You’ve got an audit date coming up. Your customer wants proof. Your board wants a straight answer. And the security firm you contacted wants a big budget, a long kickoff process, and weeks of waiting before they even start.
That’s the part nobody says out loud. A lot of compliance testing is bloated, slow, and overpriced.
Startups and SMBs get hit hardest. You don’t have time for six sales calls, vague scoping, and a report that lands after your audit window closes. You need a clear scope, a real penetration test, and an audit-ready report fast. That’s it.
Your Guide to Passing Audits Without Breaking Budgets
A familiar mess looks like this. Your team is working on SOC 2, PCI DSS, HIPAA, or ISO 27001. The auditor asks for a pen test report. You reach out to a few vendors and get the same routine. Long intake forms, high quotes, and delivery timelines that make no sense if your audit is already on the calendar.
That old model is broken for smaller teams.

Founders feel it. IT managers feel it. Compliance officers definitely feel it. You’re not trying to buy a giant consulting program. You’re trying to prove your controls were tested by qualified people and get a report your auditor can use.
Why most firms frustrate SMBs
A lot of traditional shops were built for enterprise procurement, not lean teams. They move slowly because their process is heavy, not because the work is better.
Here’s what usually wastes your time:
- Slow scoping: You answer the same questions on multiple calls before anyone gives you a real quote.
- Oversized engagements: They push broad testing when you only need a defined compliance scope.
- Weak reporting: Some reports look polished but don’t clearly support the audit requirement.
- Bad timing: By the time the report arrives, your audit or customer review is already stalled.
If you’re preparing for SOC 2, a practical checklist like Church Extension Fund SOC 2 preparation can help your team line up evidence before the auditor starts asking for it.
Practical rule: If a vendor can't explain scope, timeline, and deliverables in plain English, don't hand them your audit deadline.
Budget matters too. If you want a grounded look at pricing before you talk to vendors, review this breakdown of the average cost of penetration testing.
You do not need to accept a month-long ordeal just to check a compliance box. Security compliance testing can be fast, targeted, and useful if you choose the right scope and the right testers.
What Exactly Is Security Compliance Testing
Think of security compliance testing like a building inspection. You can say your office is safe, but an inspector still checks whether the doors lock, the wiring is right, and the fire exits work. Security compliance testing does the same job for your systems.
It proves that your controls meet a standard your auditor, customer, or regulator cares about.

What auditors are really asking
An auditor usually isn't asking whether your environment is perfect. They want evidence that you implemented controls, tested them, and handled what the testing found.
That means your test work needs to be documented, scoped, and tied to a real requirement. A random scan report usually won't cut it. A clean-looking dashboard also won't cut it.
Security control testing includes eight distinct methods, including vulnerability assessments and penetration testing, according to Pearson's explanation of security control testing. That source also states that vulnerability scans are automated and should run quarterly, while a penetration test is an annual exercise that manually exploits vulnerabilities to test defenses and provide the hard evidence needed for frameworks like SOC 2.
Why testing is different from paperwork
A policy says what your team intends to do. Testing shows whether your controls hold up.
That’s why auditors ask for proof such as:
- Defined scope: What systems, apps, or networks were tested
- Testing method: Whether the work included scanning, manual validation, and exploitation
- Findings and severity: What the testers found and why it matters
- Remediation evidence: What you fixed or accepted
- Final report: A document that maps the work to the compliance objective
A policy can satisfy a questionnaire. A penetration test report satisfies a tougher question: did anyone verify this control in the real world?
If your team is also trying to make sense of risk, governance, and evidence collection, this guide to GRC cyber security is a useful plain-English companion to the testing side.
Security compliance testing isn't about buying the biggest assessment you can find. It’s about producing evidence that stands up in an audit and helps you keep customers.
Pentesting Vulnerability Scanning And Audits Explained
These three terms get mixed together all the time. That leads companies to buy the wrong service, then scramble when the auditor says it isn’t enough.
Here’s the simple version. A vulnerability scan looks for common weaknesses. A pentest, also called a pen test or penetration test, tries to use those weaknesses the way an attacker would. An audit reviews whether your controls, records, and procedures match the standard.

