You’re probably here because you need an external penetration test fast, and the usual options look bad.
One firm wants weeks just to scope it. Another sends a giant quote, then runs a scanner and calls it penetration testing. Then the report shows up late, padded with filler, and your auditor still has questions.
That model is broken. It was built for giant enterprises with slow procurement and bigger budgets than sense. If you’re an IT manager, CISO, compliance lead, or founder, you need external penetration testing services that are manual, affordable, and fast enough to help this quarter, not next quarter.
Why Traditional Penetration Testing Is Broken
Legacy pentest firms love process. Clients need results.
The old model usually means too many sales calls, too much paperwork, and not enough actual testing. You pay enterprise prices, wait around, and get a report that reads like it was designed to impress a procurement team instead of helping your engineers fix real risk.

That frustration isn’t rare. The global penetration testing market reached USD 2.74 billion in 2025, and 51% of businesses exclusively rely on third-party pentesters for objectivity and specialized expertise, which tells you companies are moving away from slow internal processes and looking for outside help that works (Deepstrike penetration testing statistics 2025).io/blog/penetration-testing-statistics-2025)).
What clients are sick of
- Slow start times that burn half your audit window before testing even begins
- Opaque pricing that changes after scoping calls and legal review
- Scan-heavy work sold as a real pen test
- Weak reporting with vague findings and little remediation guidance
- Too much distance between you and the actual tester
Traditional firms often optimize for internal overhead. You need a team that optimizes for getting a useful report in your hands quickly.
Here’s my opinion after years in this industry. Most buyers don’t need more ceremony. They need certified pentesters who can manually test public-facing systems, explain findings in plain English, and turn around a report within a week.
What a better model looks like
A modern external pen test should be simple:
| Old model | Better model |
|---|---|
| Long sales cycle | Fast scoping |
| Layers of account managers | Direct access to testers |
| Scanner-first | Manual-first |
| Delayed reporting | Report within a week |
| Enterprise-only pricing | SMB-friendly pricing |
If your provider can’t explain how they find issues beyond a scanner, can’t commit to a practical timeline, and can’t produce something your auditor can use, keep looking.
What Is An External Penetration Test
An external penetration test is an authorized attack against the systems you expose to the internet. Think website, API, firewall, VPN, mail server, login portal, and cloud assets that are reachable from outside your company.
The simplest way to explain it is this. You hire an ethical hacker to check your doors, windows, and locks before a criminal does. Not by glancing at them, but by trying them.
What gets tested from the outside
Most external penetration testing services focus on internet-facing assets such as:
- Web applications your customers or staff can reach online
- APIs that mobile apps, partners, or internal tools depend on
- Email systems and remote access portals
- DNS and firewall exposure that can reveal weak setup choices
- Cloud resources that were meant to be private but aren’t
If you want a broader primer on how the field works, this overview of penetration testing is a useful reference. If you’re deciding between perimeter testing and inside-the-network testing, this breakdown of internal vs external penetration testing helps clarify where each fits.
Pen test versus vulnerability scan
Buyers often get burned.
A vulnerability scan is mostly automated. It looks for known issues and misconfigurations. That’s useful, but it’s not the same as a penetration test.
A real pen test goes further. The tester validates whether a weakness is exploitable and whether multiple smaller issues can be chained together into something dangerous.
A scanner tells you what might be wrong. A pentester shows you what an attacker could actually do with it.
That difference matters because risk doesn’t live in isolated findings. Risk often shows up when someone combines weak authentication, exposed services, and a bad configuration into one practical attack path.
What the outcome should look like
A good external penetration test answers plain questions:
- Can an outsider reach something they shouldn’t?
- Can weak authentication be abused?
- Are there exposed services you forgot about?
- Can a small flaw turn into a serious compromise?
You shouldn’t need a security degree to understand the answer. The best penetration testing services explain findings clearly enough that founders, IT teams, and auditors all walk away with the same picture of risk.
That’s the standard. If a vendor can’t explain the work in straightforward terms, there’s a good chance they’re hiding weak work behind technical language.
Our Manual-First Pentesting Methodology
Most low-cost providers lean too hard on automation. Most big firms lean too hard on process. A useful external penetration test sits in the middle. Use tools where they help. Put humans where it counts.
Our approach is manual-first because that’s how you find the issues that matter. Certified testers with OSCP, CEH, and CREST backgrounds don’t just dump scan output into a PDF. They investigate, validate, and chain weaknesses the way a real attacker would.
