You need a security test, not a six-week sales cycle and a bloated PDF that tells you things you already know.
Most companies looking for vulnerability assessment and penetration testing services are under pressure. A customer wants proof before signing. An auditor wants evidence before closing the audit. Your board wants to know whether the app is secure. Meanwhile, the old-school security firm wants meetings, scope creep, and a report that lands after the deadline.
That model is broken.
A lot of the market still acts like penetration testing has to be slow, expensive, and mysterious. It doesn’t. The market itself proves demand is moving hard in the other direction. The global penetration testing market was valued at USD 1.98 billion in 2025 and is projected to reach USD 4.39 billion by 2031, with SMEs growing at a 15.4% CAGR as they move to the cloud and deal with compliance pressure like SOC2 and HIPAA, according to MarketsandMarkets penetration testing market data.
Forget Slow Expensive Penetration Testing Services
The old model wastes your time
Traditional firms love process theater. They drag out scoping, throw junior staff at the work, run a scanner, then send a report so padded with screenshots and boilerplate that your team can’t tell what is important.
That’s not a security service. That’s paperwork.
If you’re trying to pass an audit or answer a customer questionnaire, you don’t need a vendor who disappears for weeks. You need a clear result, a real pen test, and findings you can act on fast.
Cheap scans are not the same thing
There’s also a bad low-end version of the same problem. Some providers sell a “penetration test” that’s really just an automated scan with a logo on the front page. It’s cheaper, but it won’t help much when a client asks whether a human personally tested exploit paths, access controls, and business logic.
Manual work matters. A real tester checks what an attacker can do, not just what a scanner thinks might be wrong.
Practical rule: If a provider can’t explain what parts of the work are manual, assume you’re buying a scan.
Fast and affordable is the right standard
You shouldn’t have to choose between speed, cost, and quality. That tradeoff gets pushed because a lot of firms still run outdated delivery models. They’re built for giant enterprises with giant budgets. Startups and SMBs get stuck paying for that overhead.
A better approach is simple:
- Keep scope tight: Test what matters for the audit, release, or customer review.
- Use certified human testers: OSCP, CEH, and CREST matter because they show the tester has done the work, not just learned the vocabulary.
- Deliver reports quickly: A report that arrives within a week is useful. A report that arrives a month later is history.
- Write findings in plain English: Your developers and your auditor should both understand it.
If you’re comparing options, start with this breakdown of an affordable pentest approach. It lines up with what most smaller teams need. Clear scope, manual validation, and no nonsense.
What Is The Difference Between These Two Tests
A lot of buyers lump everything together under “security testing.” That’s how they end up paying for the wrong thing.
A vulnerability assessment and a penetration test are related, but they are not the same. One finds possible issues across a broad surface. The other tries to prove whether those issues can be used to break in.
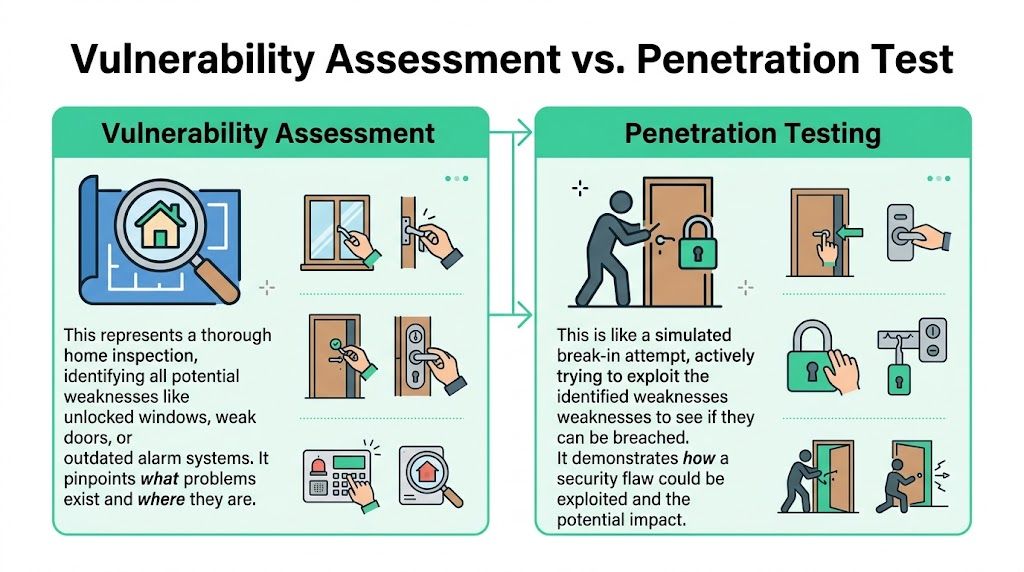
Think of it like home security
A vulnerability assessment is like walking around a house and checking for weak locks, open windows, broken lights, and doors that don’t shut right. It creates a list of possible problems.