The easiest way to picture it
Use an office building example.
- Vulnerability scanning is checking for accessible windows, broken badges, and doors that don’t latch.
- Penetration testing is hiring a trained professional to actively try those doors and see how far they can get.
- Auditing is reviewing whether the building team followed the required security procedures and documented them properly.
They are not interchangeable.
What each one is good at
A scan is fast and broad. It’s useful for routine hygiene and for spotting obvious issues early. But a scanner doesn’t think like a person, chain small weaknesses together, or explain business impact very well.
A penetration test goes further. The tester validates real risk, manually checks edge cases, and shows whether a weakness is exploitable in your environment. That’s why a pen testing engagement carries more weight with auditors and customers.
An audit is different again. Auditors review evidence. They want reports, policies, diagrams, approvals, tickets, and proof that required testing happened. They usually don’t perform the attack simulation themselves.
Side by side comparison
| Service | Main job | What you get | Best use |
|---|---|---|---|
| Vulnerability scan | Find common issues quickly | A list of possible weaknesses | Ongoing security hygiene |
| Penetration test | Prove what can really be exploited | Validated findings and attack paths | Compliance evidence and real risk testing |
| Audit | Check conformity to a framework | Pass, gap, or remediation requests | Formal compliance review |
If your team is still sorting out which service fits which requirement, this explainer on vulnerability assessment vs penetration testing helps separate the terms without the usual consultant fog.
Bottom line: Buy a scan when you need coverage. Buy a penetration test when you need proof. Expect an audit when someone else needs evidence.
The expensive mistake is assuming one can replace the others. It usually can’t.
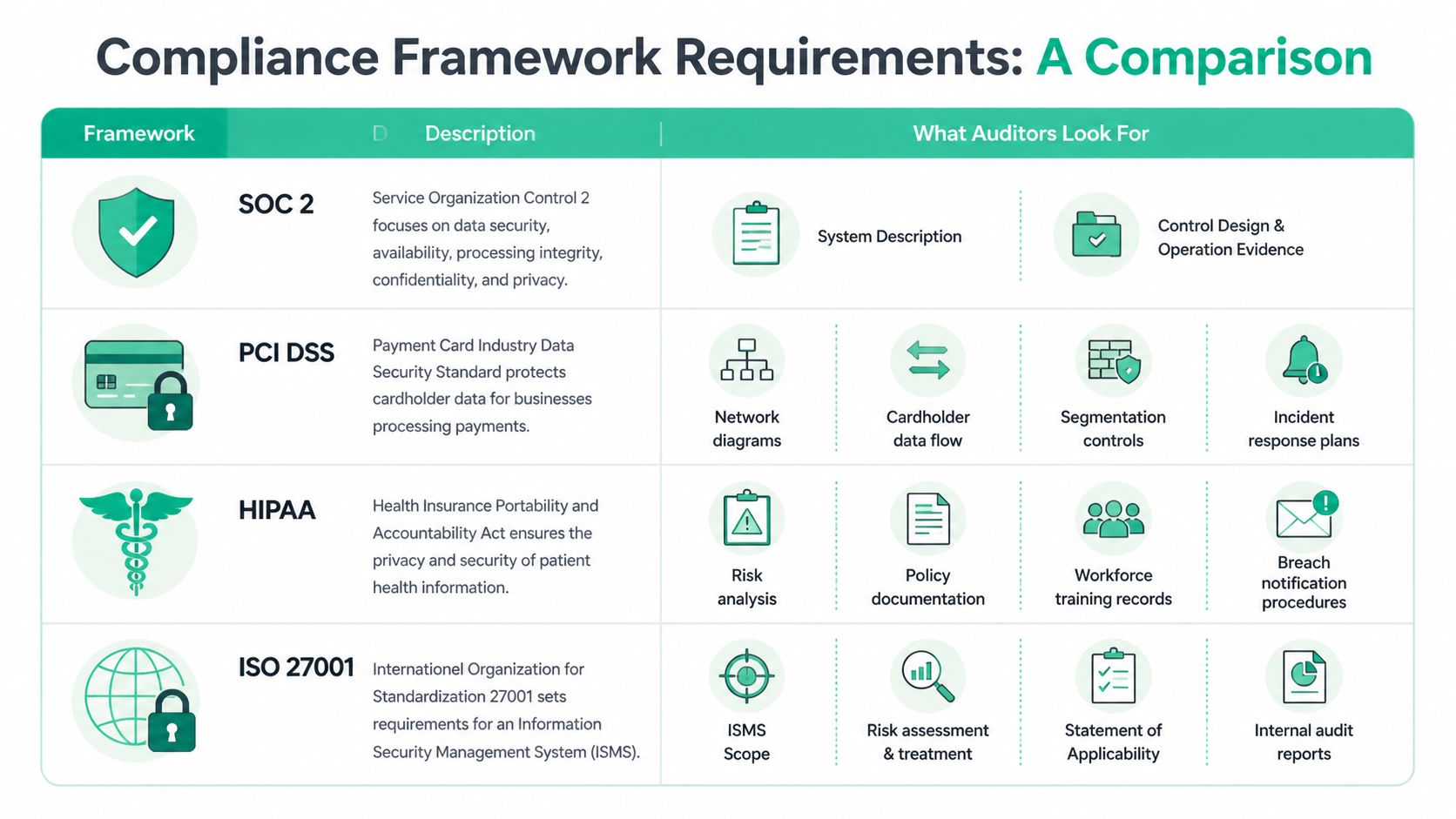
Meeting Your Specific Compliance Framework Requirements
Different frameworks ask for different evidence. That’s where a lot of companies get burned. They buy a generic penetration test, then learn too late that the report didn’t match what the auditor needed.
The fix is simple. Scope the test to the framework before the work starts.
What matters across all frameworks
No matter which framework you’re dealing with, auditors want a few basics:
- Clear boundaries: The report should state exactly what was in scope
- Credible method: The testing method needs to look like real security work, not a checkbox scan
- Actionable findings: Findings should be understandable and tied to risk
- Evidence trail: Dates, systems tested, and remediation details should be easy to follow
