Imagine your attackers find a critical flaw, but your defenders don't hear about it until a massive report lands on their desk weeks later. This old model is broken. A purple teaming exercise fixes this by getting your attack and defense teams working together, in real-time.
It's a collaborative security drill. Your red team (the attackers) and blue team (the defenders) are in the same room, working to make your defenses stronger, not just to see who wins.
What a Purple Teaming Exercise Is
Think of a traditional pentest as a one-sided game. The red team attacks in secret, and the blue team tries to defend without knowing what’s coming. The two sides rarely communicate, and you're left waiting for a report to connect the dots. A purple teaming exercise flips that on its head.
It’s more of a live, hands-on training workshop. Our red team announces their move: "I'm now attempting a credential dumping attack using Mimikatz." They execute it, and everyone immediately huddles to check the results.
Did your security tools fire an alert? If not, the teams figure out why right then and there. They can tune detection rules, adjust configurations, and validate the fix on the spot. This isn't just about finding flaws; it's about measurably improving your ability to stop them, fast.
Purple Teaming vs Traditional Pentesting
A penetration test tells you if you're vulnerable. A purple team exercise teaches your team how to get better at detecting and stopping attacks. It turns a simple assessment into a skill-building workshop centered on peer-to-peer learning.
This is critical for companies navigating compliance audits like SOC 2, PCI DSS, or HIPAA. A purple teaming exercise generates concrete proof that you are actively testing, validating, and improving your security controls. Auditors love to see this proactive approach because it shows a mature security program.
Our approach makes this process fast and affordable. We bring in certified OSCP, CEH, and CREST pentesters to act as your expert red team, guiding your internal blue team through realistic attacks. You get the value of a high-end collaborative exercise without the high price, with a full report in your hands within a week.
Planning Your First Purple Teaming Exercise
A successful purple team exercise comes down to smart planning. This isn't your typical, month-long penetration test where the goal is just to break things. This is a focused, collaborative training session designed to give your security an immediate and measurable boost.
It starts by deciding what you want to achieve. Are you worried about phishing attacks? Or maybe you want to validate that new security tool you just spent a fortune on? Getting specific keeps the exercise from becoming a massive, costly project.
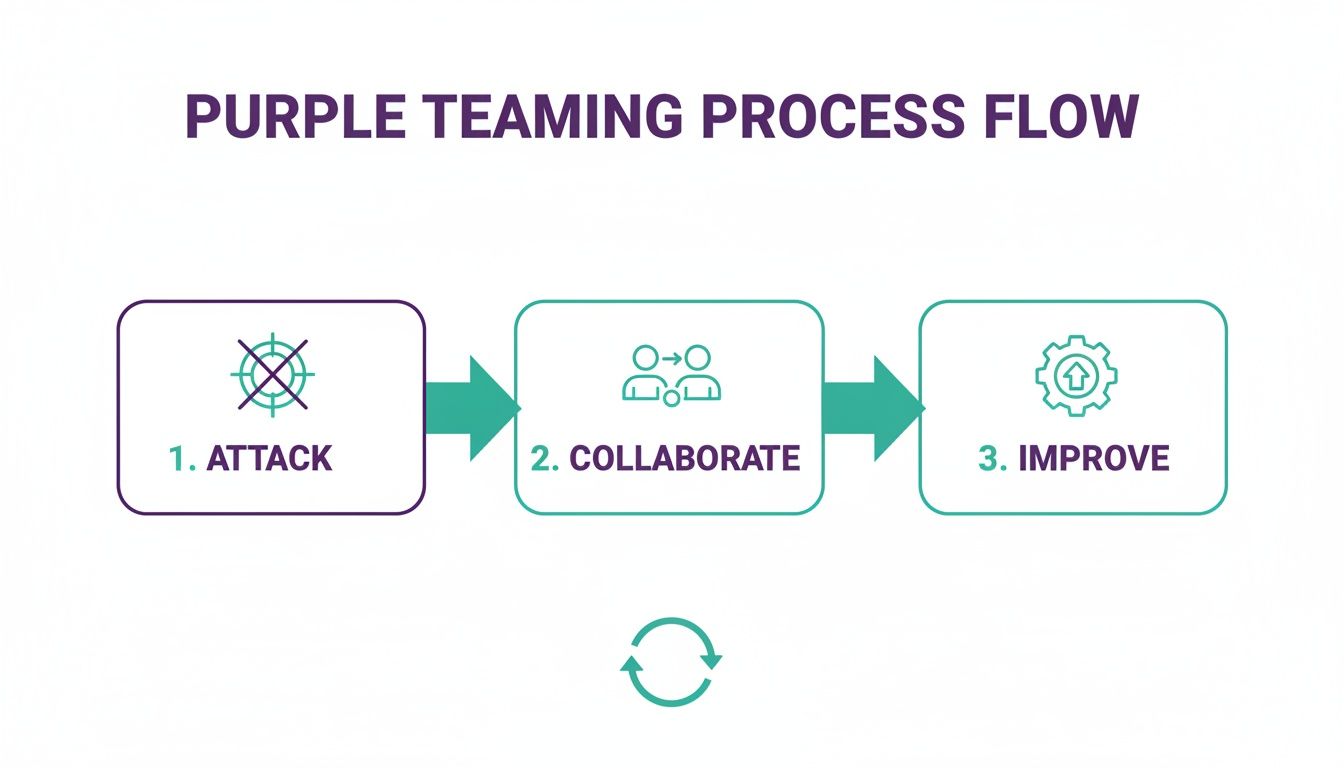
Think of it less as a one-off event and more as continuous training. Each exercise sharpens your team’s skills and hardens your security. This simple loop is the core of purple teaming.