A penetration test is like hiring someone to act like a burglar and see whether those weaknesses let them get inside, move through the house, and reach the safe.
That difference matters because scanners are noisy. Automated vulnerability scanners often produce false positives exceeding 50% without manual validation, while an expert penetration tester can reduce that to less than 10% by confirming exploitability, according to EC-Council’s explanation of penetration testing phases.
Why buyers get confused
The confusion usually starts with marketing language. Vendors use “VAPT,” “pen testing,” “security assessment,” and “scan” almost interchangeably. They shouldn’t.
If your goal is broad visibility, a vulnerability assessment helps. If your goal is proving security controls, meeting customer expectations, or validating real risk, you need a penetration test.
For another practical outside view, this guide on Penetration Testing vs Vulnerability Scanning does a good job showing where automated scanning stops and human testing starts.
Side by side comparison
| Aspect | Vulnerability Assessment | Penetration Test (Pentest) |
|---|---|---|
| Main goal | Find potential weaknesses | Prove which weaknesses are exploitable |
| How it works | Mostly automated scanning | Manual testing with targeted tooling |
| Depth | Broad coverage | Deeper validation of real attack paths |
| Output | List of possible issues | Evidence-backed findings with impact |
| Best use | Routine monitoring and hygiene | Compliance, release readiness, customer assurance |
| False positives | Higher without manual review | Lower because a tester verifies findings |
| Business value | Good for visibility | Better for prioritization and action |
What most companies actually need
The choice isn't a permanent one. Both are required, at different times.
Use a vulnerability assessment when you want ongoing coverage across your environment. Use a pen test when definitive validation is critical and you need proof. That usually means before a big release, before an audit, after major changes, or when an enterprise prospect asks hard questions.
If you want a deeper breakdown of where each fits, this comparison of vulnerability assessment vs penetration testing covers the buying decision in plain language.
A scanner tells you what might be wrong. A pentester tells you what an attacker can actually do.
How Our Fast Penetration Testing Process Works
The process shouldn’t feel like a black box. If your provider can’t explain how the work gets done, that’s a warning sign.
A clean penetration testing process has four parts. Scope it fast, test it properly, report it clearly, and help fix what matters.

Scope the test without wasting a week
Scoping should be short and direct. What’s in scope, what’s out, what kind of test you need, and who signs off. That’s it.
Good scoping keeps the project affordable because it stops the usual nonsense. You don’t need every asset tested just because a vendor wants a bigger quote. You need the internet-facing app, the API, the cloud setup, or the internal segment that matters to your risk and compliance deadline.
Test with certified humans
At this juncture, a real penetration test separates itself from a scanner package.
Certified pentesters with OSCP, CEH, and CREST backgrounds manually look for things tools miss. That includes broken access control, weak authentication flows, insecure business logic, bad privilege boundaries, and chaining smaller issues into a real path to compromise.
Manual testing also keeps the report honest. The point isn’t to flood you with findings. The point is to confirm what’s exploitable and explain why it matters.
Reporting has to be fast and useful
Most security reports fail at the one thing they’re supposed to do. Help people fix problems.
Nearly 60% of all cyber breaches are attributable to known but unpatched vulnerabilities, which is exactly why reports need to prioritize fixes based on real exploitability instead of dumping a giant list on your team, as noted in DeepStrike’s 2025 penetration testing statistics.
