For years, security has been a frustrating cycle: attackers (the red team) work in secret, while defenders (the blue team) try to catch them, often after it's too late. This old approach is slow, expensive, and often finds nothing. Purple teaming changes the game.
Purple teaming is a collaborative exercise where your attackers and defenders work together in real-time. Instead of a secret attack, it's a live training session where both sides communicate to find and fix security gaps on the spot. This makes your team stronger, faster, and proves your security is actually working.
How Does a Purple Team Exercise Work?

Let's cut through the jargon. Purple teaming isn't a new team; it's a smart strategy where attackers and defenders talk. It's a powerful alternative to a traditional penetration test, which often leaves you waiting weeks for a report with few useful findings.
The process is straightforward. An external red team of certified pentesters runs a simulated attack. Your internal blue team works to detect it. The key difference? They talk to each other the whole time.
For example, the red team says, "I'm attempting this specific attack right now." Your blue team immediately checks if your security tools fired an alert. If not, you know exactly what to fix and can test the fix moments later. This constant feedback loop provides immediate security improvements.
Red vs. Blue vs. Purple Teams
To understand purple teaming's value, you need to see how it stacks up against old-school red and blue teams. The old way creates a standoff, while the new way builds teamwork and delivers fast results.
| Aspect | Red Team (Attackers) | Blue Team (Defenders) | Purple Teaming (Collaboration) |
|---|---|---|---|
| Primary Goal | Find vulnerabilities without getting caught. | Detect and respond to threats. | Improve detection and response through open collaboration. |
| Methods | Simulates real-world attacker techniques. | Monitors networks and configures security tools. | Red team executes attacks openly; blue team validates detections. |
| Communication | Minimal. Operates in secret to test stealth. | Internal communication for incident response. | Continuous and open communication between both teams. |
| Outcome | A final report listing vulnerabilities, delivered weeks later. | Improved security posture and response plans. | Immediate feedback, on-the-spot tool tuning, and team training. |
Purple teaming combines the best of both worlds: the red team's offensive mindset and the blue team's defensive posture. It's a single, high-impact training exercise that provides far more value than a traditional penetration test.
Why Purple Teaming Beats Old-School Pentesting
For IT managers, CISOs, and startup founders, the value is clear. You aren't just getting a list of problems weeks after a pen test is over. You are actively training your team and validating your expensive security tools with immediate results.
Instead of waiting for a slow, expensive report, you get actionable insights fast. Our approach focuses on affordability and speed, delivering comprehensive reports from our OSCP, CEH, and CREST certified pentesters, often within a week. If you need to validate your defenses quickly, fill out our form to get started with purple teaming.
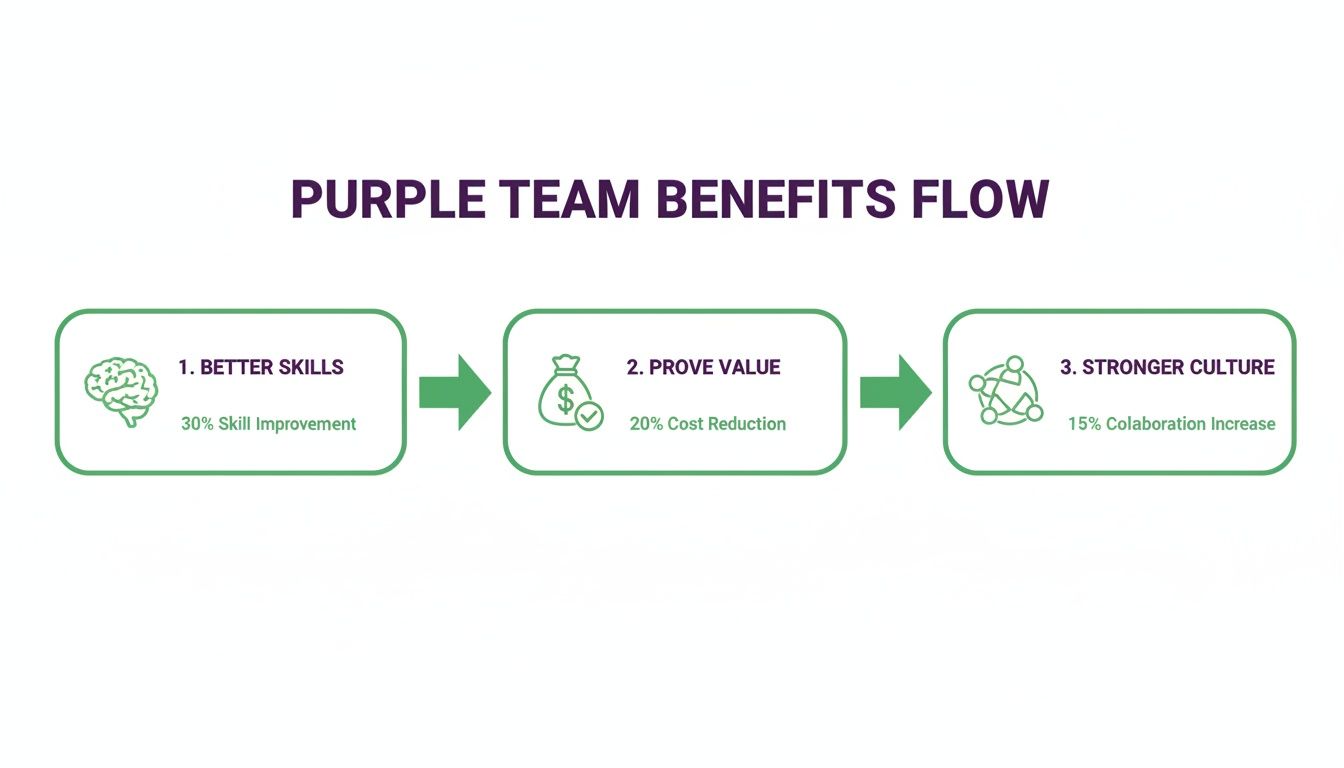
The Core Benefits of a Purple Team
Forget the traditional pen test model where you wait weeks for a report that might not find anything. A purple team exercise shifts your security from a guessing game to a validated, battle-tested defense. You get immediate, measurable improvements.