Define Your Exercise Scope and Objectives
First, what are your goals? A clear objective defines the scope and keeps costs under control. A great objective is, "Test our ability to detect credential dumping techniques." It's specific, measurable, and maps to a real-world threat.
Stay away from vague goals like "test our security." That’s too broad. Think about what keeps you up at night. Is it ransomware? Data theft? Pick one or two key areas to build the exercise around. This focus is what makes a purple team exercise so much more affordable and faster than a full-blown pentest.
By narrowing your focus, you ensure every minute is productive. It also makes it easier to measure success and show clear improvement, which is exactly what compliance auditors for SOC 2, HIPAA, and PCI DSS love to see. For more tips, see our guide on how to prepare for your penetration test.
Assemble Your Purple Team Members
Next, you need your team. A purple team isn't a formal department; it's a temporary group for the exercise. You'll need people for three key roles.
- Red Team (Attackers): These are the offensive pros who simulate attacks. Most businesses don't have an in-house red team. That’s where our certified pentesters (OSCP, CEH, CREST) provide expert attack simulation without the enterprise price tag.
- Blue Team (Defenders): This is your internal security crew. They manage your security tools and respond to incidents. They are the most important part of the exercise, as they are the ones who will learn and improve.
- Observer (Coordinator): This person is the referee. They document every action, observation, and outcome. Their notes become the foundation for the final report you'll get from us within a week.
Don’t underestimate the observer. This role is critical for keeping the exercise on track and ensuring all valuable insights are captured for the report and remediation plan.
Establish the Rules of Engagement
Finally, you need to set the rules. The "rules of engagement" is a simple document that defines the boundaries for the exercise so there are no surprises. It states what’s in scope and what’s out of scope. For example, are we testing production systems or a staging environment?
The rules also define the communication plan. How will the red team announce their actions? Who is the point of contact if something unexpected happens? Getting this sorted out beforehand ensures the exercise runs smoothly and safely. This simple step turns a potentially chaotic security test into a structured, productive training event.
Selecting the Right Attack Scenarios
Choosing what attacks to simulate is where a purple team exercise either succeeds or fails. If you just guess what hackers might do, you're wasting time and money. A sloppy approach gets you sloppy results.
What you need is a focused strategy that gives you real, actionable findings. This is what improves your security and satisfies auditors for SOC 2, HIPAA, and PCI DSS.
Use MITRE ATT&CK as Your Guide
Don't invent attack scenarios. The industry has already done the heavy lifting for you with the MITRE ATT&CK framework. Think of it as a free encyclopedia of hacker techniques seen in the wild. It’s logically organized, following the path of a real attack from initial access to data theft.
The point isn't to test everything—that's impossible and would cost a fortune. You use the framework to pick a handful of techniques that are a genuine threat to your business. This targeted method is why purple teaming is so much more affordable and efficient than a traditional penetration test.
Focus on What Matters to Your Business
Every business has different risks. A healthcare provider worries about ransomware and patient data theft. A fintech startup is focused on stopping fraudulent transactions. Your attack scenarios have to reflect what keeps you up at night.
Ask yourself these questions to narrow things down:
- What are our crown jewels? Is it customer data, proprietary code, or financial records?
