Red Team Assessment Fast Actionable Insights
You’re probably here because a compliance deadline is closing in, your leadership wants “real security testing,” and the quotes you’re getting feel absurd. Weeks of meetings. Scope documents that read like legal contracts. Then a giant price tag for a report nobody wants to read.
That model is broken for startups and SMBs.
A red team assessment can give you real answers, but only if you treat it like a business decision, not a prestige purchase. The point isn’t to buy the fanciest engagement. The point is to test whether an attacker can reach something you care about, then get clear evidence your team can act on fast.
What Is A Red Team Assessment Really
A red team assessment is a simulated real-world attack against your company. Not just your firewall. Not just your web app. Your people, your process, your cloud setup, your endpoints, and the way your team responds when something starts going wrong.
Consider it a process of employing professional operatives to challenge your fortress. A standard evaluation might inquire, "Is the side door accessible?" A red team investigates, "Can we penetrate the perimeter, evade security, navigate through the interior, and seize the crown without being detected or halted?"
That difference matters.
A lot of IT managers ask for a penetration test because that’s the term they know. Sometimes that’s exactly the right choice. But when your real question is “Could someone reach customer data?” or “Would our team catch a targeted attack?” a basic pen test won’t answer it.
What It Tests In Real Life
A red team assessment looks at security the way an attacker does. It doesn’t care which department owns the problem. It cares whether separate weaknesses can be chained together into one successful attack path.
That can include things like:
- Public information gathering from your website, job posts, and employee profiles
- Social engineering to see whether staff trust the wrong message
- External access attempts against internet-facing systems
- Internal movement after a small foothold is gained
- Objective-driven actions such as reaching sensitive records or privileged accounts
That’s why this type of work feels more real than a checkbox exercise. It follows the path an actual attacker would take instead of stopping after a list of technical findings.
Practical rule: If leadership cares about business impact, test business impact. Don’t settle for a report that only proves a scanner can spot known flaws.
Why SMBs Need A Practical Version
Traditional consulting firms tend to treat red teaming like an enterprise theater production. Endless planning. Bloated overhead. Slow delivery. That may fit a massive bank with layers of committees. It doesn’t fit a startup trying to close a customer, pass a review, or harden a lean environment without wasting a quarter.
A smaller company usually needs a narrower, sharper question answered. Can someone get into finance systems? Can someone abuse weak identity controls? Can someone access regulated data through a realistic chain of mistakes?
