You need a penetration test, an audit is coming, and the first quote lands in your inbox like a bad joke. Big price. Slow start. A waiting list that does nothing for your SOC 2, PCI DSS, or HIPAA deadline.
That old model is the problem. Many SMBs and startups still get pushed into bloated penetration testing engagements designed for enterprise procurement, not for teams that need a solid pen test quickly, affordably, and without babysitting the vendor for a month.
A good penetration testing services company should do three things well. It should scope the job correctly, test like a real attacker, and deliver a report your developers and auditors can use. If it can't do that fast, it's wasting your time.
The demand tells the story. The global penetration testing market was valued at about USD 2.45 to 2.74 billion in 2024 to 2025, with projected growth of 11.6 to 18.37% CAGR through 2030, driven by rising threats and compliance pressure like SOC 2 and PCI DSS, according to DeepStrike's 2025 penetration testing statistics. Pen testing isn't a nice extra anymore. It's part of doing business.
Most buyers still make the same mistake. They ask vendors, "How much is a pentest?" before they ask, "What exactly are we testing?"
That's backward.
If you're buying a penetration test for compliance, start with scope. For SOC 2, that often means your internet-facing web app and the systems that support it. For PCI DSS, it means the cardholder data environment. For HIPAA, it means the systems that store, process, or expose ePHI. Keep it simple. Are you testing the whole house, or the doors and windows that matter right now?
Introduction
A pentest is just a controlled attack by people you hired instead of people trying to hurt you. That's the simple version. Good testers look for the same weak points an attacker would look for, then show you what breaks, how bad it is, and how to fix it.
That matters most for SMBs because smaller teams usually have less time, less budget, and less room for security theater. You don't need a giant consulting machine. You need a penetration testing company that can focus on the assets tied to your actual risk and your compliance goal.
Start with the compliance driver
Penetration testing isn't typically purchased due to sudden inspiration. It's acquired because a customer asked for it, an auditor expects it, or leadership finally realized a production web app shouldn't go untested.
Use that pressure productively. Write down the exact reason you need the engagement.
- SOC 2 request: Usually focused on customer-facing applications, authentication flows, and the infrastructure those systems rely on.
- PCI DSS request: Narrow the pen test to the systems that touch card data or support that environment.
- HIPAA request: Focus on applications, databases, portals, and workflows that expose protected health information.
Keep the request short
Don't send a vendor a novel. Send a clean summary.
Include:
- What you're testing: Web app, API, cloud environment, external network, or a defined mix
- Why you're testing: Audit, customer due diligence, release readiness, or recurring security validation
- What matters most: Authentication, payment flow, admin access, file upload, tenant isolation, or sensitive records
- When you need it done: A real deadline, not "ASAP"
A sloppy scope creates a sloppy quote. Then the price rises, the timeline slips, and everyone acts surprised.
You want a pen testing provider that can work from a focused scope and ask smart follow-up questions. If the first response is a giant questionnaire with no practical guidance, that's your first warning sign.
First Steps Define Your Pentest Needs
A founder gets a pentest quote for $4,000 on Monday and $18,000 on Tuesday for what sounds like the same job. The difference usually isn't testing quality. It's scope. One request was clear. The other gave the vendor room to guess, expand, and bill for all of it.
If you want a fast, affordable pentest, lock down what you need before you ask for pricing.

Scope like you mean it
A vague scope gets you a vague quote. Then the timeline stretches, the report arrives late, and your team pays for systems nobody needed tested in the first place.
"We need a pen test for our platform" is a bad request. "We need our production SaaS app, API, login flow, and admin panel tested for SOC 2" is a usable one. SMBs that make this distinction early spend less and get to remediation faster.
Start with five plain questions:
- What system matters right now
- What data would hurt most if exposed
- What environment is in scope
- What deadline is driving this work
- What is explicitly out of scope
That last item saves money. If you do not name exclusions, many vendors will implicitly assume broader coverage.
Match the test to the real requirement
A startup preparing for SOC 2 does not need the same engagement as a company validating a cardholder data environment. Buy the test that fits the requirement in front of you.
For SOC 2, the usual target is the customer-facing app, authentication, access control paths, and the infrastructure that supports them. For PCI DSS, keep the scope tight around systems that store, process, or transmit card data, plus the systems that support that environment. For HIPAA, focus on the applications, databases, APIs, portals, and admin workflows that expose ePHI.
That means you should stop asking for a "full company pentest" unless you truly need one. Early-stage companies rarely do.