- What compliance rules do we follow? SOC 2, PCI, and HIPAA have different testing expectations.
- What did our last pen test find? Re-testing old vulnerabilities is a great way to prove your fixes worked.
- What attacks are happening in our industry? Threat intelligence reports tell you what hackers are using against companies like yours right now.
Answering these helps you cut through the noise and create a short, high-impact list of techniques to test. That's how you get a fast, affordable, and incredibly relevant purple teaming exercise. You can adjust the scope to fit any budget, making it perfect for businesses that need real security validation without an enterprise-sized price tag.
Create Practical and Measurable Scenarios
Once you have your techniques, turn them into simple, concrete scenarios. A good scenario is a short story the red team will act out. For instance, instead of just saying "test phishing," get specific.
Scenario Example: Phishing to Credential Theft
- Attack: The red team sends a spear-phishing email with a link to a fake login page.
- Collaborate: The user clicks the link and enters their credentials.
- Improve: Did your email filter block it? Did your web filter stop them? Did MFA prevent the login?
This simple approach makes the whole penetration testing process easy to follow. It turns an abstract technique into a real-world test with obvious results. Our OSCP and CEH-certified pentesters can help you build these scenarios, ensuring your pen testing is both realistic and affordable, with a full report delivered in under a week.
Executing the Exercise and Gathering Insights
This is where the real work gets done. A purple team exercise isn't a typical, behind-the-scenes pentest. It’s a live, collaborative workshop where your defenses get stronger with every move we make.

We start with everyone in the room. Our red team, staffed by certified OSCP and CEH pentesters, doesn't operate in the shadows. They’re completely transparent, announcing exactly what they’re about to do.
The Attack and Collaborate Loop
The entire exercise runs on a simple rhythm: attack, pause, discuss, and improve. The red team will state their intention loud and clear. For example, "We are now attempting to escalate privileges using a known kernel exploit." They run the attack, and then everyone hits pause.
Right then, the blue team jumps into their tools. Did the SIEM fire an alert? Did the EDR block the attempt? This instant feedback loop is what makes purple teaming so different from a traditional pen test.
If there’s a detection, it’s a win. We analyze the alert together to make sure it’s useful. If nothing happens, that’s not a failure—it’s an opportunity. The whole group digs in to find out why the attack was missed.
- Is it a tool configuration issue? A detection rule might be off or misconfigured.
- Is there a process gap? Maybe an alert fired, but no one was assigned to investigate it.
- Is it a visibility problem? The tool might not be collecting the right logs.
This on-the-spot troubleshooting ends the finger-pointing that can plague security teams. The goal isn't blame; it's to fix the gap immediately. This hands-on, real-time tuning delivers measurable improvements to your security before the exercise is even over.
Documenting Every Action and Insight
While the teams are in the technical weeds, the observer is documenting everything. This person captures the play-by-play of the exercise.
They meticulously record every single step:
- The specific technique the red team used.
- The exact time the attack was simulated.
- The blue team’s findings (or lack thereof).
- The root cause of any missed detections.
- The immediate fixes or tuning adjustments made.
This detailed log is the backbone of your final report. Traditional pentest reports can take a month or more to show up. Our process is built for speed. Because we capture everything in real-time, we can deliver a clear, actionable report to you within one week.
This fast turnaround is critical for busy IT managers and CISOs who need to show progress to stakeholders and auditors for regulations like SOC 2 and PCI DSS.
Analyzing Results and Driving Remediation

The exercise is over. Now what? A purple team engagement is only as good as the action you take afterward. Unlike a traditional pentest that makes you wait weeks, our process is built for speed. The observer’s notes are immediately translated into a straightforward, actionable report that lands in your hands within a week.
We write these reports to be understood, not to collect dust on a shelf. Your IT managers, CISO, and even your non-technical founders will see the risks and priorities clearly. The goal is to get you from observation to action fast.
Building Your Remediation Roadmap
With that clear report, it's time to build a practical roadmap for improvement. This isn't about fixing everything overnight. It's about smart, risk-based prioritization.
We help you sort findings into two buckets: quick wins and longer-term projects. A simple firewall rule change or an urgent patch are low-effort, high-impact fixes you can do immediately. Other things, like deploying a new security tool, will require more planning.
This structured approach makes sure you’re tackling the biggest risks first. To learn more, check out our guide on the best practices for the remediation of vulnerabilities. It’s what makes the entire testing cycle efficient and worthwhile.