A good compliance program also has to stay organized between audits. If your team is trying to tighten that process, this article on what compliance management is gives a practical overview.
SOC 2 expectations
For SOC 2, auditors care about whether your stated controls are designed well and operating as claimed. Your penetration testing should support that story.
The report should line up with the systems and services covered by your SOC 2 scope. If you say your customer data is protected by access controls, segmentation, secure development, and monitoring, your test should examine the systems where those controls matter most.
A SOC 2-focused report is more useful when it includes:
- System description alignment: The report matches the apps, environments, and boundaries in your SOC 2 documentation
- Control relevance: Findings relate to the security and confidentiality controls you say you run
- Operational evidence: The work shows that controls weren’t just written down, they were exercised
PCI DSS expectations
PCI DSS is less forgiving about scope confusion. If your team handles cardholder data, the penetration test must reflect the environment that processes, stores, or transmits it, including segmentation if you rely on segmentation to reduce scope.
PCI-focused testing usually needs supporting material such as:
- Network diagrams
- Cardholder data flow
- Segmentation controls
- Incident response plans
If your test ignores a connected system that can reach the cardholder data environment, you may end up paying twice. Once for the first test, then again for the retest or gap work.
HIPAA expectations
HIPAA is often treated like a policy exercise. That’s a mistake. Policies matter, but healthcare and health tech teams also need to show they understand where protected health information lives and how it could be exposed.
Auditors and assessors often expect evidence around:
- Risk analysis
- Policy documentation
- Workforce training records
- Breach notification procedures
A penetration test helps by showing whether technical safeguards around sensitive health data can be bypassed. It’s one of the clearest ways to move from “we believe we’re secure” to “we tested the controls.”
ISO 27001 expectations
ISO 27001 is broader because it centers on the Information Security Management System. The pentest matters, but it sits inside a larger management and risk framework.
Your evidence set typically needs to support items like:
- ISMS scope
- Risk assessment and treatment
- Statement of Applicability
- Internal audit reports
This is one reason generic security reports fall flat. They may describe vulnerabilities well but fail to support the larger control and risk story your ISO auditor is reviewing.