A clean scoping note can be short:
- Target assets: Production web application and API
- User roles: Standard user and admin
- Environment: External test of production with authenticated access
- Goal: Audit evidence for SOC 2
- Exclusions: Corporate laptops, internal office network, staging, mobile app
That is enough for a serious vendor to price the work properly and start asking useful follow-up questions.
Kill scope creep before it starts
Scope creep is where affordable pentests go to die.
It usually starts with one extra ask. Test the VPN too. Add the cloud configuration review. Check the mobile app while you're in there. Each add-on changes effort, retest needs, and reporting. Suddenly the "quick audit pentest" turns into a multi-week project with enterprise pricing.
Set a hard rule. If an asset does not affect this audit, this customer request, or this quarter's highest-risk system, leave it out.
Put the exclusions in writing. Make the vendor confirm them in the statement of work. If they keep trying to widen the project without a clear reason, keep shopping. A shortlist of penetration testing companies for startups and SMBs will help you compare firms that already understand smaller scopes and faster timelines.
Ask for the right evidence, not just credentials
Certifications matter, but only as a screening tool. They tell you whether a tester has met a baseline. They do not tell you whether the firm can deliver a focused web app test quickly, write an audit-ready report, and retest fixes without dragging the project out for weeks.
Use credentials to filter obvious weak options:
- OSCP: Good signal for hands-on exploitation skill
- CEH: Broad security knowledge, but not proof of strong application testing
- CREST: Recognized by many buyers and compliance teams
If a provider has no meaningful certifications, drop them. If they have the letters but cannot explain how they will test your app, drop them faster.
Questions that expose weak vendors fast
Skip the generic sales call. Ask direct questions that force direct answers.
- Who will do the testing? Ask for named testers or, at minimum, their role level and certifications.
- How much of the work is manual? A real pentest includes manual validation and exploitation, not scanner exports dressed up as findings.
- What assets are included in this price? Get the exact hosts, apps, APIs, and user roles in writing.
- How fast do you deliver the report? Long delays are common. They are also avoidable.
- Is retesting included? Many SMBs need proof that fixes were validated.
- Will the report be usable for auditors and customers? Your developers need technical detail. Your auditor needs a clear summary.
These questions also help with answering security questionnaires effectively, because they force you to document scope, ownership, testing method, and remediation workflow before a prospect or auditor asks.
Send an intake email that gets a real quote
Your first email should be short enough to read in one minute and specific enough to price without guesswork.
We need a penetration test for our production SaaS web app and API for SOC 2 evidence. Please quote external authenticated testing for standard-user and admin roles. Include testing methodology, report delivery timeline, retesting options, and tester certifications. Exclude internal corporate systems, staging, and mobile applications.
That message does two things. It cuts down the sales back-and-forth, and it exposes vendors that depend on ambiguity to inflate the price.
How to Evaluate a Penetration Testing Company
A polished sales process is easy to fake. A good pentest is not.
Once you have a defined scope, your job is to screen out vendors that sell speed, then deliver delays. Screen out firms that call scanner output a penetration test. Screen out providers that charge enterprise rates for SMB work.
Three things decide whether a vendor is worth hiring. Who does the testing, how they test, and whether the report is usable.
Check whether they know how to test applications, not just scan them
For most startups and SMBs, the app is the business. That is where customer data lives, where auth breaks, and where attackers get value fastest.
As noted earlier, web application flaws show up constantly in breach cases. Good testers know that. Weak vendors still lead with generic infrastructure scans because they are easier to sell and easier to automate.
Ask how they test authenticated user flows, privilege changes, account recovery, role separation, API authorization, and business logic abuse. If they cannot explain those areas in plain English, they are not the right fit.
| What to ask | Good answer | Bad answer |
|---|---|---|
| How do you test web apps | They explain recon, authenticated testing, manual exploitation, and business logic review | They mostly describe automated scanning |
| How do you handle APIs | They ask for docs, auth flows, roles, and high-risk endpoints | They say APIs are covered automatically |
| How do you validate findings | They confirm exploitability before reporting it | They paste raw tool output into the report |
Examine the methodology, then strip out the marketing language
A real pentest follows a clear sequence. Recon. Targeted scanning. Manual exploitation. Privilege testing where relevant. Reporting with evidence and remediation.
That process matters because tools do not produce judgment. Testers do. Burp, Nmap, Nessus, and Metasploit are useful only when a capable human knows what to probe, what to chain together, and what to ignore.