Proving Compliance and Driving Improvement
This documented cycle—test, find, fix—is exactly what auditors want to see. For compliance frameworks like SOC 2, PCI DSS, and HIPAA, owning security tools isn't enough. You have to prove you’re actively managing your security posture, and a purple team exercise delivers undeniable evidence of that.
Your report from a purple teaming exercise is more than a list of findings. It's a documented story of improvement that proves to auditors, stakeholders, and customers that you take security seriously. The remediation plan becomes your living guide, steering your security efforts until the next exercise.
Tools and Platforms for Purple Teaming
Let's be clear: a collaborative mindset is what makes a purple team exercise work. But the right tools can make a huge difference. You absolutely do not need to spend a fortune on enterprise platforms to get this done. Many affordable and even open-source options are perfect for startups and SMBs watching their budgets.
The goal isn't to buy software; it's to find tools that make attack simulation and team collaboration easier. For an IT Manager or CISO, a few smart investments here are far more cost-effective than calling in external teams for every single pen test. It builds up your in-house security muscle over time.
Attack Simulation and Orchestration Tools
To run a convincing exercise, your red team needs a way to simulate attacker techniques. These tools are what you use to automate and manage the offensive side of the engagement, making sure every attack is consistent, measurable, and safe.
Many of these platforms are surprisingly intuitive. They often come with a library of pre-built attack scenarios that map directly to frameworks like MITRE ATT&CK. That saves a massive amount of time. For more on the tools our pentesters use, check out our guide on penetration testing tools.
Here are a few types of tools that are great for this:
- Breach and Attack Simulation (BAS) Platforms: These tools automate threat simulation. They can run continuous, safe attacks to see what your blue team catches.
- Adversary Emulation Tools: Often open-source, these let you precisely replicate the techniques of known threat actor groups.
- Command and Control (C2) Frameworks: These are the real tools attackers use. Using them in a controlled exercise gives your defenders the most realistic test possible.
Collaboration and Documentation Platforms
A purple team exercise throws off a ton of data—fast. You need a simple way to capture every attack, every observation, and every outcome as it happens. A shared spreadsheet can work, but dedicated platforms make this process much cleaner.
These platforms act as a central dashboard for the whole exercise. The red team can log their actions, and the blue team can document their findings right alongside them. This creates a clean record of the engagement, which makes generating the final report incredibly fast. It’s a key part of how we deliver a detailed report to you within a week.
The right platform isn't about replacing people; it's about making them more effective. A good tool unifies the red and blue teams, providing a single source of truth that turns chaotic findings into a clear, actionable remediation plan. We can help you navigate these choices. Get in touch to discuss what makes sense for your organization.
Purple Teaming Exercise FAQ
Got questions about purple teaming? You’re not alone. We get a lot of them from IT managers, CISOs, and startup founders who are tired of slow, expensive penetration testing.
Here are straight answers to the most common ones.
Isn't This Just a Normal Penetration Test?
Not even close. A standard penetration test is a "gotcha" exercise. An attacker tries to break in, and you get a report card at the end. It's pass/fail.
A purple teaming exercise is a live-fire training session. Our attackers and your defenders work together openly. We announce an attack, execute it, and then huddle up to see if the defenses worked. It's a collaborative workshop, not a covert mission.
What’s a Purple Teaming Exercise Going to Cost Me?
The cost is entirely up to you. Instead of a massive, month-long engagement that tests everything, you control the budget by defining the scope. This is the biggest difference from old-school pentesting firms.
We can focus on just a few high-risk attack scenarios that are most relevant to your business and compliance needs (like SOC 2 or HIPAA). This targeted approach delivers huge value without the eye-watering price tag. For a clear, no-nonsense quote, fill out our contact form.
We Don't Have a Red Team. Can We Still Do This?
Of course. Most small and mid-sized companies don't have dedicated offensive security pros on staff. That's exactly why we're here.
Our certified penetration testers (OSCP, CEH, CREST) become your expert red team for the exercise. They simulate the real-world attacks that matter, giving your internal team the hands-on experience they need to level up their skills. You get all the benefits without the cost of hiring a full-time red teamer.
How Long Until We See Results?
You see results instantly. That’s the whole point.
During the exercise, your team gets real-time feedback on every single attack we run. There's no waiting a month for a confusing report. We deliver a clear, actionable summary with prioritized recommendations within a week. You can start plugging gaps and improving your security posture right away.
.svg)