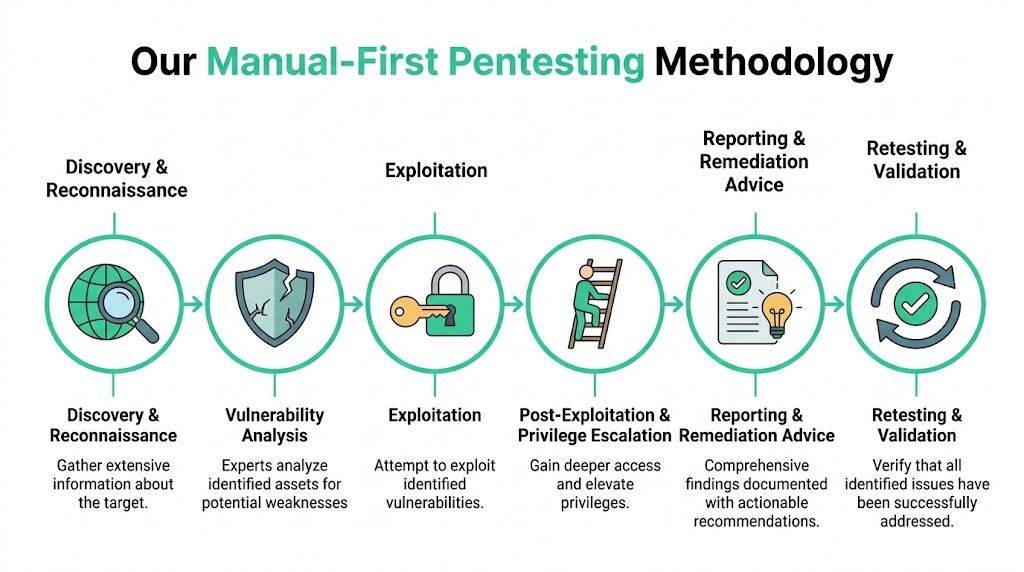
Recon starts before exploitation
External tests start with reconnaissance. That includes passive review of public records and open-source intelligence, plus active discovery like port scanning and service enumeration.
This step sounds basic, but it’s where a lot of hidden exposure shows up. Old systems, forgotten subdomains, exposed admin panels, and cloud assets often surface here before any exploitation starts.
Human testing finds the real problems
The key difference between a scan and a manual penetration test is exploitation.
According to Sprocket Security’s write-up on external pentesting best practices, strong methodology goes beyond scanning by actively exploiting and chaining vulnerabilities, which is especially important for frameworks like PCI DSS 4.0 and SOC 2 that now require validated penetration testing rather than scanning alone (external pentesting best practices).
That matters because scanners often miss things like:
- DNS mistakes that create spoofing or redirection opportunities
- Weak SSL or TLS setup combined with exposed admin access
- SMTP weaknesses that support email enumeration or relay abuse
- Default credentials left on internet-facing systems
- Misconfigured cloud services that don’t look critical until chained with another issue
A practical attack path matters more than a giant finding count
A cheap report can list dozens of minor items and still miss the one thing that puts your business at risk.
Manual testers look for attack chains. Maybe a public login leaks account detail. Maybe weak password policy makes brute forcing viable. Maybe a firewall rule exposes a management interface that should never be public. One issue alone might look mild. Combined, it becomes a real breach path.
Practical rule: Pay for validated risk, not raw scan output.
That’s also why black-box, gray-box, and white-box approaches matter. External pentesting is often black-box or lightly gray-box because you want to simulate an outsider. The more realistic the scenario, the more useful the result.
Retesting closes the loop
Testing without validation is unfinished work.
A proper engagement ends with remediation review and retesting of the important findings. That’s how you confirm that fixes worked and that the risk is reduced, not just moved around.
If you’re comparing options, one example is Affordable Pentesting, which offers external network pentest options and an AI or automated path for smaller asset counts. The right choice depends on whether you need a lightweight check, a manual penetration test for compliance, or a deeper review of a broader public attack surface.
Meet Compliance Needs for SOC2 PCI and HIPAA
A lot of companies don’t buy external penetration testing services because they woke up excited about security testing. They buy it because an auditor asked, a customer asked, or a deal is blocked until they produce a report.
That’s fine. Compliance is a business problem first. The mistake is treating the pentest like a box to check.

What auditors usually want to see
Auditors and assessors usually care about three things:
- Scope was clear
- Testing was valid
- Reporting shows evidence and remediation
If your vendor hands you a thin PDF with vague language and no proof of exploitation, you may still end up in a painful back-and-forth with your auditor.
SOC 2 needs validated testing
SOC 2 buyers and auditors want to know that your controls work in practice, especially around exposed systems and detection of weaknesses. A manual external pen test gives you evidence that someone assessed the systems attackers would see.
If you’re preparing for that audit path, this guide to SOC 2 penetration testing is worth reviewing. It helps frame what evidence your team should have ready before the auditor asks for it.
PCI DSS is more specific
PCI DSS is less forgiving because it speaks more directly to penetration testing requirements. The important point is that automated scanning alone isn’t enough. You need validated testing, and for external exposure, that means someone actively testing the perimeter the way an attacker would.
