If you are shopping for a penetration test right now, you have probably hit the same wall everyone else does. Quotes are high, timelines are slow, and the final report often tells you things you already knew while missing the one system that can sink the whole company.
That system is usually Active Directory.
This hack the box active directory penetration testing review looks at Hack The Box the way a CTO, CISO, or IT manager should. Not as a hobby lab. As a practical way to train your team faster, prepare for a pen test, and cut wasted spend before a compliance deadline lands on your desk.
Why Your AD Is Your Biggest Security Risk
Your next audit is six weeks out. The team is fixing web findings, rotating secrets, and closing tickets. Then one tester gets a standard domain user account, abuses weak AD controls, and reaches privileged access faster than anyone expected. That is how internal compromise happens in real companies, and it is why Active Directory deserves executive attention.
Active Directory controls the business. It governs authentication, access, service permissions, workstation trust, and admin paths across the environment. If AD is weak, an attacker does not need a complex exploit. They need one foothold and a chain of ordinary mistakes.

What real AD failures look like
Real internal assessments keep exposing the same problems. Weak passwords. Password reuse. Misconfigured name resolution. Service accounts with too much privilege. Local admin sprawl. None of that sounds dramatic. It still leads to lateral movement and domain control.
That pattern matters because attackers do not break AD in one move. They chain small, preventable failures until the environment gives them what they want.
Key takeaway: AD risk usually comes from common misconfigurations linked together, not from rare exploit chains.
If your team needs a clear benchmark for what an internal reviewer should be able to test, this Active Directory penetration tester checklist is the right standard to compare against. Use it to judge both staff readiness and vendor quality before you pay for a formal engagement.
Why this directly impacts compliance
SOC 2, PCI DSS, HIPAA, and ISO 27001 all care about access control, privilege management, authentication hygiene, and evidence that security controls work. Active Directory sits in the middle of all four. If users can escalate privileges through weak AD settings, you do not just have a security gap. You have an audit problem.
This is also where budgets get wasted. Companies spend heavily on annual pentests, then send an external team into an environment with obvious AD weaknesses still in place. The result is predictable. The report fills up with findings your internal staff could have identified earlier with targeted practice, and the expensive testing window gets spent proving the basics.
Why Hack The Box makes more sense
Hack The Box gives your team a faster way to build AD attack-path awareness before a paid assessment starts. Staff learn how a low-privilege account turns into credential abuse, privilege escalation, lateral movement, and domain takeover. That translates into better hardening and cleaner pentest results.
From a business perspective, the value is straightforward:
- Lower external testing cost because the team fixes simple AD issues before the engagement
- Faster remediation because engineers understand the attack chain, not just the ticket title
- Better audit readiness because access-control weaknesses are found and corrected earlier
- Higher-value pentest reports because the assessor can spend time on deeper risk, not basic hygiene failures
Traditional AD training is slow, expensive, and usually too detached from how real operators work. Hack The Box is a better use of time. It prepares internal teams for the exact class of issues that derail compliance reviews and inflate pentest scope.
This review focuses on that business outcome. Use Hack The Box to sharpen the team, reduce waste before the formal test, and make sure the final report finds meaningful risk instead of preventable AD mistakes.
Get Your AD Pentesting Lab Running Today
Many teams overcomplicate the setup. They treat AD pen testing practice like it needs a special project, a big budget, and a week of engineering time. It does not.
You need a controlled environment, a few standard tools, and one person who can follow instructions without turning the lab into a science experiment.

What you need
For many teams, the starting stack is straightforward:
- A Hack The Box account with access to machines or Academy content that covers Active Directory
- A Kali Linux virtual machine or similar pentest distro with common tools preloaded
- The HTB VPN connection so your lab machine can reach the target environment
- A note-taking workflow so the team records commands, findings, and screenshots
- One clear owner who keeps the practice focused on outcomes, not novelty
That is enough to start learning how AD attack chains work.
Keep the buying decision simple
Leaders usually ask the wrong question first. They ask which subscription tier is perfect. The better question is whether the team will use the lab consistently enough to get value from it.
Use this simple frame:
| Team situation | Better move |
|---|---|
| One engineer wants to learn AD basics | Start small and validate usage |
| Small security team needs hands-on AD practice | Buy enough access for repeated use |
| You are preparing for an upcoming pen test or audit | Prioritize guided AD paths and realistic labs |
| You need team-wide repeatable practice | Standardize one VM, one workflow, one playbook |
If you want a clearer view of the role itself, this breakdown of an Active Directory tester is a good practical reference.
