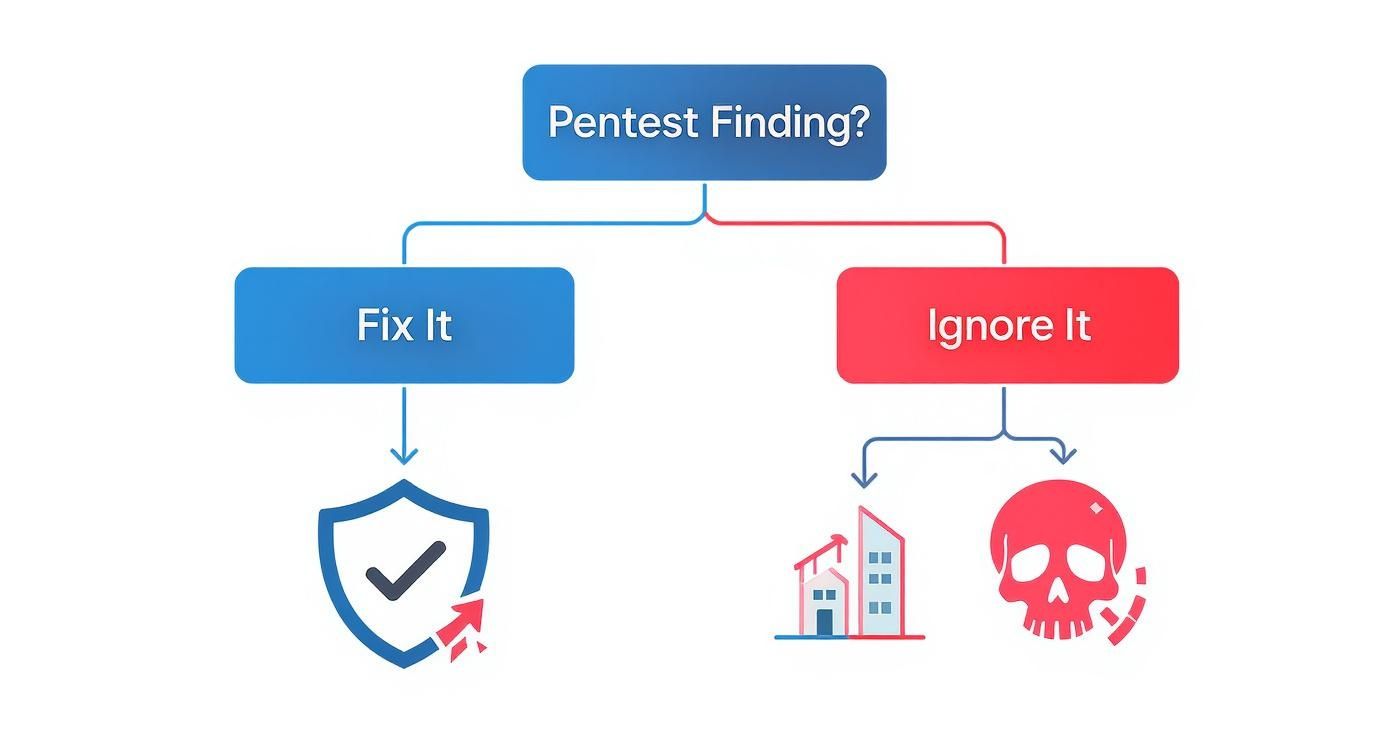
Getting your pentest report isn't the finish line—it's the starting gun. Real security comes from fixing the vulnerabilities our certified pentesters find in your systems. Ignoring these findings is like knowing your boat has a leak but setting sail anyway.
Understand Pentest Reports Are Business Health Checks
Your penetration testing report is more than a technical checklist. The real value comes from fixing the security holes our experts uncover, which directly protects your company's money and reputation.
Each finding in our report is a potential open door for an attacker. A single unpatched weakness isn't just a tech problem. It's a business risk that can lead to expensive data breaches and destroy the trust you've built with customers.
Turn Our Report Findings Into Actionable Fixes
Our job is to give you a clear, affordable, and fast security assessment. Our OSCP, CEH, and CREST certified pentesters find weaknesses before criminals do. These findings become a simple roadmap your IT team uses to fix what's broken.
Ignoring these issues is not an option. A small problem, like a misconfigured server, can quickly become a major incident. The cost to fix the issue now is always cheaper than cleaning up after a data breach.
See How Compliance and Remediation Go Hand-in-Hand
Fixing vulnerabilities isn't just good practice; it's often required for compliance. Standards like SOC 2, HIPAA, and PCI DSS demand that you find and fix security weaknesses to avoid big fines.
Proactively fixing the findings from our pentest reports is a smart investment. It protects your revenue, keeps customers happy, and ensures you meet legal duties. We provide the affordable pentesting you need to find the risks so you can focus on fixing them.
Prioritize Fixes From Your Pentest Report Fast
Getting your pentest report in under a week is great, but a long list of findings can be overwhelming. The secret is you don't have to fix everything at once. You just need to tackle the biggest risks first.
Prioritizing is about combining our technical ratings with your business knowledge. For each finding our pentesters provide, ask two simple questions: How easy is this for an attacker to use, and what's the worst that could happen if they did?