The biggest win is for your blue team—the people defending your network. They get live, hands-on training against real attack techniques. This isn't a theoretical exercise; it's a live scrimmage that sharpens their ability to spot and shut down threats fast. This direct feedback has been shown to reduce vulnerability exploitation rates by up to 30-50% in later assessments.
Prove Your Security Spending Actually Works
Purple teaming gives CISOs undeniable proof that expensive security tools are configured correctly and doing their job. It's one thing to buy a new security platform; it's another to know it will fire an alert when a real threat appears. These exercises put your technology to the test.
A purple team exercise turns your security budget from a recurring expense into a proven defense. You get hard data to show leadership that your security is getting stronger. Instead of just saying you have security tools, you can show evidence that those tools stopped a simulated ransomware attack.
The Purple Team Exercise Process Explained
So, what does a purple team exercise actually look like? It's a structured, collaborative session designed for rapid improvement. Think of it less like a long, secretive penetration test and more like a series of fast training rounds.
The entire exercise is built on an open-book philosophy. The goal isn't for attackers to "win" by staying hidden. The real win is for your defenders to see attacks unfold in real-time, ask questions, and get better on the spot.
The Live Execution and Detection Cycle
This is where the action happens. The red team executes a pre-planned attack while openly communicating each step. They might announce, "Okay, we are now attempting a phishing attack with a malicious macro."
Your blue team then jumps into action, using their security tools to hunt for the activity. The central question is simple but powerful: "Did we see that?" This collaborative approach improves skills, proves security's value, and builds a much stronger security culture.
This cycle of attacking and defending, based on frameworks like MITRE ATT&CK, provides a clear path to improving your overall security. Dig deeper into how this practice strengthens security on Rapid7.com.
The Immediate Debrief and Improvement Loop
The final step is the most important. Right after an attack, both teams huddle up for an immediate debrief. They analyze what happened, whether defenses worked, and what needs to be improved.
If your tools missed the attack, it's a golden learning opportunity. The teams work together, right then and there, to tune a detection rule or update a response playbook. The red team might even re-run the same attack to validate the new defense works.
This "test, detect, fix, re-test" cycle delivers real results in hours, not weeks. It's a world away from traditional penetration testing. For more on the offensive side of this, check out what is red team testing. Our affordable manual pentests provide the expert red team you need, with results within a week.
How to Build a Purple Team Affordably
Thinking about purple teaming probably brings to mind huge budgets and expensive security departments. That's a myth. You don't need a massive investment or a new team to get started. The secret is having access to both offensive (red team) and defensive (blue team) skills.
Your internal IT staff is already your best blue team. The real challenge is finding specialized offensive expertise for a realistic red team. This is where an affordable penetration testing partner becomes your best asset.