A good report should give you:
- An executive summary: For leadership, procurement, and auditors
- Clear technical findings: What was found, how it was validated, and what it means
- Proof of impact: Enough detail to show the issue is real
- Fix guidance: Specific remediation steps your team can use
- Retest path: A clean way to verify the fix
When we talk about speed, we mean the report lands within a week. That timeline matters because security findings expire fast. If your team has to wait too long, code changes, infrastructure moves, and the report becomes less useful.
Remediation is part of the job
A provider who sends the report and vanishes isn’t helping much.
Your team should be able to ask questions, confirm whether a fix is enough, and schedule a retest. That’s the practical part most buyers miss when comparing quotes. The report is only half the service. The other half is helping your team close the loop.
One option in this space is Affordable Pentesting, which offers manual pentests and ongoing PTaaS for companies that need a one-time assessment or repeated validation. That model makes sense for teams that need speed without buying a giant annual consulting package.
How Penetration Testing Helps With Compliance Audits
Auditors don’t care that you “take security seriously.” They care about evidence.
That’s why penetration testing matters so much for compliance. A real report gives you something concrete to show. It proves someone tested the environment, validated risk, and documented what needs remediation.

Compliance frameworks want proof
SOC 2 buyers usually need evidence that security controls are working. PCI DSS is even more direct and expects penetration testing as part of the control environment. HIPAA pushes you toward risk analysis and validation, not vague promises. ISO 27001 also rewards organizations that can show they test and verify controls in practice.
A proper penetration test earns its keep, transforming “we believe we’re secure” into “here’s the assessment, here are the findings, and here’s what we fixed.”
If SOC 2 is the pressure point, this page on SOC 2 penetration testing is a practical reference for what auditors and customers usually expect.
Breach cost changes the budget conversation
A lot of SMBs hesitate because they don’t have a huge security budget. I get it. But the math gets ugly fast when you look at breach impact in regulated sectors.
In healthcare, the average data breach cost is USD 9.8 million. In finance, it’s around USD 5-6 million, based on the analysis summarized by Scytale on penetration testing vs vulnerability assessment.
That’s why delaying testing is usually a false savings. You save money this quarter and take on much bigger risk the whole time.
What auditors want: a defined scope, test dates, methodology, findings, severity, remediation guidance, and evidence that the work was performed by qualified people.
Different audits ask different questions
Use this quick lens when matching a pen test to a framework:
- SOC 2: You need evidence that security controls aren’t just documented. They’re tested.
- PCI DSS: You need a formal penetration test that supports cardholder data environment security.
- HIPAA: You need risk analysis that reflects actual system exposure.
- ISO 27001: You need technical validation that supports your control environment.
Some companies also have adjacent requirements that sit outside those larger frameworks. If you’re dealing with UK customer requests or vendor due diligence, this overview of Cyber Essentials Plus Certification is worth reading because it shows how hands-on verification fits into broader assurance work.
The report matters as much as the test
A bad report creates audit pain even if the testing was decent.
Auditors and compliance teams need a document they can follow without playing translator. Your developers need the same thing for a different reason. They need clear steps, not security theater. If the report is just jargon and scanner output, it won’t help either group.
How To Choose The Right Pentesting Company
Buying a pentest badly is easy. The sales pitch sounds polished, the scope sounds extensive, and then the report lands with almost nothing useful in it.
You can avoid that if you ask a few direct questions.
Check the people, not just the brand
Plenty of firms sell the company logo and hide the actual testers. Don’t accept that.
Ask who will perform the work and what certifications they hold. OSCP, CEH, and CREST are worth asking about because they tell you more than a generic “our team is experienced” line.
Ask for a sample report
This is one of the fastest ways to spot a weak provider.
A solid sample report should be readable by both technical and non-technical people. You should see an executive summary, validated findings, proof, risk explanation, and specific remediation guidance. If the sample looks like raw scanner output or a hundred pages of copy-paste noise, walk away.
Ask what happens after the report
Many organizations only run annual penetration tests, which creates a validation gap where weaknesses can sit around for months. That gap matters because over 48% of vulnerabilities discovered during pentests are never remediated, as discussed in Picus on the vulnerability assessment and penetration testing gap.
That means remediation support isn’t a nice extra. It’s part of the service.
Look for a provider that offers:
- Fix clarification: Your engineers can ask whether the remediation is correct
- Retesting: The tester comes back and verifies the issue is closed
- Reasonable scheduling: You don’t wait forever to validate fixes
- Ongoing options: Useful if you release often or face constant customer reviews
Price should be clear
If pricing feels vague, it probably gets worse later.