What to standardize first
Do not let every engineer invent their own setup. Standardization saves time and reduces excuses.
Use one approved VM image. Use one VPN setup guide. Use one place for notes. Use one folder structure for screenshots and evidence. That turns practice into repeatable training instead of scattered tinkering.
Practical advice: If your team spends more time customizing the lab than attacking the lab, the setup has already failed.
Where leaders should focus
The technical details matter, but the management decision matters more. You are not buying entertainment. You are buying faster skill development around the exact system most likely to create ugly findings during a genuine penetration test.
The best early outcome is not “my team solved a hard box.” It is “my team can now identify weak service accounts, risky permissions, and obvious privilege escalation paths before an auditor or external pentester does.”
That is why Hack The Box works well in a business context. You can stand up a safe environment quickly, give your team a realistic target, and start building useful muscle memory right away.
How Pentesters Find Your AD Security Gaps
Your next audit fails faster than you expect when Active Directory is messy. The external tester does not need a flashy zero-day. They need one weak account, one bad permission chain, and enough visibility to connect the dots.
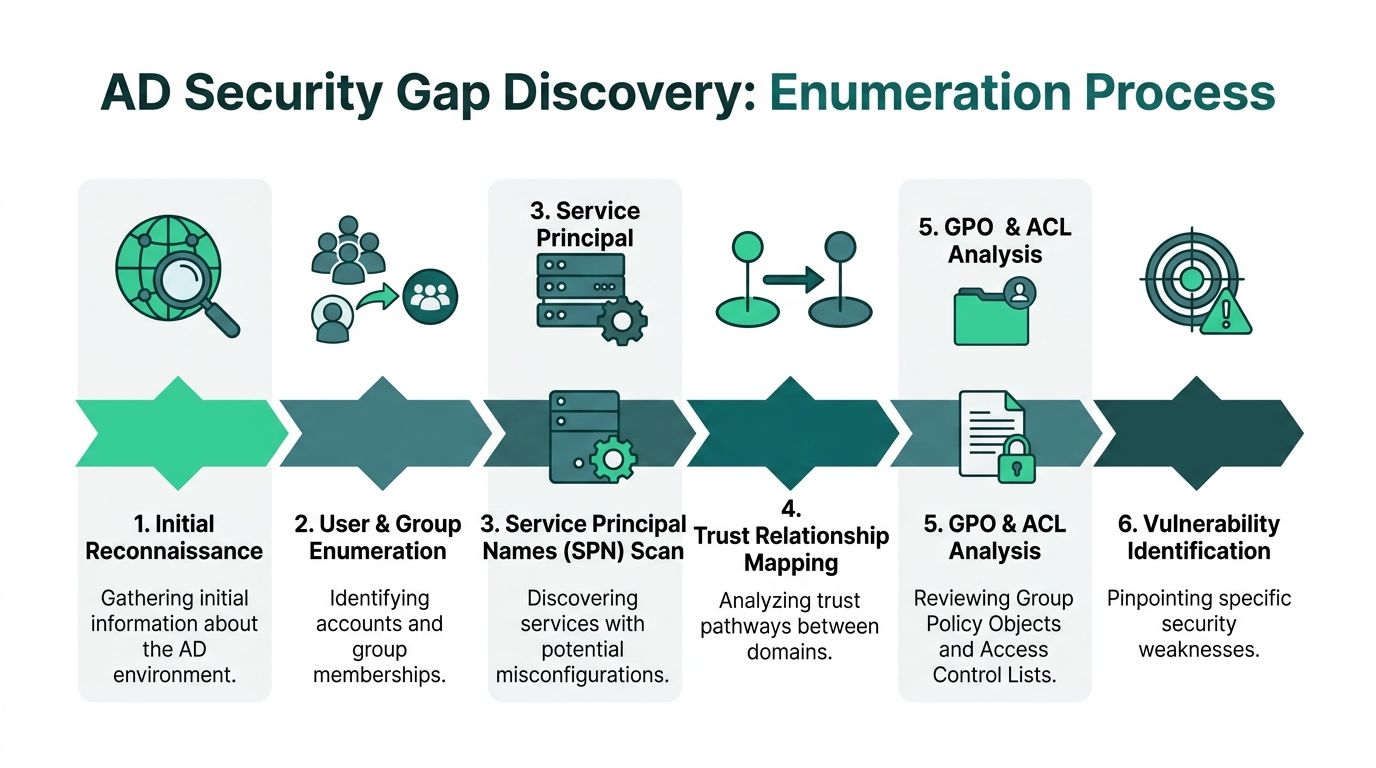
That visibility comes from enumeration.