That is where a well-scoped red team assessment becomes useful. It cuts through generic “security maturity” talk and shows what’s possible in your environment.
What Good Looks Like
Good red teaming is controlled. It isn’t chaos. You define the target, the rules, the limits, and the success conditions before anyone touches a system.
A useful engagement gives you three things:
- A believable attack story that shows how the team got in
- Clear evidence of weak controls across people, process, or technology
- A remediation path your IT and security team can execute without translation
If you don’t get those three things, you bought stress, not insight.
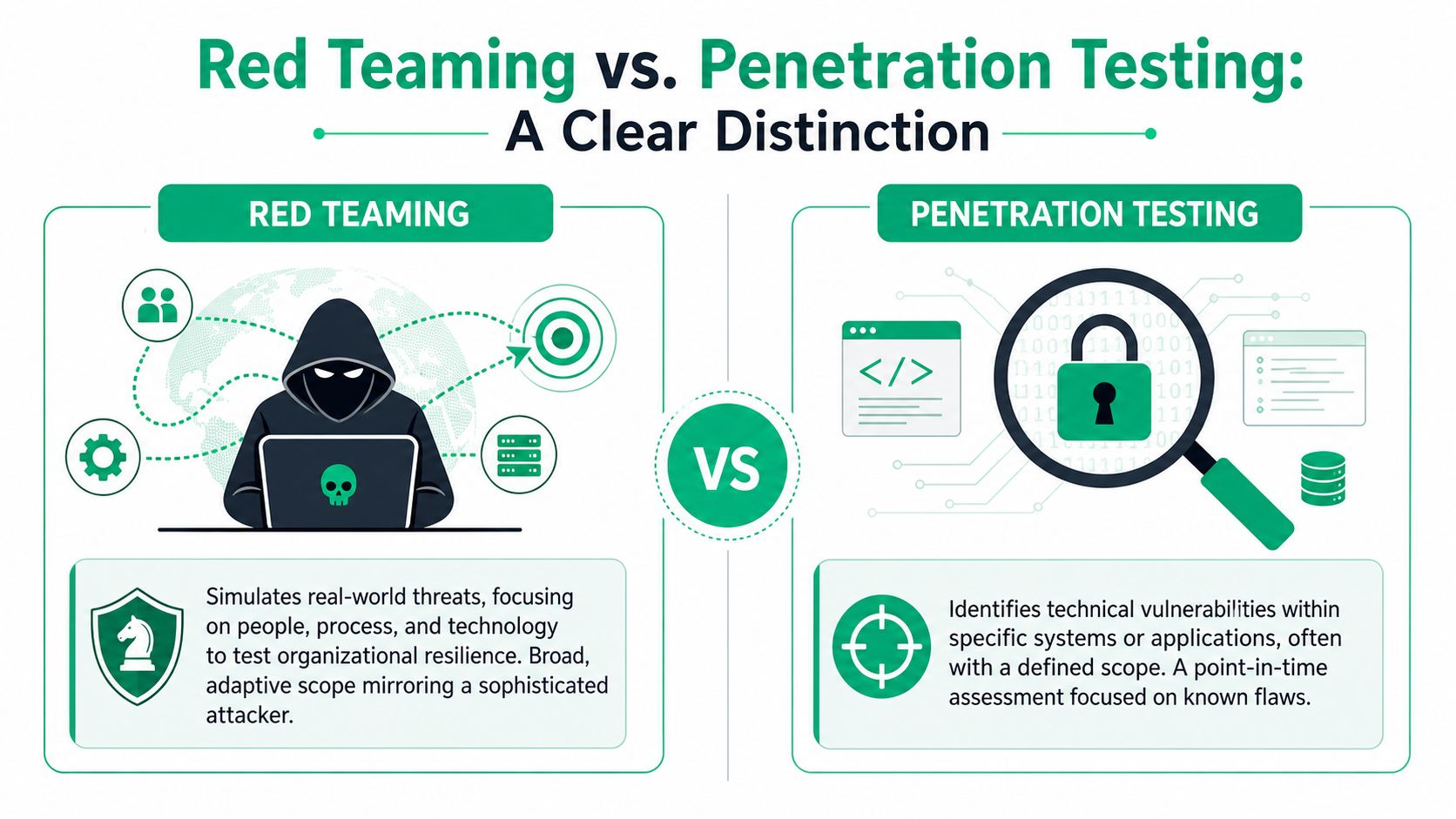
Red Teaming Is Not A Penetration Test
Buyers often get tripped up. Vendors blur the line because “red team” sounds more advanced and sells better. But a penetration test, a pen test, and a red team assessment are not the same thing.
A penetration test usually asks, “What vulnerabilities exist in this app, network, or environment?” A red team assessment asks, “Can we achieve a real objective using any approved path available to us?”
That’s a big gap.
The Simple Way To Tell Them Apart
A vulnerability scan is mostly automated. It checks for known issues. Helpful, but shallow.
A penetration test is manual and targeted. It proves whether specific weaknesses can be exploited in a defined scope.
A red team assessment is objective-driven. It simulates a realistic adversary trying to reach a meaningful outcome while avoiding detection.
Here’s the clean comparison.
| Attribute | Vulnerability Scan | Penetration Test | Red Team Assessment |
|---|---|---|---|
| Main purpose | Find known weaknesses fast | Validate exploitable security flaws | Test whether a realistic attacker can achieve a business objective |
| Scope style | Broad but shallow | Defined systems or applications | Broad and adaptive within approved rules |
| Testing method | Mostly automated | Manual plus supporting tools | Manual, adaptive, and campaign-based |
| Focus area | Technical exposures | Technical weaknesses and exploitability | People, process, and technology together |
| Output | List of detected issues | Verified findings with risk and remediation | Attack narrative, control failures, and resilience gaps |
| Best fit | Routine hygiene | Compliance and system-level assurance | Real-world readiness and incident response testing |
The Castle Analogy Works
Use this to explain it to leadership.
- Vulnerability scan checks whether doors and windows are obviously broken
- Penetration testing tries the locks and shows which doors can be opened
- Red teaming tries to steal the crown without the guards noticing
That’s why buyers who only need a web application penetration test shouldn’t buy a red team engagement. And buyers who need to know whether their defenses work under pressure shouldn’t pretend a basic pentest is enough.