Vendors love vague phrases like "AI-assisted testing" and "hybrid assessment platform." Ignore the label. Ask a simpler question: what does the tester do by hand, and what gets verified before it lands in the report? If the answer is fuzzy, keep looking.
Read a sample report before you sign anything
This step saves money.
A strong report does four jobs. It shows what was found, proves it was validated, explains the business impact, and gives your team clear remediation steps. It should also hold up when an auditor, prospect, or procurement team asks for evidence.
Look for:
- Severity with reasoning: Why the issue matters, not just a label
- Clear impact: A non-security stakeholder should understand the risk
- Technical proof: Enough detail for engineers to reproduce and fix
- Actionable remediation: Specific guidance tied to the actual issue
- Useful summary: Short, readable, and appropriate for audits
If the report creates more confusion than action, you paid for activity, not value.
Price is a signal. It is not proof.
Expensive vendors often bundle in layers of project management, long timelines, and unnecessary ceremony. Cheap vendors often plan to scan, template the results, and move on. Both can waste your budget.
Instead of asking "Who is cheapest?", ask "Who provides competent manual testing without enterprise bloat?"
That is the standard SMB buyers should use. You need fast scheduling, clear scope, direct access to the people doing the work, and reports that are ready for customers and auditors without a month of cleanup. If you want a sense of how service models differ, this comparison of best penetration testing companies is a useful shortcut.
Ask direct questions and expect direct answers
Use your first call to pressure-test the vendor, not to sit through a pitch.
- Who will perform the test, and what is their hands-on experience
- How much of the engagement is manual testing
- Do you test business logic, authorization, and role-based access issues
- How quickly do you deliver draft findings and the final report
- Is remediation validation or retesting included
- Can the final report support compliance evidence without filler
- Who answers questions during the engagement
Strong firms answer clearly and quickly. Weak firms hide behind process, jargon, and account managers.
Pentest vendors are not the only ones that need to communicate well. If your team also has to respond to customer security reviews, this guide to answering security questionnaires effectively is worth reading because buyers often ask for both a pentest report and clear written security responses.
What to Expect for Penetration Testing Prices
Pricing frustrates buyers because too many vendors act like cost is some sacred mystery. It isn't. A penetration test costs more when the scope is messy, the environment is complex, or the provider layers on unnecessary overhead.
SMBs should stop accepting enterprise pricing logic for SMB problems.

The numbers buyers should know
A 2025 Gartner report, cited by Defendify, notes that SMBs often spend 40 to 60% less on pentests than enterprises, with typical SMB spend at $5K to $20K versus $50K+ for enterprises. The same source notes that PTaaS can be 30 to 50% lower in annual cost than one-off tests for SMBs that need SOC 2 or PCI support. You can review that breakdown in Defendify's look at penetration testing companies and pricing gaps.
Those numbers match what many buyers already suspect. Enterprise firms often charge for procurement friction, layers of management, and long process chains that don't improve the actual test.
What actually drives the quote
A fair quote usually depends on a few things:
- Application size: More features, roles, and attack paths mean more work
- Authentication complexity: SSO, role separation, and multi-step workflows take time to validate
- API depth: More endpoints and more sensitive actions require more manual review
- Environment sprawl: Extra hosts, extra apps, and unclear boundaries raise cost fast
- Retesting needs: Validation after fixes should be planned from the start
What shouldn't drive the price is your logo size. A startup with a messy multi-role app can need more work than a larger company with one simple portal.
A sane engagement should feel like this
You send a focused scope. The vendor asks a few smart questions. They confirm the rules of engagement, line up access, and start quickly.
During the test, communication stays simple. You know who is testing, what they need, and when to expect the report. There isn't a parade of status meetings pretending to be value.
The final deliverable arrives fast enough that your team can fix issues while the test is still fresh in everyone's mind. That's how cost stays under control. Delay creates rework.
Don't ignore the contract terms
A lot of pentest headaches aren't technical. They're contractual.
Before you sign, check the scope language, deliverables, retest terms, and timeline commitments. If you want a quick refresher on what belongs in a legally binding contract for services, that overview helps non-lawyers spot the basics.
For a more direct look at budgeting, this breakdown of the cost of penetration testing is useful when you're comparing one-time assessments against ongoing testing options.