In Active Directory, enumeration means identifying users, groups, service accounts, trusts, shares, policies, and delegated rights, then mapping how those pieces create a path to privilege. Good pentesters do this first because it is the fastest way to find real business risk. It exposes the exact weaknesses that turn a routine internal assessment into a failed SOC 2 control review, a painful PCI remediation cycle, or an expensive retest.
BloodHound is the tool that shows the underlying problem
If your team learns one AD tool well, make it BloodHound.
BloodHound maps relationships across users, groups, computers, sessions, ACLs, and delegated privileges. That matters because AD failures rarely sit in one obvious admin account. The primary issue is usually a chain of small mistakes. An over-permissioned group here. A stale service account there. Local admin access somewhere else. BloodHound turns that sprawl into a visible attack path.
That is why serious teams train on it early. It shortens the time between “we think AD is fine” and “here is the exact route to domain compromise.”
What pentesters check before they exploit anything
Strong AD testing starts with disciplined collection, not guesswork. Pentesters want to know:
- Which users exist, and which ones are stale, over-privileged, or easy to target
- Which groups control access, and who can change membership or permissions
- Which service accounts are exposed to attacks like Kerberoasting
- Which shares and scripts leak credentials or operational secrets
- Which trusts connect systems or domains
- Which policy settings and ACLs create quiet privilege escalation paths
The tools matter, but the workflow matters more. Teams that want a repeatable process should standardize the AD enumeration and post-exploitation toolset they train with so evidence collection looks the same across every lab, internal review, and client engagement.
Why this phase saves time and money
Junior operators often rush into exploitation and miss the shortest route to impact. Experienced pentesters do the opposite. They collect first, map first, and document first.
Hack The Box is useful here because it forces teams to practice the same sequence that matters in paid work. Enumerate the domain. Confirm what is reachable. Identify who can change what. Trace the path upward. That is how teams learn to find weak service accounts, risky delegations, and hidden admin paths before an external assessor bills you to discover them.
This is the business value of HTB. It compresses the learning curve without putting production systems at risk.
Important: Teams that skip trust mapping, user discovery, and permission analysis usually miss the path that matters most.
What evidence leadership should expect
A credible AD pentest should produce evidence before it produces impact. That evidence should make remediation obvious.
| Evidence type | Why it matters |
|---|---|
| User and group relationships | Shows privilege sprawl and clear escalation routes |
| Service account details | Identifies accounts that can be abused for credential access |
| ACL and delegation data | Reveals hidden control that does not show up in standard admin reviews |
| Trust relationship mapping | Finds routes into other business systems or domains |
| Share and policy review | Exposes stored credentials, weak settings, and avoidable audit findings |
Enumeration results tell you whether AD is governed or just tolerated. If the attack graph is messy, your compliance story is weak, your remediation bill goes up, and your external pentest slows down because the tester has to spend time proving basic failures.
What your team should learn from HTB
Use Hack The Box to train judgment, not box-solving speed.
Your team should leave each AD lab able to do four things well:
- Collect evidence before attempting privilege escalation
- Map attack paths in a way other engineers can reproduce
- Explain technical weaknesses in business terms
- Identify permission mistakes that standard admin work misses
That is how practice turns into faster, cheaper, compliance-focused testing. By the time you bring in an external pentester, your internal team should already understand where AD is exposed, what to fix first, and how to present those fixes in a report an auditor can follow.
Mastering Core AD Attack And Exploitation Paths
A Windows environment can pass basic control checks and still be one weak service account away from domain compromise. That is why AD attack path training matters to a CTO. It cuts the time between "we think we are covered" and "we know exactly how an attacker would move."
Hack The Box is useful here because it teaches the attack chains that show up in real internal pentests. The pattern is consistent. An attacker gets a foothold with a weak credential or captured hash, maps privilege relationships, then converts a routine misconfiguration into broad control over users, systems, and policies. That is the difference between generic security awareness and training that reduces audit friction, shortens external test time, and lowers remediation cost.