Time And Scope Are Different
Red teaming is also slower by design. Red team assessments typically require a minimum timeline of 4 weeks for engagements targeting a single goal, which is longer than standard penetration tests because the work involves operational security, discovery of attack paths, and methods to bypass defenses, as described in Schellman’s red team methodology overview.
That doesn’t mean every company should jump straight to red teaming. It means you should stop expecting a full adversary simulation from a cheap one-week penetration test. Those are different services.
Where Blue Teams And Purple Teams Fit
A blue team is your defense side. They monitor, investigate, and respond.
A purple team is what happens when offense and defense work together during or after testing so the defenders learn faster. If your security program is still young, purple teaming can sometimes create more value than a stealth-heavy red team because your staff sees the attack path and learns how to detect it.
If you want a deeper side-by-side breakdown, read this guide on red teaming vs pentesting.
If a vendor can’t explain the difference between a vulnerability scan, a penetration test, and a red team assessment in plain English, don’t trust them with your budget.
How A Real Red Team Engagement Works
A real red team engagement isn’t random. It follows a mission plan. The team doesn’t just poke around and hope to trip over something interesting.
A thorough evaluation often uses frameworks such as MITRE ATT&CK to assess technical and administrative controls, and it can span 9 phases from planning to reporting. That structure is one reason red teaming works well in finance, healthcare, and tech environments where the details matter.

The Mission Starts Before The Attack
The best engagements begin with planning, not exploits. The client and red team define the target objective, the approved methods, the protected systems, the emergency contacts, and the exact conditions for stopping if risk gets too high.
That’s what keeps the work useful instead of reckless.
A serious team also makes sure the people doing the work know how to operate carefully. For buyers, that means asking whether the testers hold certifications such as OSCP, CEH, and CREST. Certifications don’t guarantee quality, but they do signal that the people running your assessment have been tested on real skills and recognized standards.
Recon Finds The First Cracks
Reconnaissance is simple to explain. The team gathers information before it tries to get in.
They’ll look at your public footprint. Employee names, technology clues in job listings, exposed portals, forgotten subdomains, vendor relationships, and anything else that helps map the attack surface. None of that feels dramatic, but it is through such details that smart attacks get their edge.
A lot of companies leak useful context without realizing it. The problem isn’t one bad post or one exposed page. The problem is what an attacker can build when they combine small clues.
Initial Access Is Usually Boring
Most compromises don’t start with movie-hacker magic. They start with something ordinary that works.
That might be a misconfiguration, weak identity setup, exposed service, or a convincing message sent to the right person. The red team is looking for the easiest approved path that can create a foothold.
This is why leadership should stop asking, “Did you find critical CVEs?” and start asking, “What was the first believable path in?”
Movement Inside Reveals The Real Risk
Once the team gets in, the exercise becomes far more valuable. Internal movement shows whether one mistake can turn into a larger failure.
Typical goals in this stage include:
- Persistence: Can the team maintain access long enough to continue the scenario?
- Privilege escalation: Can a low-level foothold become higher-value access?
- Lateral movement: Can the team move from one system or account to another?
- Objective completion: Can they reach the stated target without detection stopping them?
Weak segmentation, poor identity hygiene, and over-trusted internal systems begin to surface.
A lot of companies are shocked by the first access point. They should be more worried about what happened after that.
Good Red Teaming Looks Controlled
People hear “simulate an attacker” and assume the process is messy. It shouldn’t be. Strong operators document what they do, preserve evidence, avoid unnecessary disruption, and clean up after the engagement.
That discipline matters as much as technical skill.
A solid engagement usually has these visible traits:
- A clear objective tied to business risk
- Defined rules of engagement so testing stays safe
- Documented attack paths instead of vague summaries
- Debrief sessions where your team can ask direct questions
- Actionable remediation guidance instead of generic advice
The process can feel complex, but the output should feel simple. Here’s how they got in. Here’s what they reached. Here’s why your controls missed it. Here’s what to fix first.
Setting The Goals For Your Red Team
If you don’t set a clear goal, you’ll get a vague result. That’s the fastest way to waste money on a red team assessment.
The scope should answer a business question your leadership cares about. Not “test security.” That means nothing. A useful objective sounds more like, “Can an attacker reach protected health information?” or “Can someone compromise a finance workflow and avoid detection long enough to do damage?”

