Managing SaaS security feels like a constant fight because it is. You're responsible for your company's data, but it lives inside apps you don't fully control. This shared responsibility model is exactly why SaaS creates everlasting security concerns for so many businesses.
Why SaaS Security Is A Constant Battle

If you're an IT manager, CISO, or founder, you know this feeling. Every new SaaS tool adds another potential door for attackers to walk through. You worry about misconfigurations, unapproved apps, and sensitive data going where it shouldn't. It feels like a problem that never goes away.
Research shows a staggering 75% of organizations had a SaaS security incident last year. Many of these issues come from simple mistakes or unauthorized apps. You can see more of the SaaS statistics and their impact. This isn't a rare problem; it's the daily reality of managing cloud tools.
The good news is you can solve this. The solution isn't another expensive, slow security firm that finds nothing. It’s an affordable manual pentest that gives you answers fast. A penetration test is simply where you hire certified ethical hackers to find weaknesses before the bad guys do.
Our OSCP, CEH, and CREST certified pentesters deliver your report within a week. This fast and affordable pen test process helps you validate your security and fix real issues without the usual headaches. To get started, get in touch via our contact form.
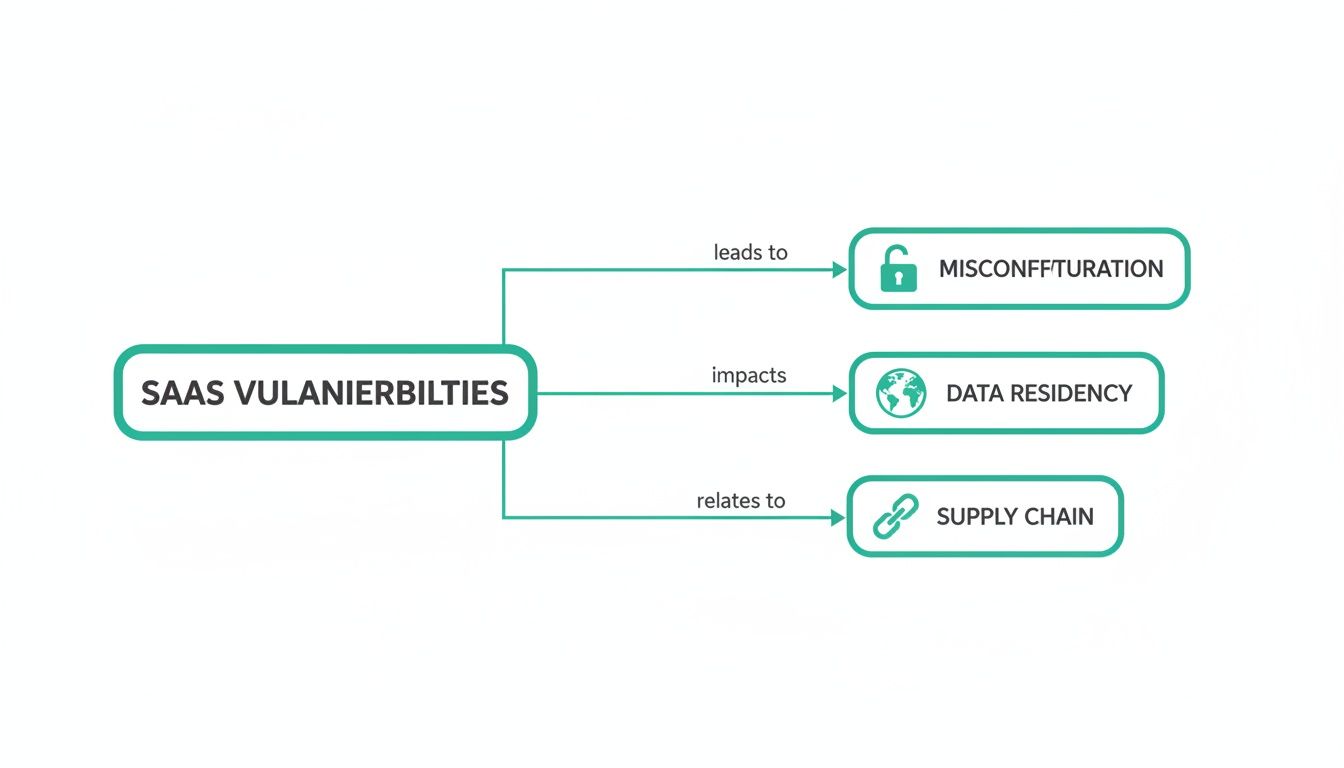
Finding Your Most Common SaaS Vulnerabilities
To secure your SaaS apps, you must know where attackers look first. Think of it like defending a castle. You need to find the weak walls and unlocked gates before the enemy does. For SaaS, those weak spots are common vulnerabilities that hackers exploit every day.
Most SaaS platforms use a multi-tenant architecture. This is like a big office building where many companies rent space. Everyone shares the same foundation and plumbing. A single weakness in that shared infrastructure could expose everyone's data.
Do you know where your customer data is physically stored? When you use a SaaS product, your data could be on a server in another country. This is called data residency, and it's a huge deal for compliance with rules like GDPR or HIPAA.