The attack paths that deserve your team’s time
Focus on the paths that repeatedly turn ordinary domain users into high-value access:
LLMNR and NBT-NS spoofing
Windows hosts can still ask the local network to resolve names. If an attacker answers first, they can capture authentication material and use it to expand access.Kerberoasting
Service accounts with weak passwords are easy targets. An attacker requests a Kerberos service ticket, cracks it offline, and gets credentials without touching the service itself.Password reuse
Shared local administrator passwords let one compromised machine unlock many others. This is one of the fastest ways to turn a small incident into an internal breach.Weak AD passwords
Low-complexity passwords on user or service accounts make privilege escalation cheap and quiet.DCSync abuse
Replication rights are often assigned too broadly. If an attacker reaches an account with those rights, they can pull password hashes from the domain controller and effectively own the directory.
These are not exotic techniques. They are operational failures. They also map directly to the issues external testers keep writing up in SOC 2, PCI, and HIPAA-driven assessments.
What these attacks mean to the business
Each of these paths points to a management problem, not just a technical one.
Weak service accounts usually mean no ownership model and no rotation standard. Password reuse points to weak endpoint administration. DCSync exposure points to poor privilege governance. Name resolution abuse points to legacy settings left in place because nobody tested whether they were still needed.
That is why traditional AD training underperforms. It spends too much time on isolated tools and not enough time on attack economics. Your team needs to know which misconfigurations lead to fast compromise, which ones create audit findings, and which ones will waste money during an external engagement.
What to practice first in Hack The Box
Train your team to work a repeatable sequence:
- Identify valid users and service accounts
- Review SPNs and test for Kerberoasting exposure
- Check for shared or predictable local admin credentials
- Map privilege relationships in BloodHound
- Confirm whether low-privilege access can reach replication rights or administrative groups
That sequence mirrors how a capable tester works under time pressure. It also produces evidence your internal team can hand to leadership and auditors: affected accounts, exposed paths, business impact, and clear fixes.
If non-security stakeholders need context on the stack behind this work, point them to this overview of common penetration testing tools used during internal assessments.
Recommendation: Train your team on chained AD abuse, not isolated tricks. External pentesters charge for time. If your staff already knows how these paths form, they will remove obvious failures before the engagement starts and get a cleaner, faster report at the end.
What a CTO should expect after this training
You should expect better remediation quality.
Teams that practice these attack paths stop filing vague tickets and start fixing the controls that matter. They remove unnecessary privileges. They rotate and strengthen service account credentials. They eliminate insecure name resolution where the business does not need it. They review replication permissions and local admin practices with clear risk context.
That is the business value of HTB for AD. It is faster than classroom training, cheaper than learning during a paid pentest, and far more useful for companies trying to tighten controls before an audit.
The Path From User To Full Domain Control
A real breach often starts with a valid user account on Monday and turns into domain control by Wednesday.
That is the Active Directory problem most leadership teams underestimate. The attacker does not need flashy malware or an instant domain admin login. They need one weak credential, one overlooked delegation, or one service account nobody reviewed after the last migration. From there, they work through the directory until they control the system that controls your staff, servers, and business applications.
How the chain builds
Hack The Box is useful here because it trains people to work through a full attack path instead of memorizing isolated tricks. A hard AD box such as APT forces the tester to enumerate carefully, collect credentials, validate privileges, and turn small findings into larger access. That sequence matches real internal pentests far better than classroom labs built around a single exploit.
For a CTO, the lesson is simple. Low-privilege access is often enough.
Once an operator has a foothold, they look for the same patterns that show up in rushed enterprise environments:
- Service accounts with weak or reusable credentials
- Kerberos paths that expose crackable material
- Group memberships nobody cleaned up after role changes
- ACL mistakes that allow object changes or delegated abuse
- Users or groups that sit too close to replication rights or administrative control
None of that is theoretical. It is how an ordinary account becomes an identity breach.
Why DCSync changes the severity of the incident
DCSync is one of the fastest ways to explain business impact to non-technical leadership. If an account has replication rights, it can request password hash data from the domain controller as though it were trusted infrastructure. At that point, the issue is no longer one compromised user. It is exposure of the identity store behind the environment.
That changes the response plan, the remediation cost, and the audit conversation.