Start With Business Risk
Your red team goal should map to one of three things:
- Sensitive data such as customer records, payment data, or internal IP
- Critical systems such as production apps, cloud admin roles, or identity platforms
- Response capability such as whether your team can detect and contain a realistic attack
That’s how you turn a technical exercise into something that matters to compliance, insurance discussions, and leadership decisions.
A broad “see what you find” scope sounds flexible, but it usually creates noise. A better engagement starts with a target that matters and a boundary that keeps the work efficient.
Rules Of Engagement Matter More Than People Think
Rules of engagement are just the ground rules. They define what’s allowed, what’s off-limits, who gets notified in an emergency, and what counts as success.
That can include things like approved social engineering methods, whether production systems can be touched, whether after-hours testing is allowed, and which executive accounts are excluded. Without that clarity, even a skilled team can create unnecessary risk.
The human side belongs in scope too. In red team assessments, the human element is a primary target, and testing employee awareness matters because human error is the root cause in 74% of all data breaches, according to SecureLayer7’s red team assessment overview.
Good Goals Are Specific
These are useful examples for SMBs and startups:
- HIPAA-focused question: Can an attacker reach systems tied to protected health information through a realistic chain of user and technical failures?
- SOC 2-focused question: Can an attacker disrupt a key workflow and expose whether monitoring and response controls function as intended?
- Cloud-focused question: Can someone pivot from a weak user account into higher-value cloud access?
- Executive-risk question: Can an attacker compromise a high-value mailbox or identity account using approved social engineering tactics?
Those goals are concrete. They produce evidence your team can defend in front of auditors, customers, and leadership.
Scope advice: Test one painful question well. Don’t test ten questions badly.
Training Matters Too
Some companies use a red team assessment to expose weak awareness and then realize the root problem is a skills gap on the internal side. That’s common in cloud-heavy teams where engineers own a lot of security responsibility whether they want to or not.
If your team needs a stronger baseline on cloud security concepts before or after a red team exercise, this AWS security certification prep guide is a practical resource. It won’t replace testing, but it can help your staff understand the controls and failure points attackers often target in cloud environments.
The point is simple. A red team assessment works best when the objective is narrow, the rules are clear, and the result ties back to a real business concern.
Getting A Report You Can Actually Use
Most red team reports fail for one reason. They’re written for the consulting firm, not for the client.
You wait forever, then get a bloated PDF packed with screenshots, jargon, and filler. Leadership can’t tell what happened. Engineers can’t tell what to fix first. The whole thing lands with a thud.
A useful report should read like a case file. It should tell the story of the attack from first move to final objective, in plain language, with evidence attached.

The Best Reports Tell A Story
A strong red team report answers these questions fast:
- How did the team get in
- What controls failed
- How far did they move
- What business asset was at risk
- What should be fixed first
That structure matters because different people read the same report for different reasons. Executives want impact. Security leads want control gaps. System owners want remediation steps. If the report doesn’t support all three, it becomes shelfware.
Clarity Beats Length
Longer is not better. Better is better.
A solid report usually includes:
| Report section | What it should do |
|---|---|
| Executive summary | Explain the business outcome and why it matters |
| Attack narrative | Show the path from recon to objective in plain English |
| Technical findings | Document the weaknesses that enabled progress |
| Evidence | Provide screenshots, timestamps, and proof of access |
| Remediation guidance | Give practical steps in the right order |
| Debrief notes | Capture questions, context, and next actions |
If you want to see what a more practical deliverable looks like, this pentest report template guide is a useful benchmark for evaluating whether a vendor’s reporting style will help your team.
Fast Reporting Changes The Value
A report that shows up quickly is more useful because the environment is still fresh in everyone’s mind. The affected owners remember what changed. Security staff remember the alerts they saw or missed. Leadership still cares because the engagement hasn’t faded into the background.
That speed changes follow-through.
The best debriefs are direct. The testers walk through the path, answer uncomfortable questions, and explain what to fix now versus later. No theater. No hiding behind jargon. Just evidence and priority.
You’re not paying for a document. You’re paying for a clear explanation of risk your team can act on immediately.