One mention worth making
Some providers now package manual work with lightweight automation so buyers aren't paying humans to do repetitive triage. For example, Affordable Pentesting offers manual penetration testing for compliance-focused SMB use cases and also lists automated and AI-driven network assessments plus API pentests with defined starting points. That kind of narrower service design is often more practical for startups than a giant consulting engagement.
Buyers don't need mystery pricing. They need scoping discipline, clear deliverables, and a provider that doesn't bill like a law firm.
The Fast Penetration Test Process You Deserve
A good pentest shouldn't feel like a slow-moving consulting project. It should feel like focused security work with a beginning, a middle, and a useful end.
The process below is what buyers should expect when a penetration testing company respects your deadline.
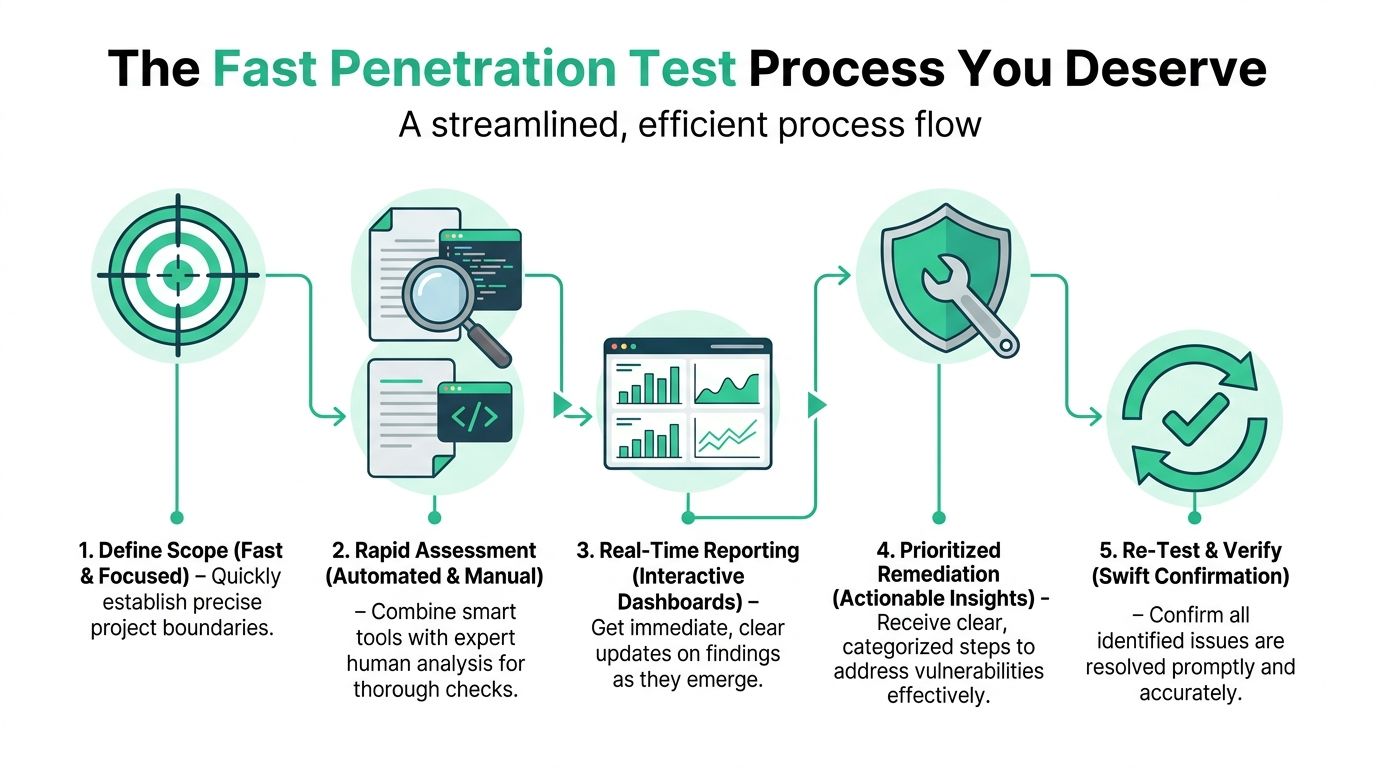
Kickoff should be short
The kickoff call is not the place for theater. It should confirm scope, access, test windows, contacts, and any guardrails around sensitive systems.
If a vendor needs endless meetings to start, that's not thoroughness. That's drag.
Testing should blend tools and judgment
Real pentesting combines automation with manual work. Tools help find the obvious faster. Humans test the parts that scanners miss, especially auth flaws, broken permissions, business logic issues, and exploit chains.