That’s why methodology matters so much in payment environments. It isn’t enough to say “the scanner came back clean.” You need proof that the internet-facing attack surface was exercised.
HIPAA demands documentation discipline
HIPAA conversations often get messy because teams assume broad security tools cover everything. They don’t.
For healthcare and adjacent vendors, external penetration testing helps demonstrate that public-facing systems handling sensitive operations were assessed with rigor. If your web presence is part of your HIPAA story, this article on mastering HIPAA compliance is a useful companion read for the broader website and operational side.
Reports need to hold up under scrutiny
A pentest report isn’t just a technical file. It becomes part of your compliance evidence set.
Dataprise notes that a report should include risk-tiered findings, exploitation evidence, and step-by-step remediation guidance, and that this documentation is important not just for PCI DSS and HIPAA but also for cyber insurance underwriting decisions (penetration testing services data sheet).dataprise.com/wp-content/uploads/2025/02/Dataprise_Penetration-Testing-Services_DataSheet.pdf)).
If your report can’t stand on its own in front of an auditor, insurer, customer questionnaire, and internal engineering review, it’s not good enough.
What a compliance-ready report should contain
| Report element | Why it matters |
|---|---|
| Executive summary | Gives leadership and auditors the short version |
| Technical findings | Helps engineers reproduce and fix issues |
| Severity by business risk | Prevents teams from treating every issue the same |
| Evidence of exploitation | Shows the risk was validated, not guessed |
| Remediation guidance | Helps your team act quickly |
| Retest results | Proves fixes were verified |
The fastest path to passing an audit isn’t the cheapest-looking PDF. It’s a report that answers questions before the auditor asks them.
Our Simple Pentesting Engagement Lifecycle
The best engagements feel boring in the right way. No chaos. No mystery. No endless waiting.
Here’s what a clean external pen test process should look like when the provider respects your time.

Step one is quick scoping
You send the public-facing assets in scope. That may be domains, URLs, or external IP ranges, depending on the engagement.
A good provider doesn’t drag this out. They ask the questions that matter, flag risky assumptions early, and lock scope without turning it into a procurement marathon.
Kickoff should be short and useful
Kickoff is where you confirm contact points, testing windows, sensitive systems, and any operational concerns. That’s it.
You shouldn’t need three separate meetings to start an external penetration test. One practical call is usually enough if the provider knows what they’re doing.
Testing happens fast
Once testing starts, you want signal, not silence.
A strong team gives short updates as work progresses, especially if they uncover something urgent. That keeps IT, security, and compliance aligned without forcing anyone into daily status theater.
Good pentesters don’t disappear for two weeks and then return with surprises.
Reporting should follow right after testing
When the test ends, the report should not vanish into a black hole of “quality assurance” for another month.
You want an executive summary, technical findings, evidence, and remediation guidance quickly while context is still fresh. For many SMBs and startups, getting that report within a week is the difference between hitting a compliance deadline and missing it.
Verification matters after the fixes
A lot of providers stop at the report. That’s lazy.
Bishop Fox highlights post-remediation verification as a critical step, noting that teams are shifting away from point-in-time annual tests toward more continuous validation cycles to maintain security posture (external penetration testing services). That lines up with what practical teams already know. A finding isn’t closed because someone said it was fixed. It’s closed when the fix is verified.
The old process versus a useful one
Old way
Multiple sales calls, slow scoping, legal drag, delayed start, delayed reportUseful way
Fast scope, kickoff, manual testing, prompt updates, report delivery, retest
That simpler lifecycle is one reason smaller teams get better value from modern providers. They’re paying for testing, not bureaucracy.
Affordable Pricing and Actionable Reports
Let’s be blunt. Price matters. If a penetration test blows up your budget, it doesn’t matter how polished the proposal looked.
That’s why affordable external penetration testing services need two things at the same time. Clear pricing and reports your team can use.
Cheap scans are expensive mistakes
The lowest quote on the market often buys you automated output dressed up as a penetration test. That creates a nasty double cost. You pay for the report, then pay again when your auditor, customer, or insurer asks for evidence that the testing was real.
A better approach is fixed, transparent pricing tied to scope and testing depth. You should know whether you’re buying a scan-heavy assessment, a manual pen test, or a mix of both.
What a useful report includes
A proper report should help three audiences at once:
- Leadership needs a plain-English summary of business risk
- Engineers need technical detail and remediation steps
- Auditors and insurers need evidence and documentation quality
Dataprise makes the point clearly. A penetration testing report is effectively a financial instrument, and it should include risk-tiered findings, exploitation evidence, and step-by-step remediation guidance because that documentation affects compliance and cyber insurance decisions.