Why penetration testing keeps rising in importance
According to the A-Lign Compliance Benchmark 2025 summary published by Bright Defense, penetration testing, SOC 1, and ISO 27001 are considered the most critical audit types for businesses. The same source says 45% of companies expect compliance to become more involved in cyber resilience, which is exactly why testers need to produce evidence that shows how your organization stands up to realistic attack paths.
Don’t buy a “compliance pentest” unless the provider can explain how the report will support your exact framework and scope.
If a vendor can’t talk through scope boundaries, in-scope assets, and auditor expectations in plain English, keep looking.
Our Simple Pentest Process Start To Finish
A good compliance pen test shouldn’t feel like buying enterprise software. It should feel like hiring a specialist to do a defined job quickly and clearly.
The process that works is short, direct, and easy to verify.
Step one is fast scoping
Many firms waste your time. They ask broad questions, schedule multiple calls, then send a quote that still leaves key details vague.
A better scoping process does four things right away:
- Defines targets clearly so everyone knows what’s in and out.
- Matches the test to the framework so the report supports the audit.
- Sets timing upfront including testing window and report delivery.
- Explains assumptions such as whether testing is authenticated, external, internal, or web app focused.
If any of that is fuzzy, the engagement is already drifting.
Step two is real manual testing
This is the part that matters most. Scanners help, but compliance-grade penetration testing needs human validation and manual exploitation where appropriate.
That means the testers should be able to explain what they attempted, what worked, what failed, and why that matters to your risk. Certifications such as OSCP, CEH, and CREST matter here because they signal that the tester has been trained and evaluated, not just handed a tool.
Cheap reports are expensive when nobody can defend the testing method to an auditor.
Step three is clear reporting
A useful report should be readable by more than one audience. Security staff need technical detail. Compliance staff need traceable evidence. Leadership needs a short, honest summary.
Audit-ready reporting should include:
- Executive summary: Plain-English overview of what was tested and what was found
- Scope and methodology: Enough detail for an auditor to understand the engagement
- Findings with proof: Clear descriptions, evidence, risk context, and remediation advice
- Retest status if applicable: Confirmation of what was fixed and rechecked
The timeline matters too. If a provider takes forever to write the report, they’re slowing down your audit, not helping it.
Step four is remediation support
A lot of firms disappear once they send the PDF. That’s lazy.
You need direct remediation guidance so your team can fix the issues without guessing what the tester meant. You also need a path to retesting if the auditor or customer asks for proof that the issues were addressed.
One option in this market is Affordable Pentesting, which provides manual penetration testing for frameworks such as SOC 2, PCI DSS, HIPAA, and ISO 27001, with audit-ready reporting designed for startups and SMBs. The point isn’t brand hype. The point is to choose a provider that respects your budget, explains the scope clearly, and gets the report back fast enough to be useful.
Choosing Internal Testers Versus A Third Party
Internal teams know your environment. That’s their biggest strength. It’s also the reason they’re not always the right people to perform your compliance penetration test.
People who build and manage a system tend to inherit assumptions about it. They know what “should” be locked down. A third party checks what is in place.
When internal teams help most
Your internal team is valuable before and after the engagement.
They can help with:
- Scoping: They know what systems matter and where the risky edges are
- Access and coordination: They can line up credentials, contacts, and maintenance windows
- Remediation: They own the fixes after the report lands
That work is essential. It just isn't the same as independent testing.
Why third-party testing usually wins
Independence matters in compliance. Auditors want testing that isn’t clouded by the same team that designed or runs the controls.
Third-party testers also bring a more adversarial mindset. They don’t give your environment the benefit of the doubt. That’s useful because attackers won’t either.
For startups and SMBs, budget is the biggest barrier. A 2025 analysis summarized by WeSecureApp’s penetration testing guide for compliance and audits says 62% of small firms cite budget as the top barrier to compliance testing. That same source also claims affordable penetration testing can reduce breach costs by 30-50%, and argues that targeted, automated-assisted tests can deliver 80% efficacy for compliance at lower cost than full manual engagements.