Ask what is included, what triggers extra cost, whether retesting is separate, and how scope changes are handled. You’re not looking for the cheapest number. You’re looking for a provider that won’t trap you with add-ons after the kickoff call.
Good pen testing should feel structured, not theatrical. You should know what you’re buying, when it starts, and what you’ll get at the end.
Your Simple Checklist Before Starting A Pentest
You don’t need to overprepare, but you do need to be organized. A little prep makes the project faster, cheaper, and less painful for everyone.
Start with the basics
Use this checklist before you book a penetration test or pen testing engagement:
Define the scope
Decide what needs testing. Your web app, API, external network, cloud setup, or internal environment. Don’t throw in extra systems just because they exist.Get leadership approval
Make sure the right person knows why this is happening. That avoids delays when legal, compliance, or operations asks questions.Pick one technical contact
Give the testers one person who can answer scope questions fast. If nobody owns communication, timelines slip.Choose a testing window
Pick a time that won’t collide with a major release, migration, or customer event. Testing during chaos creates false alarms and bad decisions.Prepare written authorization
This is your permission slip. It protects both sides and makes the rules clear.
Keep the scope realistic
The biggest mistake I see is bloated scope. Teams ask for everything because they think more assets means better security. Usually it just means slower work and a bigger invoice.
A focused penetration test is often more valuable than a sprawling one. Test the systems that matter most to revenue, compliance, or customer trust first.
Tell your team what to expect
Your developers and IT staff should know testing is happening. They don’t need a long speech. They need the dates, the scope, and the contact person.
That one step prevents internal confusion and makes the engagement feel normal instead of disruptive.
Common Questions About Penetration Testing
Is a vulnerability assessment enough
Sometimes, yes. Often, no.
If you just need broad visibility into known issues, a vulnerability assessment is useful. If you need evidence for compliance, customer assurance, or real-world exploitability, you need a penetration test. That’s the cleaner answer.
How often should we do pen testing
At minimum, do it when a framework, customer contract, or audit requires it. Also do it after major application changes, infrastructure shifts, or big product launches.
If you release often, annual testing won’t feel like enough. In that case, a recurring model makes more sense than treating security like a once-a-year event.
What if the pentest finds nothing
That’s not automatically good news.
Sometimes it means the environment is well secured. Sometimes it means the scope was weak, the testing was shallow, or the provider mostly ran tools and called it a day. The core question is whether the tester can explain what was tested, what was validated, and what methods were used.
Are manual pentests worth the extra effort
Yes, because they answer the question buyers and auditors care about. Can someone exploit this or not?
Manual testing is where you catch the subtle stuff. Access control mistakes. Weird logic flaws. Chained issues that don’t look dangerous on their own but become serious together.
How long does the process usually take
The answer depends on scope, but the part that matters to most buyers is report speed. If you’re waiting weeks after testing ends, the service is dragging.
A good provider keeps the process tight, communicates clearly, and gets the report back quickly enough that your team can still act on it without redoing half the environment.
Will pen testing break production
A professional tester works within agreed rules and tests carefully. Some testing carries real risk, which is why scoping and communication matter.
You should always ask how the provider handles sensitive systems, production testing, and high-impact actions. If they can’t answer that clearly, don’t hire them.
How do we know if the quote is fair
Look at four things together:
- Scope quality: Is it focused and sensible
- Manual effort: Are humans doing real validation
- Report quality: Will developers and auditors both use it
- Retest support: Does the provider help close the loop
A low quote that buys you a shallow scan is expensive in the worst way. You still have to pay for a real test later.
What should we ask on the first call
Keep it simple.
Ask who does the testing, what certifications they hold, what parts are manual, how long reporting takes, whether retesting is included, and whether you can review a sample report. Those answers tell you more than a polished slide deck ever will.
If you need vulnerability assessment and penetration testing services without the usual drag, use the Affordable Pentesting contact form and ask for a scoped quote. Keep it simple. Tell them what needs testing, what deadline you’re facing, and what compliance requirement is driving it. That gets you to a real conversation faster than another round of vendor theater.
.svg)