The report should answer practical questions
When you open the final document, you should immediately understand:
| Question | What the report should show |
|---|---|
| What was tested | Clear scope and test type |
| What was found | Findings ranked by severity and exploitability |
| How it was proven | Screenshots, logs, and concise evidence |
| What to fix first | Business-focused prioritization |
| How to fix it | Step-by-step remediation guidance |
| Was it retested | Verification notes after remediation |
If those answers aren’t easy to find, the report isn’t doing its job.
Security reporting should reduce decision time. If your team needs a translator to understand next steps, the report failed.
Write for humans, not just auditors
This matters more than many firms admit.
A report packed with jargon can still be technically correct and practically useless. Good penetration testing services explain the issue, show the evidence, and give remediation guidance your sysadmin, developer, or cloud engineer can act on without a long interpretive dance.
That means plain wording like:
- exposed admin interface
- weak authentication flow
- default credentials
- exploitable misconfiguration
- internet-facing service with unnecessary exposure
Not vague consultant language that sounds smart but says nothing.
Affordability is about fit, not just sticker price
The right external penetration test isn’t always the biggest engagement. It’s the one that matches your public attack surface, compliance need, and internal capacity to fix issues.
If you’re an SMB or startup, don’t let anyone shame you into buying enterprise bloat. Buy the scope you need, insist on manual validation where it matters, and make sure remediation verification is part of the conversation from day one.
Checklist for Choosing a Pentest Vendor
Most buyers ask the wrong opening question. They ask, “How much does the pentest cost?”
Ask this first instead. “What exactly are you doing for that price?”
A vendor can sound polished and still deliver weak penetration testing services. Use this checklist to filter out the noise fast.
Ask about the testing model
The market has shifted toward more flexible delivery. Over 70% of firms now use PTaaS platforms, which is why you should ask whether the vendor offers a continuous or platform-based model rather than only a one-time annual engagement (Deepstrike penetration testing statistics 2025).
That doesn’t mean every company needs a platform right away. It means you should know whether the vendor is built for one slow report a year or for ongoing validation and collaboration.
Questions that expose weak vendors
Who is doing the testing
Ask whether the actual testers hold certifications such as OSCP, CEH, or CREST.Is the work manual or scan-only
If they dance around this question, that’s a bad sign.How fast is report delivery
If they can’t give you a practical timeframe, expect delays.Do you include remediation verification
If not, you’re buying half a service.Will we talk directly to the tester
You want access to the person doing the work, not just an account manager.Is pricing fixed and scoped clearly
If the quote feels slippery now, it won’t improve later.
If you want a fuller buying framework, this vendor selection guide is a good place to start: how to choose a pentest vendor.
A simple scorecard helps
| Vendor question | Good answer | Bad answer |
|---|---|---|
| Manual testing included | Yes, with validated exploitation | “We use advanced tooling” |
| Certifications | Named certs and tester background | “Our team is highly experienced” |
| Report timeline | Clear and short | “Depends on internal review” |
| Retesting | Included or clearly available | Extra process with vague timing |
| Compliance support | Knows SOC 2, PCI, HIPAA evidence needs | Generic “compliance friendly” wording |
Buyer check: If a vendor avoids direct answers, assume the engagement will be the same.
Don’t confuse volume with value
Some firms try to impress you with giant finding counts, thick deliverables, or endless methodology slides. None of that proves the test was useful.
What matters is simple. Did they manually test your external attack surface? Did they validate meaningful risk? Did they give you a report your team can act on quickly?
If the answer to any of those is no, keep looking.
Get Your External Pentest Report Next Week
You don’t need another slow vendor, another padded proposal, or another report that says very little in too many pages.
You need an external penetration test that checks the boxes that matter. Manual testing. Fast turnaround. Clear reporting. Real remediation guidance. That’s what moves an audit forward and helps your team reduce risk without wasting time.
The old pentesting model was built around delay. Delay in scoping. Delay in scheduling. Delay in reporting. That doesn’t work for startups, lean security teams, and compliance-driven companies trying to ship, close deals, and pass audits on a real deadline.
What to insist on
- Manual validation instead of scan-only output
- Certified testers with practical credentials like OSCP, CEH, and CREST
- A report within a week so findings are still actionable
- Compliance-ready evidence for SOC 2, PCI DSS, HIPAA, and similar frameworks
- Post-remediation verification so fixes get confirmed
That’s the baseline now. It should not be hard to buy.
If you’re under pressure from an auditor, customer, board member, or insurer, don’t overcomplicate it. Scope the public-facing assets, pick a provider that can move quickly, and demand a deliverable that works for both engineers and compliance reviewers.
A good pen test doesn’t just point at problems. It gives your team a clean path to fix them and prove they’re fixed.
If you need a fast quote and a clear path forward, contact Affordable Pentesting through the contact form. You can scope an external pen test quickly, get a practical timeline, and move toward a compliance-ready report without the usual enterprise drag.
.svg)