Those numbers should make one thing obvious. Smaller companies don’t need bloated consulting packages. They need a scoped test that includes the right assets, uses qualified testers, and produces evidence the auditor accepts.
A simple decision test
Use this quick comparison:
| Option | Best use | Main weakness |
|---|---|---|
| Internal team | Prep, validation, remediation | Lacks independence for many compliance needs |
| Third-party specialist | Formal pentest and audit evidence | Requires careful vendor selection |
If the result needs to persuade an auditor, a customer, or a board member, an independent penetration test is usually the smarter call.
Look for testers with OSCP, CEH, or CREST backgrounds, clear scope language, and report samples that read like evidence instead of marketing.
Make Compliance Testing Your Competitive Advantage
Teams often treat compliance testing like a tax. They just want it over with.
That mindset is too small.
A solid penetration test report helps you pass an audit, but it also helps you answer customer security reviews faster, reduce deal friction, and show that your team takes security seriously. That matters when you’re selling into larger accounts that expect proof, not promises.
What smart teams do differently
They stop buying mystery services. They scope tightly, test the systems that matter, and ask for reporting that an auditor can use.
They also move faster. Waiting weeks for a vendor to get organized doesn’t make your company safer. It just delays revenue, procurement approval, and internal signoff.
Here’s the practical shift:
- Treat testing like evidence generation: The report should support sales, audits, and internal remediation
- Buy only the scope you need: Broad engagements sound impressive but often waste money
- Use speed as a requirement: If the report arrives too late, the engagement failed
Security compliance testing doesn’t have to drain your budget or hijack your quarter. Done right, it becomes proof that your company is serious, organized, and safe to do business with.
Frequently Asked Questions About Compliance Pentesting
Teams usually ask the same few questions once they realize they need a pen test for compliance. Good. Those are the right questions to ask before you sign anything.
How quickly can I get a pentest report for my audit
It depends on scope and provider process. A focused engagement with a clear target list can move quickly, while a poorly scoped project drags.
If speed matters, ask for the report timeline before kickoff, not after testing starts. If a provider can’t commit to a practical delivery window, don’t assume they’ll suddenly become fast later.
What makes a penetration testing report audit-ready
An audit-ready report clearly states the scope, the testing dates, the methodology, the assets tested, the findings, and the remediation guidance. It should read like evidence, not like a sales brochure.
The best reports are easy for three audiences to understand. Technical staff, compliance staff, and auditors should all be able to use the document without needing a translator.
Does a clean pentest guarantee I pass my audit
No. A penetration test is one piece of the evidence set.
Auditors also care about policies, access control, logging, training, change management, asset inventory, and other controls tied to your framework. A clean report helps. It does not replace the rest of the program.
How often should we schedule compliance testing
Planned testing beats reactive testing. According to Secureframe’s compliance statistics overview, only 22% of organizations regularly audit third parties, 11% report annually, and 77% of security leaders planned to transition to updated frameworks such as PCI DSS 4.0 within 18 months as of 2023. That combination creates obvious risk if your team only tests when an auditor or customer forces the issue.
The practical answer is simple. Put penetration testing on a schedule that matches your framework and your rate of change.
How much should a compliance penetration test cost
Cost depends on scope, environment complexity, and whether you need web app, external, internal, or segmented testing. What matters most is whether the quote maps cleanly to what the auditor expects.
Ask vendors to explain exactly what’s included, how much of the work is manual, whether retesting is included, and what the final report looks like. If the quote is vague, the engagement will be vague too.
What should I ask before hiring a provider
Use this short list:
- Who performs the test: Ask whether certified testers like OSCP, CEH, or CREST staff will do the work
- How manual the testing is: Don’t pay pentest prices for a scan with screenshots
- What the report includes: Get clarity on scope, findings, and retest documentation
- When you get the report: Make timeline a contract point, not a verbal promise
If you need a penetration test for SOC 2, PCI DSS, HIPAA, or ISO 27001 and you want a fast, plain-English quote, contact Affordable Pentesting through the contact form. Ask for a clearly scoped engagement, an audit-ready report, and a timeline that fits your deadline.
.svg)
