Picture your offense and defense practicing together and sharing notes to plug gaps before a big game. That's purple teaming. It's not a new team but a smart strategy where attackers (red team) and defenders (blue team) work together.
Instead of working separately, they share information instantly. This makes your defenses stronger and your response time much faster.
Understanding Purple Teaming and Why It Matters

If you're a CISO, IT manager, or founder, you're likely tired of old-school security assessments. The slow timelines, high prices, and confusing reports with no real findings don't work. This is where a purple teaming mindset changes everything.
A traditional penetration test is like hiring someone to find cracks in your walls and getting a report weeks later. Purple teaming is like having that person show your guards exactly how they broke in, so the guards can fix it on the spot. This creates a powerful and immediate feedback loop.
How Purple Teaming Maximizes Your Security Budget
Too many companies spend a fortune on security tools that are poorly configured or don't stop real attacks. Purple teaming tests if your tools actually work as intended. It's a fast, affordable way to prove your security controls are effective.
For businesses needing to meet compliance like SOC 2, HIPAA, or PCI DSS, this model is incredibly efficient. It validates your controls in real time, so you get actionable feedback immediately instead of waiting weeks for a pen test report. This means you fix issues faster and get more value from your security spending.
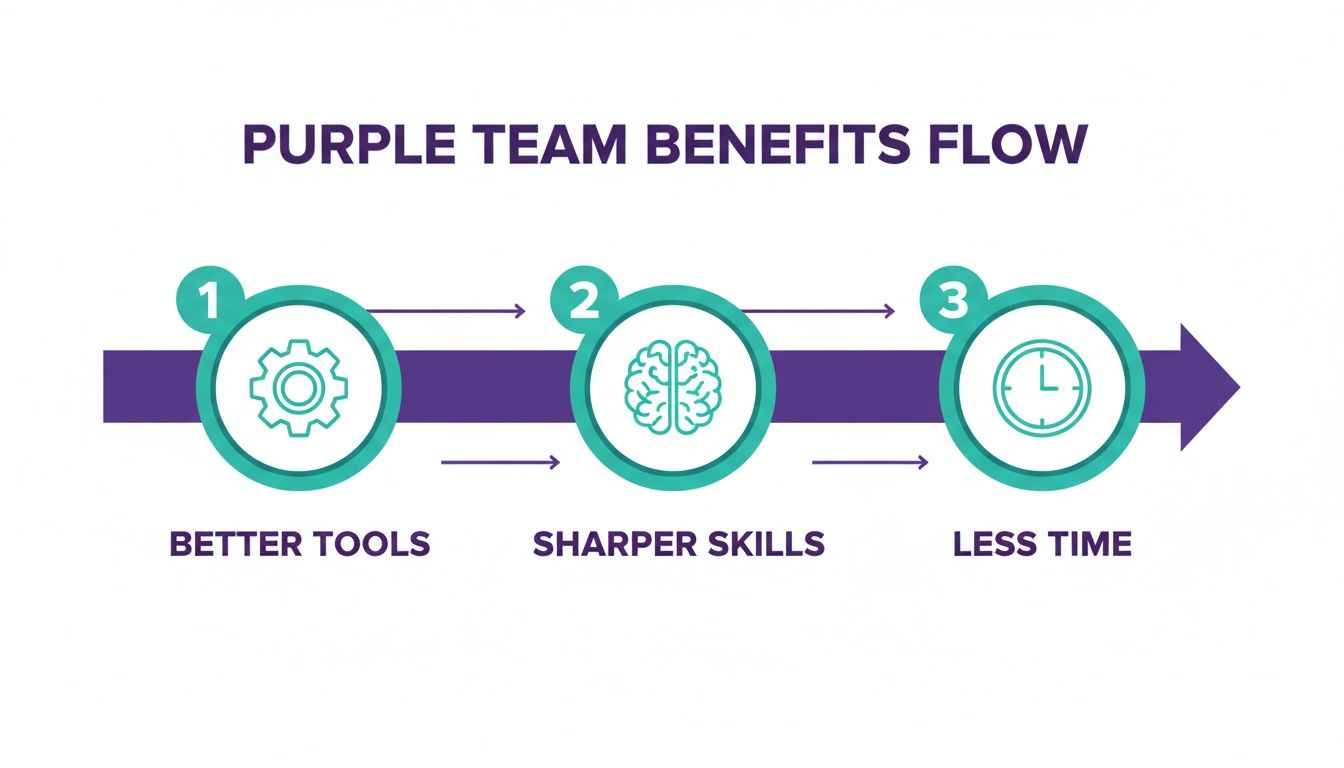
Key Benefits of a Purple Team Strategy
Adopting a purple teaming strategy delivers immediate wins. Forget waiting weeks for a traditional penetration test report. This approach gives you feedback now, helping you fix security gaps in hours, not weeks.