APIs are the digital handshakes that let your software talk to each other. But an insecure API is like a secret password that everyone knows. An attacker can use it to steal data or hijack accounts. You can learn more about these weaknesses in our guide on common web application security vulnerabilities.
How Simple Mistakes Cause Major Breaches
You might picture data breaches as complex, high-tech heists. The reality is much simpler. Most security failures start with small, avoidable mistakes. A developer forgets to remove a password from public code on GitHub, or an IT admin misconfigures a cloud server.
These simple errors are gold for hackers. They are constantly scanning for exposed API keys or open storage buckets. It’s the digital version of leaving the key to your office taped to the front door. An attacker finds the key, walks in, and takes everything.
Cloud security breaches have exploded, with 80% of companies hit in the past year. You can read more about these cloud security statistics and their growing impact. This shows how everlasting these SaaS vulnerabilities really are. The problem is real, but it is fixable.
The scary part is that 60% of all data breaches involve a human mistake. You can find more data breach statistics and their causes to see the full picture. Attackers don't need to be geniuses; they just need to find one person who made a mistake.
This is why an affordable penetration test is so effective. Our OSCP, CEH, and CREST certified pentesters think like attackers. They hunt for these exact kinds of holes and deliver a clear, actionable report in under a week. This lets you fix what matters fast, without the ridiculous price tag of traditional firms.
How To Start Mitigating Your Risks
Knowing the risks is one thing; fixing them is what counts. You don't need a massive budget to improve your defenses. Let's walk through simple, high-impact steps to cut your risk today.
First, make a list of every single SaaS application your company uses. You can't protect what you don't know you have. This includes the "shadow IT" apps that employees use without approval. Once you have a list, you can start asking who has access and what data is stored in each tool.
Next, enforce strong access controls. This means only giving employees access to the data they absolutely need to do their jobs. This is known as the principle of least privilege. You can learn more in our guide on how to implement zero trust security.
Your security is only as strong as your weakest vendor. Before you buy any new SaaS tool, vet its security. Ask for compliance certifications like SOC 2 and make sure they support multi-factor authentication. If you handle payments, make sure your vendors know what is PCI DSS compliance.
Finally, you must test your controls. A penetration test is the single best way to validate that your defenses actually work. Our fast and affordable pen test process gives you an objective, real-world assessment of your security posture. It answers the most important question: "Can an attacker get in?"
How We Find Flaws Before Hackers

So, how do you find these hidden weaknesses before an attacker does? The answer is a penetration test. Think of it as hiring ethical hackers to try and break into your systems. They use the same tactics as real criminals to see if your security can withstand an attack.
A manual pen test goes much deeper than an automated scan. Our certified pentesters think like attackers. They find business logic flaws that automated tools are completely blind to. This is how you discover the critical issues that scanners always miss, as we explain in our guide on SaaS pentesting.
The goal of a pen test is simple: find your security holes before the bad guys do. Our team of OSCP, CEH, and CREST certified professionals specializes in finding the weak points in your SaaS environment that expose you to risk.
Traditional penetration testing is notoriously slow and expensive, which doesn't work for startups. We built our service to fix this. We deliver a comprehensive penetration testing report in your hands within a week, at a price you can actually afford.
What To Expect From Your Report
A good pentest report is a clear, practical guide to making your business safer. We write our reports for busy IT managers, compliance officers, and founders. We tell you what to fix first so you can focus your team's effort where it counts.
We built our entire process around speed and affordability. You will get your complete, easy-to-understand pentest report within one week. This quick turnaround means you can start fixing vulnerabilities immediately, shrinking the window of opportunity for attackers.
Our reports are written by our OSCP, CEH, and CREST certified pentesters. They explain each finding in simple terms and provide clear steps to fix them. If you're ready for a pentest that delivers real value quickly, reach out through our contact form.
Frequently Asked SaaS Security Questions
We get it. You need clear, direct answers, not more jargon. Here are the most common questions we hear from IT managers, CISOs, and startup founders about SaaS security and our affordable pentests.
How much does a pentest cost?
Traditional penetration testing costs a fortune because you're paying for their massive overhead. We are different. We focus on efficiency, which lets us offer a high-quality manual pen test at a price that startups and SMBs can afford. Get a fast, no-nonsense quote from our contact form for a fast, no-nonsense quote.
How quickly can I get my report?
We know you can't wait months for a report while your business is at risk. Our streamlined process ensures you receive your complete penetration test report within one week. This speed lets you fix vulnerabilities immediately and meet tight compliance deadlines.
Will this pentest help with compliance?
Yes. A manual pen test is critical for compliance frameworks like SOC 2, HIPAA, and ISO 27001. Auditors and customers want to see that you've tested your defenses against a real-world attack. Our reports provide the third-party validation you need to prove your security posture.
What is a manual pen test?
Automated scanners find common, low-hanging fruit. A manual pen testing engagement is driven by a creative human expert who thinks like an attacker. Our OSCP, CEH, and CREST certified pentesters find high-impact security holes that scanners always miss.
Ready to find and fix your SaaS security weaknesses? Fill out our contact form to get a quote today. We deliver fast, affordable, and expert-led penetration tests that give you the clarity and confidence to secure your business.
.svg)
