deadline, and compliance goal, and ask for a focused engagement that gives you a real report within a week instead of another slow, overpriced sales cycle.
.svg)