This speed shrinks your window of risk almost overnight. For CISOs and IT managers, it means you stop overpaying for slow, outdated security assessments. You get clear proof of improvement that satisfies both leadership and auditors without blowing your budget.
Sharpen Your Team's Defensive Skills Fast
A purple team exercise is one of the best training investments you can make. It drops theory and puts your team in hands-on scenarios against real attack techniques. When your defenders see exactly how an attacker breaks in, they gain priceless knowledge.
Our pentesters hold top certifications like OSCP, CEH, and CREST. They don't just find flaws; they teach your team to think like an attacker. This knowledge transfer is a core benefit, making your staff better at threat hunting and incident response.
Get Faster Fixes and Actionable Reports
The biggest frustration with old-school penetration testing is the waiting. You do the test, then wait weeks for a long, confusing report. With purple teaming, the feedback is instant, and the results are clear.
This process turns security from a slow chore into a continuous improvement machine. Instead of a static report that's outdated as soon as you get it, you get a dynamic, ongoing boost to your defenses. This covers digital threats and even physical security, where practices like hard drive shredding as a best defense against data breaches are critical.
How to Structure a Purple Team Exercise
You don’t need a huge budget or a massive security team to run a purple team exercise. The process is simple and creates a feedback loop for fast, measurable results. It's built for speed, delivering actionable insights in real time, unlike a traditional pen test.
The goal is to turn your security spend into an active defense. Let's walk through the three simple phases of a successful exercise.
Phase 1: Planning and Defining Scope
First, you need a plan. This phase is about setting clear goals and rules before anyone starts. What are you trying to test? Maybe you want to see if your defenses can stop a ransomware strain or a specific phishing attack.
Once you have a goal, you pick the attack techniques. The MITRE ATT&CK framework is a great resource here, as it lists real-world attacker tactics. Finally, you set the rules of engagement, like the timeline and how everyone will communicate, to keep the exercise focused.
Phase 2: Collaborative Hands-On Execution
This is where the real work happens. The execution phase is a live, open session where your red and blue teams work together. This is a huge shift from a classic what red team testing is, where attackers work in secret.
Here’s how a typical cycle works. The red team announces an attack, launches it, and the blue team watches their tools. If the attack gets through, everyone stops to figure out why, fix the gap, and then re-run the test to confirm the fix works. This rapid loop provides instant proof that your defenses are getting stronger.
Phase 3: Analysis and Final Remediation
Once the live exercise is done, the final phase is about turning those quick wins into permanent improvements. Both teams get together to review what happened, analyze the results, and build a concrete action plan.
The final report shouldn't be a 100-page book. It should be a short summary of what was tested, what was missed, what got fixed, and what still needs attention. The output is a simple, prioritized list of action items your team can start working on immediately.
How to Measure Your Purple Teaming Success

How do you prove a purple team exercise was worth it? Forget complex spreadsheets. Success comes down to a few simple metrics that prove your security is actually getting better.
The point isn't just to get a list of vulnerabilities like in a standard pentest. The goal is to show your defenses are getting faster, smarter, and more effective. These numbers provide the hard evidence you need to justify your security budget.
Track Detection and Response Speed Metrics
When it comes to purple teaming, the most important metrics are about speed. How fast can you spot an attack, and how quickly can you shut it down? These two numbers show your team’s real-world readiness.
Mean Time to Detect (MTTD) is how long it takes to realize a threat is active. Mean Time to Respond (MTTR) is how long it takes to contain it. Watching these two metrics drop is the ultimate goal, proving the collaboration is working.
Measure Your Overall Detection Coverage
Speed is key, but you also need to know how much you can actually see. The MITRE ATT&CK framework helps you map known attacker tactics to test against. You can systematically test your defenses against specific, real-world attacks.
After each purple team session, you update your coverage map. The goal is to turn more of that map from a blind spot into a confirmed detection. For example, your detection coverage for certain attacks might jump from 15% to 45% after a few sessions, showing a clear, quantifiable improvement.