Look Beyond Just The Standard CVSS Score
The Common Vulnerability Scoring System (CVSS) gives a technical score from 0 to 10. But context is what truly matters. A high score on a system that’s hard to access might be less urgent than a medium score on your main website.
Our OSCP, CEH, and CREST certified experts provide this context in your report. We don’t just tell you what the vulnerability is; we explain what it means for your business. This helps you focus on what matters most.
Create A Simple Triage And Action Plan
To make this process easier, sort the findings from our pentest report into a few simple buckets. This helps your team know exactly where to start.
- Fix Now: Critical issues on your most important systems. Think of a bug on your login page. Your team needs to fix this immediately.
- Fix Soon: High or medium issues on less critical systems. These need to be fixed, but they can be scheduled for your next work cycle.
- Plan to Fix: Low-risk findings. Log these in your system and have your team address them when they have time.
A formal vulnerability management plan helps turn this list into assigned tasks. It ensures your team is always working on the most important things first, protecting your business without wasting time.
Follow Practical Steps For Patching And Configuration
You've got your pentest report and know what to fix first. Now it's time for your team to get to work. Most findings come down to two things: updating software or changing a setting.
Our reports, delivered within a week, give your team a clear checklist to get started right away. A software patch is like a free part from a carmaker to fix a defect. A configuration fix is like finally remembering to lock your car doors. Both stop a thief.

Apply Security Patches The Smart Way
Outdated software is the most common finding in our pentest reports. Hackers love it because exploits are easy to find online. Patching just means applying a vendor's update to close known security holes.
Our OSCP, CEH, and CREST certified pentesters will tell you exactly what software is vulnerable and which update to apply. The key step is to always test patches in a safe environment before deploying them live. This prevents accidental downtime.
Make Simple But Powerful Configuration Changes
Not every vulnerability is a complex code problem. Sometimes, the issue is just a bad setting. These misconfigurations are often the quickest wins for your team, giving you a big security boost with little effort.
Our pentest report will highlight these with simple instructions. For example, we might find weak password rules. The fix is to require stronger passwords and turn on multi-factor authentication (MFA), a huge security improvement.
Verify Your Fixes With Affordable Retesting
So, you’ve patched the server and tweaked the configurations. Are you done? Not yet. The most important part of remediation is proving the fix actually worked.
Assuming a vulnerability is gone without checking is a huge risk. You need confirmation. This is where retesting comes in, and it's a standard part of our affordable pentesting process. It's the only way to be sure the security gap is closed.
Get Independent Verification For Peace Of Mind
After your team applies the fixes from our report, you need an independent party to try to break in again. This isn't about mistrust; it's about good science. You have to test your work.
Our certified pentesters, the same experts who found the issue, will try the exact same attacks again. Their goal is to prove the attack now fails. This step turns an open risk into a closed issue and gives you proof for auditors.
Report Your Remediation Success To Leadership
Security isn't just an IT problem; it's a business issue. After your team fixes the vulnerabilities from our report, you have to show leadership the value of that effort.
It's about translating technical work into business terms, like risk reduction. Your pentest report is a list of business risks. Your remediation work is how you eliminate them. Reporting this success justifies your security budget and proves you are managing risk.

Translate Technical Wins Into Business Language
Your CEO doesn't need to know the details of a software flaw. They do need to know that a risk to customer data has been eliminated. You have to frame your report around business outcomes.
For example, instead of saying, "We patched the server," say, "We closed a security hole that could have led to a data breach." This simple shift connects your team's work directly to what leadership cares about: protecting the business.
Focus On Key Metrics To Show Progress
You don't need complex charts to prove your point. Focus on a few simple numbers that tell a clear story of progress. Track how long it takes to fix issues and how many critical vulnerabilities you close each quarter.
A simple graph showing the number of open critical risks going down over time is very powerful. Our fast, affordable pentesting gives you a clear baseline to measure against. You can review our pentest report template to see how we structure these findings.
Your Top Vulnerability Remediation Questions Answered
Even with a detailed pentest report, questions will come up. Here are the most common ones we get from clients after we deliver their report in under a week.
How Long Should Vulnerability Remediation Take?
There is no single answer, but a good rule is to fix the biggest risks first. We recommend fixing critical vulnerabilities within 15 to 30 days. The actual timeline depends on how complex the fix is.
A simple settings change might take a few hours. A complex software patch that needs a lot of testing could take a few weeks. Our reports explain the risk clearly so your team can set realistic deadlines.
What If There Is No Patch Available?
This happens with new "zero-day" vulnerabilities. When there's no official patch, the goal is to use other methods to make it much harder for an attacker to succeed.
These can include using a Web Application Firewall (WAF) to block bad traffic or restricting network access to the vulnerable system. Our reports from OSCP, CEH, and CREST certified pentesters will suggest these temporary fixes to protect you now.
How Do I Prove Vulnerabilities Are Fixed?
For audits, you need proof. The process is simple: document everything and get it verified. Keep a record of each finding from our report and when your team fixed it.
Most importantly, you need a retest. After your team applies the fixes, we re-run the original attacks to confirm they now fail. The updated report showing a "Closed" status is the independent proof auditors want to see.
Ready to get clear, actionable findings you can actually fix? At Affordable Pentesting, we deliver high-quality, manual pentests with reports in under a week, all at a price that makes sense. Get the expert insights you need to secure your business without the traditional cost and delays. Fill out our contact form to get started.
.svg)