A company preparing for SOC 2 or PCI should care because loose AD permissions create exactly the kind of control failure auditors question after an incident. You are no longer discussing one laptop or one employee account. You are explaining why identity governance, access review, and privileged access controls did not stop escalation.
Executive takeaway: A standard user account can become a company-wide incident if Active Directory delegation and replication rights are poorly controlled.
What teams should learn from this before a paid pentest
Traditional AD training is slow, expensive, and too abstract. People leave knowing terminology, then struggle to trace how read access becomes write access, or how one delegated permission can lead to full compromise. Hack The Box fixes that by forcing repetition under realistic constraints. Enumerate the environment. Validate the path. Escalate with evidence. Document what happened.
That produces better outcomes for the business. Your internal team finds and fixes obvious escalation paths before the external engagement starts. Your pentest moves faster because the testers are not wasting paid hours on basic hygiene failures. Your report is cleaner, your remediation list is tighter, and your compliance team gets evidence tied to actual control gaps instead of generic advice.
If you want those findings written in a format leadership and auditors can act on, use a clear penetration test report template for security findings and remediation.
Why leadership should care
Domain control is an operations problem with security consequences.
An attacker who controls AD can reset access, move across servers, abuse service accounts, disrupt scheduled tasks, and break trust in the identity layer your company depends on. That means downtime, emergency privilege reviews, forced credential resets, and a harder audit cycle.
HTB is the faster way to prepare for that reality. It costs less than learning during a live engagement, builds skill faster than classroom-only training, and gives your team practice that maps directly to internal pentests, remediation planning, and audit readiness.
Turn Your Skills Into Compliance-Ready Pentest Reports
A lab is only useful if it changes the quality of the penetration test.
That is where most training falls apart. People can run tools. They can solve challenge boxes. Then they freeze when it is time to explain risk to a CISO, an auditor, or a founder who just wants the short version and the fix.
Why reporting skill matters
Hack The Box gets this part right. The Certified Active Directory Pentesting Expert (CAPE) path requires candidates to chain attacks like Kerberos exploits and NTLM relays, then submit a professional report. That mirrors enterprise pentests. The same CAPE material notes that incomplete trust enumeration is a common failure point, that GPP password storage vulnerabilities are found in 75% of legacy AD environments, and that modern EDR blocks over 70% of basic attack payloads, as described in the HTB CAPE path overview.
That combination matters. Testing is not just exploitation. It is method plus evidence plus reporting.
What a compliance-ready report needs
A useful report does three things well:
| Report element | What leadership needs |
|---|---|
| Executive summary | Business impact in plain English |
| Clear findings | What is wrong, how it was validated, why it matters |
| Actionable remediation | Specific fixes your admins can implement |
Most weak reports fail because they are either too technical or too vague. Auditors do not want mystery. Engineers do not want hand-waving.
How HTB improves the paid pen test
When a team has practiced realistic AD penetration testing first, the external engagement gets tighter.
You usually see better outcomes like:
- Cleaner scoping conversations because internal teams know what matters
- Faster validation because obvious AD issues are already understood
- Better remediation planning because attack paths are documented in a way operations can follow
- Stronger audit support because findings map more clearly to actual control gaps
If you want to see what that structure should look like, a strong pentest report template helps set expectations before you buy a penetration test.
Recommendation: Judge a pentest provider by the quality of the report they can produce, not by how dramatic their exploit screenshots look.
The practical business outcome
This is the core reason to care about Hack The Box from a business angle. It shortens the path from “we think our AD is probably okay” to “we can prove where it breaks, fix it, and walk into the formal pen test prepared.”
That saves money in two ways.
First, your team stops wasting external testing hours on beginner mistakes. Second, you reduce the chance of a bad report that creates panic right before a compliance deadline.
For companies chasing SOC 2, PCI DSS, HIPAA, or ISO 27001, that is the difference between a penetration test that checks a box and a penetration test that improves the environment.
Hack The Box is not a substitute for independent validation. It is the smarter way to prepare for it.
If you need a fast, affordable pentest, pen test, or penetration testing report that is built for SOC2, PCI DSS, HIPAA, and real business deadlines, talk to Affordable Pentesting. Their OSCP, CEH, and CREST-certified pentesters deliver clear, actionable reports within a week, so you can fix real issues quickly and move your audit forward. Use the contact form to get started.
.svg)