Quantify Your Security Gaps and Fixes
Finally, a simple way to measure success is to count the number of security gaps you find and, more importantly, the number you close. This isn't just about patching a vulnerability; it's about improving your detection rules and response playbooks.
Every purple team exercise should produce a clear list of action items. Tracking these from identification to resolution gives you a perfect audit trail of continuous improvement. This builds a rock-solid foundation for your entire security incident response planning.
Purple Teaming for Startups and Compliance
For compliance officers and startup founders, purple teaming is the most direct way to prove your security works. It provides the evidence you need to satisfy auditors for standards like SOC 2, PCI DSS, and HIPAA, which all require regular security testing.
This approach is perfect for startups and small businesses because it's efficient and affordable. Forget the slow, expensive pen test. With purple teaming, you can run focused exercises on the threats that matter most and get answers right away.
Making Your Compliance Audits Much Easier
Meeting compliance often feels like scrambling for evidence. Purple teaming builds the audit trail for you. When your teams work together, every test creates a detailed log of what happened.
Did your tools catch the simulated ransomware? Your exercise notes and system logs become undeniable proof for your SOC 2 audit. This active validation is what auditors really look for, showing a mature approach to security even if you're a small team.
Cost-Effective Security for Savvy Startups
As a startup, every dollar counts. Purple teaming is an affordable alternative to traditional security tests that have high prices and slow turnaround times. You get the benefits of a pen test without the bloated cost.
You don't need a huge, dedicated team. A startup can use its existing IT staff as the blue team and bring in affordable, certified pentesters for the offensive side. This gives you access to expert attackers with certifications like OSCP, CEH, and CREST without the huge overhead. For more tips, check out our guide on cyber security for startups.
Frequently Asked Questions About Purple Teaming
As a CISO, IT manager, or founder, you need practical answers. Let's get straight to the questions we hear all the time about how purple teaming works in the real world. Here are the direct, no-nonsense answers.
How Big Does My Purple Team Need to Be?
You can start with the people you already have. A "purple team" isn't a new department. Your existing IT staff can be the blue team, and an affordable pentest service can provide the red team. One person from each side is all it takes to start.
What Tools Are Absolutely Necessary to Start?
You don’t need to spend a fortune. The goal is to get better with the tools you already own. At a minimum, you need a way to launch attacks, like a VM with Kali Linux, and a way to see what happens, like a free SIEM like Splunk or the Elastic Stack.
You can even use free tools like Sysmon for endpoint monitoring. The goal isn't buying more tools. It's about tuning the ones you have to catch real threats. Our pentesters are experts at helping you do exactly that.
How Does This Compare to a Standard Pentest?
A standard penetration test is a secret inspection where you get a report weeks later. A purple team exercise is a live, collaborative training session. The attacker shows the defender exactly how they are bypassing defenses so the gap can be fixed on the spot.
The feedback loop is incredibly tight. You're not just getting a list of problems; you're actively sharpening your team's skills and your tools' effectiveness in real time. It’s about continuous improvement, not just a yearly check-up.
Is Purple Teaming Too Expensive for a Startup?
Absolutely not. In fact, purple teaming is one of the most cost-effective security investments a startup can make. Traditional penetration testing is slow and expensive, with reports often taking a month or more to arrive.
With a purple team approach, you get real, actionable results in a week, not a month. By using our affordable pentest services, you get access to OSCP and CEH certified experts without the bloated enterprise price tag, making it a perfect fit for a tight budget.
Can We Run Purple Team Exercises Remotely?
Yes, and it’s incredibly effective. Today, almost all purple team exercises are done remotely over video calls and screen sharing. The attacker shares their screen to walk through an attack, and the defender shares their screen to show what they see in their tools. It's a fantastic way to collaborate and eliminates travel costs.
How Long Does a Typical Exercise Take?
The beauty of purple teaming is its flexibility. An exercise can be a focused half-day workshop or a multi-day engagement, depending on your goals. Unlike a long, drawn-out penetration test, you control the timeline and focus to ensure you get maximum value for your time.
Ready to see how a fast, affordable, and collaborative approach can transform your security? At Affordable Pentesting, we deliver high-quality pentests with actionable reports in under a week. Our certified experts are ready to help you strengthen your defenses and meet your compliance needs. Contact us through our form to get started.
.svg)