It Is a Function, Not a Team
Effective purple teaming doesn't require a dedicated, full-time team. It can be run as a process where key roles are assigned for specific exercises. Core roles include a coordinator, red team attackers, and your internal blue team defenders.
This approach makes purple teaming accessible even for smaller organizations. You tap into expert offensive skills when you need them, without the overhead. You can find more details from Microsoft on how this functional approach works.
By partnering with us, you get immediate access to pentesters with certifications like OSCP, CEH, and CREST. They bring the attacker's mindset needed to challenge your defenses. Your team gets to focus on what they do best: learning from attacks and improving your security in real time. We move fast, delivering your pen test report within a week.
Using Purple Teaming for Security Compliance

Compliance frameworks like SOC 2, PCI DSS, and HIPAA demand you prove your security controls work. A purple team exercise is your most powerful tool for getting through an audit. It's the difference between telling an auditor "we have a firewall" and showing them proof that it stopped a simulated attack.
The alerts, logs, and remediation steps from the exercise are exactly the evidence auditors want. This proof makes audits smoother and gives you confidence that you're secure, not just compliant on paper. It's how you show you're not just doing checkbox security.
How Purple Teaming Supports Key Frameworks
A purple team exercise gives you the specific proof you need to satisfy auditors. For example, it provides documented evidence that your alerts are firing and your team is responding, which supports requirements for intrusion detection and incident response from the PCI Security Standards Council.
Here's how it helps with major frameworks:
- SOC 2: To meet the Security Trust Service Criterion (CC7), you must demonstrate effective monitoring. A purple team exercise generates the logs and reports that prove you can detect and shut down threats.
- PCI DSS: Requirement 11 mandates regular testing of security systems. Purple teaming directly tests your defenses against realistic attack scenarios.
- HIPAA: The Security Rule requires protection against "reasonably anticipated threats." Purple teaming delivers hard evidence that you're proactively testing your defenses.
An Affordable Path to Proving Compliance
For companies needing a SOC 2 penetration testing or other compliance-driven assessment, a purple team approach delivers a far more meaningful result. It's a live-fire validation of your entire security program.
Our affordable pentesting services are built for this. We bring in OSCP, CEH, and CREST certified pentesters to run the red team side. Your team validates your controls, and you get a comprehensive report in about a week, perfect for audit evidence.
Partner with an External Pentest Provider
Running a real purple team exercise needs skilled attackers. If you don't have an in-house red team, you should bring in an external penetration testing partner. It's the smartest and most affordable move, especially if you're tired of high prices and slow timelines.
You get the offensive firepower you need on-demand, without the huge cost of hiring a full-time red team. An external partner also brings a fresh, unbiased perspective. A third-party pentester comes in with zero assumptions, just like a real attacker would.
The Fastest Way to Strengthen Your Defenses
We provide the "red team" piece of the puzzle for your purple team exercise. We bring our pentesters—holding OSCP, CEH, and CREST certifications—to simulate the latest attacks and give your blue team a realistic challenge.
This collaborative model is the fastest way to get started with purple teaming. Instead of a static report weeks later, your defenders get an interactive training session that hardens your security on the spot. With our affordable model, you skip the frustrations of traditional pen testing.
If you're ready to strengthen your security with a collaborative, affordable, and fast penetration test, fill out our contact form to see how we can help.
Frequently Asked Questions About Purple Teaming
Got questions about purple teaming? Here are the quick, straightforward answers to what we hear most often from IT managers and startup founders.
How Is Purple Teaming Different From a Pen Test?
A standard pen test is adversarial. Attackers work in secret, and you get a report weeks later. A purple team exercise is the opposite; it's a live, open-book training session where your offensive and defensive teams work together. The goal isn't just to find flaws, it's to fix gaps on the spot.
Do I Need to Hire a Dedicated Purple Team?
No. This is a big myth. You don't need to hire a full-time "purple team." Purple teaming is a function, not a job title. The best model is using your internal IT staff as the blue team and bringing in an affordable external firm for the expert red team attackers.
How Often Should We Do Purple Team Exercises?
For most companies, a quarterly purple team exercise is a great place to start. This creates a regular rhythm for testing defenses and sharpening skills. Our fast and affordable model delivers reports in about a week, making it easy to fit regular purple teaming into your schedule.
Ready to move beyond slow, expensive penetration tests and see real improvement in your security? Affordable Pentesting provides the certified OSCP, CEH, and CREST experts to act as your red team, delivering actionable results in about a week. Fill out our contact form to get started.
.svg)