What To Reject Immediately
Walk away from reports that do any of the following:
- Dump raw scanner output with little human analysis
- Bury the objective under pages of generic boilerplate
- Avoid plain language because the writers want to sound impressive
- Skip remediation order and leave your team guessing
- Arrive too late to support real operational change
A red team assessment should end with clarity. Your team should know what happened, why it mattered, and what gets fixed first. If the report can’t do that, the engagement didn’t finish the job.
How To Find Affordable Red Team Services
Red team services are expensive for two very different reasons. One reason is valid. Skilled operators are hard to find. The other reason is nonsense. A lot of firms carry heavy sales overhead, slow project management, and layers of process that add cost without adding insight.
You don’t need to pay for someone’s marble lobby and six-step discovery cycle.
SMBs and startups should buy red teaming the same way they buy any other technical service. Focus on operator quality, scope discipline, reporting quality, and turnaround. Ignore the theater.
Why Traditional Firms Cost So Much
Big consulting firms often build cost into the wrong places:
- Large sales teams that require multiple calls before a quote appears
- Heavy project layers where too many people touch the engagement
- Generic processes designed for giant enterprises, not lean teams
- Slow report cycles that burn time after the testing is already done
That doesn’t automatically make them bad. It just makes them a poor fit for many smaller companies that need direct answers fast.
What Smart Buyers Check First
Use this checklist before you sign anything:
- Operator credentials: Ask whether the people doing the work hold certifications such as OSCP, CEH, or CREST.
- Actual scope fit: Ask what business objective they would test in your environment, not just what package they sell.
- Report delivery time: Ask how fast you’ll get the report and whether there’s a live debrief.
- Manual testing depth: Ask how much of the work is manual versus automated.
- Communication style: Ask who you’ll talk to during the engagement when questions come up.
- Pricing clarity: Ask whether the proposal is fixed and transparent or likely to expand after more meetings.
A vendor that dodges simple questions will usually be painful once the project starts.
Cheap And Affordable Are Not The Same
Cheap security testing often means shallow testing. You get a templated report, weak validation, and findings that don’t tell a coherent story.
Affordable is different. Affordable means the provider cuts waste, not skill.
That usually looks like:
- Tighter scoping
- Certified pentesters doing the actual work
- Shorter sales cycles
- Faster reporting
- Less bureaucracy between test and result
If you’re comparing options, this guide on how to choose a penetration testing vendor gives a practical lens for separating serious providers from firms that mostly sell process.
The Questions Worth Asking On The First Call
Don’t ask vague questions like “How do you approach security?”
Ask these instead:
- What objective would you recommend for our environment and why
- Who performs the testing and what certifications do they hold
- How do you keep testing safe in production
- What will the final report look like
- How quickly do we get findings after the engagement
Those questions force a real answer. You’ll learn more in ten minutes than you will from a polished slide deck.
Your Top Red Team Assessment Questions Answered
Do I need a red team assessment for SOC 2
Not always. A standard penetration test may be enough for your immediate requirement, depending on your environment and what your auditor expects. A red team assessment is better when you need to validate whether controls hold up against a realistic attack path, especially around detection and response.
What if the red team doesn’t succeed
That’s a good result. It means the approved attack path didn’t reach the objective under the conditions you set. You still learn a lot from the attempts, the blocked paths, and the control checks that worked.
What’s the difference between red team and purple team
A red team acts like the attacker. A purple team is more collaborative and helps defenders learn during the exercise. If your internal team needs hands-on improvement in detection, response, and tuning, purple teaming can be a very practical next step.
Should startups do red teaming or just penetration testing
Most startups should start with penetration testing unless they have a specific high-risk scenario they need to validate. If you already know the business question and it involves people, process, and technology together, red teaming makes sense. If you still need baseline validation on an app, API, cloud setup, or external perimeter, start with a pentest.
Will a red team assessment disrupt production
It shouldn’t if the scope and rules of engagement are set properly. A professional team works within agreed boundaries, avoids unnecessary impact, and coordinates for safety. That’s why planning matters so much.
How do I know if a vendor is serious
Ask who will do the work, how they scope the engagement, what the report looks like, and how fast they deliver results. If the answers are fuzzy, the engagement will be too.
If you need security testing that’s practical, fast, and priced for practical situations, Affordable Pentesting is worth contacting through their form. They focus on affordable penetration testing and red team style assessments for startups and SMBs, use certified pentesters with credentials like OSCP, CEH, and CREST, and keep the process focused on useful findings instead of slow consulting theater.
.svg)