Data from Vaadata shows a structured methodology typically uncovers an average of 1.3 important and 0.7 critical vulnerabilities per target, and that kind of value depends on a real process, not just a scan dump. Vaadata's analysis also makes the practical point that faster reporting lets development teams start fixing problems right away, which you can review in their write-up on frequent pentest vulnerabilities and methodology.
You should not wait forever for results
Long delays are one of the worst habits in this industry. Teams forget context. Release schedules move. Audit timelines tighten. Then the report arrives too late to be useful.
What you want is rapid communication during the engagement and a final report within about a week of the testing window, especially for a focused SMB web app or API assessment. That isn't unrealistic. It's basic operational competence.
A fast process usually looks like this:
- Scope confirmed quickly: Targets, roles, and timelines are locked
- Testing begins without drama: Access is ready and the tester gets to work
- Important findings surface early: Critical issues don't wait for the final PDF
- Report lands while fixes are still fresh: Engineering can act immediately
- Retest closes the loop: The provider verifies what was fixed
The report should help two audiences
Developers need exact remediation steps. Auditors need evidence the testing happened, what was found, and how it was resolved. One report should serve both.
That means a good report includes:
- Plain-language summary: What matters and why
- Technical details: Enough for reproduction and repair
- Proof of validation: Evidence that the issue was real
- Remediation priority: What to fix first
- Retest path: What happens after the fixes ship
Fast doesn't mean rushed. It means the vendor knows how to scope tightly, test efficiently, and write clearly.
Retesting is part of the job
A penetration test is not complete when the PDF is delivered. It's complete when the important issues are fixed and verified.
That final step matters because teams often patch the obvious symptom but miss the deeper access path. Good providers retest the exact findings they reported and confirm whether the risk is closed.
After the Report Validating Fixes and Retesting
A lot of penetration testing companies act like the job ends when they send the report. That's lazy. The ultimate finish line is validation.
You found the problems. Good. Now prove the fixes work.
That matters for compliance and for reality. A 2026 Verizon DBIR report, cited by UnderDefense, showed that 52% of SMBs fail audits due to unverified remediations. The same source notes that free re-tests are a major differentiator and that boutique firms reporting dashboard-tracked re-tests have seen 90% client retention. You can review that discussion in UnderDefense's page on penetration testing services and fix verification.
What good retesting looks like
Retesting should be simple. Your team fixes the issue, shares what changed, and the tester verifies the original exploit path no longer works.
That process should not turn into a second full-price engagement unless the scope changed dramatically. For the original findings, validation should be part of the expected service.
Questions to settle before the test starts
Buyers should ask these early, not after the report lands:
- How do we submit fixes for validation
- What is included in the retest
- How quickly can you verify remediated findings
- Will the final status be documented for auditors
- Do you charge extra for verifying the original issues
If a vendor gets slippery here, expect pain later.
Why this is where value shows up
The cheapest-looking pentest can become the most expensive one if you have to chase the tester, pay for a second engagement, or explain to an auditor why the fixes were never confirmed.
The best outcomes come from a simple chain. Tight scope. Real manual testing. Fast report. Clear remediation. Then verification. That's the model buyers should demand.
If you want a practical view of what fixing common findings looks like, this guide to remediation of vulnerabilities is a useful next read.
Conclusion
Most SMBs don't need a giant security consultancy. They need a penetration testing services company that respects scope, moves quickly, and does real manual work.
The smart path is simple. Define the exact assets tied to your compliance or business risk. Vet the vendor's certifications, methodology, and report quality. Push for pricing that matches the application, not your company size. Expect a clean process and a report that lands fast enough to matter. And don't accept a pentest that ends before fixes are verified.
The market is full of noise. Enterprise branding. Inflated timelines. Reports padded with scanner clutter. You don't have to buy that model.
A good pen test should help you make decisions. It should tell your developers what to fix, tell your auditor what was tested, and tell leadership whether the current risk is acceptable. These outcomes define its value.
If you're a founder, IT manager, CISO, or compliance lead who is tired of paying too much for slow penetration testing, raise your standard. Ask sharper questions. Demand a faster process. Insist on retesting.
Then use a contact form and get a quote from a team that can deliver the work without the usual nonsense.
If you need fast, affordable, audit-ready testing from certified ethical hackers, contact Affordable Pentesting through their contact form and request a quote for your web app, API, or compliance-focused penetration test.
.svg)